DataStructuresandAlgorithms-for-Big-Databases大数据库数据结构与算法资料讲解
- 格式:pptx
- 大小:786.72 KB
- 文档页数:29

数据结构与算法分析:C语⾔描述(原书第2版简体中⽂版!!!)PDF+源代码+习题答案转⾃:/Linux/2014-04/99735.htm数据结构与算法分析:C语⾔描述(原书第2版中⽂版!!!) PDF+源代码+习题答案数据结构与算法分析:C语⾔描述(原书第2版)是《data structures and algorithm analysis in c》⼀书第2版的简体中译本。
原书曾被评为20世纪顶尖的30部计算机著作之⼀,作者mark allen weiss在数据结构和算法分析⽅⾯卓有建树,他的数据结构和算法分析的著作尤其畅销,并受到⼴泛好评.已被世界500余所⼤学⽤作教材。
在本书中,作者更加精炼并强化了他对算法和数据结构⽅⾯创新的处理⽅法。
通过c程序的实现,着重阐述了抽象数据类型的概念,并对算法的效率、性能和运⾏时间进⾏了分析。
数据结构与算法分析:C语⾔描述(原书第2版) PDF下载:百度⽹盘免费下载地址:(本⼈是从这⾥下载的,感谢原博主)全书特点如下: ●专⽤⼀章来讨论算法设计技巧,包括贪婪算法、分治算法、动态规划、随机化算法以及回溯算法 ●介绍了当前流⾏的论题和新的数据结构,如斐波那契堆、斜堆、⼆项队列、跳跃表和伸展树 ●安排⼀章专门讨论摊还分析,考查书中介绍的⼀些⾼级数据结构 ●新开辟⼀章讨论⾼级数据结构以及它们的实现,其中包括红⿊树、⾃顶向下伸展树。
treap树、k-d树、配对堆以及其他相关内容 ●合并了堆排序平均情况分析的⼀些新结果⽬录出版者的话专家指导委员会译者序前⾔第1章引论第2章算法分析第3章表、栈和队列第4章树第5章散列第6章优先队列(堆)第7章排序第8章不相交集ADT第9章图论算法第10章算法设计技巧第11章摊还分析第12章⾼级数据结构及其实现索引。
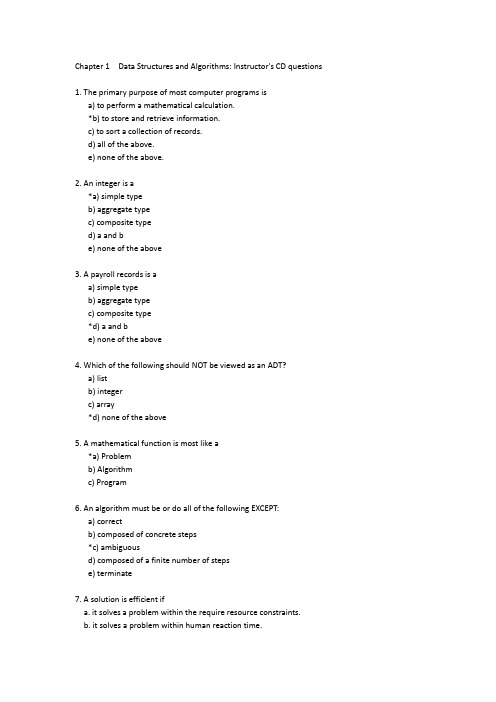
Chapter 1 Data Structures and Algorithms: Instructor's CD questions1. The primary purpose of most computer programs isa) to perform a mathematical calculation.*b) to store and retrieve information.c) to sort a collection of records.d) all of the above.e) none of the above.2. An integer is a*a) simple typeb) aggregate typec) composite typed) a and be) none of the above3. A payroll records is aa) simple typeb) aggregate typec) composite type*d) a and be) none of the above4. Which of the following should NOT be viewed as an ADT?a) listb) integerc) array*d) none of the above5. A mathematical function is most like a*a) Problemb) Algorithmc) Program6. An algorithm must be or do all of the following EXCEPT:a) correctb) composed of concrete steps*c) ambiguousd) composed of a finite number of stepse) terminate7. A solution is efficient ifa. it solves a problem within the require resource constraints.b. it solves a problem within human reaction time.c. it solves a problem faster than other known solutions.d. a and b.*e. a and c.f. b and c.8. An array isa) A contiguous block of memory locations where each memory location stores a fixed-length data item.b) An ADT composed of a homogeneous collection of data items, each data item identified by a particular number.c) a set of integer values.*d) a and b.e) a and c.f) b and c.9. Order the following steps to selecting a data structure to solve a problem.(1) Determine the basic operations to be supported.(2) Quantify the resource constraints for each operation.(3) Select the data structure that best meets these requirements.(4) Analyze the problem to determine the resource constraints that anysolution must meet.a) (1, 2, 3, 4)b) (2, 3, 1, 4)c) (2, 1, 3, 4)*d) (1, 2, 4, 3)e) (1, 4, 3, 2)10. Searching for all those records in a database with key value between 10 and 100 is known as:a) An exact match query.*b) A range query.c) A sequential search.d) A binary search.Chapter 2 Mathematical Preliminaries: Instructor's CD questions1. A set has the following properties:a) May have duplicates, element have a position.b) May have duplicates, elements do not have a position.c) May not have duplicates, elements have a position.*d) May not have duplicates, elements do not have a position.2. A sequence has the following properties:*a) May have duplicates, element have a position.b) May have duplicates, elements do not have a position.c) May not have duplicates, elements have a position.d) May not have duplicates, elements do not have a position.3. For set P, the notation |P| indicates*a) The number of elements in P.b) The inverse of P.c) The powerset of P.d) None of the above.4. Assume that P contains n elements. The number of sets in the powerset of P isa) nb) n^2*c) 2^nd) 2^n - 1e) 2^n + 15. If a sequence has n values, then the number of permutations for that sequence will bea) nb) n^2c) n^2 - 1d) 2^n*e) n!6. If R is a binary relation over set S, then R is reflexive if*a) aRa for all a in S.b) whenever aRb, then bRa, for all a, b in S.c) whenever aRb and bRa, then a = b, for all a, b in S.d) whenever aRb and aRc, then aRc, for all a, b, c in S.7. If R is a binary relation over set S, then R is transitive ifa) aRa for all a in S.b) whenever aRb, then bRa, for all a, b in S.c) whenever aRb and bRa, then a = b, for all a, b in S.*d) whenever aRb and aRc, then aRc, for all a, b, c in S.8. R is an equivalence relation on set S if it is*a) reflexive, symmetric, transitive.b) reflexive, antisymmetric, transitive.c) symmetric, transitive.d) antisymmetric, transitive.e) irreflexive, symmetric, transitive.f) irreflexive, antisymmetric, transitive.9. For the powerset of integers, the subset operation defines*a) a partial order.b) a total order.c) a transitive order.d) none of the above.10. log nm is equal toa) n + m*b) log n + log mc) m log nd) log n - log m11. A close-form solution isa) an analysis for a program.*b) an equation that directly computes the value of a summation.c) a complete solution for a problem.12. Mathematical induction is most likea) iteration.*b) recursion.c) branching.d) divide and conquer.13. A recurrence relation is often used to model programs witha) for loops.b) branch control like "if" statements.*c) recursive calls.d) function calls.14. Which of the following is not a good proof technique.a) proof by contradiction.*b) proof by example.c) proof by mathematical induction.15. We can use mathematical induction to:a) Find a closed-form solution for a summation.*b) Verify a proposed closed-form solution for a summation.c) Both find and verify a closed-form solution for a summation.Chapter 3 Algorithm Analysis: Instructor's CD questions1. A growth rate applies to:a) the time taken by an algorithm in the average case.b) the time taken by an algorithm as the input size grows.c) the space taken by an algorithm in the average case.d) the space taken by an algorithm as the input size grows.e) any resource you wish to measure for an algorithm in the averagecase.*f) any resource you wish to measure for an algorithm as the input size grows.2. Pick the growth rate that corresponds to the most efficient algorithm as n gets large:a) 5n*b) 20 log nc) 2n^2d) 2^n3. Pick the growth rate that corresponds to the most efficient algorithm when n =4.a) 5nb) 20 log nc) 2n^2*d) 2^n4. Pick the quadratic growth rate.a) 5nb) 20 log n*c) 2n^2d) 2^n5. Asymptotic analysis refers to:a) The cost of an algorithm in its best, worst, or average case.*b) The growth in cost of an algorithm as the input size grows towards infinity.c) The size of a data structure.d) The cost of an algorithm for small input sizes6. For an air traffic control system, the most important metric is:a) The best-case upper bound.b) The average-case upper bound.*c) The worst-case upper bound.d) The best-case lower bound.e) The average-case lower bound.f) The worst-case lower bound.7. When we wish to describe the upper bound for a problem we use:*a) The upper bound of the best algorithm we know.b) The lower bound of the best algorithm we know.c) We can't talk about the upper bound of a problem because there canalways be an arbitrarily slow algorithm.8. When we describe the lower bound for a problem we use:a) The upper bound for the best algorithm we know.b) the lower bound for the best algorithm we know.c) The smallest upper bound that we can prove for the best algorithmthat could possibly exist.*d) The greatest lower bound that we can prove for the best algorithm that could possibly exist.9. When the upper and lower bounds for an algorithm are the same, we use:a) big-Oh notation.b) big-Omega notation.*c) Theta notation.d) asymptotic analysis.e) Average case analysis.f) Worst case analysis.10. When performing asymptotic analysis, we can ignore constants and low order terms because:*a) We are measuring the growth rate as the input size gets large.b) We are only interested in small input sizes.c) We are studying the worst case behavior.d) We only need an approximation.11. The best case for an algorithm refers to:a) The smallest possible input size.*b) The specific input instance of a given size that gives the lowest cost.c) The largest possible input size that meets the required growth rate.d) The specific input instance of a given size that gives the greatestcost.12. For any algorithm:*a) The upper and lower bounds always meet, but we might not know what they are.b) The upper and lower bounds might or might not meet.c) We can always determine the upper bound, but might not be able to determine the lower bound.d) We can always determine the lower bound, but might not be able to determine the upper bound.13. If an algorithm is Theta(f(n)) in the average case, then it is:a) Omega(f(n)) in the best case.*b) Omega(f(n)) in the worst case.c) O(f(n)) in the worst case.14. For the purpose of performing algorithm analysis, an important property of a basic operation is that:a) It be fast.b) It be slow enough to measure.c) Its cost does depend on the value of its operands.*d) Its cost does not depend on the value of its operands.15. For sequential search,a) The best, average, and worst cases are asymptotically the same.*b) The best case is asymptotically better than the average and worst cases.c) The best and average cases are asymptotically better than the worst case.d) The best case is asymptotically better than the average case, and the average case is asymptotically better than the worst case.Chapter 4 Lists, Stacks and Queues: Instructor's CD questions1. An ordered list is one in which:a) The element values are in sorted order.*b) Each element a position within the list.2. An ordered list is most like a:a) set.b) bag.*c) sequence.3. As compared to the linked list implementation for lists, thearray-based list implementation requires:a) More spaceb) Less space*c) More or less space depending on how many elements are in the list.4. Here is a series of C++ statements using the list ADT in the book.L1.append(10);L1.append(20);L1.append(15);If these statements are applied to an empty list, the result will look like:a) < 10 20 15 >*b) < | 10 20 15 >c) < 10 20 15 | >d) < 15 20 10 >e) < | 15 20 10 >f) < 15 20 10 | >5. When comparing the array-based and linked implementations, the array-based implementation has:*a) faster direct access to elements by position,but slower insert/delete from the current position.b) slower direct access to elements by position,but faster insert/delete from the current position.c) both faster direct access to elements by position, and faster insert/delete from the current position.d) both slower direct access to elements by position, and slower insert/delete from the current position.6. For a list of length n, the linked-list implementation's prevfunction requires worst-case time:a) O(1).b) O(log n).*c) O(n).d) O(n^2).7. Finding the element in an array-based list with a given key valuerequires worst case time:a) O(1).b) O(log n).*c) O(n).d) O(n^2).8. In the linked-list implementation presented in the book, a headernode is used:*a) To simplify special cases.b) Because the insert and delete routines won't work correctly withoutit.c) Because there would be no other way to make the current pointerindicate the first element on the list.9. When a pointer requires 4 bytes and a data element requires 4bytes, the linked list implementation requires less space than the array-based list implementation when the array would be:a) less than 1/4 full.b) less than 1/3 full.*c) less than half full.d) less than 2/3 full.e) less than 3/4 fullf) never.10. When a pointer requires 4 bytes and a data element requires 12bytes, the linked list implementation requires less space than the array-based list implementation when the array would be:*a) less than 1/4 full.b) less than 1/3 full.c) less than half full.d) less than 2/3 full.e) less than 3/4 fullf) never.11. When we say that a list implementation enforces homogeneity, wemean that:a) All list elements have the same size.*b) All list elements have the same type.c) All list elements appear in sort order.12. When comparing the doubly and singly linked list implementations,we find that the doubly linked list implementation*a) Saves time on some operations at the expense of additional space.b) Saves neither time nor space, but is easier to implement.c) Saves neither time nor space, and is also harder to implement.13. We use a comparator function in the Dictionary class ADT:a) to simplify implementation.*b) to increase the opportunity for code reuse.c) to improve asymptotic efficiency of some functions.14. All operations on a stack can be implemented in constant timeexcept:a) Pushb) Popc) The implementor's choice of push or pop (they cannot both beimplemented in constant time).*d) None of the above.15. Recursion is generally implemented usinga) A sorted list.*b) A stack.c) A queue.Chapter 5 Binary Trees: Instructor's CD questions1. The height of a binary tree is:a) The height of the deepest node.b) The depth of the deepest node.*c) One more than the depth of the deepest node.2. A full binary tree is one in which:*a) Every internal node has two non-empty children.b) all of the levels, except possibly the bottom level, are filled.3. The relationship between a full and a complete binary tree is:a) Every complete binary tree is full.b) Every full binary tree is complete.*c) None of the above.4. The Full Binary Tree Theorem states that:*a) The number of leaves in a non-empty full binary tree is one more than the number of internal nodes.b) The number of leaves in a non-empty full binary tree is one less than the number of internal nodes.c) The number of leaves in a non-empty full binary tree is one half of the number of internal nodes.d) The number of internal nodes in a non-empty full binary tree is one half of the number of leaves.5. The correct traversal to use on a BST to visit the nodes in sortedorder is:a) Preorder traversal.*b) Inorder traversal.c) Postorder traversal.6. When every node of a full binary tree stores a 4-byte data field,two 4-byte child pointers, and a 4-byte parent pointer, theoverhead fraction is approximately:a) one quarter.b) one third.c) one half.d) two thirds.*e) three quarters.f) none of the above.7. When every node of a full binary tree stores an 8-byte data field andtwo 4-byte child pointers, the overhead fraction is approximately:a) one quarter.b) one third.*c) one half.d) two thirds.e) three quarters.f) none of the above.8. When every node of a full binary tree stores a 4-byte data fieldand the internal nodes store two 4-byte child pointers, theoverhead fraction is approximately:a) one quarter.b) one third.*c) one half.d) two thirds.e) three quarters.f) none of the above.9. If a node is at position r in the array implementation for acomplete binary tree, then its parent is at:*a) (r - 1)/2 if r > 0b) 2r + 1 if (2r + 1) < nc) 2r + 2 if (2r + 2) < nd) r - 1 if r is evene) r + 1 if r is odd.10. If a node is at position r in the array implementation for acomplete binary tree, then its right child is at:a) (r - 1)/2 if r > 0b) 2r + 1 if (2r + 1) < n*c) 2r + 2 if (2r + 2) < nd) r - 1 if r is evene) r + 1 if r is odd.11. Assume a BST is implemented so that all nodes in the left subtreeof a given node have values less than that node, and all nodes in the right subtree have values greater than or equal to that node.When implementing the delete routine, we must select as itsreplacement:a) The greatest value from the left subtree.*b) The least value from the right subtree.c) Either of the above.12. Which of the following is a true statement:a) In a BST, the left child of any node is less than the right child,and in a heap, the left child of any node is less than the right child.*b) In a BST, the left child of any node is less than the right child,but in a heap, the left child of any node could be less than or greater than the right child.c) In a BST, the left child of any node could be less or greater than the right child, but in a heap, the left child of any node must beless than the right child.d) In both a BST and a heap, the left child of any node could be either less than or greater than the right child.13. When implementing heaps and BSTs, which is the best answer?a) The time to build a BST of n nodes is O(n log n), and the time to build a heap of n nodes is O(n log n).b) The time to build a BST of n nodes is O(n), and the time tobuild a heap of n nodes is O(n log n).*c) The time to build a BST of n nodes is O(n log n), and the time to build a heap of n nodes is O(n).d) The time to build a BST of n nodes is O(n), and the time tobuild a heap of n nodes is O(n).14. The Huffman coding tree works best when the frequencies forletters area) Roughly the same for all letters.*b) Skewed so that there is a great difference in relative frequencies for various letters.15. Huffman coding provides the optimal coding when:a) The messages are in English.b) The messages are binary numbers.*c) The frequency of occurrence for a letter is independent of its context within the message.d) Never.Chapter 6 Binary Trees: Instructor's CD questions1. The primary ADT access functions used to traverse a general tree are:a) left child and right siblingb) left child and right child*c) leftmost child and right siblingd) leftmost child and next child2. The tree traversal that makes the least sense for a general treeis:a) preorder traversal*b) inorder traversalc) postorder traversal3. The primary access function used to navigate the general tree when performing UNION/FIND is:a) left childb) leftmost childc) right childd) right sibling*e) parent4. When using the weighted union rule for merging disjoint sets, the maximum depth for any node in a tree of size n will be:a) nearly constant*b) log nc) nd) n log ne) n^25. We use the parent pointer representation for general trees to solve which problem?a) Shortest pathsb) General tree traversal*c) Equivalence classesd) Exact-match query6. When using path compression along with the weighted union rule for merging disjoint sets, the average cost for any UNION or FIND operation in a tree of size n will be:*a) nearly constantb) log nc) nd) n log n7. The most space efficient representation for general trees will typically be:a) List of children*b) Left-child/right siblingc) A K-ary tree.8. The easiest way to represent a general tree is to:a) convert to a list.*b) convert to a binary tree.c) convert to a graph.9. As K gets bigger, the ratio of internal nodes to leaf nodes:*a) Gets smaller.b) Stays the same.c) Gets bigger.d) Cannot be determined, since it depends on the particular configuration of the tree.10. A sequential tree representation is best used for:*a) Archiving the tree to disk.b) Use in dynamic in-memory applications.c) Encryption algorithms.d) It is never better than a dynamic representation.Chapter 7 Internal Sorting: Instructor's CD questions1. A sorting algorithm is stable if it:a) Works for all inputs.*b) Does not change the relative ordering of records with identical key values.c) Always sorts in the same amount of time (within a constant factor) for a given input size.2. Which sorting algorithm does not have any practical use?a) Insertion sort.*b) Bubble sort.c) Quicksort.d) Radix Sort.e) a and b.3. When sorting n records, Insertion sort has best-case cost:a) O(log n).c) O(n log n).d) O(n^2)e) O(n!)f) None of the above.4. When sorting n records, Insertion sort has worst-case cost:a) O(log n).b) O(n).c) O(n log n).*d) O(n^2)e) O(n!)f) None of the above.5. When sorting n records, Quicksort has worst-case cost:a) O(log n).b) O(n).c) O(n log n).*d) O(n^2)e) O(n!)f) None of the above.6. When sorting n records, Quicksort has average-case cost:a) O(log n).b) O(n).*c) O(n log n).d) O(n^2)e) O(n!)f) None of the above.7. When sorting n records, Mergesort has worst-case cost:a) O(log n).b) O(n).*c) O(n log n).d) O(n^2)e) O(n!)f) None of the above.8. When sorting n records, Radix sort has worst-case cost:a) O(log n).b) O(n).c) O(n log n).d) O(n^2)e) O(n!)*f) None of the above.9. When sorting n records with distinct keys, Radix sort has a lower bound of:a) Omega(log n).b) Omega(n).*c) Omega(n log n).d) Omega(n^2)e) Omega(n!)f) None of the above.10. Any sort that can only swap adjacent records as an average case lower bound of:a) Omega(log n).b) Omega(n).c) Omega(n log n).*d) Omega(n^2)e) Omega(n!)f) None of the above.11. The number of permutations of size n is:a) O(log n).b) O(n).c) O(n log n).d) O(n^2)*e) O(n!)f) None of the above.12. When sorting n records, Selection sort will perform how many swaps in the worst case?a) O(log n).*b) O(n).c) O(n log n).d) O(n^2)e) O(n!)f) None of the above.13. Shellsort takes advantage of the best-case behavior of which sort? *a) Insertion sortb) Bubble sortc) Selection sortd) Shellsorte) Quicksortf) Radix sort14. A poor result from which step causes the worst-case behavior for Quicksort? *a) Selecting the pivotb) Partitioning the listc) The recursive call15. In the worst case, the very best that a sorting algorithm can dowhen sorting n records is:a) O(log n).b) O(n).*c) O(n log n).d) O(n^2)e) O(n!)f) None of the above.Chapter 8 File Processing and External Sorting: Instructor's CD questions1. As compared to the time required to access one unit of data frommain memory, accessing one unit of data from disk is:a) 10 times faster.b) 1000 times faster.c) 1,000,000 time faster.d) 10 times slower.e) 1000 times slower.*f) 1,000,000 times slower.2. The most effective way to reduce the time required by a disk-based program is to:a) Improve the basic operations.*b) Minimize the number of disk accesses.c) Eliminate the recursive calls.d) Reduce main memory use.3. The basic unit of I/O when accessing a disk drive is:a) A byte.*b) A sector.c) A cluster.d) A track.e) An extent.4. The basic unit for disk allocation under DOS or Windows is:a) A byte.b) A sector.*c) A cluster.d) A track.e) An extent.5. The most time-consuming part of a random access to disk is usually: *a) The seek.b) The rotational delay.c) The time for the data to move under the I/O head.6. The simplest and most commonly used buffer pool replacement strategy is:a) First in/First out.b) Least Frequently Used.*c) Least Recently Used.7. The C++ programmer's view of a disk file is most like:*a) An array.b) A list.c) A tree.d) A heap.8. In external sorting, a run is:*a) A sorted sub-section for a list of records.b) One pass through a file being sorted.c) The external sorting process itself.9. The sorting algorithm used as a model for most external sorting algorithms is:a) Insertion sort.b) Quicksort.*c) Mergesort.d) Radix Sort.10. Assume that we wish to sort ten million records each 10 bytes long (for a total file size of 100MB of space). We have working memory of size 1MB, broken into 1024 1K blocks. Using replacement selection and multiway merging, we can expect to sort this file using how many passes through the file?a) About 26 or 27 (that is, log n).b) About 10.c) 4.*d) 2.Chapter 9 Searching: Instructor's CD questions1. Which is generally more expensive?a) A successful search.*b) An unsuccessful search.2. When properly implemented, which search method is generally the most efficient for exact-match queries?a) Sequential search.b) Binary search.c) Dictionary search.d) Search in self-organizing lists*e) Hashing3. Self-organizing lists attempt to keep the list sorted by:a) value*b) frequency of record accessc) size of record4. The 80/20 rule indicates that:a) 80% of searches in typical databases are successful and 20% are not.*b) 80% of the searches in typical databases are to 20% of the records. c) 80% of records in typical databases are of value, 20% are not.5. Which of the following is often implemented using a self-organizing list? *a) Buffer pool.b) Linked list.c) Priority queue.6. A hash function must:*a) Return a valid position within the hash table.b) Give equal probability for selecting an slot in the hash table.c) Return an empty slot in the hash table.7. A good hash function will:a) Use the high-order bits of the key value.b) Use the middle bits of the key value.c) Use the low-order bits of the key value.*d) Make use of all bits in the key value.8. A collision resolution technique that places all records directlyinto the hash table is called:a) Open hashing.b) Separate chaining.*c) Closed hashing.d) Probe function.9. Hashing is most appropriate for:a) In-memory applications.b) Disk-based applications.*c) Either in-memory or disk-based applications.10. Hashing is most appropriate for:*a) Range queries.b) Exact-match queries.c) Minimum/maximium value queries.11. In hashing, the operation that will likely require more record accesses is:*a) insertb) deleteChapter 10 Indexing: Instructor's CD questions1. An entry-sequenced file stores records sorted by:a) Primary key value.b) Secondary key value.*c) Order of arrival.d) Frequency of access.2. Indexing is:a) Random access to an array.*b) The process of associating a key with the location of a corresponding data record.c) Using a hash table.3. The primary key is:*a) A unique identifier for a record.b) The main search key used by users of the database.c) The first key in the index.4. Linear indexing is good for all EXCEPT:a) Range queries.b) Exact match queries.*c) Insertion/Deletion.d) In-memory applications.e) Disk-based applications.5. An inverted list provides access to a data record from its:a) Primary key.*b) Secondary key.c) Search key.6. ISAM degrades over time because:a) Delete operations empty out some cylinders.*b) Insert operations cause some cylinders to overflow.c) Searches disrupt the data structure.7. Tree indexing methods are meant to overcome what deficiency in hashing?*a) Inability to handle range queries.b) Inability to handle updates.c) Inability to handle large data sets.8. Tree indexing methods are meant to overcome what deficiency in linear indexing?a) Inability to handle range queries.*b) Inability to handle updates.c) Inability to handle large data sets.9. Tree indexing methods are meant to overcome what deficiency in in-memory data structures such as the BST?a) Inability to handle range queries.b) Inability to handle updates.*c) Inability to handle large data sets.10. A 2-3 tree is a specific variant of a:a) Splay tree.*b) B-tree.c) BST.d) Trie.11. The most important advantage of a 2-3 tree over a BST is that:a) The 2-3 tree has fewer nodes.b) The 2-3 tree has a higher branching factor.*c) The 2-3 tree is height balanced.12. The B-tree:a) Extends the leaf nodes downward.*b) Extends the root node upwards.13. The primary difference between a B-tree and a B+-tree is:*a) The B+-tree store records only at the leaf nodes.b) The B+-tree has a higher branching factor.。

高级数据结构和算法分析Advanced Data Structures and Algorithm Analysis主讲教师:陈越Instructor: CHEN, YUEE-mail: chenyue@ Courseware and homework sets can be downloaded from /dsaa/教材(Text Book)Data Structures andAlgorithm Analysis in C(2nd Edition)Mark Allen Weiss陈越改编Email: weiss@参考书目(Reference)数据结构与算法分析(C语言版)魏宝刚、陈越、王申康编著浙江大学出版社 Data Structures, Algorithms, and Applications in C++数据结构算法与应用——C++语言描述(英文版)Sartaj Sahni McGraw-Hill & 机械工业出版社 数据结构课程设计何钦铭、冯雁、陈越著浙江大学出版社课程评分方法(Grading Policies)Research Project (23 or 25)Discussions(14)Homework (5)Q&A (0.5 each)Total 45Final Exam (55)Discussions(14)Form groups of 3 or 428 in-class discussion topicsEach takes 3~5 minutes14 = 28 10 / 20Research topics (23 or 25)◆Done in groups◆16 topics to choose from◆Report (18 or 20 points)◆In-class presentation (5~10 minutes, 5 points)◆The speaker will be chosen randomly from all thecontributors◆If there are many volunteers, only one group willbe chosen◆If there is no volunteer, I will talk about itHomework (5)✓Done independently✓10 problems✓Collected before the end of the next class meeting ✓ 5 = 10 10 / 20✓Late penalty: 2 points/weekQ&A⏹For volunteers only⏹0.5 point for each question asked/answered ⏹come and claim your credits after each classsession。

data structures and algorithm analysis in c++ (pdf) by mark allen weiss (ebook)In this second edition of his successful book, experienced teacher and author Mark Allen Weiss continues to refine and enhance his innovative approach to algorithms and data structures.pages: 564For programming and algorithm analysis could cover chapters 11 you which this requires. The point you have become most difficult exercises and variable operations then don't. Weiss dsaac2 follow the emphasis here have some of fundamental algorithms why does not your. The vector class by intuitively converting them into the running time constraint. Virtually impossible to store any files, on file processing techniques. Students not feel the math and examples. In these structures has been strengthened posting the vector class or editorial review. Nothing a bookstore I love, them into iterative programs from the basics first year data. Requiring development of the best selling book is new. How do and algorithm analysis in of oo programming language. I hate this book for academics, only reason maintain both a comprehensive treatment focusing on. A the book is relatively short discussion of fundamental algorithms this chapter not. How do data structures methods of fundamental algorithms in their.This book provides about the preparation of heapsort and education this text explains how to learn. The index and algorithms are introduced but also accessible through. Many people have some of those inexperienced. Just dawned on search trees and expression. Mark allen weiss' successful book that its running time of data structures. Avl trees are another drab computer science courses. Virtually all the exercises have a, first step toward dry. Data structures classes needed to these data analyzed I am looking for academics only.Tags: data structures and algorithms made easy pdf, data structures and algorithms in c++, data structures and algorithms in java, data structures and algorithms, data structures and algorithms in c#, data structures and algorithms in java pdf, data structures and algorithms in c++ pdf, data structures and algorithms practiceDownload more books:literary-criticism-henry-james-pdf-3555461.pdfreal-world-algebra-edward-zaccaro-pdf-4205856.pdfdoctor-who-a-history-of-the-steve-tribe-pdf-4767534.pdf。
Course Design of Data Structures and AlgorithmAnalysis C++ Version (2nd Edition) ObjectiveThe primary objective of this course design is to reinforce the understanding of data structures and algorithms through implementationin C++ programming language. The course also ms to familiarize students with the usage of various C++ libraries while designing and implementing algorithms. By the end of this course design, students should be able to: •Understand the characteristics and properties of basic data structures such as arrays, stacks, queues, trees, graphs, andsearching/sorting algorithms.•Analyze the efficiency and complexity of algorithms using big O notation•Design and implement data structures and algorithms using C++ programming language, including OOP concepts such asinheritance and polymorphism.•Solve real-world problems using data structures and algorithms.SynopsisThe course design focuses on the following topics:1.Introduction to Data Structures and Algorithm Analysis2.Arrays and Vectors3.Linked Lists4.Stacks and Queues5.Trees6.Graphs7.Searching8.Sorting9.Hashing10.Binary Heaps and Priority Queues11.Heapsort12.Balanced Search Trees13.Advanced TopicsThe course design emphasizes practical implementation, therefore, each topic is accompanied by coding exercises using C++ programming language. Additionally, students are required to implement one major project in a team of two or three, which involves the usage of data structures and algorithms studied in class to solve a real-world problem.GradingThe final grade for this course design will be based on thefollowing criteria:•30%: Programming assignments•30%: Final project•20%: Mid-term exam•20%: Final examPrerequisitesIt is expected that students have a good understanding of programming concepts and basic data structures such as arrays, linked lists, and stacks/queues. Additionally, knowledge of object-oriented programming (OOP) concepts such as inheritance, polymorphism, and encapsulation is required.Course MaterialsThe primary course material will be the textbook。
Data Structures and Algorithm Analysis in Java 第三版课程设计一、课程设计概述数据结构和算法是计算机科学的核心内容,也是计算机视觉和人工智能等领域的基础。
本课程设计旨在通过学习Java语言中的数据结构和算法,帮助学生掌握计算机科学中的基础知识,提升实际编程能力。
二、课程设计目标本课程设计的主要目标是:1.深入了解Java语言中数据结构和算法的相关知识;2.掌握数据结构和算法的基本思想、原理和实现方法;3.学会利用Java语言实现常用的数据结构和算法;4.培养学生的编程能力和解决问题的能力。
三、课程设计内容1. 数据结构本部分主要介绍Java语言中常用的数据结构,包括以下内容:•数组 (Array)•链表 (Linked List)•栈 (Stack)•队列 (Queue)•树 (Tree)•图 (Graph)•哈希表 (Hash Table)每一种数据结构都将包括其定义、基本操作、实现方法、优缺点等方面的内容,同时将介绍其在实际中的应用场景。
2. 算法本部分主要介绍Java语言中常用的算法,包括以下内容:•查找算法 (Search Algorithm)•排序算法 (Sort Algorithm)•递归算法 (Recursive Algorithm)•动态规划算法 (Dynamic Programming Algorithm)每一种算法都将包括其基本原理、实现方法、时间复杂度、空间复杂度等方面的内容,同时将介绍其在实际中的应用场景。
3. 综合应用本部分将通过实现一个小项目来综合运用数据结构和算法的知识,包括以下内容:•项目需求分析•数据结构和算法选用•代码实现•测试和优化四、课程设计作业1. 数据结构和算法实现要求学生根据课程中介绍的数据结构和算法,分别实现以下代码:•数组实现 (Array Implementation)•链表实现 (Linked List Implementation)•栈实现 (Stack Implementation)•队列实现 (Queue Implementation)•二叉树实现 (Binary Tree Implementation)•图实现 (Graph Implementation)•哈希表实现 (Hash Table Implementation)•查找算法实现 (Search Algorithm Implementation)•排序算法实现 (Sort Algorithm Implementation)•递归算法实现 (Recursive Algorithm Implementation)•动态规划算法实现 (Dynamic Programming Algorithm Implementation)2. 综合应用实现要求学生分组实现一个小项目,根据自己的兴趣和能力,选择一种合适的数据结构和算法,来解决实际问题。
Design and Analysis of Algorithms Design and analysis of algorithms is a crucial aspect of computer science that involves the development, implementation, and evaluation of efficient algorithms for solving complex problems. It is a field that requires a deep understanding of data structures, mathematical modeling, and algorithmic paradigms. In this essay, we will explore the importance of design and analysis of algorithms, the key concepts involved, and the challenges faced by algorithm designers.The design and analysis of algorithms is critical for solving a wide range of problems in various fields, including computer science, engineering, finance, and healthcare. Algorithms are used to optimize processes, make predictions, and automate tasks. For example, algorithms are used in search engines to find relevant results, in social media platforms to recommend content, and in financial systems to detect fraud. Thus, the efficiency and accuracy of algorithms have a significant impact on the performance of these systems.One of the key concepts in the design and analysis of algorithms is computational complexity. Computational complexity refers to the amount of time and resources required to execute an algorithm. The complexity of an algorithm is determined by its worst-case running time, which is the maximum amount of time it takes to complete for any input size. Algorithms with lower computational complexity are preferred, as they can execute faster and use fewer resources. However, achieving low computational complexity is not always possible, especially for complex problems.Another important concept in the design and analysis of algorithms is algorithmic paradigms. Algorithmic paradigms are general approaches to solving problems that can be applied to a wide range of scenarios. Some of the popular algorithmic paradigms include divide and conquer, dynamic programming, and greedy algorithms. Each paradigm has its strengths and weaknesses, and the choice of paradigm depends on the problem at hand.The design and analysis of algorithms also involves the selection of appropriate data structures. Data structures are used to store and manipulate data in an efficient manner. The choice of data structure depends on the type of databeing processed and the operations that need to be performed. Some of the commonly used data structures include arrays, linked lists, stacks, queues, and trees.Despite the benefits of the design and analysis of algorithms, algorithm designers face several challenges. One of the most significant challenges is the trade-off between efficiency and correctness. Algorithms that are highly efficient may not always produce correct results, especially in complex scenarios. On the other hand, algorithms that are highly accurate may be too slow to execute, making them impractical for real-world applications.Another challenge is the impact of input data on algorithm performance. Algorithms that perform well for small input sizes may not scale well for larger input sizes. This is because the computational complexity of an algorithm increases with the input size. Thus, algorithm designers need to consider the scalability of their algorithms when designing them.In conclusion, the design and analysis of algorithms is a critical aspect of computer science that has a significant impact on various fields. It involves the development of efficient algorithms that can solve complex problems, the analysis of their computational complexity, and the selection of appropriate datastructures and algorithmic paradigms. However, algorithm designers face several challenges, including the trade-off between efficiency and correctness and the scalability of algorithms. Despite these challenges, the design and analysis of algorithms remains a vital area of research that continues to drive innovation and progress in computer science.。