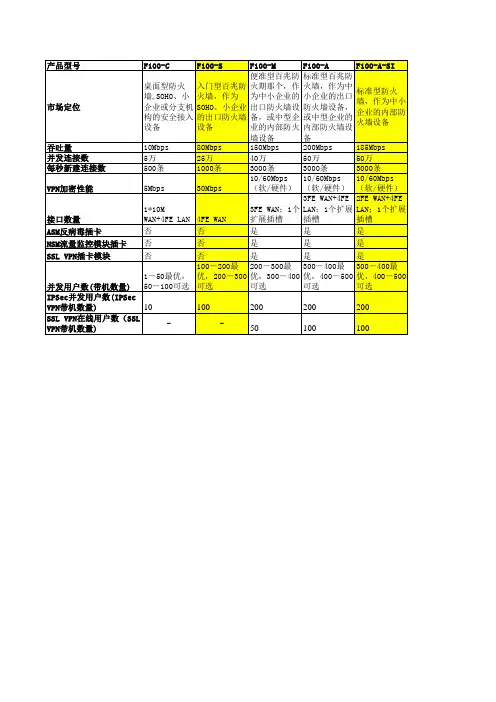
数据中心防火墙参数
- 格式:docx
- 大小:18.75 KB
- 文档页数:2
![华为防火墙配置使用手册(自己写)[4]](https://uimg.taocdn.com/2085ce1fcdbff121dd36a32d7375a417866fc10f.webp)
华为防火墙配置使用手册(自己写)华为防火墙配置使用手册一、概述二、防火墙基本概念包过滤防火墙:它只根据数据包的源地址、目的地址、协议类型和端口号等信息进行过滤,不对数据包的内容进行分析。
它的优点是处理速度快,开消小,但是安全性较低,不能阻挠应用层的攻击。
状态检测防火墙:它在包过滤防火墙的基础上,增加了对数据包的连接状态的跟踪和记录,可以识别出非法的连接请求和数据包,并拒绝通过。
它的优点是安全性较高,可以阻挠一些常见的攻击,但是处理速度较慢,开消较大。
应用代理防火墙:它对数据包的内容进行深度分析,可以识别出不同的应用协议和服务,并根据应用层的规则进行过滤。
它的优点是安全性最高,可以阻挠复杂的攻击,但是处理速度最慢,开消最大。
访问控制:它可以根据源地址、目的地址、协议类型、端口号、应用类型等信息对网络流量进行分类和过滤,实现对内外网之间访问权限的控制和管理。
虚拟专网:它可以建立安全隧道,实现不同地域或者组织之间的数据加密传输,保证数据的机密性、完整性和可用性。
内容安全:它可以对网络流量中携带的内容进行检查和过滤,如、网页、文件等,并根据预定义的规则进行拦截或者放行。
用户认证:它可以对网络访问者进行身份验证,如用户名、密码、证书等,并根据不同的用户或者用户组分配不同的访问权限和策略。
流量管理:它可以对网络流量进行统计和监控,如流量量、流量速率、流量方向等,并根据预定义的规则进行限制或者优化。
日志审计:它可以记录并保存网络流量的相关信息,如源地址、目的地址、协议类型、端口号、应用类型、过滤结果等,并提供查询和分析的功能。
三、防火墙配置方法命令行界面:它是一种基于文本的配置方式,用户可以通过控制台或者远程终端访问防火墙,并输入相应的命令进行配置。
它的优点是灵便性高,可以实现细致的配置和管理,但是需要用户熟悉命令的语法和逻辑。
图形用户界面:它是一种基于图形的配置方式,用户可以通过浏览器或者客户端软件访问防火墙,并通过或者拖拽等操作进行配置。

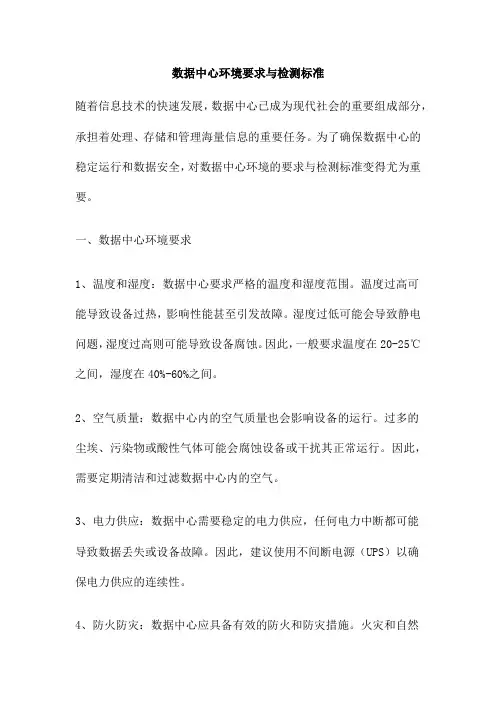
数据中心环境要求与检测标准随着信息技术的快速发展,数据中心已成为现代社会的重要组成部分,承担着处理、存储和管理海量信息的重要任务。
为了确保数据中心的稳定运行和数据安全,对数据中心环境的要求与检测标准变得尤为重要。
一、数据中心环境要求1、温度和湿度:数据中心要求严格的温度和湿度范围。
温度过高可能导致设备过热,影响性能甚至引发故障。
湿度过低可能会导致静电问题,湿度过高则可能导致设备腐蚀。
因此,一般要求温度在20-25℃之间,湿度在40%-60%之间。
2、空气质量:数据中心内的空气质量也会影响设备的运行。
过多的尘埃、污染物或酸性气体可能会腐蚀设备或干扰其正常运行。
因此,需要定期清洁和过滤数据中心内的空气。
3、电力供应:数据中心需要稳定的电力供应,任何电力中断都可能导致数据丢失或设备故障。
因此,建议使用不间断电源(UPS)以确保电力供应的连续性。
4、防火防灾:数据中心应具备有效的防火和防灾措施。
火灾和自然灾害都可能对数据中心造成严重损害,因此必须采取适当的预防措施。
5、噪声和振动:噪声和振动可能会干扰数据中心的正常运行。
因此,需要采取措施来减少这些影响,例如使用隔音材料和减震设备。
二、数据中心检测标准1、设备性能:定期检查和维护数据中心的设备,确保其性能正常。
应定期进行硬件和软件的更新和升级,以保持最佳性能。
2、温度和湿度:定期检查数据中心的温度和湿度,确保其在规定的范围内。
如果发现任何异常,应立即采取行动进行调整。
3、空气质量:定期进行空气质量检测,确保数据中心内没有过多的尘埃、污染物或酸性气体。
4、电力供应:定期检查电力供应的稳定性和UPS的性能。
如果发现任何问题,应立即采取行动解决。
5、防火防灾:定期检查防火和防灾设施的性能和状态,确保其在良好的工作状态。
6、噪声和振动:定期检查数据中心的噪声和振动水平,确保其不会干扰设备的正常运行。
为了确保数据中心的稳定运行和数据安全,必须严格遵守上述环境要求和检测标准。

Hillstone X-SeriesData Center Firewall X10800X10800The Hillstone X10800 Data Center Firewall offers outstanding performance, reliability, andscalability, for high-speed service providers, large enterprises and carrier networks. The product is based on an innovative fully distributed architecture that fully implements firewalls with high throughput, concurrent connections, and new sessions. Hillstone X10800 also supportslarge-capacity virtual firewalls, providing flexible security services for virtualized environments, and features such as application identification, traffic management, intrusion prevention, and attack prevention to fully protect data center network security.FrontRearProduct HighlightHigh Performance based on Elastic Security ArchitectureWith traffic explosively increasing, data center firewalls need powerful capabilities to handle high traffic and massive concurrent user access, as well as the ability to effectively cope with sudden bursts of user activity. Therefore, data center firewalls must not only have high throughput but also extremely high concurrent connections and new session processing capabilities.The Hillstone X10800 Data Center Firewall adopts an inno-vative, fully distributed architecture to implement distributed high-speed processing of service traffic on Service Modules (SSMs) and Interface Modules (IOMs) through intelligent traffic distribution algorithms. Through patented resource management algorithms, it allows for the full potential of dis-tributed multi-core processor platforms, to further increase the performance of firewall concurrent connections, new sessions per second, and achieve a fullly linear expansionof system performance. The X10800 data center firewall can process up to 1 Tbps, up to 10 million new sessionsper second, and up to 480 million concurrent connections. The device can provide up to 44 100GE interfaces, 88 10G interfaces, or 22 40GE interface, 132 10G interface expansion capabilities. Moreover, the packet forwarding delay is less than 10us, which can fully meet a data center’s demand for real-time service forwarding.Carrier Grade ReliabilityThe hardware and software of the X10800 data center fire-wall delivers 99.999% carrier-grade reliability. It can support active/active or active/passive mode redundant deployment solutions to ensure uninterrupted service during single failure. The entire system adopts a modular design, supporting con-trol module redundancy, service module redundancy, inter-face module redundancy and switching module redundancy, and all modules are hot-swappable.The X10800 data center firewall supports multi-mode and single-mode optical port bypass modules. When the device is running under a special condition, such as power off, the system will start in Bypass mode to ensure uninterrupted operation of business. It also provides power redundancy, fan redundancy and other key components to guarantee reliability.Twin-mode HA effectively solves the problem of asymmetric traffic in redundant data centers. The firewall twin-mode isa highly reliable networking mode building on dual-device backup. Two sets of active/passive firewalls in the two data centers are connected via a dedicated data link and control link. The two sets of devices synchronize session information and configuration information with each other.Leading Virtual Firewall TechnologyVirtualization technology is more and more widely used in data centers. The X10800 data center firewall can logically divide a physical firewall into upwards of 1000 virtual fire-walls for the data center’s virtualization needs, providing virtual firewall support capabilities for large data centers. At the same time, users can dynamically set resource for each virtual firewall based on actual business conditions, suchas CPUs, sessions, number of policies, ports, etc., to ensure flexible changes in service traffic in a virtualized environment. Each virtual firewall system of X10800 data center firewalls not only has independent system resources, but also can be individually and granularly managed to provide independent security management planes for different services or users. Granular Application Control and Comprehensive SecurityThe X10800 data center firewall uses advanced in-depth application identification technology to accurately iden-tify thousands of network applications based on protocol features, behavior characteristics, and correlation analysis, including hundreds of mobile applications and encrypted P2P applications. It provides sophisticated and flexible application security controls.The X10800 data center firewall provides intrusion prevention technology based on deep application identification, proto-col detection, and attack principle analysis. It can effectively detect threats such as Trojans, worms, spyware, vulnerability attacks, and escape attacks, and provide users with L2-L7Product Highlight (Continued) FeaturesNetwork Services• Dynamic routing (OSPF, BGP, RIPv2)• Static and Policy routing• Route controlled by application• Built-in DHCP, NTP, DNS Server and DNS proxy • Tap mode – connects to SPAN port• Interface modes: sniffer, port aggregated, loopback, VLANS (802.1Q and Trunking)• L2/L3 switching & routing• Virtual wire (Layer 1) transparent inline deploymentFirewall• Operating modes: NAT/route, transparent (bridge), and mixed mode• Policy objects: predefined, custom, and object grouping• Security policy based on application, role and geo-location• Application Level Gateways and session support: MSRCP, PPTP, RAS, RSH, SIP, FTP, TFTP, HTTP, dcerpc, dns-tcp, dns-udp, H.245 0, H.245 1, H.323 • NAT and ALG support: NAT46, NAT64, NAT444, SNAT, DNAT, PAT, Full Cone NAT, STUN• NAT configuration: per policy and central NAT table• VoIP: SIP/H.323/SCCP NAT traversal, RTP pin holing• Global policy management view• Security policy redundancy inspection, policygroup, policy configuration rollback• Policy Assistant for easy detailed policydeployment• Policy analyzing and invalid policy cleanup• Comprehensive DNS policy• Schedules: one-time and recurringIntrusion Prevention• Protocol anomaly detection, rate-based detection,custom signatures, manual, automatic push orpull signature updates, integrated threat encyclo-pedia• IPS Actions: default, monitor, block, reset(attackers IP or victim IP, incoming interface) withexpiry time• Packet logging option• Filter Based Selection: severity, target, OS, appli-cation or protocol• IP exemption from specific IPS signatures• IDS sniffer mode• IPv4 and IPv6 rate based DoS protection withthreshold settings against TCP Syn flood, TCP/UDP/SCTP port scan, ICMP sweep, TCP/UDP/SCIP/ICMP session flooding (source/destination)• Active bypass with bypass interfaces• Predefined prevention configurationAnti-Virus• Manual, automatic push or pull signature updates• Flow-based Antivirus: protocols include HTTP,SMTP, POP3, IMAP, FTP/SFTP• Compressed file virus scanningAttack Defense• Abnormal protocol attack defense• Anti-DoS/DDoS, including SYN Flood, DNS QueryFlood defense• ARP attack defenseURL Filtering• Abnormal protocol attack defense• Anti-DoS/DDoS, including SYN Flood, DNS QueryFlood defense• ARP attack defense• Flow-based web filtering inspection• Manually defined web filtering based on URL, webcontent and MIME header• Dynamic web filtering with cloud-based real-timecategorization database: over 140 million URLswith 64 categories (8 of which are security related)• Additional web filtering features:- Filter Java Applet, ActiveX or cookie- Block HTTP Post- Log search keywords- Exempt scanning encrypted connections oncertain categories for privacy• Web filtering profile override: allows administratorto temporarily assign different profiles to user/group/IP• Web filter local categories and category ratingoverridenetwork security. Among them, Web protection function can meet the deep security protection requirements of Web server; Botnet filtering function can protect internal hosts from infection.The X10800 data center firewall supports URL filtering for tens of millions of URL signature library. It can help admin-istrators easily implement web browsing access control and avoid threat infiltration of malicious URLs. It also provides Anti-virus feature that can effectively detect and block mal-wares with low latency.The intelligent bandwidth management of X10800 data center firewall is based on deep application identification and user identification. Combined with service application priorities, the X10800 data center firewall can implement fine-grained, two-layer, eight-level traffic control based on policies and provide elastic QoS functions. Used with functions such as session restrictions, policies, routing, link load balancing, and server load balancing, it can provide users with more flexible traffic management solutions.Strong Network AdaptabilityThe X10800 data center firewall fully supports next-genera-tion Internet deployment technologies (including dual-stack, tunnel, DNS64/NAT64 and other transitional technologies). It also has mature NAT444 capabilities to support static mapping of fixed-port block of external network addresses to intranet addresses. It can generate logs based on session and user for easy traceability. Enhanced NAT functions (Full-cone NAT, port multiplexing, etc.) can fully meet the require-ments of current ISP networks and reduce the cost of user network construction.The X10800 data center firewall provides full compliance with standard IPSec VPN capabilities and integrates third-gen-eration SSL VPN to provide users with high-performance, high-capacity, and full-scale VPN solution. At the same time, its unique plug-and-play VPN greatly simplifies configuration and maintenance challenges and provides users with convenient and remote secure access services.IP Reputation• Identify and filter traffic from risky IPs such as botnet hosts, spammers, Tor nodes, breached hosts, and brute force attacks• Logging, dropping packets, or blocking for different types of risky IP traffic• Regular IP reputation signature database upgrade Endpoint Identification and Control• Support to identify endpoint IP, endpoint quantity, on-line time, off-line time, and on-line duration • Support 10 operation systems, including Windows, iOS, Android, etc.• Support query based on IP, endpoint quantity, control policy and status etc.• Support the identification of accessed endpoints quantity across layer 3, logging and interference on overrun IP• Redirect page display after custom interference operation• Supports blocking operations on overrun IP Application Control• Over 3,000 applications that can be filtered by name, category, subcategory, technology and risk • Each application contains a description, risk factors, dependencies, typical ports used, and URLs for additional reference• Actions: block, reset session, monitor, traffic shaping• Identify and control cloud applications in the cloud • Provide multi-dimensional monitoring and statistics for cloud applications, including risk category and characteristicsQuality of Service (QoS)• Max/guaranteed bandwidth tunnels or IP/user basis• Tunnel allocation based on security domain, interface, address, user/user group, server/server group, application/app group, TOS, VLAN• Bandwidth allocated by time, priority, or equal bandwidth sharing• Type of Service (TOS) and Differentiated Services (DiffServ) support• Prioritized allocation of remaining bandwidth • Maximum concurrent connections per IP• Bandwidth allocation based on URL category • Bandwidth limit by delaying access for user or IP • Automatic expiration cleanup and manual cleanup of user used trafficServer Load Balancing• Weighted hashing, weighted least-connection, and weighted round-robin• Session protection, session persistence and session status monitoring• Server health check, session monitoring and session protectionLink Load Balancing• Bi-directional link load balancing• Outbound link load balancing includes policy based routing, ECMP and weighted, embeddedISP routing and dynamic detection• Inbound link load balancing supports SmartDNSand dynamic detection• Automatic link switching based on bandwidth,latency, jitter, connectivity, application etc.• Link health inspection with ARP, PING, and DNSVPN• IPSec VPN- IPSEC Phase 1 mode: aggressive and main IDprotection mode- Peer acceptance options: any ID, specific ID, ID indialup user group- Supports IKEv1 and IKEv2 (RFC 4306)- Authentication method: certificate andpre-shared key- IKE mode configuration support (as server orclient)- DHCP over IPSEC- Configurable IKE encryption key expiry, NATtraversal keep alive frequency- Phase 1/Phase 2 Proposal encryption: DES,3DES, AES128, AES192, AES256- Phase 1/Phase 2 Proposal authentication:MD5, SHA1, SHA256, SHA384,SHA512- Phase 1/Phase 2 Diffie-Hellman support: 1,2,5- XAuth as server mode and for dialup users- Dead peer detection- Replay detection- Autokey keep-alive for Phase 2 SA• IPSEC VPN realm support: allows multiple customSSL VPN logins associated with user groups (URLpaths, design)• IPSEC VPN configuration options: route-based orpolicy based• IPSEC VPN deployment modes: gateway-to-gateway, full mesh, hub-and-spoke, redundanttunnel, VPN termination in transparent mode• One time login prevents concurrent logins with thesame username• SSL portal concurrent users limiting• SSL VPN port forwarding module encrypts clientdata and sends the data to the application server• Supports clients that run iOS, Android, andWindows XP/Vista including 64-bit Windows OS• Host integrity checking and OS checking prior toSSL tunnel connections• MAC host check per portal• Cache cleaning option prior to ending SSL VPNsession• L2TP client and server mode, L2TP over IPSEC,and GRE over IPSEC• View and manage IPSEC and SSL VPN connec-tions• PnPVPNIPv6• Management over IPv6, IPv6 logging and HA• IPv6 tunneling, DNS64/NAT64 etc• IPv6 routing protocols, including static routing,policy routing, ISIS, RIPng, OSPFv3 and BGP4+• IPS, Application identification, URL filtering,Access control, ND attack defense, iQoS• Track address detectionVSYS• System resource allocation to each VSYS• CPU virtualization• Non-root VSYS support firewall, IPSec VPN, SSLVPN, IPS, URL filtering• VSYS monitoring and statisticHigh Availability• Redundant heartbeat interfaces• Active/Active and Active/Passive mode• Standalone session synchronization• HA reserved management interface• Failover:- Port, local & remote link monitoring- Stateful failover- Sub-second failover- Failure notification• Deployment options:- HA with link aggregation- Full mesh HA- Geographically dispersed HATwin-mode HA• High availability mode among multiple devices• Multiple HA deployment modes• Configuration and session synchronization amongmultiple devicesUser and Device Identity• Local user database• Remote user authentication: TACACS+, LDAP,Radius, Active• Single-sign-on: Windows AD• 2-factor authentication: 3rd party support,integrated token server with physical and SMS• User and device-based policies• User group synchronization based on AD andLDAP• Support for 802.1X, SSO Proxy• WebAuth page customization• Interface based Authentication• Agentless ADSSO (AD Polling)• Use authentication synchronization based onSSO-monitor• Support MAC-based user authenticationAdministration• Management access: HTTP/HTTPS, SSH, telnet,console• Central Management: Hillstone Security Manager(HSM), web service APIs• System Integration: SNMP, syslog, alliancepartnerships• Rapid deployment: USB auto-install, local andremote script execution• Dynamic real-time dashboard status and drill-inmonitoring widgets• Language support: EnglishFW Throughput (Maximum) (1)IPSec Throughput (Maximum) (2)IMIX Throughput(3)NGFW Throughput (4)Threat Protection Throughput (5)Concurrent Sessions (Maximum)New Sessions/s(6)IPS Throughput (Maximum) (7)Virtual Systems (Default/Max)I/O ModuleMaximum InterfacesMaximum Power Consumption Power SupplyManagement Interfaces Network Interfaces Expansion Module Slot Dimension (W × D × H)WeightCompliance and CertificateSpecificationsSG-6000-X10800Logs & Reporting• Logging facilities: local memory and storage (if available), multiple syslog servers and multiple Hillstone Security Audit (HSA) platforms • Encrypted logging and log integrity with HSA scheduled batch log uploading• Reliable logging using TCP option (RFC 3195) • Detailed traffic logs: forwarded, violated sessions, local traffic, invalid packets, URL etc.• Comprehensive event logs: system and adminis -trative activity audits, routing & networking, VPN, user authentications, WiFi related events• IP and service port name resolution option • Brief traffic log format option• Three predefined reports: Security, Flow and network reports• User defined reporting• Reports can be exported in PDF , Wordl and HTML via Email and FTPStatistics and Monitoring• Application, URL, threat events statistic and monitoring• Real-time traffic statistic and analytics• System information such as concurrent session, CPU, Memory and temperature• iQOS traffic statistic and monitoring, link status monitoring• Support traffic information collection and forwarding via Netflow (v9.0)Module OptionsDescriptionmodule 100GE, 10GE interface moduleQoS service module Security control moduleNetwork Interface4 QSFP28 100GEinterfaces, 8 SFP+ 10Gbinterfaces, transceiver notincluded N/AN/ASlot expansion slot Occupies 1 universal expansion slot expansion slot Occupies 1 universal expansion slot expansion slot Occupies 1 universal expansion slot Weight12.67 lb (5.75 kg)12.56 lb (5.70 kg)7.6 lb (3.45 kg)NOTES:(1) FW Throughput data is obtained under single-stack UDP traffic with 1518-byte packet size;(2) IPSec throughput data is obtained under Preshare Key AES256+SHA-1 configuration and 1400-byte packet size packet; (3) IMIX throughput data is obtained under UDP traffic mix (68 byte : 512 byte : 1518 byte =5:7:1);(4) NGFW throughput data is obtained under 64 Kbytes HTTP traffic with application control and IPS enabled;(5) Threat protection throughput data is obtained under 64 Kbytes HTTP traffic with application control, IPS, AV and URL filtering enabled; (6) New Sessions/s is obtained under TCP traffic;(7) IPS throughput data is obtained under bi-direction HTTP traffic detection with all IPS rules being turned on;(8) At least 3 AC power modules are required for full load operation with AC power, and at least 4 DC power modules are required for full load operation with DC power.Unless specified otherwise, all performance, capacity and functionality are based on StoneOS5.5R7. Results may vary based on StoneOS ® version and deployment.IOM-P100-300IOM-P40-300SWM-300QSM-300SSM-300SCM-300。

数据中心防火墙方案随着信息技术的快速发展,数据中心已经成为企业信息管理的核心。
然而,随着网络攻击的不断增加,如何保障数据中心的安全成为了亟待解决的问题。
其中,数据中心防火墙作为第一道防线,对于保护数据中心的安全具有至关重要的作用。
本文将介绍一种数据中心防火墙方案,以期为相关企业和人员提供参考。
一、需求分析数据中心防火墙方案的需求主要包括以下几个方面:1、高性能:随着数据量的不断增加,数据中心防火墙需要具备高性能的处理能力,能够快速地处理数据流量,避免网络拥堵和延迟。
2、安全性:数据中心防火墙需要具备强大的安全防护能力,能够有效地防止各种网络攻击,如DDoS攻击、SQL注入、XSS攻击等。
3、可扩展性:随着业务的发展,数据中心规模可能会不断扩大,因此防火墙需要具备良好的可扩展性,能够方便地扩展其性能和功能。
4、易管理性:数据中心防火墙需要具备易管理性,以便管理员能够方便地进行配置和管理,同时需要提供可视化的管理界面和日志分析功能。
二、方案介绍针对上述需求,我们提出了一种基于高性能、可扩展、安全性佳、易管理的数据中心防火墙方案。
该方案采用了最新的防火墙技术,具有以下特点:1、高性能:采用最新的ASIC芯片和多核处理器技术,具备超高的吞吐量和处理能力,可以满足大规模数据中心的业务需求。
2、安全性:具备完善的防御机制,包括DDoS攻击防御、IP防欺诈、TCP会话劫持、HTTP协议过滤等,可有效地保护数据中心的网络安全。
3、可扩展性:采用模块化设计,可根据实际需求灵活地扩展性能和功能,支持多种接口卡和安全模块的扩展。
4、易管理性:提供友好的Web管理界面和日志分析功能,支持远程管理和故障排除,方便管理员进行配置和管理。
三、实施步骤以下是数据中心防火墙方案的实施步骤:1、需求调研:了解数据中心的规模、业务需求以及网络架构等信息,为后续的方案设计和实施提供依据。
2、方案设计:根据需求调研结果,设计符合实际需求的防火墙方案,包括硬件配置、安全策略设置、网络拓扑等。
数据中心网络安全中的防火墙配置方法论数据中心网络安全是企业信息安全的重要组成部分。
为了保护数据中心免受网络攻击和数据泄露的威胁,防火墙配置起着关键的作用。
防火墙配置方法论的制定和实施对于确保数据中心的安全至关重要。
本文将讨论数据中心网络安全中的防火墙配置方法论。
一、数据中心网络安全的背景数据中心储存了企业的重要数据和业务关键应用程序,所以保护数据中心的网络安全至关重要。
数据中心的网络安全面临各种威胁,包括网络攻击、恶意软件、数据泄露等。
因此,在建设和管理数据中心网络时,必须采取措施保护其安全性和完整性。
二、防火墙在数据中心网络安全中的作用防火墙是数据中心网络安全的基石。
它是一种网络安全设备,通过过滤和监控网络流量,来保护内部网络免受恶意攻击和未授权访问。
防火墙可以根据预设的安全策略和规则对传入和传出的数据进行检查,确保只有符合安全规则的流量才能通过。
防火墙的配置方法论对于实施有效的防火墙策略至关重要。
三、防火墙配置方法论的制定1. 确定安全需求:在制定防火墙配置方法论之前,需明确数据中心的安全需求。
根据企业的具体情况,确定数据中心是否需要遵循特定的合规要求,譬如PCI DSS(Payment Card Industry Data Security Standard)和GDPR(General Data Protection Regulation)等。
同时,还需要根据数据中心的业务需求,确定允许通信和访问的范围。
2. 制定安全策略:根据数据中心的安全需求,制定相应的安全策略。
安全策略包括定义允许通过防火墙的数据流量、禁止或阻止的数据流量、身份验证规则、安全审计策略等。
制定完善的安全策略可以限制网络攻击和恶意活动,并提升数据中心的整体安全性。
3. 选择合适的防火墙类型:选择适合数据中心网络的防火墙类型。
根据需求,可以选择传统的硬件防火墙、软件防火墙、云防火墙等。
不同的防火墙类型有不同的安全功能和特性,需根据实际需求选择最佳方案。
2) 连接数评估连接在状态防火墙中是一个很重要的概念,与连接相关的性能指标对评估防火墙非常重要。
这些指标包括并发连接数、新建连接速率。
l 并发连接数的测试并发连接是一个很重要的指标,它主要反映了被测设备维持多个会话的能力。
关于此指标的争论也有很多。
一般来说,它是和测试条件紧密联系的,但是这方面的考虑有时会被人们忽略。
比如,测试时采用的传输文件大小就会对测试结果有影响。
例如,如果在传输中应用层流量很大的话, 被测设备将会占用很大的系统资源去处理包检查,导致无法处理新请求的连接,引起测试结果偏小;反之测试结果会大一些。
所以没有测试条件而只谈并发连接数是难以定断的。
从宏观上来看,这个测试的最终目的是比较不同设备的“资源”,也就是说处理器资源和存储资源的综合表现。
目前市场上出现了大家盲目攀比并发连接数的情况。
事实上,并发几十万的连接数应该完全可以满足一个电信级数据中心的网络服务需求了,对于一般的企业来讲, 甚至几千个并发连接数还绰绰有余。
并发连接总数能由仪表自动测试得出结果,减少了测试所用的时间和人力,这类仪表目前很多,常见的有Spirent的 Avalanche、IXIA的IxLoad以及BPS等。
l 新建连接速率这个指标主要体现了被测设备对于连接请求的实时反应能力。
对于中小用户来讲,这个指标显得更为重要。
可以设想一下,当被测设备可以更快的处理连接请求,而且可以更快传输数据的话,网络中的并发连接数就会倾向于偏小,从而设备压力也会减小,用户感受到的防火墙性能也就越好。
Avalanche、IXLOAD以及BPS等测试工具都可以测试新建连接速率,帮助使用者搜索到被测设备能够处理的峰值,测试原理基本都是相同的。
2. 模拟真实应用环境进行性能指标测试如果能够100%模拟用户的实际应用环境对防火墙性能进行测试,那么防火墙选型这类活动将变得非常简单,而且防火墙性能指标将变得更加有意义。
但是模拟真实应用环境并不是简单的事情。