CCNA中英文试题两套
- 格式:doc
- 大小:453.50 KB
- 文档页数:12
CCNA中英对照题库(0-10.pdfCCNA (200-120)题库中英对照整理于:2015 年 3 月 31 日版本:1.2 声明:本题库来源互联网(鸿鹄论坛)本题库为英文考试原版左右选择题中文考试为随机抽取英文题的中译版此题库非中文考试题库,而是英文题库手动翻译此题库为手工个人翻译,存在错误和不妥难免,不代表任何官方机构和组织本题库旨在更好的理解英文原本题库,也可以用于中文考试参考用。
如发现任何错误或不当之处,可以自行修改,但请更新版本以免混乱,也可致上传者。
QUESTION 001 Refer to the exhibit. What will Router1 do when it receives the data frame shown? (Choose three.) 参照下图,这个图示显示了R1接受到如图所示数据帧的时候会怎么做? A. Router1 will strip off the source MAC address and replace it with the MAC address 0000.0c36.6965. R1会剥离源MAC地址,以 0000:0C36.6965 代替。
B. Router1 will strip off the source IP address and replace it with the IP address 192.168.40.1. R1会剥离源 IP 地址,1/ 10以 192.168.40.1 代替。
C. Router1 will strip off the destination MAC address and replace it with the MAC address 0000.0c07.4320. R1会剥离源MAC地址,以 0000:0C36.6965 代替。
D. Router1 will strip off the destination IP address and replace it with the IP address of 192.168.40.1. R1会剥离目的 IP 地址,以 192.168.40.1 代替。
CCNA 2 - Chapter 11What is one advantage of using the cut-through switching method instead of the store-and-forward switching method?has a positive impact on bandwidth by dropping most of the invalid framesmakes a fast forwarding decision based on the source MAC address of the framehas a lower latency appropriate for high-performance computing applications*provides the flexibility to support any mix of Ethernet speeds2A network designer must provide a rationale to a customer for a design which will move an enterprise from a flat network topology to a hierarchical network topology. Which two features of the hierarchical design make it the better choice? (Choose two.)reduced cost for equipment and user trainingless required equipment to provide the same performance levelssimpler deployment for additional switch equipment*easier to provide redundant links to ensure higher availability*lower bandwidth requirements3What are two advantages of modular switches over fixed-configuration switches? (Choose two.)availability of multiple ports for bandwidth aggregationlower forwarding ratesneed for fewer power outlets*lower cost per switchincreased scalability*4Refer to the exhibit. Consider that the main power has just been restored. PC1 asks the DHCP server for IPv4 addressing. The DHCP server sends it an IPv4 address. While PC2 is still booting up, PC3 issues a broadcast IPv4 DHCP request. To which port will SW1 forward this request?to Fa0/1, Fa0/2, and Fa0/4 onlyto Fa0/1, Fa0/2, Fa0/3, and Fa0/4to Fa0/1 and Fa0/2 onlyto Fa0/1, Fa0/2, and Fa0/3 only*to Fa0/1 only5What is one function of a Layer 2 switch?forwards data based on logical addressinglearns the port assigned to a host by examining the destination MAC addressduplicates the electrical signal of each frame to every portdetermines which interface is used to forward a frame based on the destination MAC address*6Refer to the exhibit. Fill in the blank.There are ” 12” collision domains in the topology.7What is a collapsed core in a network design?a combination of the functionality of the access, distribution, and core layersa combination of the functionality of the access and core layersa combination of the functionality of the distribution and core layers*a combination of the functionality of the access and distribution layers 8What are two reasons a network administrator would segment a network with a Layer 2 switch? (Choose two.)to enhance user bandwidth*to eliminate virtual circuitsto create more broadcast domainsto isolate traffic between segments*to isolate ARP request messages from the rest of the networkto create fewer collision domains9Refer to the exhibit.How is a frame sent from PCA forwarded to PCC if the MAC address table on switch SW1 is empty?SW1 forwards the frame directly to SW2. SW2 floods the frame to all ports connected to SW2, excluding the port through which the frame entered the switch.SW1 floods the frame on all ports on the switch, excluding the interconnected port to switch SW2 and the port through which the frame entered the switch.SW1 floods the frame on all ports on SW1, excluding the port through which the frame entered the switch.*SW1 drops the frame because it does not know the destination MAC address.10Place the options in the following order:[+] appropriate for high performance computing applications[+] forwarding process can begin after receiving the destination address [+] may forward invalid frames[#] error checking before forwarding[#] forwarding process only begin after receiving the entire frame [#] only forward valid frames[+] Order does not matter within this group.[#] Order does not matter within this group.11What is a basic function of the Cisco Borderless Architecture distribution layer?aggregating Layer 3 routing boundaries*aggregating all the campus blocksacting as a backboneproviding access to the user12ABC, Inc. has about fifty hosts in one LAN. The administrator would like to increase the throughput of that LAN. Which device will increase the number of collision domains and thereby increase the throughput of the LAN?hubhostNICswitch*13What does the term “port density” represent for an Ethernet switch?the numbers of hosts that are connected to each switch portthe speed of each portthe memory space that is allocated to each switch portthe number of available ports*14Which type of transmission does a switch use when the destination MAC address is not contained in the MAC address table?anycastunicastbroadcast*multicast15What is a basic function of the Cisco Borderless Architecture access layer?aggregates Layer 3 routing boundariesprovides high availabilityaggregates Layer 2 broadcast domainsprovides access to the user*16What information is added to the switch table from incoming frames?source MAC address and incoming port number*destination MAC address and incoming port numberdestination IP address and incoming port numbersource IP address and incoming port number17Fill in the blank.A “converged” network is one that uses the same infrastructure to carry voice, data, and video signals.18An administrator purchases new Cisco switches that have a feature called StackPower. What is the purpose of this feature?It enables many switches to be connected with a special fiber-optic power cable to provide higher bandwidth.It enables the sharing of power among multiple stackable switches.*It enables many switches to be connected to increase port density.It enables many switches to be physically stacked in an equipment rack.It enables AC power for a switch to be provided from a powered patch panel.19Which switch form factor should be used when large port density, fault tolerance, and low price are important factors?fixed-configuration switchmodular switchstackable switch*rackable 1U switch20Refer to the exhibit. Fill in the blank.There are ” 5 ”CCNA 2 - Chapter 2Posted by beotron at 8:59 PM1. A static route that points to the next hop IP will have what administrative distance and metric in the routing table?• administrative distance of 0 and metric of 0• administrative distance of 0 and metric of 1• administrative distance of 1 and metric of 0• administrative distance of 1 and metric of 12. What address can be used to summarize networks 172.16.1.0/24, 172.16.2.0/24, 172.16.3.0/24, and 172.16.4.0/24?• 172.16.0.0/21• 172.16.1.0/22• 172.16.0.0 255.255.255.248• 172.16.0.0 255.255.252.03. The routers in the diagram use the subnet assignments shown. What is the most efficient route summary that can be configured on Router3 to advertise the internal networks to the cloud?• 192.1.1.0/26 and 192.1.1.64/27• 192.1.1.128/25• 192.1.1.0/23 and 192.1.1.64/23• 192.1.1.0/24• 192.1.1.0/25• 192.1.1.0/24 and 192.1.1.64/244. Refer to the exhibit. What is the significance of the /8 in the route to the 10.0.0.0 network?• It indicates that there are 8 hops between this router and the 10.0.0.0 network.• It represents the time, in milliseconds, it takes for a ping to reply when sent to the 10.0.0.0 network.• It indicates that there are 8 subnets in the destination network to which the router can forward packets.• It indicates the number of consecutive bits, from the left, in the destination IP address of a packet that must match 10.0.0.0 to use that route.5. Refer to the exhibit. How will packets destined to the 172.16.0.0 network be forwarded?• Router1 will perform recursive lookup and packet will exit S0/0.• Router1 will perform recursive lookup and packet will exit S0/1.• There is no matching interface associated with network 172.16.0.0 so packets will be dropped.• There is no matching interface associated with network 172.16.0.0 so packets will take gateway of last resort and exit out S0/2.6. A network administrator enters the following command into Router1: ip route 192.168.0.0255.255.255.0 S0/1/0. Router1 then receives a packet that is destined for 192.168.0.22/24. After finding the recently configured static route in the routing table, what does Router1 do next to process the packet? • drops the packet because the destination host is not listed in the routing table• looks up the MAC address of the S0/1/0 interface to determine the destination MAC address of the new frame• performs a recursive lookup for the IP address of the S0/1/0 interface before forwarding the packet• encapsulates the packet into a frame for the WAN link and forwards the packet out the S0/1/0 interface7. Refer to the exhibit. Given the output in the exhibit, how would a clock rate be determined for this link? • The rate would be negotiated by both routers.• A rate would not be selected due to the DCE/DTE connection mismatch.• The rate configured on the DTE determines the clock rate.• The rate configured on the DCE determines the clock rate.8. Refer to the exhibit. Which set of commands will configure static routes that will allow the WinterPark and the Altamonte routers to deliver packets from each LAN and direct all other traffic to the Internet? • WinterPark(config)# ip route 0.0.0.0 0.0.0.0 192.168.146.1Altamonte(config)# ip route 10.0.234.0 255.255.255.0 192.168.146.2Altamonte(config)# ip route 0.0.0.0 0.0.0.0 s0/1• WinterPark(config)# ip route 0.0.0.0 0.0.0.0 192.168.146.1Altamonte(config)# ip route 10.0.234.0 255.255.255.0 192.168.146.2Altamonte(config)# ip route 198.18.222.0 255.255.255.255 s0/1• WinterPark(config)# ip route 172.191.67.0 255.255.255.0 192.168.146.1• WinterPark(config)# ip route 0.0.0.0 0.0.0.0 192.168.146.1Altamonte(config)# ip route 10.0.234.0 255.255.255.0 192.168.146.2• WinterPark(config)# ip route 172.191.67.0 255.255.255.0 192.168.146.1Altamonte(config)# ip route 10.0.234.0 255.255.255.0 192.168.146.2Altamonte(config)# ip route 0.0.0.0 0.0.0.0 s0/09. Hosts on two separate subnets cannot communicate. The network administrator suspects a missing route in one of the routing tables. Which three commands can be used to help troubleshoot Layer 3 connectivity issues? (Choose three.)• ping• show arp• traceroute• show ip route• show interface• show cdp neighbor d etail10. Refer to the exhibit. A company network engineer is assigned to establish connectivity between the two Ethernet networks so that hosts on the 10.1.1.0/24 subnet can contact hosts on the 10.1.2.0/24 subnet. The engineer has been told to use only static routing for these company routers. Which set of commands will establish connectivity between the two Ethernet networks?• R1(config)# ip route 10.1.2.0 255.255.255.0 192.168.0.1R2(config)# ip route 10.1.1.0 255.255.255.0 192.168.0.2• R1(config)# ip route 10.1.2.0 255.255.255.0 192.168.0.2R2(config)# ip route 10.1.1.0 255.255.255.0 192.168.0.1• R1(config)# ip route 10.1.1.0 255.255.255.0 192.168.0.2R2(config)# ip route 10.1.2.0 255.255.255.0 192.168.0.1• R1(config)# ip route 10.1.1.0 255.255.255.0 192.168.0.1R2(config)# ip route 10.1.2.0 255.255.255.0 192.168.0.2• R1(config)# ip route 0.0.0.0 0.0.0.0 10.1.2.1R2(config)# ip route 0.0.0.0 0.0.0.0 10.1.1.111. Which of the following are displayed by the Router# show cdp neighbors command? (Choose three.) • load• platform• reliability• holdtime• local interface12. Refer to the exhibit. What two commands are required to provide connectivity between the192.168.1.0 and 10.0.0.0 networks without requiring recursive lookup? (Choose two.)• A(config)# ip route 10.0.0.0 255.0.0.0 s 0/1/0• A(config)# ip route 10.0.0.0 255.0.0.0 172.16.40.2• A (config)# ip route 10.0.0.0 255.0.0.0 s 0/0/0• B(config)# ip route 192.168.1.0 255.255.255.0 s 0/0/0• B (config)# ip route 192.168.1.0 255.255.255.0 172.16.40.1• B(config)# ip route 192.168.1.0 255.255.255.0 s 0/1/013. Refer to the exhibit. What two commands will change the next-hop address for the 10.0.0.0/8 network from 172.16.40.2 to 192.168.1.2? (Choose two.)• A(config)# no network 10.0.0.0 255.0.0.0 172.16.40.2• A(config)# no ip address 10.0.0.1 255.0.0.0 172.16.40.2• A(config)# no ip route 10.0.0.0 255.0.0.0 172.16.40.2• A(config)# ip route 10.0.0.0 255.0.0.0 s0/0/0• A(config)# ip route 10.0.0.0 255.0.0.0 192.168.1.214. What happens to a static route entry in a routing table when the outgoing interface is not available? • The route is removed from the table.• The router polls neighbors for a replacement route.• The route remains in the table because it was defined as static.• The router redirects the static route to compensate for the loss of the next hop device.15. A router has one static route to each destination network. Which two scenarios would require an administrator to alter the static routes that are configured on that router? (Choose two.)• The destination network no longer exists.• The destination network is moved to a different interface on the same router.• The path between the source and destination is upgraded with a higher bandwidth link.• A topology change occurs where the exi sting next-hop address or exit interface is not accessible.• The remote destination network interface has to be down for 15 minutes of maintenance.16. Why is it advisable to enter a next-hop IP address when creating a static route whose exit interface is an Ethernet network?• Adding the next-hop address eliminates the need for the router to do any lookups in the routing table before forwarding a packet.• In a multi-access network, the router cannot determine the next-hop MAC address for the Ethernet frame without a next-hop address.• Using a next-hop address in a static route provides a route with a lower metric.• In multi-access networks, using a next-hop address in a static route makes that route a candidate default route.17. The output of the Router# show interfaces serial 0/1 command displays the following:• Serial0/1 is up, line protocol is down.• What is the most likely cause for the line protocol being down?• Serial0/1 is shutdown.• There is no cable connecting the routers.• The remote rout er is using serial 0/0.• No clock rate has been set.18. Refer to the exhibit. Which static route should be configured on Router1 so that host A will be able to reach host B on the 172.16.0.0 network?• ip route 192.168.0.0 172.16.0.0 255.255.0.0• ip rou te 172.16.0.0 255.255.0.0 192.168.0.1• ip route 172.16.0.0 255.255.0.0 S0/0/1• ip route 172.16.0.0 255.255.0.0 S0/0/019. What two devices are responsible for converting the data from the WAN service provider into a form acceptable by the router? (Choose two).• the serial port of the router• a modem• a switch• the ethernet port of the router• a CSU/DSU device• a DTE device20. Which of the following is true regarding CDP and the graphic shown?• CDP running on Router D will gather information about routers A, B, C, and E.• By default, Router A will receive CDP advertisements from routers B and C.• If routers D and E are running different routing protocols, they will not exchange CDP information.• Router E can use CDP to identify the IOS running on Router B.21. Which two statements describe functions or characteristics of CDP? (Choose two.)• It starts up automatically and allows the device to detect directly connected neighbor devices that use CDP.• It operates at the network layer and allows two systems to learn about each other.• It creates a topology map of the entire network.• It allows systems to learn about each other even if different network layer protocols are configured.• It forwards advertisements about routes for faster convergence.22. Which piece of information is available from examining the output of the command show ip interface brief?• Interface speed and duplex• Interface MTU• Errors• Interface MAC address• Interface IP addressCCNA 2 - Chapter 31A network administrator is determining the best placement of VLAN trunklinks. Which two types of point-to-point connections utilize VLAN trunking? (Choose two.)between two switches that share a common VLANbetween a switch and a server that has an 802.1Q NIC*between a switch and a client PCbetween a switch and a network printerbetween two switches that utilize multiple VLANs*2What happens to a port that is associated with VLAN 10 when the administrator deletes VLAN 10 from the switch?The port automatically associates itself with the native VLAN. The port creates the VLAN again.The port goes back to the default VLAN.The port becomes inactive.*3Refer to the exhibit. Interface Fa0/1 is connected to a PC. Fa0/2 is a trunk link to another switch. All other ports are unused. Which security best practice did the administrator forget to configure?Configure all unused ports to a ‘black-hole’ VLAN that is not used f or anything on the network.Disable autonegotiation and set ports to either static access or static trunk.Change the native VLAN to a fixed VLAN that is distinct from all user VLANs and to a VLAN number that is not VLAN 1.All user ports are associated with VLANs distinct from VLAN 1 and distinct from the ‘black-hole’ VLAN.*4Which command is used to remove only VLAN 20 from a switch?no switchport access vlan 20delete flash:vlan.datno vlan 20*delete vlan.dat5A Cisco Catalyst switch has been added to support the use of multiple VLANs as part of an enterprise network. The network technician finds it necessary to clear all VLAN information from the switch in order to incorporate a new network design. What should the technician do to accomplish this task?Erase the startup configuration and reboot the switch.Erase the running configuration and reboot the switch.Delete the startup configuration and the vlan.dat file in the flash memory of the switch and reboot the switch.*Delete the IP address that is assigned to the management VLAN and reboot the switch.6What is the effect of issuing a switchport access vlan 20 command on the Fa0/18 port of a switch that does not have this VLAN in the VLAN database?VLAN 20 will be created automatically.*The command will have no effect on the switch.Port Fa0/18 will be shut down.An error stating that VLAN 20 does not exist will be displayed and VLAN 20 is not created.Which command displays the encapsulation type, the voice VLAN ID, and the access mode VLAN for the Fa0/1 interface?show mac address-table interface Fa0/1show interfaces Fa0/1 switchport*show interfaces trunkshow vlan brief8Place the options in the following order:- not scored -dynamic autononegotiatedynamic desirabletrunk9Port Fa0/11 on a switch is assigned to VLAN 30. If the command no switchport access vlan 30 is entered on the Fa0/11 interface, what will happen?Port Fa0/11 will be returned to VLAN 1.*VLAN 30 will be deleted.An error message would be displayed.Port Fa0/11 will be shutdown.What must the network administrator do to remove Fast Ethernet port fa0/1 from VLAN 2 and assign it to VLAN 3?Enter the no vlan 2 and the vlan 3 commands in global configuration mode. Enter the switchport trunk native vlan 3 command in interface configuration mode.Enter the switchport access vlan 3 command in interface configuration mode.*Enter the no shutdown in interface configuration mode to return it to the default configuration and then configure the port for VLAN 3.11Which two Layer 2 security best practices would help prevent VLAN hopping attacks? (Choose two.)Disable DTP autonegotiation on end-user ports.*Change the management VLAN to a distinct VLAN that is not accessible by regular users.Statically configure all ports that connect to end-user host devices to be in trunk mode.Change the native VLAN number to one that is distinct from all user VLANs and is not VLAN 1.*Use SSH for all remote management access.12In a basic VLAN hopping attack, which switch feature do attackers take advantage of?automatic encapsulation negotiationthe default automatic trunking configuration*an open Telnet connectionforwarding of broadcasts13A Cisco switch currently allows traffic tagged with VLANs 10 and 20 across trunk port Fa0/5. What is the effect of issuing a switchport trunk allowed vlan 30 command on Fa0/5?It allows only VLAN 30 on Fa0/5.*It allows a native VLAN of 30 to be implemented on Fa0/5.It allows VLANs 1 to 30 on Fa0/5.It allows VLANs 10, 20, and 30 on Fa0/5.14Refer to the exhibit. A frame is traveling between PC-A and PC-B through the switch. Which statement is true concerning VLAN tagging of the frame?No VLAN tag is added to the frame.*A VLAN tag is added when the frame is accepted by the switch.A VLAN tag is added when the frame is forwarded out the port to PC-B.A VLAN tag is added when the frame leaves PC-A.15Refer to the exhibit. PC-A and PC-B are both in VLAN 60. PC-A is unable to communicate with PC-B. What is the problem?The native VLAN is being pruned from the link.The VLAN that is used by PC-A is not in the list of allowed VLANs on the trunk.*The trunk has been configured with the switchport nonegotiate command. The native VLAN should be VLAN 60.16What VLANs are allowed across a trunk when the range of allowed VLANs is set to the default value?All VLANs will be allowed across the trunk.*Only the native VLAN will be allowed across the trunk.The switches will negotiate via VTP which VLANs to allow across the trunk. Only VLAN 1 will be allowed across the trunk.17Under which two occasions should an administrator disable DTP while managing a local area network? (Choose two.)on links that should not be trunking*when connecting a Cisco switch to a non-Cisco switch*on links that should dynamically attempt trunkingwhen a neighbor switch uses a DTP mode of dynamic autowhen a neighbor switch uses a DTP mode of dynamic desirable18Open the PT Activity. Perform the tasks in the activity instructions and then answer the question.Which PCs will receive the broadcast sent by PC-C?PC-D, PC-E*PC-A, PC-B, PC-D, PC-EPC-A, PC-BPC-A, PC-B, PC-D, PC-E, PC-FPC-A, PC-B, PC-E19Which two statements are true about VLAN implementation? (Choose two.)The network load increases significantly because of added trunking information.Devices in one VLAN do not hear the broadcasts from devices in another VLAN.*The size of the collision domain is reduced.VLANs logically group hosts, regardless of physical location.*The number of required switches in a network decreases.20Refer to the exhibit. DLS1 is connected to another switch, DLS2, via a trunk link. A host that is connected to DLS1 is not able to communicate to a host that is connected to DLS2, even though they are both in VLAN 99. Which command should be added to Fa0/1 on DLS1 to correct the problem?switchport trunk allowed vlan add 99switchport trunk native vlan 66*switchport mode dynamic autoswitchport nonegotiate21Which switch feature ensures that no unicast, multicast, or broadcast traffic is passed between ports that are configured with this feature?switch port securityPVLAN protected port*ACLVLAN22Fill in the blank. Use the full command syntax.The ” show vlan brief” command displays the VLAN assignment for all ports as well as the existing VLANs on the switch.23Which three statements accurately describe VLAN types? (Choose three).An 802.1Q trunk port, with a native VLAN assigned, supports both tagged and untagged traffic.*A management VLAN is any VLAN that is configured to access management features of the switch.*A data VLAN is used to carry VLAN management data and user-generated traffic.Voice VLANs are used to support user phone and e-mail traffic on a network. VLAN 1 is always used as the management VLAN.After the initial boot of an unconfigured switch, all ports are members of the default VLAN.*24Which command should the network administrator implement to prevent the transfer of DTP frames between a Cisco switch and a non-Cisco switch?S1(config-if)# switchport mode trunkS1(config-if)# switchport mode accessS1(config-if)# switchport nonegotiate*S1(config-if)# switchport mode dynamic desirableS1(config-if)# switchport trunk allowed vlan noneCCNA 2 - Chapter 41What type of IPv6 address is required as a minimum on IPv6 enabled interfaces?staticglobal unicastlink-local*loopbackunique local2In order for packets to be sent to a remote destination, what three pieces of information must be configured on a host? (Choose three.)default gateway*hostnameDNS server addressDHCP server addressIP address*subnet mask*3What two pieces of information are displayed in the output of the show ip interface brief command? (Choose two.)MAC addressesLayer 1 statuses*IP addresses*next-hop addressesinterface descriptionsspeed and duplex settings4Place the options in the following order:next hopdestination networkmetric- not scored -administrative distanceroute timestamproute source protocol- not scored -5Which two items are used by a host device when performing an ANDing operation to determine if a destination address is on the same local network? (Choose two.)destination MAC addressnetwork numberdestination IP address*source MAC addresssubnet mask*6Refer to the exhibit. A network administrator issues the show ipv6 route command on R1. What two conclusions can be drawn from the routing table? (Choose two.)Packets that are destined for the network 2001:DB8:ACAD:2::/64 will be forwarded through Fa0/1.R1 does not know a route to any remote networks.*The interface Fa0/1 is configured with IPv6 address2001:DB8:ACAD:A::12.*Packets that are destined for the network 2001:DB8:ACAD:2::54/128 will be forwarded through Fa0/0.The network FF00::/8 is installed through a static route command.7Refer to the exhibit. What is the purpose of the highlighted field in the line that is displayed from the show ip route command?It indicates that this is a directly connected route.It indicates that this route has been deleted from the routing table. It indicates that this route was learned via EIGRP.*It indicates that this is a default route.8Which two statements correctly describe the concepts of administrative distance and metric? (Choose two.)The metric varies depending which Layer 3 protocol is being routed, such as IP.A router first installs routes with higher administrative distances. The value of the administrative distance can not be altered by the network administrator.Routes with the smallest metric to a destination indicate the best path.* Administrative distance refers to the trustworthiness of a particular route.*The metric is always determined based on hop count.9What are two functions of a router? (Choose two.)It manages the VLAN database.It increases the size of the broadcast domain.It controls the flow of data via the use of Layer 2 addresses.It determines the best path to send packets.*It connects multiple IP networks.*10A packet moves from a host on one network to a device on a remote network within the same company. If NAT is not performed on the packet, which two items remain unchanged during the transfer of the packet from source to destination? (Choose two.)destination MAC addresssource ARP tablesource IP address*destination IP address*source MAC addressLayer 2 header11。
1、下列哪两种说法正确描述了VLAN的优点?(选择两项。
)45Which two statements describe the benefits of VLANs? (Choose two.)VLAN通过调节流量控制和窗口大小来提升网络性能。
VLANs improve network performance by regulating flow control and window size.VLAN使交换机可通过VLAN ID过滤将数据包路由到远程网络。
VLANs enable switches to route packets to remote networks via VLAN ID filtering.VLAN通过减少交换机上所需的物理端口数量来降低网络开销。
VLANs reduce network cost by reducing the number of physical ports required on switches. VLAN通过识别有权访问敏感数据和应用程序的用户来提升网络安全性。
VLANs improve network security by isolating users that have access to sensitive data and applications.VLAN将网络划分为较小的逻辑网络,这降低了网络对广播风暴的敏感性。
VLANs dividea network into smaller logical networks, resulting in lower susceptibility to broadcast storms.2、默认交换机配置中的VLAN1有哪两项特点?(选择两项。
)23What are two characteristics of VLAN1 in a default switch configuration? (Choose two.)VLAN1应重命名。
CCNA学习指南第2章复习题中英文翻译版1. What are the decimal and hexadecimal equivalents of the binary number 10011101?(Choose two.)1. 二进制数10011101等效的十进制和十六进制数分别是多少?(选择两项。
)A. 159B. 157C. 185D. 0x9DE. 0xD9F. 0x1592. Which of the following allows a router to respond to an ARP request that is intended for a remote host?2. 下列哪一项允许路由器对远端主机的ARP请求做出响应?A. Gateway DP网关DPB. Reverse ARP (RARP)反向ARPC. Proxy ARP代理ARPD. Inverse ARP逆向ARPE. Address Resolution Protocol (ARP)地址解析协议3. You want to implement a mechanism that automates the IP configuration, including IP address, subnet mask, default gateway, and DNS information. Which protocol will you use to accomplish this?3. 你想实现自动IP配置,包括IP地址,子网掩码,默认网关和DNS信息。
你应该使用什么协议来完成这?A. SMTP简单邮件传输协议B. SNMP简单网络管理协议C. DHCP动态主机控制协议D. ARP地址解析协议4. What protocol is used to find the hardware address of a local device?4. 什么协议用来找本地设备的硬件地址?A. RARPB. ARPC. IPD. ICMPE. BootP5. Which of the following are layers in the TCP/IP model? (Choose three.)5. 下列哪些层属于TCP/IP模型?(选择三项。
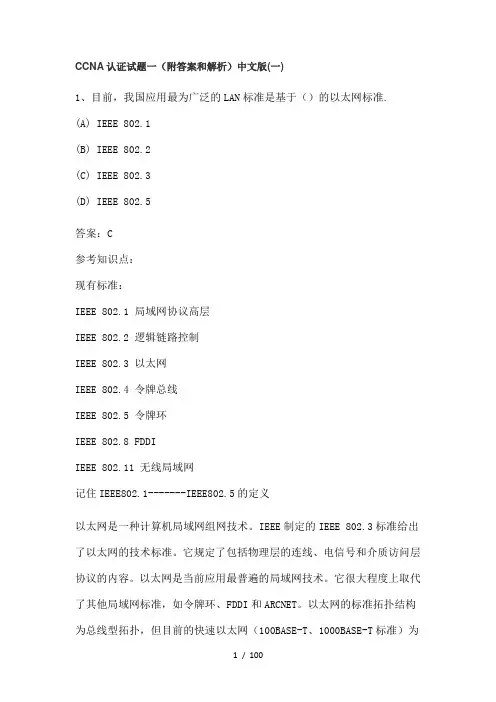
1. 1. QuestionWhat is a result of connecting two or more switches together?o The number of broadcast domains is increased.o The size of the broadcast domain is increased.o The number of collision domains is reduced.o The size of the collision domain is increased.2. 2. QuestionRefer to the exhibit. How many broadcast domains are there?CCNA1 v6.0 Chapter 8 Exam 005o 1o 2o 3o43. 3. QuestionWhat are two reasons a network administrator might want to create subnets?(Choose two.)o simplifies network designo improves network performanceo easier to implement security policieso reduction in number of routers neededo reduction in number of switches needed4. 4. QuestionRefer to the exhibit. A company uses the address block of 128.107.0.0/16 for its network. What subnet mask would provide the maximum number of equal size subnets while providing enough host addresses for each subnet in the exhibit?CCNA1 v6.0 Chapter 8 Exam 007o 255.255.255.0o 255.255.255.128o 255.255.255.192o 255.255.255.224o 255.255.255.2405. 5. QuestionRefer to the exhibit. The network administrator has assigned the LAN of LBMISS an address range of 192.168.10.0. This address range has beensubnetted using a /29 prefix. In order to accommodate a new building, the technician has decided to use the fifth subnet for configuring the newnetwork (subnet zero is the first subnet). By company policies, the router interface is always assigned the first usable host address and the workgroup server is given the last usable host address. Which configuration should be entered into the properties of the workgroup server to allow connectivity to the Internet?CCNA1 v6.0 Chapter 8 Exam 004o IP address: 192.168.10.65 subnet mask: 255.255.255.240, default gateway: 192.168.10.76o IP address: 192.168.10.38 subnet mask: 255.255.255.240, default gateway: 192.168.10.33o IP address: 192.168.10.38 subnet mask: 255.255.255.248, default gateway: 192.168.10.33o IP address: 192.168.10.41 subnet mask: 255.255.255.248, default gateway: 192.168.10.46o IP address: 192.168.10.254 subnet mask: 255.255.255.0, defaultgateway: 192.168.10.16. 6. QuestionIf a network device has a mask of /28, how many IP addresses are available for hosts on this network?o 256o 254o 62o 32o 16o 147. 7. QuestionWhich subnet mask would be used if 5 host bits are available?o 255.255.255.0o 255.255.255.128o 255.255.255.224o 255.255.255.2408. 8. QuestionHow many host addresses are available on the network 172.16.128.0 with a subnet mask of 255.255.252.0?o 510o 512o1022o 1024o 2046o 20489. 9. QuestionHow many bits must be borrowed from the host portion of an address to accommodate a router with five connected networks?o twoo threeo fouro five10. 10. QuestionA network administrator wants to have the same network mask for allnetworks at a particular small site. The site has the following networks and number of devices:IP phones – 22 addressesPCs – 20 addresses neededPrinters – 2 addresses neededScanners – 2 addresses neededThe network administrator has deemed that 192.168.10.0/24 is to be the network used at this site. Which single subnet mask would make the most efficient use of the available addresses to use for the four subnetworks?o 255.255.255.0o 255.255.255.192o 255.255.255.224o 255.255.255.240o 255.255.255.248o 255.255.255.25211. 11. QuestionA company has a network address of 192.168.1.64 with a subnet mask of255.255.255.192. The company wants to create two subnetworks that would contain 10 hosts and 18 hosts respectively. Which two networks wouldachieve that? (Choose two.)o 192.168.1.16/28o 192.168.1.64/27o 192.168.1.128/27o 192.168.1.96/28o 192.168.1.192/2812. 12. QuestionA network administrator is variably subnetting a network. The smallestsubnet has a mask of 255.255.255.248. How many usable host addresses will this subnet provide?o 4o 6o 8o 10o 1213. 13. QuestionRefer to the exhibit. Given the network address of 192.168.5.0 and a subnet mask of 255.255.255.224 for all subnets, how many total host addresses are unused in the assigned subnets?CCNA1 v6.0 Chapter 8 Exam 001o 56o 60o 64o 68o7214. 14. QuestionRefer to the exhibit. Considering the addresses already used and having to remain within the 10.16.10.0/24 network range, which subnet address could be assigned to the network containing 25 hosts?CCNA1 v6.0 Chapter 8 Exam 002o 10.16.10.160/26o 10.16.10.128/28o 10.16.10.64/27o 10.16.10.224/26o 10.16.10.240/27o 10.16.10.240/2815. 15. QuestionA network administrator needs to monitor network traffic to and fromservers in a data center. Which features of an IP addressing scheme should be applied to these devices?o random static addresses to improve securityo addresses from different subnets for redundancyo predictable static IP addresses for easier identificationo dynamic addresses to reduce the probability of duplicate addresses 16. 16. QuestionWhich two reasons generally make DHCP the preferred method of assigning IP addresses to hosts on large networks? (Choose two.)o It eliminates most address configuration errors.o It ensures that addresses are only applied to devices that require apermanent address.o It guarantees that every device that needs an address will get one.o It provides an address only to devices that are authorized to be connected to the network.o It reduces the burden on network support staff.17. 17. QuestionA DHCP server is used to assign IP addresses dynamically to the hosts on anetwork. The address pool is configured with 192.168.10.0/24. There are 3 printers on this network that need to use reserved static IP addresses from the pool. How many IP addresses in the pool are left to be assigned to other hosts?o 254o251o 252o 25318. 18. QuestionRefer to the exhibit. A company is deploying an IPv6 addressing scheme for its network. The company design document indicates that the subnet portion of the IPv6 addresses is used for the new hierarchical network design, with the s ite subsection to represent multiple geographical sites of the company, the s ub-site section to represent multiple campuses at each site, and thes ubnet section to indicate each network segment separated by routers. With such a scheme, what is the maximum number of subnets achievedper sub-site?CCNA1 v6.0 Chapter 8 Exam 003o 0o 4o16o 25619. 19. QuestionWhat is the prefix for the host address 2001:DB8:BC15:A:12AB::1/64?o 2001:DB8:BC15o 2001:DB8:BC15:Ao 2001:DB8:BC15:A:1o 2001:DB8:BC15:A:1220. 20. QuestionConsider the following range of addresses:2001:0DB8:BC15:00A0:0000::2001:0DB8:BC15:00A1:0000::2001:0DB8:BC15:00A2:0000::…2001:0DB8:BC15:00AF:0000::The prefix-length for the range of addresses is /6021. 21. QuestionMatch the subnetwork to a host address that would be included within the subnetwork. (Not all options are used.)CCNA1 v6.0 Chapter 8 Exam 0122. 22. QuestionRefer to the exhibit. Match the network with the correct IP address and prefix that will satisfy the usable host addressing requirements for each network. (Not all options are used.)CCNA1 v6.0 Chapter 8 Exam 006。
CCNA认证试题一(附答案和解析)中文版(一)1、目前,我国应用最为广泛的LAN标准是基于()的以太网标准.(A) IEEE 802.1(B) IEEE 802.2(C) IEEE 802.3(D) IEEE 802.5答案:C参考知识点:现有标准:IEEE 802.1 局域网协议高层IEEE 802.2 逻辑链路控制IEEE 802.3 以太网IEEE 802.4 令牌总线IEEE 802.5 令牌环IEEE 802.8 FDDIIEEE 802.11 无线局域网记住IEEE802.1-------IEEE802.5的定义以太网是一种计算机局域网组网技术。
IEEE制定的IEEE 802.3标准给出了以太网的技术标准。
它规定了包括物理层的连线、电信号和介质访问层协议的内容。
以太网是当前应用最普遍的局域网技术。
它很大程度上取代了其他局域网标准,如令牌环、FDDI和ARCNET。
以太网的标准拓扑结构为总线型拓扑,但目前的快速以太网(100BASE-T、1000BASE-T标准)为了最大程度的减少冲突,最大程度的提高网络速度和使用效率,使用交换机(Switch)来进行网络连接和组织,这样,以太网的拓扑结构就成了星型,但在逻辑上,以太网仍然使用总线型拓扑的C***A/CD介质访问控制方法。
电气电子工程师协会或IEEE(Institute of Electrical and Electronics Engineers)是一个国际性的电子技术及信息科学工程师的协会。
建会于1963年1月1日。
总部在美国纽约市。
在150多个国家中它拥有300多个地方分会。
目前会员数是36万。
专业上它有35个专业学会和两个联合会。
IEEE发表多种杂志,学报,书籍和每年组织300多次专业会议。
IEEE定义的标准在工业界有极大的影响。
下面列出:IEEE802.3以太网标准802.3--------- 10Base以太网标准802.3u-------- 100Base-T(快速以太网)802.3z-------- 1000Base-X(光纤吉比特以太网)802.3ab-------- 1000Base-T(双绞线吉比特以太网)2、对于这样一个地址,192.168.19.255/20,下列说法正确的是: ()(A) 这是一个广播地址(B) 这是一个网络地址(C) 这是一个私有地址(D) 地址在192.168.19.0网段上(E) 地址在192.168.16.0网段上(F) 这是一个公有地址答案:CE注:IP地址中关键是看她的主机位,将子网掩码划为二进制,1对应上面的地址是网络位,0对应的地址是主机位192.168.19.255/20划为二进制为:11000000.10101000.00010011.1111111111111111.11111111.11110000.00000000主机位变成全0表示这个IP的网络地址主机槐涑扇?表示这个IP的广播地址RFC1918文件规定了保留作为局域网使用的私有地址:10.0.0.0 - 10.255.255.255(10/8 prefix)172.16.0.0 - 172.31.255.255 (1 72.16/12 prefix)192.168.0.0 - 192.168.255.255 (192.168/16 prefix)3、Quidway系列路由器在执行数据包转发时,下列哪些项没有发生变化(假定没有使用地址转换技术)?()(A) 源端口号(B) 目的端口号(C) 源网络地址(D) 目的网络地址(E) 源MAC地址(F) 目的MAC地址答案:ABCD参考知识点:路由功能就是指选择一条从源网络到目的网络的路径,并进行数据包的转发。
思科试题中文阅读一、计算机网络基础知识1.Which of the following devices can be an administrator use to segment their Lan?() (choose all that apply)A. hubsB. repeatersC.switchesD. bridgesE.routersF. media convertersG.all of the above1.以下哪些设备可以用来分割局域网?A.集线器B。
中继器C。
交换机D。
网桥E。
路由器F。
多媒体网关G。
以上都是2.which type of cable should be used to make a connection between the Fa0/0 port on a router and the Fa0/0 port switch? ( )A. rollover cableB.console cableC. crossover cableD. straight-through cableE.serial cable2.哪种类型的电缆可以用于连接一个Fa0/0路由器端口及Fa0/0交换机端口?()A.rollover 电缆 B.console 电缆 C. crossover 电缆 D. straight-through 电缆 E.serial 电缆3.given the choices below,which address represents a unicast address? ( )A. 224.1.5.2B. FFFF.FFFF.FFFFC.192.168.24.59/30D.255.255.255.255E.172.31.128.255/183.以下的选项中,哪个代表单播地址?A. 224.1.5.2B. FFFF.FFFF.FFFFC.192.168.24.59/30D.255.255.255.255E.172.31.128.255/184.if a host on a network has the address 172.16.45.14/30,what is the address of the subnetwork to which this host belong?( )A.172.16.45.0B. 172.16.45.4C.172.16.45.8D. 172.16.45.12E.172.16.45.18 4.一台主机所在的网络地址是172.16.45.14/30,那么该主机所在的子网地址是多少?A.172.16.45.0B. 172.16.45.4C.172.16.45.8D. 172.16.45.12E.172.16.45.185.which one of the binary number ranges shown below corresponds to the value of the first octet in class B address range?()A.10000000---11101111B. 11000000----11101111C.10000000---10111111D.10000000-----11111111E.11000000---101111115.以下那个二进制数范围符合B类地址的头八位范围?A.10000000---11101111B. 11000000----11101111C.10000000---10111111D.10000000-----11111111E.11000000---101111116.how many subnetworks and hosts are avaibable per subnet if you apply a /28 mask to the 210.10.2.0 class C network?A. 30 networks and 6 hostsB. 6 networks and 30 hostsC.8 networks and 32 hostsD. 32 networks and 18 hostsE. 14 networks and 14 hostsF. none of the above6.如果你在C类网络210.10.2.0使用一个/28的掩码,可有多少子网,每个子网有多少台可用主机?A.30个子网,6台主机B.6个子网,30台主机C.8个子网,32个主机 D. 32个子网,18台主机E. 14个子网,14台主机F.以上都不对7.what is the subnet for the host IP address 172.16.210.0/22 ?( )A. 172.16.42.0B. 172.16.107.0C. 172.16.208.0D. 172.16.252.0E.172.16.254.0F.none of the above7.那个是主机ip地址172.16.210.0/22所归属的子网?A. 172.16.42.0B. 172.16.107.0C. 172.16.208.0D. 172.16.252.0E.172.16.254.0F. 以上都不对8.3 address are shown in binary form below:A. 01100100.00001010.11101011.00100111B.10101100.00010010.10011110.00001111C.11000000.10100111.10110010.01000101Below are correct ?(select three ) ( )A.address C is a public class C address .B.address C is a private class C addressC.address B is a public class B address .D.address A Is a public class A address .E.address B is a private class b address .F.address A is a private class A address.8.以下是三种二进制地址:A. 01100100.00001010.11101011.00100111B.10101100.00010010.10011110.00001111C.11000000.10100111.10110010.01000101以下哪些是正确的?(选择三项)()A.地址C是一个公有C类地址B.地址C是一个私有C类地址C.地址B是一个公有B类地址D.地址A是一个公有A类地址E.地址B是一个私有B类地址F.地址A是一个私有A类地址9.You have a network that supports VLAN and you need to reduce IP address waste in your point to point W AN links .which of the masks below would you useb? ( )A. /38B. /30C. /27D./23E. /18F./329.你有一个支持VLAN的网络,你需要接入W AN时减少IP地址浪费,你将使用以下哪个掩码?A. /38B. /30C. /27D./23E. /18F./32二:路由器基本知识1.Which of the commands below would you enter, if you wanted to see the configuration register of your router ? ( )A. show bootB. show flashC. show registerD. show versionE. show config 1.如果你想看路由器的配置注册信息,你应该输入以下哪个命令?A. show bootB. show flashC. show registerD. show versionE. show config 2.Y ou attempt to telnet from the router R1 to Router R2 192.1.2.65 . the telnet connection is unsuccessful .however, a ping to 192.1.2.65 is successful.What could cause this problem (select two ) ( )A.PPP authentication configuration problem.B.IP address / subnet mask configuration errorC.Access control list filteringD.Defective serial cableE.No clock rate on interface s0 on R2F.Missing VTY password2.你试图从路由器R1远程登陆到路由器R2 R2 192.1.2.65,远程登陆连接不成功,但是PING192.1.2.65成功。

CCNA考试题库中英文翻译版及答案1[1]1. What are two reasons that a network administrator would use access lists? (Choose two.)1.出于哪两种理由,网络管理员会使用访问列表?A. to control vty access into a routerA.控制通过VTY访问路由器B. to control broadcast traffic through a routerB.控制广播流量穿越路由器2.一个默认的帧中继WAN被分类为哪种物理网络类型?A. point-to-pointA.点到点B. broadcast multi-accessB.广播多路访问C. nonbroadcast multi-accessC.非广播多路访问D. nonbroadcast multipointD.非广播多点E. broadcast point-to-multipointE.广播点到多点Answer: C3. A single 802.11g access point has been configured and installed in the center of a squarA few wireless users are experiencing slow performance and drops while most users are oat peak efficiency. What are three likely causes of this problem? (Choose three.)3.一个802.11接入点被部署在一个方形办公室的中央,当大多数用户在大流量传输数一些无线用户发现无线网络变得缓慢和出现丢包A. mismatched TKIP encryptionB. null SSIDC. cordless phonesD. mismatched SSIDE. metal file cabinetsF. antenna type or directionAnswer: CEF4. Refer to the exhibit. How many broadcast domains exist in the exhibited topology?根据下图,图中的拓扑中存在多少个广播域?A. one A.1B. two B.2C. three C.3D. four D.4E. five E.5F. six F.6Answer: C5. Refer to the exhibit. What two facts can be determined from the WLAN diagram? (Choose two.)5.根据下图,WLAN diagram决定了哪两个事实A. The area of overlap of the two cells represents a basic service set (BSS).A. 两个 cells的overlap的区域描述了一个basic service setB. The network diagram represents an extended service set (ESS).B. 网络描述了一个extended service setC. Access points in each cell must be configured to use channel 1.C. 再每个CELL中的AP必须被配置成使用channel 1D. The area of overlap must be less than 10% of the area to ensure connectivity.D. 为了确保连通性,重叠区域必须小于10%E. The two APs should be configured to operate on different channels.E. 两个访问点应该被配置成工作在不同的频道Answer: BE6. The command frame-relay map ip 10.121.16.8 102 broadcast was entered on the router.Which of the following statements is true concerning this command?6.路由器上输入命令frame-relay map ip 10.121.16.8 102 broadcast,以下选项正确的是?A. This command should be executed from the global configuration mode.A.该命令应该在全局配置模式下被执行B. The IP address 10.121.16.8 is the local router port used to forward data.B.IP地址10.121.16.8是本地路由器用来转发数据的接口C. 102 is the remote DLCI that will receive the information.C.102是远端的DLCI它将接受信息。
1. Refer to the exhibit. What could bepossible causes for the "Serial0/0 is down"interfacestatus? (Choosetwo.)A. A Layer 1 problem exists.B. The bandwidth is set too low.C. A protocol mismatch exists.D. An incorrect cable is being used.E. There is an incorrect IP address on the Serial 0/0 interface.Answer: AD2. Before installing a new, upgraded version of the IOS, what should be checked on the router, andwhichcommand should be used to gather this information? (Choose two.)A. the amount of available ROMB. the amount of available flash and RAM memoryC. the version of the bootstrap software present on the routerD. show versionE. show processesF. show running-configAnswer: BD3. Refer to the exhibit. Which two statements are true about interVLAN routing in the topologythat is shownin the exhibit? (Choose two.)中国思科华为3COM 网络技术发布A. Host E and host F use the same IP gateway address.B. Router1 and Switch2 should be connected via a crossover cable.C. Router1 will not play a role in communications between host A and hostD.D. The FastEthernet 0/0 interface on Router1 must be configured with subinterfaces.E. Router1 needs more LAN interfaces to accommodate the VLANs that are shown in the exhibit.F. The FastEthernet 0/0 interface on Router1 and Switch2 trunk ports must be configured using thesameencapsulation type.Answer: DF4. Refer to the exhibit. Which two statements are true about the loopback address that isconfigured onRouterB? (Choose two.)A. It ensures that data will be forwarded by RouterB.B. It provides stability for the OSPF process on RouterB.中国思科华为3COM 网络技术发布C. It specifies that the router ID for RouterB should be 10.0.0.1.D. It decreases the metric for routes that are advertised from RouterB.E. It indicates that RouterB should be elected the DR for the LAN.Answer: BC5. A network administrator is explaining VTP configuration to a new technician. What should thenetworkadministrator tell the new technician about VTP configuration? (Choose three.)A. A switch in the VTP client mode cannot update its local VLAN database.B. A trunk link must be configured between the switches to forward VTP updates.C. A switch in the VTP server mode can update a switch in the VTP transparent mode.D. A switch in the VTP transparent mode will forward updates that it receives to other switches.E. A switch in the VTP server mode only updates switches in the VTP client mode that have a higherVTPrevision number.F. A switch in the VTP server mode will update switches in the VTP client mode regardless of the configured VTP domain membership.Answer: ABD6. Which two locations can be configured as a source for the IOS image in the boot system command?(Choose two.)A. RAMB. NVRAMC. flash memoryD. HTTP serverE. TFTP serverF. TelnetserverAnswer: CE7. What are two reasons a network administrator would use CDP? (Choose two.)A. to verify the type of cable interconnecting two devicesB. to determine the status of network services on a remote deviceC. to obtain VLAN information from directly connected switchesD. to verify Layer 2 connectivity between two devices when Layer 3 failsE. to obtain the IP address of a connected device in order to telnet to the deviceF. to determine the status of the routing protocols between directly connected routersAnswer: DE中国思科华为3COM 网络技术发布8. Refer to the exhibit. Both switches are using a default configuration. Which two destinationaddresses willhost 4 use to send data to host 1? (Choose two.)A. the IP address of host 1B. the IP address of host 4C. the MAC address of host 1D. the MAC address of host 4E. the MAC address of the Fa0/0 interface of the R1 routerF. the MAC address of the Fa0/1 interface of the R1 routerAnswer: AF9. Refer to the exhibit. The router has been configured with these commands:hostname Gatewayinterface FastEthernet 0/0ip address 198.133.219.14 255.255.255.248no shutdowninterface FastEthernet 0/1ip address 192.168.10.254 255.255.255.0no shutdowninterface Serial 0/0ip address 64.100.0.2 255.255.255.252no shutdownip route 0.0.0.0 0.0.0.0 64.100.0.1What are the two results of this configuration? (Choose two.)中国思科华为3COM 网络技术发布A. The default route should have a next hop address of 64.100.0.3.B. Hosts on the LAN that is connected to FastEthernet 0/1 are using public IP addressing.C. The address of the subnet segment with the WWW server will support seven more servers.D. The addressing scheme allows users on the Internet to access the WWW server.E. Hosts on the LAN that is connected to FastEthernet 0/1 will not be able to access the Internetwithoutaddress translation.Answer: DE10. A company is installing IP phones. The phones and office computers connect to the same device.Toensure maximum throughput for the phone data, the company needs to make sure that the phonetraffic ison a different network from that of the office computer data traffic. What is the best networkdevice to whichto directly connect the phones and computers, and what technology should be implemented on thisdevice?(Choose two.)A. hubB. routerC. switchD. STPE. subinterfacesF. VLANAnswer: CF11. What are two benefits of using VTP in a switching environment? (Choose two.)中国思科华为3COM 网络技术发布A. It allows switches to read frame tags.B. It allows ports to be assigned to VLANs automatically.C. It maintains VLAN consistency across a switched network.D. It allows frames from multiple VLANs to use a single interface.E. It allows VLAN information to be automatically propagated throughout the switching environment.Answer: CE12. Which two statements are true about the command ip route172.16.3.0 255.255.255.0 192.168.2.4?(Choose two.)A. It establishes a static route to the 172.16.3.0 network.B. It establishes a static route to the 192.168.2.0 network.C. It configures the router to send any traffic for an unknown destination to the 172.16.3.0network.D. It configures the router to send any traffic for an unknown destination out the interface withthe address192.168.2.4.E. It uses the default administrative distance.F. It is a route that would be used last if other routes to the same destination exist.Answer: AE13. What are two advantages of Layer 2 Ethernet switches over hubs? (Choose two.)A. decreasing the number of collision domainsB. filtering frames based on MAC addressesC. allowing simultaneous frame transmissionsD. increasing the size of broadcast domainsE. increasing the maximum length of UTP cabling between devicesAnswer: BC14. Refer to the exhibit. A network associate needs to configure the switches and router in thegraphic sothat the hosts in VLAN3 and VLAN4 can communicate with the enterprise server in VLAN2. Which twoEthernet segments would need to be configured as trunk links? (Choose two.)中国思科华为3COM 网络技术发布A. AB. BC. CD. DE. EF. FAnswer: CF15. Which two values are used by Spanning Tree Protocol to elect a root bridge? (Choose two.)A. amount of RAMB. bridge priorityC. IOS versionD. IP addressE. MAC addressF. speed of the linksAnswer: BE16. Refer to the exhibit. Assume that the routing protocol referenced in each choice below isconfigured withits default settings and the given routing protocol is running onall the routers. Which twoconditionalstatements accurately state the path that will be chosen between networks 10.1.0.0 and 10.3.2.0for therouting protocol mentioned? (Choose two.)中国思科华为3COM 网络技术发布A. If OSPF is the routing protocol, the path will be from R1 to R3to R4 to R5.B. If OSPF is the routing protocol, the path will be from R1 to R2to R5.C. If OSPF is the routing protocol, the path will be from R1 to R5.D. If RIPv2 is the routing protocol, the path will be from R1 to R3to R4 to R5.E. If RIPv2 is the routing protocol, the path will be from R1 to R5.Answer: AE17. Refer to the exhibit. A network administrator is adding two new hosts to SwitchA. Which threevaluescould be used for the configuration of these hosts? (Choose three.)A. host A IP address: 192.168.1.79。

CCNA认证试题一(附答案和解析)中文版(一)CCNA1 2007-09-30 15:49:59 阅读139 评论0 字号:大中小订阅1、目前,我国应用最为广泛的LAN标准是基于()的以太网标准.(A) IEEE 802.1(B) IEEE 802.2(C) IEEE 802.3(D) IEEE 802.5答案:C参考知识点:现有标准:IEEE 802.1 局域网协议高层IEEE 802.2 逻辑链路控制IEEE 802.3 以太网IEEE 802.4 令牌总线IEEE 802.5 令牌环IEEE 802.8 FDDIIEEE 802.11 无线局域网记住IEEE802.1-------IEEE802.5的定义以太网是一种计算机局域网组网技术。
IEEE制定的IEEE 802.3标准给出了以太网的技术标准。
它规定了包括物理层的连线、电信号和介质访问层协议的内容。
以太网是当前应用最普遍的局域网技术。
它很大程度上取代了其他局域网标准,如令牌环、FDDI和ARCNET。
以太网的标准拓扑结构为总线型拓扑,但目前的快速以太网(100BASE-T、1000BASE-T标准)为了最大程度的减少冲突,最大程度的提高网络速度和使用效率,使用交换机(Switch)来进行网络连接和组织,这样,以太网的拓扑结构就成了星型,但在逻辑上,以太网仍然使用总线型拓扑的C***A/CD介质访问控制方法。
电气电子工程师协会或IEEE(Institute of Electrical and Electronics Engineers)是一个国际性的电子技术与信息科学工程师的协会。
建会于1963年1月1日。
总部在美国纽约市。
在150多个国家中它拥有300多个地方分会。
目前会员数是36万。
专业上它有35个专业学会和两个联合会。
IEEE发表多种杂志,学报,书籍和每年组织300多次专业会议。
IEEE 定义的标准在工业界有极大的影响。
下面列出:IEEE802.3以太网标准802.3--------- 10Base以太网标准802.3u-------- 100Base-T(快速以太网)802.3z-------- 1000Base-X(光纤吉比特以太网)802.3ab-------- 1000Base-T(双绞线吉比特以太网)2、对于这样一个地址,192.168.19.255/20,下列说法正确的是: ()(A) 这是一个广播地址(B) 这是一个网络地址(C) 这是一个私有地址(D) 地址在192.168.19.0网段上(E) 地址在192.168.16.0网段上(F) 这是一个公有地址答案:CE注:IP地址中关键是看她的主机位,将子网掩码划为二进制,1对应上面的地址是网络位,0对应的地址是主机位192.168.19.255/20划为二进制为:11000000.10101000.00010011.1111111111111111.11111111.11110000.00000000主机位变成全0表示这个IP的网络地址主机槐涑扇?表示这个IP的广播地址RFC1918文件规定了保留作为局域网使用的私有地址:10.0.0.0 - 10.255.255.255 (10/8 prefix)172.16.0.0 - 172.31.255.255 (172.16/12 prefix)192.168.0.0 - 192.168.255.255 (192.168/16 prefix)3、Quidway系列路由器在执行数据包转发时,下列哪些项没有发生变化(假定没有使用地址转换技术)?()(A) 源端口号(B) 目的端口号(C) 源网络地址(D) 目的网络地址(E) 源MAC地址(F) 目的MAC地址答案:ABCD参考知识点:路由功能就是指选择一条从源网络到目的网络的路径,并进行数据包的转发。
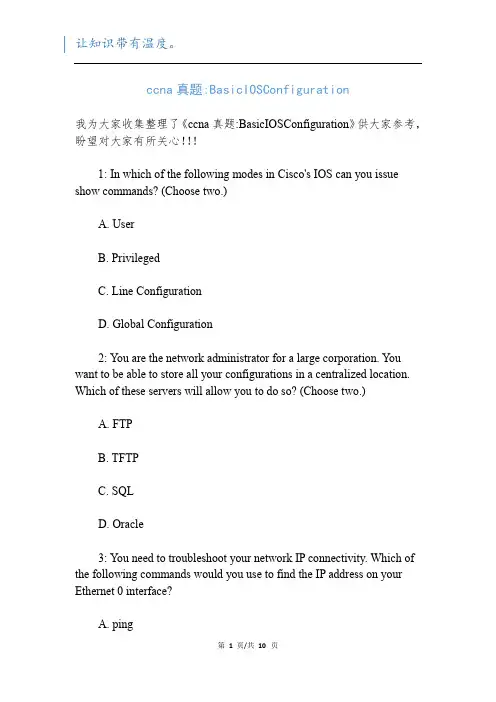
ccna真题:BasicIOSConfiguration我为大家收集整理了《ccna真题:BasicIOSConfiguration》供大家参考,盼望对大家有所关心!!!1: In which of the following modes in Cisco's IOS can you issue show commands? (Choose two.)A. UserB. PrivilegedC. Line ConfigurationD. Global Configuration2: You are the network administrator for a large corporation. You want to be able to store all your configurations in a centralized location. Which of these servers will allow you to do so? (Choose two.)A. FTPB. TFTPC. SQLD. Oracle3: You need to troubleshoot your network IP connectivity. Which of the following commands would you use to find the IP address on your Ethernet 0 interface?A. ping第1页/共10页B. IPConfigC. tracerouteD. Show interface Ethernet 04: Which command would you use at the CLI in User mode to enter Privileged EXEC mode?A. PrivilegeB. AdminC. EnableD. Disable5: You have just received 14 Catalyst switches for your network. You would like to install these switches into your production network to provide separate collision domains for each of the connected devices. What configuration is required to provide this functionality?A. No configuration is required.B. You must set up an IP address on the switch.C. You must configure unique VLANs on the switches.D. You must install the Cisco IOS.6: Which of the following prompts indicates your router is in Privileged EXEC mode?第2页/共10页A. Router>B. Router#C. Router then press XB. Ctrl+EscC. Ctrl+ZD. Type exit32: When you are establishing a PPP link, which of the following would be negotiated? (Choose three.)A. IPCPB. CHAPC. UDPD. Q.931E. Multilink Protocol33: Which of the following commands returns your router to a previously saved configuration?A. Router1#setupB. Router1#copy running-config startup-configC. Router1#copy startup-config running-config第3页/共10页D. Router1#reload34: You are in Interface Configuration mode and would like to recall the last command you typed, move your cursor to the beginning of the command line, and type no before the recalled command. You notice your up- and down-arrow keys do not function because you are using an older terminal program. What command combinations could you use to recall the previous command and move your cursor to the beginning of the line?Press Ctrl+P to recall the previous command and Ctrl+A to move to the beginning of the command line.Press Ctrl+L to recall the previous command and Ctrl+B to move to the beginning of the command line.Press Ctrl+D to recall the previous command and Ctrl+A to move to the beginning of the command line.Press Ctrl+E to recall the previous command and Ctrl+A to move to the beginning of the command line.35: What is the baud rate setting for your terminal emulation program so that you can communicate through your console port?A. 2400B. 9600C. 14400D. 3630036: What must be configured on a Cisco device to enable Telnet functionality?第4页/共10页A. A management IP addressB. SNMPC. CDPD. vty ports37: You are configuring your Cisco router and need to go back to User EXEC mode. What command takes you back to User EXEC mode?A. Router1#enableB. Router1#exitC. Router1#configure terminalD. Router1#disable38: Which of the following commands places an IP address on your Catalyst switch?A. Switch1#ip address 10.2.2.2 255.255.255.0B. Switch1(config)#Set IP 10.2.2.2 255.255.255.0C. Switch1(config-vlan)#ip address 10.2.2.2D. Switch1(config-vlan)#ip address 10.2.2.2 255.255.255.039: Which of the following commands would you enter to receive this output shown in the figure above?第5页/共10页A. Router1#show NVRAMB. Router1#show FlashC. Router1#show Flash-MemD. Router1#show Version40: Your senior network administrator is unable to telnet to a Catalyst switch because she forgot the IP address. You have physical access and are able to console in. Which of the following commands is the best to get the IP address on the switch?A. Switch1#show ipB. Switch1#show vlan 1C. Switch1#show ip routeD. Switch1#show interface vlan141: You have powered up your Cisco 3640 router. The first thing you see is this output. Which of the following statements about this screen is accurate (see figure above)?A. Your IOS is corrupt and unable to load.B. Your configuration is missing parameters.C. You do not have a configuration saved in NVRAM.D. You have typed setup in the Privileged mode.42: You type in a command and are shown the following output:% Ambiguous command: "show con"第6页/共10页What does this mean?A. You did not enter enough characters for your device to recognize the command.B. You did not enter all the keywords or values required by this command.C. You entered the command incorrectly.D. Context-sensitive help is unable to help you with this command.43: You are typing a command into the Cisco IOS. It is more than one terminal line long. What will the IOS do?A. The router automatically moves the cursor to the next line and uses a caret (^) to indicate the line break.B. The router truncates the command because commands longer than one line are not allowed.C. The router automatically scrolls the line to the left and uses a dollar sign ($) to indicate that there is text to the left of the $.D. The router shortens all the commands to squeeze the command on to the screen.44: You want to change the size of the command history buffer. Which of the following commands will set it permanently to 100?A. Router1#terminal history 100B. Router1#history size 100第7页/共10页C. Router1(config)#terminal history 100D. Router1(config-line)#history size 10045: You have configured a description on your serial interfaces. Which of the following commands displays the description? (Choose two.)A. Show running-configB. Show flashC. Show interfacesD. Show ip protocols46: You are typing commands into your Cisco IOS on your 3640 router. However, your typing is consistently interrupted by console messages, forcing you to retype. Which of the following commands forces the IOS to retype your original input after it displays the console message?A. Exec-timeoutB. Logging synchronousC. Line consoleD. Exec message readout47: You are configuring a router and issue the command interface ethernet 1/0/0. What do the numbers represent?A. Slot/port/interface第8页/共10页B. Slot/interface/portC. Port/slot/port numberD. Slot/port adapter/port number48: Which of the following commands correctly sets the physical speed of a serial interface to 64Kbps?A. Router1(config-if)#bandwidth 64B. Router1(config-if)#bandwidth 64000C. Router1(config-if)#clockrate 64D. Router1(config-if)#clockrate 6400049: In what mode do you use the encapsulation command?A. Interface Configuration modeB. Sub-interface Configuration modeC. User modeD. Privileged mode50: You are configuring your router, and your boss happens to look over your shoulder as you type a show running-config command. She sees one of the lines that says password 7 14361F009A056E7D and asks what this means. What do you tell her?A. It is the actual password.第9页/共10页B. It is the result of a service password-encryption command.C. The console output made a mistake.D. It is the result of an enable secret command.文档内容到此结束,欢迎大家下载、修改、丰富并分享给更多有需要的人。
1请参见图示。
下列哪三种说法正确描述了图中所示的网络设计?(选择三项。
)136Refer to the exhibit. Which three statements describe the network design shown in the exhibit?此设计不易扩展。
This design will not scale easily.路由器将VLAN合并到单个广播域内。
The router merges the VLANs into a single broadcast domain.此设计使用了一些不必使用的交换机端口或路由器端口。
This design uses more switch and router ports than are necessary.此设计超出了交换机可连接的VLAN的最大数量。
This design exceeds the maximum number of VLANs that can be attached to a switch.此设计需要在交换机与路由器之间的链路上使用ISL或802.1q协议。
This design requires the use of the ISL or 802.1q protocol on the links between the switch and the router.如果交换机与路由器之间的物理接口可以正常工作,则不同VLAN中的设备可通过路由器通信。
If the physical interfaces between the switch and router are operational, the devices on the different VLANs can communicate through the router.2、某路由器有两个快速以太网接口,需要连接到本地网络中的四个VLAN。
在不降低网络必要性能的情况下,如何才能使用数量最少的物理接口达到此要求?1A router has two FastEthernet interfaces and needs to connect to four VLANs in the local network. How can this be accomplished using the fewest number of physical interfaces without unnecessarily decreasing network performance?实施单臂路由器配置。
25. QuestionWhat is the binary equivalent of the decimal number 232?o 11101000o 11000110o 10011000o 1111001026. QuestionWhat is the decimal equivalent of the binary number 10010101?o149o 157o 168o 1921. QuestionHow many bits are in an IPv4 address?o32o 64o 128o 2562. QuestionWhich two parts are components of an IPv4 address? (Choose two.)o subnet portiono network portiono logical portiono host portiono physical portiono broadcast portion3. QuestionWhat does the IP address 172.17.4.250/24 represent?o network addresso multicast addresso host addresso broadcast address4. QuestionWhat is the purpose of the subnet mask in conjunction with an IP address?o to uniquely identify a host on a networko to identify whether the address is public or privateo to determine the subnet to which the host belongso to mask the IP address to outsiders5. QuestionWhat subnet mask is represented by the slash notation /20?o 255.255.255.248o 255.255.224.0o 255.255.240.0o 255.255.255.0o 255.255.255.1926. QuestionA message is sent to all hosts on a remote network. Which type of message isit?o limited broadcasto multicasto directed broadcasto unicast7. QuestionWhat are three characteristics of multicast transmission? (Choose three.)o The source address of a multicast transmission is in the range of 224.0.0.0 to 224.0.0.255.o A single packet can be sent to a group of hosts.o Multicast transmission can be used by routers to exchange routing information.o The range of 224.0.0.0 to 224.0.0.255 is reserved to reach multicast groups on a local network.o Computers use multicast transmission to request IPv4 addresses.o Multicast messages map lower layer addresses to upper layer addresses.8. QuestionWhich three IP addresses are private ? (Choose three.)o 10.1.1.1o 172.32.5.2o 192.167.10.10o 172.16.4.4o 192.168.5.5o 224.6.6.69. QuestionWhich two IPv4 to IPv6 transition techniques manage the interconnection of IPv6 domains? (Choose two.)o trunkingo dual stacko encapsulationo tunnelingo multiplexing10. QuestionWhich of these addresses is the shortest abbreviation for the IP address:3FFE:1044:0000:0000:00AB:0000:0000:0057?o 3FFE:1044::AB::57o 3FFE:1044::00AB::0057o 3FFE:1044:0:0:AB::57o 3FFE:1044:0:0:00AB::0057o 3FFE:1044:0000:0000:00AB::57o 3FFE:1044:0000:0000:00AB::005711. QuestionWhat type of address is automatically assigned to an interface when IPv6 is enabled on that interface?o global unicasto link-localo loopbacko unique local12. QuestionWhat are two types of IPv6 unicast addresses? (Choose two.)o multicasto loopbacko link-localo anycasto broadcast13. QuestionWhat are three parts of an IPv6 global unicast address? (Choose three.)o an interface ID that is used to identify the local network for a particular hosto a global routing prefix that is used to identify the network portion of the address that has been provided by an ISPo a subnet ID that is used to identify networks inside of the local enterprise siteo a global routing prefix that is used to identify the portion of the network address provided by a local administratoro an interface ID that is used to identify the local host on the network14. QuestionAn administrator wants to configure hosts to automatically assign IPv6 addresses to themselves by the use of Router Advertisement messages, but also to obtain the DNS server address from a DHCPv6 server. Which address assignment method should be configured?o SLAACo stateless DHCPv6o stateful DHCPv6o RA and EUI-6415. QuestionWhich protocol supports Stateless Address Autoconfiguration (SLAAC) for dynamic assignment of IPv6 addresses to a host?o ARPv6o DHCPv6o ICMPv6o UDP16. QuestionWhich two things can be determined by using the ping command? (Choose two.)o the number of routers between the source and destination deviceo the IP address of the router nearest the destination deviceo the average time it takes a packet to reach the destination and for theresponse to return to the sourceo the destination device is reachable through the networko the average time it takes each router in the path between source and destination to respond17. QuestionWhat is the purpose of ICMP messages?o to inform routers about network topology changeso to ensure the delivery of an IP packeto to provide feedback of IP packet transmissionso to monitor the process of a domain name to IP address resolution 18. QuestionWhat is indicated by a successful ping to the ::1 IPv6 address?o The host is cabled properly.o The default gateway address is correctly configured.o All hosts on the local link are available.o The link-local address is correctly configured.o IP is properly installed on the host.19. QuestionA user is executing a tracert to a remote device. At what point would a router,which is in the path to the destination device, stop forwarding the packet?o when the router receives an ICMP Time Exceeded messageo when the RTT value reaches zeroo when the host responds with an ICMP Echo Reply messageo when the value in the TTL field reaches zeroo when the values of both the Echo Request and Echo Reply messages reach zero20. QuestionWhat field content is used by ICMPv6 to determine that a packet has expired?o TTL fieldo CRC fieldo Hop Limit fieldo Time Exceeded field21. QuestionFill in the blank.The decimal equivalent of the binary number 10010101is 149 .22. QuestionFill in the blank.The binary equivalent of the decimal number 232 is 1110100023. QuestionFill in the blank.What is the decimal equivalent of the hex number 0x3F? 63。
这是我学习过程中遇见的ccna试题,中文一份,英文一份,很经典呀。
1 技术人员需要为某幢已经布设有线以太网络的大厦提供无线连接。
哪三个因素会影响需要的接入点数目?(选择三项。
)大厦的规模大厦中实体内墙的数目多个办公室中有微波炉无线网络中使用的加密方法Windows 和Appletalk 操作系统的同时使用AP 中短波或红外线的使用2 下列关于无线网桥的陈述,哪一项是正确的?通过无线链路连接两个网络连接无线局域网的固定设备允许无线客户端连接到有线网络增强无线信号的强度3 接入点默认使用哪一类身份验证?开放式PSKWEPEAP4请参见图示。
在Linksys 集成路由器的Wireless 菜单选项中,Network Mode 选项Mixed 是什么意思?路由器支持加密和身份验证。
路由器支持有线和无线两种连接。
路由器支持802.11b、802.11g 和802.11n 设备。
路由器支持通过红外和无线电射频连接。
5 接入点可以使用哪两种身份验证方法?(选择两项。
)WEPWPAEAPASCII预共享密钥6 哪项接入点功能允许网络管理员定义可以进入无线网络的数据类型?加密黑客攻击拦截通信过滤MAC 地址过滤身份验证7 下列关于服务集标识符(SSID) 的陈述中,哪两个是正确的?(选择两项。
)标识无线设备所属的WLAN是一个包含32 个字符的字符串,不区分大小写负责确定信号强度同一WLAN 中的所有无线设备必须具有相同的SSID用于加密通过无线网络发送的数据8请参见图示。
在Linksys 集成路由器的Wireless 菜单中,哪个配置选项可用于让附近的客户端知道接入点的存在。
Network ModeNetwork Name (SSID)Radio BandWide ChannelStandard ChannelSSID Broadcast9 下列哪个术语准确描述了为防止黑客读取截取到的数据而进行的无线数据编码?地址过滤身份验证广播加密密码短语编码10 两种WEP 密钥长度分别是多少?(选择两项。
1请参见图示。
该网络中所有交换机的MAC表均为空。
而且,该网络中的交换机已禁用STP。
该网络中会如何处理主机PC1所发送的广播帧?2Refer to the exhibit. All switches in the network have empty MAC tables. STP has been disabled on the switches in the network. How will a broadcast frame that is sent by host PC1 be handled on the network?交换机SW1会拦截广播并丢弃该帧。
Switch SW1 will block the broadcast and drop the frame 交换机SW1会将广播从除源端口之外的所有交换机端口转发出去。
这会在网络中造成无限循环。
Switch SW1 will forward the broadcast out all switch ports, except the originating port. This will generate an endless loop in the network.交换机SW1会将广播从除源端口之外的所有交换机端口转发出去。
而该网络中的所有主机则通过向主机PC1发送单播帧来回应。
Switch SW1 will forward the broadcast out all switch ports, except the originating port. All hosts in the network will reply with a unicast frame sent to host PC1交换机SW1会将该通信作为单播帧从除源端口之外的所有交换机端口转发出去。
而该网络中的所有主机则通过向交换机SW1发送单播帧来回应。
Switch SW1 will forward the traffic out all switch ports except the originating port as a unicast frame. All hosts in the network will reply with a unicast frame sent to switch SW1.2请参见图示。
CCNA第二学期《Final Examinnation》英文A卷1 What are two functions of a router? (Choose two.)It forwards data packets toward their destination.It forwards the packet to the destination if the TTL value is 0.It changes the destination IP address of data packets before forwarding them to an exit interface. It determines the best path based on the destination MAC address.It acts as an intersection between multiple IP networks.2 Which router component contains a scaled-down version of the IOS that can be used to reload a complete version of the IOS in the event that the IOS becomes damaged or corrupted?ROMFlashSDRAMNVRAM3 Using default settings, what is the next step in the router boot sequence after the IOS loads from flash?Perform the POST routine.Search for a backup IOS in ROM.Load the bootstrap program from ROM.Load the running-config file from RAM.Locate and load the startup-config file from NVRAM.4Refer to the exhibit. How many routes are ultimate routes?34575Refer to the exhibit. Which path will traffic from the 172.16.1.0/24 network take to get to the 10.0.0.0/24 network?ADCABCIt will load balance the traffic between ADC and ABCIt will send the traffic via ABC, and will use ADC as a backup path only when ABC fails.6Refer to the exhibit. Routers R1 and R3 use different routing protocols with default administrative distance values. All devices are properly configured and the destination network is advertised by both protocols.Which path will be used to transmit the data packets from PC1 to PC2?The packets will travel via R2-R1.The packets will travel via R2-R3.The traffic will be load-balanced between two paths — via R2-R1 and via R2-R3.The packets will travel via R2-R3, and the other path via R2-R1 will be retained as the backup path.7Refer to the exhibit. The network is configured for OSPF routing with default settings. The bandwidths have been configured correctly for each link. If the T1 link between router A and router E fails, what path will a packet from router A take to reach the LAN attached to router F when the network has converged?A, B, C, FA, B, C, E, FA, D, G, E, FA, D, G, H, F8 In a lab test environment, a router has learned about network 172.16.1.0 through four different dynamic routing processes. Which route will be used to reach this network?D 172.16.1.0/24 [90/2195456] via 192.168.200.1, 00:00:09, Serial0/0/0O 172.16.1.0/24 [110/1012] via 192.168.200.1, 00:00:22, Serial0/0/0R 172.16.1.0/24 [120/1] via 192.168.200.1, 00:00:17, Serial0/0/0I 172.16.1.0/24 [100/1192] via 192.168.200.1, 00:00:09, Serial0/0/09 Which two statements are true for link-state routing protocols? (Choose two.)Routers that run a link-state protocol can establish a complete topology of the network. Routers in a multipoint network that run a link-state protocol can exchange routing tables. Routers use only hop count for routing decisions.The shortest path first algorithm is used.Split horizon is used to avoid routing loops.10Refer to the exhibit. Which option will provide the configuration that is needed for router R1 to dynamically learn routes to the 192.168.100.16/28, 192.168.100.32/28, and 192.168.100.48/28 subnetworks?with static routeswith a routed protocolwith a routing protocolwith directly connected routes11Refer to the exhibit. What is the meaning of the highlighted value 120?It is the metric that is calculated by the routing protocol.It is the value that is used by the DUAL algorithm to determine the bandwidth for the link.It is the administrative distance of the routing protocol.It is the hold-down time, measured in seconds, before the next update.12 Which statement is true about the metrics used by routing protocols?A metric is a value used by a particular routing protocol to compare paths to remote networks.A common metric is used by all routing protocols.The metric with the highest value is installed in the routing table.The router may use only one parameter at a time to calculate the metric.13 Which routing protocol by default uses bandwidth and delay to calculate the metric of a route? RIPv1RIPv2OSPFEIGRP14 Which three routing metrics are correctly defined? (Choose three.)delay - the link speedreliability - the error rate on a linkload - the amount of traffic on a linkcost - the value to indicate preference for a routehop count - the path selected with the highest bandwidthbandwidth - the amount of time it takes a packet to travel a link15 Which two statements about routing protocols are accurate? (Choose two.)OSPF supports VLSM.RIPv1 supports VLSM.RIPv2 does not have a hop count limit.EIGRP supports discontiguous network designs.RIPv2 does not support discontiguous network designs.16Refer to the exhibit. A device is required to complete the connection between router R1 and the WAN. Which two devices can be used for this? (Choose two.)a CSU/DSU devicea modeman Ethernet switcha huba bridge17 When connecting two devices, which situation would normally require the use of a crossover cable?connecting a host to a switchconnecting a switch to a routerconnecting a switch to a switchconnecting a host to a router console port18Refer to the exhibit. A network administrator has run the show interface command. The output of this command is displayed. What is the first step that is required to make this interface operational?Switch the cable with a known working cable.Issue the no shutdown command on the interface.Configure the interface as a loopback interface.Set the encapsulation for the interface.19 Which port should a terminal emulator be connected to in order to access a router without network connectivity?T1serialconsoleFastEthernet20 Which router mode is accessed by entering the enable command?user EXECprivileged EXECglobal configurationinterface configuration21Refer to the exhibit. When a static IP address is being configured on the host, what address shouldbe used for the default gateway?10.1.1.110.1.1.2172.16.1.1192.168.1.122Refer to the exhibit. The show cdp neighbors command was run on one of the devices as shown. Based on this information, which two facts can be determined? (Choose two.)The command was run on the router.ABCD is a non- CISCO device.Layer 3 connectivity between two devices exists.ABCD supports routing capability.ABCD is connected to the Fa0/0 interface of the neighboring device.23Refer to the exhibit. Which statement is true about the Ethernet interfaces shown in the network?A frame leaves interface Fa0/0 of R1 with the source MAC address as 000C.3010.9260.Hosts on 10.1.1.0/24 will use 172.16.3.1/24 as their default gateway.A packet will not be forwarded between R1 and R2 until the no shutdown command is issued on the Fa0/0 interface of R1.The Fa0/0 interface of R2 could be configured with the IP address 172.16.4.1/24 and still have connectivity on this link.24Refer to the exhibit. Which solution provides the most efficient use of router resources for forwarding traffic between BR and HQ?RIPRIPv2EIGRPstatic routes25Refer to the exhibit. Pings are failing between HostA and HostB. The network administrator discovers that Router1 does not have a route to the 172.16.0.0 network. Assuming Router2 is configured correctly, which two static routes could be configured on Router1 to enable Host A to reach network 172.16.0.0? (Choose two.)ip route 172.16.0.0 255.255.0.0 S0/0ip route 172.16.0.0 255.255.0.0 S0/1ip route 172.16.0.0 255.255.0.0 192.168.0.1ip route 172.16.0.0 255.255.0.0 192.168.0.2ip route 192.168.0.1 172.16.0.0 255.255.0.0 S0/0ip route 192.168.0.1 172.16.0.0 255.255.0.0 S0/126Refer to the exhibit. How was the OSPF default gateway entry for R2 determined?Default routes are automatically injected by OSPF into all advertisements.A static default gateway route is defined in the configuration of R2.The default-information originate command is applied on R1.The ISP defines the gateway of last resort and automatically passes it to R1 and R2.The ip default-gateway command is applied on R2.27Refer to the exhibit. On the basis of the show running-config output, which option correctly reflects the routes that will be listed in the R2 routing table?答案:D28Refer to the exhibit. A network administrator configures a static route on router R1 to reach the 192.168.1.0/24 network. Which IP address should be used as the next-hop address in the ip route command?192.168.1.1192.168.2.1192.135.250.1192.135.250.229 Because of a topology change, the next hop IP address in the current static route must be reconfigured. How can a static route entry be altered to accommodate a topology change?Keep the existing static route and configure a new static route with the correct next hop IP address.Negate the existing static route and configure a new static route with the correct next hop IP address.Do nothing. The existing static route will automatically update the next hop entry with the new IP address.Keep the existing static route, reload the router, and configure a new static route with the correctnext hop IP address.30Refer to the exhibit. The entire 192.168.1.0 network has been allocated to address hosts in the diagram. Utilizing VLSM with contiguous address blocks, which set of addresses and prefixes could be used to create an addressing solution with a minimum waste of IP addresses?答案:D31Refer to the exhibit. Which host has a combination of IP address and subnet mask on the same network as Fa0/0 of Router1?host Ahost Bhost Chost D32Refer to the exhibit. If the EIGRP routing protocol is used throughout the network, which IP address and mask prefix should be sent by router R1 to the Edge router as a result of manual summarization of LANs A, B, C, and D?192.168.4.0/20192.168.4.0/22192.168.4.0/24192.168.4.0/2633Refer to the exhibit. Routers RTRA and RTRB are running OSPF. What entry does RTRA add in the routing table when Serial 0/0/0 receives an update about the network that is attached to RTRB? O 172.16.7.0/30 [110/51] via 10.10.10.2, 00:00:25, Serial0/0/0O 172.16.7.16/28 [110/51] via 10.10.10.2, 00:00:25, Serial0/0/0O 172.16.7.0/24 [110/51] via 10.10.10.2, 00:00:25, Serial0/0/0O 172.16.0.0/16 [110/51] via 10.10.10.2, 00:00:25, Serial0/0/034Refer to the exhibit. If RIPv1 is used as the routing protocol throughout the network, what RIPv1 route will router R1 advertise to router R3?10.0.0.010.1.0.010.1.1.010.1.2.035 Which statement correctly describes a feature of RIP?RIP is a link-state routing protocol.RIP uses only one metric—hop count— for path selection.Advertised routes with hop counts greater than 10 are unreachable.Messages are broadcast every 10 seconds.36Refer to the exhibit. The network is using the RIPv2 routing protocol. If network 10.0.0.0 goes down, what mechanism will prevent Router1 from advertising false routing information back to Router2?triggered updatespoison reverseholddown timerssplit horizon37 Which mechanism helps to avoid routing loops by advertising a metric of infinity?route poisoningsplit horizonhold-down timertriggered updates38Refer to the exhibit. When troubleshooting a network, it is important to interpret the output of various router commands. On the basis of the exhibit, which three statements are true? (Choose three.)The missing information for Blank 1 is the command show ip route.The missing information for Blank 1 is the command debug ip route.The missing information for Blank 2 is the number 100.The missing information for Blank 2 is the number 120.The missing information for Blank 3 is the letter R.The missing information for Blank 3 is the letter C.39Refer to the exhibit. R1 and R2 are adjacent routers both running RIP. All interfaces on both routers are correctly configured and operational. Both routers are configured to include all connected interfaces in routing updates. R2 is not showing any routes from R1 in the routing table. What is the likely cause?The adjacent interfaces are passive.The distance of 120 exceeds 15 hops.R2 will not accept version 1 updates from R1.Routes are being summarized by R1 but not by R2.40Refer to the exhibit. All routers are configured to use the EIGRP routing protocol with defaultsettings, all routes are advertised on all routers, and the network is fully converged. Which path will the data take to travel between 172.16.1.0/24 and 192.168.100.0/24?It will travel via A, B, and C.It will travel via A, F, E, D, and C.It will travel via A, G, H, and C.The traffic will be load-balanced on all paths.41 Which multicast address does EIGRP use to send hello and updates packets?224.0.0.5224.0.0.6224.0.0.9224.0.0.1042 A router has EIGRP configured as the only routing protocol. In what way might EIGRP respond if there is no feasible successor route to a destination network and the successor route fails?It broadcasts hello packets to all routers in the network to re-establish neighbor adjacencies.It sends queries to adjacent neighbors until a new successor route is found.It immediately sends its entire routing table to its neighbors.It will set the metric for the failed route to infinity.43Refer to the exhibit. EIGRP 1 has been configured on R1. What is the effect of configuring the ip bandwidth-percent eigrp command?The EIGRP bandwidth routing metric will be reduced by 30%.EIGRP 1 protocol traffic will be restricted to 30% of the link bandwidth.Packets that are routed based on EIGRP routing table entries will be limited to 30% of the link bandwidth.EIGRP traffic will be permitted to burst for short periods to 30% above the configured link bandwidth.44Refer to the exhibit. Which two statements are true based on the exhibited output? (Choose two.) All routes are stable.Each route has one feasible successor.The serial interface between the two routers is down.The administrative distance of EIGRP has been set to 50.The show ip eigrp topology command has been run on R1.45Refer to the exhibit. A network designer is testing a prototype of WAN connections. All of therouters in the exhibit are configured for OSPF routing. The design requires that the path between routers A and D through ISP-A is the primary and the path through ISP-B servers as a backup. The designer notices that router A has two equal-cost paths to the LAN on router D. How can the designer correct this problem?Issue a clock rate 2000000 interface command on S0/0/1 of router ISP-B.Change the default OSPF reference bandwidth on router A.Configure two static routes with administrative distances of 10.Use the bandwidth command to change the default bandwidth on the link to router B.46Refer to the exhibit. R1 and R2 are unable to establish an adjacency. What two configuration changes will correct the problem? (Choose two.)Set a lower priority on R2.Configure the routers in the same area.Set a lower cost on R2 compared to R1.Add a backup designated router to the network.Match the hello and dead timers on both routers.47Refer to the exhibit. If the router loopback interfaces, FastEthernet interfaces, and OSPF priorities are configured as shown, which router would win an OSPF DR election?ABCD48 Two routers need to be configured within a single OSPF area. Which two components need to be configured on both routers to achieve this? (Choose two.)the same process IDthe same area IDnetwork addresses and wildcard masksthe same router IDthe same loop back address49Refer to the exhibit. What OSPF network statements are required for the router B to advertise the three networks that are attached?router ospf 1network 10.0.0.0 0.0.0.255 area 0router ospf 1network 10.1.1.0 0.3.255.255 area 0network 10.10.1.0 0.255.255.255 area 0network 10.20.1.0 0.255.255.255 area 0router ospf 1network 10.1.1.0 0.0.0.3 area 0network 10.10.1.0 0.0.255.255 area 0network 10.20.1.0 0.0.255.255 area 0router ospf 1network 10.1.1.0 0.0.0.3 area 0network 10.10.1.0 0.0.0.255 area 0network 10.20.1.0 0.0.0.255 area 050Refer to the exhibit. A network administrator is trying to determine why router JAX has no OSPF routes in its routing table. All routers are configured for OSPF area 0. From the JAX router, the administrator is able to ping its connected interfaces and the Fa0/1 interface of the ORL router but no other router interfaces. What is a logical step that the network administrator should take to troubleshoot the problem?Reboot the routers.Change the OSPF process ID on all of the routers to 0.Check to see if the cable is loose between ORL and JAX.Check to see if CDP packets are passing between the routers.Use show and debug commands to determine if hellos are propagating.CCNA第二学期《Final Examinnation》英文B卷1 A network administrator is in charge of two separate networks that share a single building. What device will be required to connect the two networks and add a common connection to the Internet that can be shared?hubrouteraccess pointEthernet switch2 Which two router component and operation pair are correctly described? (Choose two.)DRAM - loads the bootstrapRAM - stores the operating systemFlash - executes diagnostics at bootupNVRAM - stores the configuration fileROM - stores the backup configuration filePOST - runs diagnostics on hardware modules3 A router boots and enters setup mode. What is the reason for this?The IOS image is corrupt.Cisco IOS is missing from flash memory.The configuration file is missing from NVRAM.The POST process has detected hardware failure.4Refer to the exhibit. Packets destined to which two networks will require the router to perform a recursive lookup? (Choose two.)10.0.0.0/864.100.0.0/16128.107.0.0/16172.16.40.0/24192.168.1.0/24192.168.2.0/245 Which candidate route has the longest match for a packet with a destination address of 10.30.16.48?10.30.0.0/1610.30.15.0/2310.30.16.0/2410.30.16.32/2710.30.16.32/306Refer to the exhibit. Routers R1 and R3 use different routing protocols with default administrative distance values. All devices are properly configured and the destination network is advertised by both protocols.Which path will be used to transmit the data packets from PC1 to PC2?The packets will travel via R2-R1.The packets will travel via R2-R3.The traffic will be load-balanced between two paths — via R2-R1 and via R2-R3.The packets will travel via R2-R3, and the other path via R2-R1 will be retained as the backup path.7 In a complex lab test environment, a router has discovered four paths to 192.168.1.0/24 via the use of the RIP routing process. Which route will be installed in the routing table after the discovery of all four paths?R 192.168.1.0/24 [120/3] via 192.168.110.1, 00:00:17, Serial0/1/0R 192.168.1.0/24 [120/2] via 192.168.200.1, 00:00:17, Serial0/0/0R 192.168.1.0/24 [120/1] via 192.168.100.1, 00:00:17, Serial0/0/1R 192.168.1.0/24 [120/4] via 192.168.101.1, 00:00:17, Serial0/1/18Refer to the exhibit. The router receives a packet that is destined for 192.168.5.79. How will the router handle this packet?It will forward the packet via the FastEthernet0/0 interface.It will forward the packet via the Serial0/0/0 interface.It will forward the packet via the Serial0/0/1 interface.It will drop the packet.9 A network administrator uses the RIP routing protocol to implement routing within an autonomous system. What are two characteristics of this protocol? (Choose two.)It uses the Bellman-Ford algorithm to determine the best path.It displays an actual map of the network topology.It offers rapid convergence in large networks.It periodically sends complete routing tables to all connected devices.It is beneficial in complex and hierarchically designed networks.10 Which two statements are true for link-state routing protocols? (Choose two.)Routers that run a link-state protocol can establish a complete topology of the network. Routers in a multipoint network that run a link-state protocol can exchange routing tables. Routers use only hop count for routing decisions.The shortest path first algorithm is used.Split horizon is used to avoid routing loops.11 Which two statements are true about classless routing protocols? (Choose two.)They can be used for discontiguous subnets.They can forward supernet routes in routing updates.They cannot implement classful routes in routing tables.They use only a hop count metric.They do not include the subnet mask in routing updates.12 Which statement is true regarding routing metrics?All routing protocols use the same metrics.EIGRP uses bandwidth as its only metric.Routers compare metrics to determine the best route.The larger metric generally represents the better path.13 Which routing protocol by default uses bandwidth and delay to calculate the metric of a route? RIPv1RIPv2OSPFEIGRP14 You have been asked to explain converged networks to a trainee. How would you accurately describe a converged network?A network is converged when all routers have formed an adjacency.A network is converged immediately after a topology change has occurred.A network is converged when all routers flush the unreachable networks from their routing tables.A network is converged after all routers share the same information, calculate best paths, and update their routing tables.15Refer to the exhibit. All the routers are properly configured to use the RIP routing protocol with default settings, and the network is fully converged. Router A is forwarding data to router E. Which statement is true about the routing path?Router A will send the data via the A-D-E path that is listed in the routing table.Router A will load-balance the traffic between A-B-E and A-C-E.Router A will determine that all paths have equal metric cost.Router A will send the data through A-D-E and keep A-B-E and A-C-E as the backup paths.16Refer to the exhibit. A device is required to complete the connection between router R1 and the WAN. Which two devices can be used for this? (Choose two.)a CSU/DSU devicea modeman Ethernet switcha huba bridge17 Which component is typically used to connect the WIC interface of a router to a CSU/DSU? V.35 cableRJ-45 adaptercrossover cablestraight-through cable18 Which router mode is accessed by entering the enable command?user EXECprivileged EXECglobal configurationinterface configuration19Refer to the exhibit. What are the effects of the exhibited commands on the router?All passwords are encrypted.Only Telnet sessions are encrypted.Only the enable password is encrypted.Only the enable password and Telnet session are encrypted.Enable and console passwords are encrypted.20Refer to the exhibit. A technician has configured the interfaces on the Router, but upon inspection discovers that interface FastEthernet0/1 is not functioning. Which action will most likely correct the problem with FastEthernet0/1?A clock rate should be added to the interface configuration.The subnet mask should be added to the interface configuration.An interface description needs to be added to the interface configuration.The no shutdown command needs to be added to the interface configuration.21Refer to the exhibit. Which two facts can be derived from this output? (Choose two.)Three network devices are directly connected to Router2.The serial interface between Router2 and Router3 is up.Router1 and Router3 are directly connected.Six devices are up and running on the network.Layer 3 functionality between routers is configured properly.22Refer to the exhibit. Which route in the routing table of R1 will be discarded by its neighboring router?192.168.2.0192.168.3.0192.168.4.0192.168.9.0192.168.10.0192.168.11.023Refer to the exhibit. All interfaces are addressed and functioning correctly. The network administrator runs the tracert command on host A. Which two facts could be responsible for the output of this command? (Choose two.)The gateway for Host A is missing or improperly configured.The gateway for Host B is missing or improperly configured.The entry for 192.168.1.0/24 is missing from the routing table of R1.The entry for 192.168.1.0/24 is missing from the routing table of R2.The entry for 192.168.2.0/24 is missing from the routing table of R1.The entry for 192.168.2.0/24 is missing from the routing table of R2.24 In which situation would a default static route be recommended?when connecting an edge router to the Internetwhen variable length subnet masking is in effectwhen there is more than one valid route for a destination networkwhen a destination network has a larger mask than any routes in the routing table25 What is the advantage of configuring a static route with an exit interface instead of a next-hop address?The router will perform a recursive lookup.This route will automatically be used as the gateway of last resort.The exit interface configuration consumes less router processing time.The exit interface configuration has an administrative distance value of 1.26Refer to the exhibit. On the basis of the show running-config output, which option correctly reflects the routes that will be listed in the R2 routing table?答案:D27 A static route has been configured on a router. However, the destination network no longer exists. What should an administrator do to remove the static route from the routing table? Change the routing metric for that route.Nothing. The static route will go away on its own.Change the administrative distance for that route.Remove the route using the no ip route command.28Refer to the exhibit. Hosts on the 192.168.1.0 network cannot communicate with hosts on the 172.16.1.1 network. The network administrator has run the show ip route command on R1.What could be the cause of this problem?The FastEthernet interface on R1 is disabled.Autosummarization is enabled on R1.The serial interface S0/0/0 of R1 is administratively down.No static route or routing protocol is configured.29Refer to the exhibit. The users on the local network 172.16.1.0/24 complain that they are unable to connect to the Internet. What step should be taken to remedy the problem?A new static route must be configured on R1 with the R3 serial interface as the next hop.A new default route must be configured on R1 with the R3 serial interface as the next hop.The default route on R2 should be configured with the R3 serial interface as the next hop.The default route on R2 must be replaced with a new static route and the next hop should be the R1 FastEthernet interface.30 A network administrator needs to assign the very last usable IP address in the 172.24.64.0/18 network range to the router interface that serves this LAN. Which IP address should the administrator configure on the interface?172.16.128.154/18172.16.255.254/18172.24.64.254/18172.24.127.254/1831。
640-607Cisco Certified Network Associate 3.0CCNA 3.0Demo Version 4.0Important NotePlease Read CarefullyStudy TipsThis product will provide you questions and answers along with detailed explanations carefully compiled and written by our experts. Try to understand the concepts behind the questions instead of cramming the questions. Go through the entire document at least twice so that you make sure that you are not missing anything. Further MaterialFor this test TestKing also provides:* Study Guide. Concepts and labs.* Interactive Test Engine Examinator. Check out an Examinator Demo at/index.cfm?pageid=724Latest VersionWe are constantly reviewing our products. New material is added and old material is revised. Free updates are available for 90 days after the purchase. You should check your member zone at TestKing an update 3-4 days before the scheduled exam date.Here is the procedure to get the latest version:1.Go to 2.Click on Member zone/Log in3.The latest versions of all purchased products are downloadable from here. Just click the links.For most updates, it is enough just to print the new questions at the end of the new version, not the whole document.FeedbackFeedback on specific questions should be send to feedback@. You should state: Exam number and version, question number, and login ID.Our experts will answer your mail promptly.QUESTION NO: 1Which of the following troubleshooting tools use the protocol ICMP? (Choose two)A.PingB.TelnetC.ConfigureD.Trace routeE.Show commandsF.Standard access listAnswer: A, DExplanation: The two protocol tools that use ICMP messaged to perform their function are ping and trace route.Incorrect Answers:B: Telnet uses TCP.C:Configure is not a protocol tool.E:They are not part of ICMP, nor do they use ICMP.Steve McQuerry. Interconnecting Cisco Network Devices. (Cisco Press: 2000) pages 217-218.QUESTION NO: 2Which one of the following is a layer two broadcast?A.The IP subnet used is 255.255.255.0B.The IP address used is 255.255.255.255C.The MAC address used is 00-00-00-00-00-00D.The MAC address used is FF-FF-FF-FF-FF-FF.Answer: DExplanation: The MAC address for a broadcast is FF-FF-FF-FF-FF-FF.Incorrect Answers:A and B: These are IP addresses and 802.3 uses MAC addresses.C:This is the address used for a multicast.Steve McQuerry. Interconnecting Cisco Network Devices. (Cisco Press: 2000) pages 149-152.QUESTION NO: 1Exhibit:The network administrator of the TestKing1 router adds the following command to the router configuration: ip route 192.168.12.0 255.255.255.0 172.16.12.1What are the results of adding this command? (Choose two)A.The command establishes a static route.B.The command invokes a dynamic routing protocol for 192.168.12.0.C.Traffic for network 192.168.12.0 is forwarded to 172.16.12.1.D.Traffic for all networks is forwarded to 172.16.12.1.E.This route is automatically propagated throughout the entire network.Answer: A, CExplanation:IP route command defines static route on a particular router, Traffic from 192.168.12.0 network is forwarded to 172.16.12.1 ( IP address of next hop interface).Incorrect answersB: It will not invoke any routing Protocol. It defines static route.D: Only traffic from 192.168.12.0 network is forwarded to 172.16.12.1.E: It will not propagate route automatically by using ip route command. Route will be propagated only if you defined routing protocol configured networks.QUESTION NO: 2What does a configuration Register Setting of 0x2105 indicate to the Router?A.The Boot IOS Code is Located in the NVRAM.B.Check NVRAM for boot system Commands.C.Bypass NVRAM Configurations.D.Boot the IOS Code Located in ROM.E.Perform a Password Recovery.F.Bypass The Code In ROM.Answer: BExplanation:It is stated in the book ICND by Steve McQuerry page 127 that if the configuration register boot field value is from 0x2 to 0xF, the bootstrap code parses any configuration in NVRAM for boot system commands. Incorrect Answers:A: Statement is wrong because IOS code is located in flash not NVRAM (startup-configuration)C: Register setting of 0x2105 where 5 is the boot field. Boot field value of 0x2 to 0xF will look for startup-configuration in the NVRAM and won't be bypass.D: Statement is wrong because IOS code is located in flash not ROM (RxBoot).E: This register is not for password recovery.F: This statement is wrong.QUESTION NO: 3Exhibit:After Configuring the router show in the exhibit, the TestKing technician decides to test and document the network, pings from the technician’s laptop to all of the interface on each router were successful, if a technician initiates a telnet session to Router TestKing1 and issues the show arp command, which of the following items will be among the entries displayed in the output?A.The MAC address of the S0 interface on Router TestKing1B.The MAC address of the E0 interface on Router TestKing1C.The MAC address of the S0 interface on Router TestKing2D.The MAC address of the E0 interface on Router TestKing2Answer: BExplanation: Because the question stated that the technician initiated a telnet session to Testking1 not TestKing2 so the layer 2 destination address will have the TestKing1 MAC address.Incorrect Answers:A, C: Serial interfaces don't have layer 2 addresses (MAC addresses)?D: Telnet initiated from Testking 1. It will not show Mac address of EO on Testking2QUESTION NO: 4Exhibit:*** Out Put Omitted***MTU 1500 bytes, Bw 10000 kbit, Dly 100 Usec.reliability 128/255, txload 1/255. rx 253/255Encapsulation Arpa, Loopback not setKeepalive set (10 sec)Arp type: Arpa Timeout 04:00:00Last Input 21:24:36, output 00:00:08, Output hang never*Out Put Omitted***Users have been complaining that network applications are running very slowly and responding to input commands intermittently. While troubleshooting the problem, a TestKing technician issues the slow interface E0 command on the router attached to the network. Based on the partial output shown in the exhibit.. Which of the following items indicates that interface E0 is overloaded and causing the networkto perform slowly?A.MTU 1500 bytesB.BW 10000 kbitC.DLY 1000 usecD.Reliability 128/255E.txload 1/255F.rxload 253/255Answer: DExplanation: Interface E0 is only 50% reliable (128/255) where 255/255 being 100% reliable.Incorrect Answers:A, B, C: Because those are default settings and those output are the output readings in normal operation.QUESTION NO: 5Which of the following correctly describe steps in the OSI data encapsulation process? (Choose two)A.Transport layer divides a data stream into segments & adds reliability & flow control informationB.Data link layer adds physical source & destination address & an FCS to the segmentC.Packets are created when the network layer encapsulate a frame with source & destination host address& protocol related control informationD.Packets are created when the network layers adds layers 3 address & control information to a segmentE.The presentation layer translated bits into bits into voltages for transmission across the physical link Answer: A, DExplanation:A: It is the function of Transport layer. TCP and UDP operates in this layerD: It is the function of the network layer.Incorrect answers:B: It will use frames instead of segments.C: The network layer can not encapsulate frame. It adds Layer 3 address to segment received from transport layer.E: It is not the function of Presentation layer. It is function of Physical layer.。
这是我学习过程中遇见的ccna试题,中文一份,英文一份,很经典呀。
1 技术人员需要为某幢已经布设有线以太网络的大厦提供无线连接。
哪三个因素会影响需要的接入点数目?(选择三项。
)大厦的规模大厦中实体内墙的数目多个办公室中有微波炉无线网络中使用的加密方法Windows 和Appletalk 操作系统的同时使用AP 中短波或红外线的使用2 下列关于无线网桥的陈述,哪一项是正确的?通过无线链路连接两个网络连接无线局域网的固定设备允许无线客户端连接到有线网络增强无线信号的强度3 接入点默认使用哪一类身份验证?开放式PSKWEPEAP4请参见图示。
在Linksys 集成路由器的Wireless 菜单选项中,Network Mode 选项Mixed 是什么意思?路由器支持加密和身份验证。
路由器支持有线和无线两种连接。
路由器支持802.11b、802.11g 和802.11n 设备。
路由器支持通过红外和无线电射频连接。
5 接入点可以使用哪两种身份验证方法?(选择两项。
)WEPWPAEAPASCII预共享密钥6 哪项接入点功能允许网络管理员定义可以进入无线网络的数据类型?加密黑客攻击拦截通信过滤MAC 地址过滤身份验证7 下列关于服务集标识符(SSID) 的陈述中,哪两个是正确的?(选择两项。
)标识无线设备所属的WLAN是一个包含32 个字符的字符串,不区分大小写负责确定信号强度同一WLAN 中的所有无线设备必须具有相同的SSID用于加密通过无线网络发送的数据8请参见图示。
在Linksys 集成路由器的Wireless 菜单中,哪个配置选项可用于让附近的客户端知道接入点的存在。
Network ModeNetwork Name (SSID)Radio BandWide ChannelStandard ChannelSSID Broadcast9 下列哪个术语准确描述了为防止黑客读取截取到的数据而进行的无线数据编码?地址过滤身份验证广播加密密码短语编码10 两种WEP 密钥长度分别是多少?(选择两项。
)8 位16 位32 位64 位128 位11 使用开放式身份验证与使用预共享密钥有何差异?开放式身份验证需要密码。
预共享密钥不需要密码。
开放式身份验证用于无线网络。
预共享密钥用于有线网络。
预共享密钥需要加密的密码。
开放式身份验证不需要加密密码。
预共享密钥需要将MAC 地址编程到接入点中。
开放式身份验证不需要这种编程。
12 下列关于在接入点上启用开放式身份验证的陈述,哪一项是正确的?不需要身份验证使用64 位加密算法需要使用身份验证服务器需要共同商定的密码13 Wi-Fi 徽标对无线设备意味着什么?该设备已通过IEEE 认证。
该设备能够与所有其它无线标准交互操作。
该设备能够与其它符合Wi-Fi 标准并贴有Wi-Fi 徽标的其它设备交互操作。
该设备与所有以前的无线标准后向兼容。
14 下列哪两项陈述说明了无线网络安全的特征?(选择两项。
)无线网络提供的安全功能与有线网络相同。
驾驶攻击增强了无线网络的安全性。
禁用SSID 广播后,攻击者必须知道SSID 才能连接。
在接入点上使用默认IP 地址使黑客攻击更容易。
攻击者需要物理接触至少一台网络设备才能发动攻击。
15 与有线技术相比,无线技术有哪三大优势?(选择三项。
)更安全范围更大连接不受时间和地点限制安装简单、经济许可空间的使用很方便便于增加设备16 下列关于无线对等网络的陈述,哪一项是正确的?由点对点网络的无线客户端互联组成由无线客户端与一个中央接入点互联组成由多个无线基本服务集通过分布系统互联组成由无线客户端通过ISR 与有线网络互联组成17 完成以下句子:WEP 用于______,而EAP 则用于在无线网络中_____。
加密;验证用户身份过滤通信量;选择工作频率识别无线网络;压缩数据创建最小的无线网络;限制用户数量18 为什么安全性在无线网络中如此重要?无线网络的速度通常比有线网络慢。
电视及其它设备可能干扰无线信号。
无线网络采用了非常易于接入的介质来广播数据。
雷暴等环境因素可能影响无线网络。
19 无线网络与有线网络相比有哪两项优势?(选择两项)速度安全性移动性减少安装时间用户可以共享更多资源不易受到其它设备干扰20 为什么IEEE 802.11 无线技术传输的距离比蓝牙技术更远?传输的频率低得多功率输出更高传输的频率高得多使用更好的加密方法21 哪个WLAN 组件通常被称为STA?移动电话天线接入点无线网桥无线客户端Under what conditions does the router enter setup mode? (Choose three.)immediately after issuing the command Router#erase startafter issuing the command Router#setupduring the initial configuration of a routerafter deleting the backup configuration and reloading the routerafter deleting the running configuration2What information about the router and its startup process can be gathered from the output of the show version command?three.)the last restart methodthe command buffer contentsthe amount of NVRAM and FLASH usedthe configuration register settingsthe location from where the IOS loaded3Which tasks can be performed in the ROM monitor mode? (Choose two.)recover from system failurescreate startup configuration filesrecover from lost passwordsconfigure IP addresses on all router interfacesperform high level diagnostics4After the active IOS image has been loaded into RAM from flash memory, which commands could be used to display the fil active IOS? (Choose two.)Router# show IOSRouter# show flashRouter# show nvramRouter# show versionRouter# show startup-configRouter# show running-config5 Cisco IOS software is separated into two levels as a security feature. What are those two levels? (Choose two.)globalprivilegedlocaluserinterface6What does the command sh? return as output if issued at the Router# prompt?all show commands allowed in privileged modeall commands beginning with the letters shan incomplete command error messagean invalid command error message7Which tasks can be accomplished by using the command history feature? (Choose two.)View a list of commands entered in a previous session.Recall up to 15 command lines by default.Set the command history buffer size.Recall previously entered commands.Save command lines in a log file for future reference.8When the router output is being viewed through a terminal program, which statements are true regarding the --More-- prom bottom of the router display? (Choose two.)Press the Spacebar to display the next line.Press the Spacebar to view the next screen.Press the PgDn key to view the next screen.Press the Enter key to display the next line.Press the Enter key to view the next screen.9What is the default sequence for loading the configuration file?NVRAM, FLASH, ROMFLASH, TFTP,CONSOLENVRAM, TFTP, CONSOLEFLASH, TFTP, ROM10.Which connection method can be used to perform the initial configuration of a router?use a serial connection of a computer connected to the console port of a routertelnet to the router through a serial portuse a vty port through the Ethernet interfaceuse a modem connected to the AUX port of the router11Which keystrokes can be used to return to the privileged mode from the interface configuration mode?Ctrl-PCtrl-Shift-6, then XCtrl-ZEsc12Which command takes precedence if the commands enable password and enable secret are both configured on a rouenable passwordenable secretNeither. They are both enabled.Neither. They cancel each other out.13Which of the following identifies the correct items needed to initially configure a router?1) DB-9-to-RJ-45 on the PC's serial port2) a straight through cable3) the router's console port1) PC's Ethernet port2) a crossover cable3) the router's Ethernet port1) DB-9-to-RJ-45 on the PC's serial port2) a rollover cable3) the router's Ethernet port1) PC's Ethernet port2) a rollover cable3) the router's console port1) DB-9-to-RJ-45 on the PC's serial port2) a rollover cable3) the router's console port1) PC's Ethernet port2) a rollover cable3) the router's Ethernet port14.A network administrator needs to configure a router. Which of the following connection methods requires network functionalitaccessible?consoleAUXTelnetmodem15What baud rate needs to be configured on terminal emulation software to allow a connection to the console port of a route240048009600142003840016 What information does the name of the IOS file provide to the network administrator? (Choose three.)the amount of NVRAM required to run the imagethe hardware platform the image runs onthe various software platforms the image can run onspecial features and capabilities of the imagethe bandwidth supported by the IOSwhere the image executes from and if it has been compressed17Which of the following is the correct flow of routines for a router startup?load bootstrap, load IOS, apply configurationload bootstrap, apply configuration, load IOSload IOS, load bootstrap, apply configuration, check hardwarecheck hardware, apply configuration, load bootstrap, load IOS18Which of the following statements concerning router interface modes are correct? (Choose three.)User EXEC mode provides commands to monitor router operation.Privileged EXEC mode only provides commands to change or configure router operation.Password protected configuration modes can be accessed from either user EXEC or privileged EXEC modes.On a router with the name Core1, the prompt indicating privileged EXEC mode is Core1#.The command to enter privileged EXEC mode is Router# enable.A username and password may be required to enter privileged EXEC mode.19Which keystroke is used to move to the beginning of a command line?Ctrl-ACtrl-BEsc-AEsc-BCtrl-CCtrl-Z。