计算机网络课后作业以与答案(中英文对照)
- 格式:doc
- 大小:41.02 KB
- 文档页数:11

计算机网络(第5版)课后习题答案完整版《计算机网络》课后习题答案<完整版>第一章概述1-1 计算机网络向用户可以提供哪些服务?答:计算机网络向用户提供的最重要的功能有两个,连通性和共享。
1-2 试简述分组交换的特点答:分组交换实质上是在“存储——转发”基础上发展起来的。
它兼有电路交换和报文交换的优点。
分组交换在线路上采用动态复用技术传送按一定长度分割为许多小段的数据——分组。
每个分组标识后,在一条物理线路上采用动态复用的技术,同时传送多个数据分组。
把来自用户发端的数据暂存在交换机的存储器内,接着在网内转发。
到达接收端,再去掉分组头将各数据字段按顺序重新装配成完整的报文。
分组交换比电路交换的电路利用率高,比报文交换的传输时延小,交互性好。
1-3 试从多个方面比较电路交换、报文交换和分组交换的主要优缺点。
答:(1)电路交换电路交换就是计算机终端之间通信时,一方发起呼叫,独占一条物理线路。
当交换机完成接续,对方收到发起端的信号,双方即可进行通信。
在整个通信过程中双方一直占用该电路。
它的特点是实时性强,时延小,交换设备成本较低。
但同时也带来线路利用率低,电路接续时间长,通信效率低,不同类型终端用户之间不能通信等缺点。
电路交换比较适用于信息量大、长报文,经常使用的固定用户之间的通信。
(2)报文交换将用户的报文存储在交换机的存储器中。
当所需要的输出电路空闲时,再将该报文发向接收交换机或终端,它以“存储——转发”方式在网内传输数据。
报文交换的优点是中继电路利用率高,可以多个用户同时在一条线路上传送,可实现不同速率、不同规程的终端间互通。
但它的缺点也是显而易见的。
以报文为单位进行存储转发,网络传输时延大,且占用大量的交换机内存和外存,不能满足对实时性要求高的用户。
报文交换适用于传输的报文较短、实时性要求较低的网络用户之间的通信,如公用电报网。
(3)分组交换分组交换实质上是在“存储——转发”基础上发展起来的。

Chapter 5: Data CodingFill In the Blank5-1.It is much easier for a machine to process a code if all the characters in the code have _____.5-2.The number of possible combinations or characters in a coding system are called _____.5-3.The minimum number of bits that would be required to encode only the 26 characters of the alphabet is _____.5-4.The three different groups of character assignments that are normally made in a coding system are _____, _____, and _____.5-5.The coding system that has enough bit combinations to encode all of the characters in all of the worlds languages is called _____.5-6.Three major types of data compression are called _____, _____, and _____. 5-7.Arguably, the most important data coding scheme because it is the mostly widely used is _____.5-8.In an even parity system, a 1 bit is added to a character’s code when necessary to make the total number of 1 bits representing the character an _____ number.5-9.Character compression is also known as _____.5-10. Character stripping removes the leading and trailing _____ characters from a message and adds them back at the receiving end.5-11.R un length encoding replaces _____ characters or repetitive groups of characters with a different, much shorter group of characters.5-12. A measure of how few bits are required to accurately convey the meaning of a character is called _____ _____.5-13. Bits that are used to determine the code points in a code are called _____ _____.5-14. The _____ code is an 8-bit code that has 256 code points.True or False5-1.The term binary digit is abbreviated bit.5-2.Machines cannot send Morse code because the coded characters have different numbers of code elements.5-3.It is more difficult for a machine to process a code if all of the bits are of the same duration.5-4.When even parity is used, a 0 bit is added, if necessary, to make the total number of 0 bits in the character an even number.5-5.The escape character in a coding system is a different character than the one that is generated when you press the ESC key on the keyboard of a PC.5-6.ASCII is a 7-bit code.5-7.Unicode provides enough code points so that all characters in all languages of the world have a unique 16-bit code point.5-8.Code efficiency is a measure of how many extra bits are used beyond those required to convey the meaning of a character.5-9.Data compression is the process of reducing the number of bits used to represent a character, or reducing the number of characters before they are transmitted.5-10.C haracter stripping is the process of removing control characters from a message before it is transmitted.5-11.T he binary digits are 1 and 2.5-12.A code is a predetermined set of symbols that have variable meanings.5-13.M orse code is not considered a binary code, because its two elements are of different length.5-14.A binary code works well for machines communicating by electrical means because the 1 bits and 2 bits can be represented by a current flow that is either on or off.5-15.F or transmission efficiency, it is ideal to have a coding system that uses a minimum number of bits to represent each character.5-16.M ost coding systems include a technique called an escape character.5-17.T he necessity to support escape characters complicates the design of equipment that is to code and decode the data.5-18.T he ASCII code is the most widely used code in computers and communications networks today.5-19.U nicode is a 16-bit character code.Multiple Choice5-1. Characters that control the positioning of information on a workstation screen or paper are called _____.a. page control charactersb. format effector charactersc. device control charactersd. screen control characterse. a and b5-2. It is much easier for a machine to process a code if the code has the following attributes: _____.a. it is a true binary codeb. all of the characters have the same number of bitsc. all of the bits are perfectly formedd. all of the bits are the same duratione. a and cf. All of the above.5-3. The unique sequence of bits assigned to represent the various characters of a code are called _____.a. code pointsb. character assignmentsc. control charactersd. character algorithmse. None of the above.5-4.The purpose of escape characters is to _____.a. allow a program to abort a message prematurelyb. implement a priority system by allowing one message to be prematurelyended so another can be sent on the circuitc. act as an alternate escape control character when more than 8 bits areneededd. indicate that the characters that follow are to be interpreted as having analternate meaninge. indicate that a PDU has been received correctly5-5. The ASCII code is also known as the _____.a. International Telegraph Alphabet 5b. extended ASCII codec. 8-bit coded. PC codee. EBCDIC code5-6. The EBCDIC code _____.a. was developed by IBMb. is an 8-bit codec. has 256 code pointsd. is used on older IBM mainframe computerse. All of the above.f. None of the above.5-7. Unicode _____.a. is a 16-bit codeb. was developed by a group of companiesc. supports the characters of all languagesd. All of the above.e. None of the above.5-8. Code efficiency is calculated _____.a. by minimizing the number of bits transmitted for a given messageb. by dividing the information bits by the total number of bits in a characterc. by dividing the total number of bits by the information bits in a characterd. by measuring the error rate at the receiving end of a transmission5-9. Three major types of data compression are _____.a. character removal, run length encoding, and bit compressionb. bit stripping, double clocking, and character strippingc. character compression, Huffman coding, and character strippingd. character stripping, run length encoding, and character compressione. over clocking, transmission digitizing, and double ACKing5-10. A 10-bit code could represent how many characters?a. 100b. 210 -1c. 29d. 512e. 2105-11.The number of possible combinations or characters in a coding system is called the _____.a. character assignmentb. code pointsc. control characterd. code limite. binary code5-12.Many coding systems include an extra bit, called a _____ , for checking purposes.a. parity bitb. padding bitc. control bitd. binary digite. checking bit5-13.When an ESC character is sent as a part of the data, it means that _____.a. the transmission is being abortedb. this is the end of the transmissionc. the characters that follow are to be interpreted as having an alternate meaningd. the characters that follow are encryptede. the transmission should be ignored5-14. Graphic characters _____.a. can be displayed on a workstation screenb. are special characters only used by graphic artistsc. are only present in specialized code systemsd. can also be used as format effector characters5-15Code conversion _____.a. changes one character to another for security purposesb. changes the characters in one coding system to those of another coding systemc. can be readily performed by a computerd. All of the above.e. b and cChapter 6: Data Communication FundamentalsFILL IN THE BLANK6-1. The three attribute s of a sine wave are its _____ , _____ , and _____.6-2. The FM radio band in the United States extends from 88 MHz to 108 MHz. Its bandwidth is _____.6-3. A signal drop of 10 dB represents a drop in power of _____times.6-4. A radio signal with a frequency of 101 MHz falls within the _____radio band.6-5. Speech with frequencies above _____is attenuate d and not transmitted through the public telephone network.6-6. Changing a communication signal by alter ing its amplitude, frequency, or phase is called _____.6-7. The unit of signaling rate on a communication circuit is called _____.6-8. The unit of measure of a circuit's data carrying rate is called _____6-9. Sending a tribit on a circuit requires _____(how many) unique signal changes to be transmitted?6-10. A circuit that allows transmission in one direction only is called a _____ circuit.6-11. A circuit that allows transmission in either direction but not at the same time is called a _____circuit.6-12. A circuit that allows transmission in both directions simultaneously is called a _____circuit.6-13. A circuit that allows all of the bits in a character to be transmitted simultaneously is called a _____circuit.6-14. A circuit in which the bits of a character are transmitted one after the other on a single communication path is called a _____circuit.6-15. The mechanism by which character synchronization occurs in asynchronous transmission is called _____and _____bits.6-16. The means by which the receiver knows which bits to group together to form a character is called _____.6-17. When each block of data to be transmitted is surrounded with synchronizing and other control characters the transmission is called _____.6-18. When each character to be transmitted is surrounded with start and stop bits, the transmission is called _____.6-19. The _____condition is the idle condition on a line. Conventionally it is the same as the signal for a 1 bit.6-20. The purpose of the _____in synchronous transmission is to maintain synchronization between the transmitting node and the receiving node.6-21. _____modulation is better suited for high-speed analog transmission because the receiver more easily detects changes in _____than changes in amplitude or frequency.6-22. _____equalizers assume that the circuit meets a n average set of loss, noise, and distortion parameter s, and shape the transmitted signal accordingly.6-23. _____equalizers examine the actual parameters of the circuit being used, and shape the signal to match its specific characteristics.6-24. Modems that use the V.34 standard use a sophisticated modulation technique called _____, and they assume that most of the actual transmission will occur on _____circuits.6-25. High-speed modems achieve a high throughput rate by using sophisticated modulation and __________techniques.6-26. A _____ensures that the signal entering a digital circuit has properly shaped, square pulses, and is precisely timed.6-27. The time it takes the modems on an HDX circuit to reverse their function –the time for the transmitting modem to switch to being the receiver, and the receiving modem to switch to being the transmitter—is called _____.6-28. The advantages of _____transmission over _____transmission include better data integrity; higher capacity circuits; easier integration of voice, data and other signals; better security and privacy; and lower cost.6-29. The type of digital modulation that takes 8,000 samples per second but uses only 4 bits per sample to code the difference between the values of two samples is called _____.6-30. An _____converts analog signals to a digital format.6-31. The difference between the actual value (height) of an analog signal and the nearest integer value, which is assigned when the signal is digitized, is called_____.6-32. When the number of data bits in a character is divided by the total number of bits required to transmit the character, the __________is being calculated. TRUE OR FALSE6-1. Signaling is the propagation of a signal on a medium.6-2. Playing the A key above middle C on a piano results in a digital signal that has 880 pulses per second.6-3. Sound waves, electrical waves, and electromagnetic waves have essentially different characteristics.6-4. A digital signal level is measured in decibels.6-5. The loss of signal strength between two points on a communication circuit is called attenuation.6-6. The amplitude and phase of a voice signal remain constant while its frequency changes.6-7. ADPCM is accomplished by shifting each channel to a different part of the frequency spectrum.6-8. The speed of a circuit is measured in baud.6-9. A 2,400 baud signal can carry data at a maximum rate of 7,200 bps.6-10. When 2 bits of information are coded into one signal change, they are called bi-bits.6-11. The most common digital signals are unipolar.6-12. When transmitting digital signals on an analog circuit, a modem is used.6-13. An analog signal that has been digitized can be closely restored to its original analog shape by a D/A converter.6-14. PCM is the ITU-T’s recommended method for digitizing voice at 32 Kbps. 6-15. In a modem, equalizer circuitry compensates for the variability of the actual transmission line used.6-16. Line turnaround time in a modem can be a significant part of the total transmission time.6-17. Modems can never handle full-duplex transmission.6-18. Phase modulation is the technique of chang ing a digital signal’s phase in order to modulate it.6-19. V.34-bis modems assume that most data transmission occurs on digital lines.6-20. The transmission speed between a pair of V.90 modems is symmetric.6-21. Cable modems for each CATV system are unique.6-22. Modem eliminator s are a low-cost alternative to modems on LAN circuits.6-23. There are very few practical uses for simplex transmission.6-24. Parallel mode transmission is widely used on WANs to achieve high throughput.6-25. Asynchronous transmission is widely used today.6-26. Start bits precede every data block in synchronous transmission.6-27. To jam a spread spectrum signal, one simply broadcasts a jamming signal on the spread spectrum signal’s carrier frequency.MULTIPLE CHOICE6-1. The reasons that digital transmission is superior to analog transmission are _____.a. better data integrityb. higher capacityc. easier integrationd. better security and privacye. lower costf. All of the above.g. only a, b, c, and d6-2. A modem is a form of a _____.a. A/D converterb. D/A converterc. codecd. DTEe. None of the above.f. a and b6-3. The three attributes of an analog signal discussed in the chapter are _____.a. frequency, decibels, and modulationb. phase, frequency, and amplitudec. amplitude, carrier, and sined. bit rate, speed, and error ratee. unipolarity, quantization, and equilibrium6-4. Parallel transmission occurs _____.a. during spread spectrum transmissionb. when a PC sends data to a printer using a serial cablec. on most WAN circuitsd. All of the above.e. None of the above.6-5. Differential Manchester coding _____.a. is often used on WANsb. is almost never usedc. is subservient to Manchester codingd. requires an analog circuit to work properlye. None of the above.6-6. The most widely used interface standard between PCs and modems is _____.a. point-to-pointb. USBc. RS-232-Dd. RS-232-Ce. X.256-7. The X.21 interface standard _____.a. is a replacement for RS-232-Cb. defines the interface to a digital circuitc. uses a PL-259 connectord. All of the above.e. None of the above.6-8. A network interface card _____.a. provides the interface from a PC to a networkb. provides the interface from one network to anotherc. provides the interface from a modem to a networkd. converts signals from analog to digitale. None of the above.6-9. When two modems send signals to each other for the process of establishing transmission parameters, it is called _____.a. synchronizingb. call setupc. call establishmentd. MOST (acronym for modem startup)e. handshaking6-10. Hertz is the unit of measure for _____.a. baudb. bit ratec. trellis code modulationd. cycles per seconde. data ratef. None of the above.6-11. The difference between the exact height of an analog signal and the nearest integer value when a digitizing sample is taken is called _____.a. digitizing discrepancyb. digitizing errorc. quantizing noised. digitizing discernmente. a and cf. b and c6-12. QAM uses a combination of _____and _____to generate quadbits.a. phase changes and relative amplitudesb. phase changes and dibitsc. phase changes and frequency changesd. amplitude changes and frequency changese. amplitude changes and dibitsChapter 7: Data Link Control ProtocolsFILL IN THE BLANK7-1. A set of rules that define the exact format of messages exchanged between computers or between computers and people is called a _____.7-2. Data link protocols are necessary so that all of the devices on the network are operating by the same set of rules and are able to _____with each other.7-3. The part of a protocol consisting of the rules that specify the way the receiving terminal signals the sending terminal if it has received data correctly, how and under what circumstances the line will be turned around, and whether the receiving terminal can accept more data is called _____.7-4. The part of the protocol consisting of rules specifying what happens when an error is detected, what to do if communications suddenly and unexplainably cease, and the way communications are reestablished after they are broken is called _____.7-5. The part of a protocol consisting of rules for ending the communications under normal and abnormal circumstances is called _____.7-6. The ability of data terminal equipment (DTE) to be able to transmit and receive any bit pattern as data is called _____.7-7. Predetermined communication parameters are those that are set _____by switches or specified as parameters in software.7-8. When a central or control station asks each station on the circuit or network if it has traffic to send, it is using a line control technique called _____.7-9. When any station that has traffic looks to see if the circuit is free, and if it is, begins sending its traffic the line control technique is called _____.7-10. In a polling system, one way that priority can be given to a terminal is by listing its address in the polling list _____.7-11. The _____of a message contains and conveys information about the message, such as the destination node’s address, a sequence number, and perhaps a date and time.7-12. BISYNC is defined to only support the 6-bit transcode (SBT), EBCDIC, and _____.7-13. Character synchronization is accomplished in BISYNC by sending _____ characters at the beginning and periodically in the middle of each transmission.7-14. Compared to BISYNC, DDCMP and other byte-count protocols implement transparency in a much more _____manner.7-15. The HDLC ___ field is used to mark the beginning and ending of frames.7-16. The technique that ensures a flag’s uniqueness by not allowing any other sequence of six consecutive 1 bits in the data stream is called _____.7-17. A protocol that is primarily used by PC workstations to send IP overdial-up lines, typically when dial ing in to an ISP for connection to the Internet, is called _____.7-18. The _____protocol was developed by IBM and then generalize d to become HDLC.7-19. SDLC is a _____of HDLC.7-20. SDLC is a subset of _____.7-21. A _____changes one protocol to another, when, for example, a message is sent between two networks that use different protocols.7-22. A sophisticated check character at the end of each block of data is called a _____.7-23. A technique used to ensure that a fast transmitting node does not send data faster than a receiving node can receive and process it is called _____.7-24. The flow control technique that allows multiple frames to be in transit on the line at one time is called _____.TRUE OR FALSE7-1. Data link protocols are concerned with the transmission of data through an entire network.7-2. All protocols use the same bit patterns as control characters.7-3. Data transparency allows a protocol to be able to transmit and receive any bit patterns as data.7-4. A protocol is implemented by transmitting certain bit patterns or characters on the communication circuit.7-5. The code used for the data is independent of the protocol being used.7-6. Because of collision s, contention systems are rarely used for line access.7-7. Poll ing systems require several stations on the circuit to act as master stations.7-8. Hub polling is the most common implementation of a polling system.7-9. Polling systems are dependent on the data code being used.7-10. Token passing systems require one station on the circuit to take responsibility to ensure that there are always multiple tokens circulating on the circuit.7-11. Data messages normally consist of three parts: the header, text, and trailer. 7-12. The ACK character normally acknowledges the receipt of a block of data. 7-13. Stop-and-wait flow control is inherently efficient because of its simplicity. 7-14. Stop-and-wait flow control allows multiple blocks of data to be in transit on the line at one time.7-15. PPP has largely replaced the SLIP protocol because it has better error detection.7-16. KERMIT is error checked but is a very slow protocol.7-17. A bit-oriented protocol uses multiple control characters to mark the start and end of parts of a message.7-18. HDLC is a bit-oriented protocol.7-19. SLDC is a byte-count-oriented protocol.7-20. The best known bit-oriented protocol is BISYNC.7-21. SDLC was an outgrowth of the original work on HDLC.7-22. SDLC operates in one of three modes; however, one mode is rarely used. 7-23. The basic operational unit for HDLC is a PDU.7-24. HDLC uses a FRA character to mark the beginnings and ends of frames. 7-25. BISYNC supports only selected data codes.7-26. BISYNC supports transparency.7-27. DDCMP has largely been replaced by HDLC.7-28. Go-back-n is an implementation of sliding window flow control.7-29. The LAP protocols are variant s of HDLC.7-30. PPP is a widely used synchronous protocol for dialing into the Internet through an ISP.MULTIPLE CHOICE7-1. In HDLC, when a 0 bit is inserted after all strings of five consecutive 1 bits, the term applied is _____.a. zeroingb. bit stuffingc. synchronizingd. oneinge. string breaking7-2. When two stations on a circuit transmit at the same time, a(n)_____occurs.a. altercationb. divisionc. pollingd. bit stuffinge. collision7-3. In order to know what stations to poll and in what sequence, the master station uses a _____.a. message headerb. polling listc. start of header characterd. polling PDAe. cyclic redundancy check7-4. When a receiver must acknowledge every block of data before the next block is sent, the _____type of flow control is being used.a. stop-and-waitb. stop-and-checkc. stop-and-flopd. sliding framee. sliding window7-5. The name of the flow control protocol in which the sending station, on receipt of a NAK, resends the damaged or out of sequence frame and all frames after it is _____.a. selective rejectb. TCPc. selective repeatd. send all before ne. HDLC7-6. HDLC is an example of _____.a. sliding window flow controlb. a serial line interface protocolc. an asynchronous protocold. All of the above.e. None of the above.7-7. When an HDLC node receives a flag character, it knows that _____.a. an error has occurredb. it should signal the sender to stop sending trafficc. a frame is beginning or endingd. it should switch to transparent modee. None of the above.7-8. HDLC’s information frames _____.a. are used to send an NAK when a frame is received incorrectlyb. are used to establish the way the protocol will proceedc. are used to send information from one node to a router for flow controld. contain the data field that holds the information being transmittede. are not used in ABM mode7-9. The part of a message that contains the destination address is called the_____.a. headerb. address PDUc. textd. trailere. flag7-10. Software or hardware that changes one protocol to another is called a_____ .a. CODECb. protocol converterc. modemd. routere. encryptor7-11. Contention systems work best _____.a. on circuits that have only more than two DTEsb. when the speed of the circuit is relatively fastc. on circuits that have heavy message trafficd. All of the above.e. None of the above.7-12. Desirable attributes for a data link protocol to have are _____.a. transparencyb. efficiencyc. bit linearityd. a, b, and ce. a and b7-13. Techniques to ensure that a fast transmitting node does not send data faster than the receiving node can receive and process it are called _____ .a. token passingb. flow controlc. parity checkingd. cyclic redundancy checkinge. error control7-14. The LAPD protocol is used _____.a. between an X.25 DTE and a packet switching networkb. on an ISDN D channelc. on frame relay networksd. on value added networkse. as a substitute for TCP/IP7-15. Go-back-n and selective repeat are two common implementations of _____.a. bit oriented protocolsb. byte protocolsc. byte-count oriented protocolsd. sliding window flow controle. transmission control protocolsChapter 8: Transmission MediaFILL IN THE BLANK8-1. A type of media that provides some type of physical path, such as wire, cable, or optical fiber, along which the signal moves from end to end is called _______ or guided media.8-2. Air is an example of _______ media.8-3. Twisted pair wire is an example of _______ media.8-4. The best media to use in homes and offices where costs must be kept low and bandwidth requirements are moderate is ____.8-5. The most appropriate media to use when there is a need for very high bandwidth and high security is _____.8-6. The most appropriate media to use when there is a need for high bandwidth and to broadcast to a wide area is ____.8-7. Wire containing at least three twists per foot and that is about the same as normal telephone cable installed in most office buildings is called _____.8-8. _____ cable normally contains four pairs of wires and is the type that is most commonly being installed in new homes and businesses, particularly when it is known that a computer network will be used.8-9. The shielding in shielded twisted pair wire provides a degree of _____ _____ in electrically noisy environments.8-10. _____ is advantageous when tap s in the cable need to be made—it is easier to tap than optical fiber.8-11. The characteristic of _____ include: high bandwidth, difficult to tap and splice; not subject to electrical interference, cable is very small diameter and lightweight.8-12. A _____ is required to operate a microwave transmitter.8-13. _____ _____ is the delay that occurs because light and radio signals only travel at 186,000 miles per second.8-14. Satellites in _____ orbits circle the earth at 22,300 miles.8-15. Satellites in _____ orbits are approximately 6,000 miles high.8-16. _____ works by modulating a laser light beam instead of broadcasting a radio wave.8-17. _____ is a fiber that has a glass core approximately 9 microns in diameter. 8-18. Data are placed on an optical fiber with a light source, either an LED or a _____.8-19. When UTP is used in a data application it is normally terminate d with a _____ jack.8-20. A type of satellite commonly used to send television programming into homes is called a _____.TRUE OR FALSE8-1. Optical fiber is an example of an unguided medium.8-2. Guided media are also known as wireless media.8-3. Wireless media are the most common media used today.8-4. Optical fiber emits an electro-optical field when carrying communications signals.8-5. CAT 3 cable is most frequently used for telephone transmission in older buildings.8-6. CAT 5 cable is commonly being installed in new homes and businesses.8-7. An advantage of UTP wire is its relatively low cost.8-8. Coaxial cable can be tapped easily.8-9. Optical fiber can be tapped easily.。

Chapter11-11.What are two reasons for using layered protocols?(请说出使用分层协议的两个理由)答:通过协议分层可以把设计问题划分成较小的易于处理的片段。
分层意味着某一层的协议的改变不会影响高层或低层的协议。
1-13. What is the principal difference between connectionless communication and connection-oriented communication?(在无连接通信和面向连接的通信两者之间,最主要的区别是什么?)答:主要的区别有两条。
其一:面向连接通信分为三个阶段,第一是建立连接,在此阶段,发出一个建立连接的请求。
只有在连接成功建立之后,才能开始数据传输,这是第二阶段。
接着,当数据传输完毕,必须释放连接。
而无连接通信没有这么多阶段,它直接进行数据传输。
其二:面向连接的通信具有数据的保序性,而无连接的通信不能保证接收数据的顺序与发送数据的顺序一致。
1-20. A system has an n-layer protocol hierarchy. Applications generate messages of length M bytes. At each of the layers, an h-byte header is added. What fraction of the network bandwidth is filled with headers?(一个系统有n层协议的层次结构。
应用程序产生的消息的长度为M字节。
在每一层上需要加上一个h字节的头。
请问,这些头需要占用多少比例的网络带宽)答:hn/(hn+m)*100%1-28. An image is 1024 x 768 pixels with 3 bytes/pixel. Assume the image is uncompressed. How long does it take to transmit it over a 56-kbps modem channel? Over a 1-Mbps cable modem? Over a 10-Mbps Ethernet? Over 100-Mbps Ethernet?(一幅图像的分辨率为1024 x 768像素,每个像素用3字节来表示。

计算机网络第五版答案完整版Computers have become an integral part of our lives, and computer networking plays a crucial role in connecting various devices and enabling communication between them. In the fifth edition of the book "Computer Networks," the authors provide comprehensive answers and solutions to various exercises and questions, giving readers a complete understanding of the concepts and principles of computer networking.1. Introduction to Computer NetworksComputer networks are essential for transmitting data and enabling communication between devices. In this chapter, the authors explain the basics of networks, including the OSI model, network topology, and types of networks. They also provide answers to exercises that help readers grasp the fundamental concepts of computer networking.2. Physical LayerThe physical layer is responsible for transmitting raw bits over a communication channel. The authors cover topics such as analog and digital signals, transmission media, and modulation techniques. Through detailed explanations and examples, readers gain a solid understanding of the physical layer's functions and mechanisms.3. Data Link LayerThe data link layer ensures reliable data transfer between two connected nodes. This chapter focuses on topics like error detection and correction, flow control, and media access control. The authors provide accurateanswers to questions related to these concepts, enabling readers to comprehend the data link layer's role in establishing error-free communication.4. Network LayerThe network layer facilitates the delivery of data packets across multiple networks. Addressing, routing algorithms, and internet protocols are among the key topics discussed in this chapter. By examining the provided answers, readers can enhance their knowledge of the network layer's functionalities and protocols.5. Transport LayerThe transport layer provides end-to-end communication between applications running on different hosts. This chapter explores topics like multiplexing, demultiplexing, reliable data transfer protocols, and congestion control. The authors offer complete solutions to exercises, allowing readers to grasp the complexities and mechanisms of the transport layer.6. Application LayerThe application layer enables network applications to communicate with each other. This chapter covers topics such as domain name system (DNS), email protocols, and World Wide Web (WWW) protocols. The authors present accurate and detailed answers, enabling readers to understand the application layer's role in facilitating various network services.7. Network SecurityNetwork security is essential to protect data from unauthorized access and malicious activities. This chapter discusses topics like symmetric and asymmetric encryption, public key infrastructure (PKI), and network security protocols. The authors provide comprehensive answers, helping readers to comprehend the importance of network security and the techniques used to safeguard data.8. Multimedia NetworkingIn the modern era, multimedia applications require robust networking capabilities. This chapter delves into topics such as streaming and real-time applications, multimedia protocols, and quality of service (QoS) mechanisms. By examining the provided answers, readers can gain a deeper understanding of the challenges and solutions in multimedia networking.9. Network ManagementEfficient network management is crucial for ensuring the smooth operation of computer networks. This chapter covers topics like Simple Network Management Protocol (SNMP), network monitoring, and network troubleshooting. The authors provide accurate and comprehensive answers, allowing readers to learn about the tools and techniques used in network management.By providing complete and accurate answers to exercises, the fifth edition of "Computer Networks" equips readers with the knowledge and understanding required to master the field of computer networking. The authors' attention to detail, clear explanations, and concise yet informative solutions make this book an invaluable resource for students, professionals, and anyone interested in computer networks.。
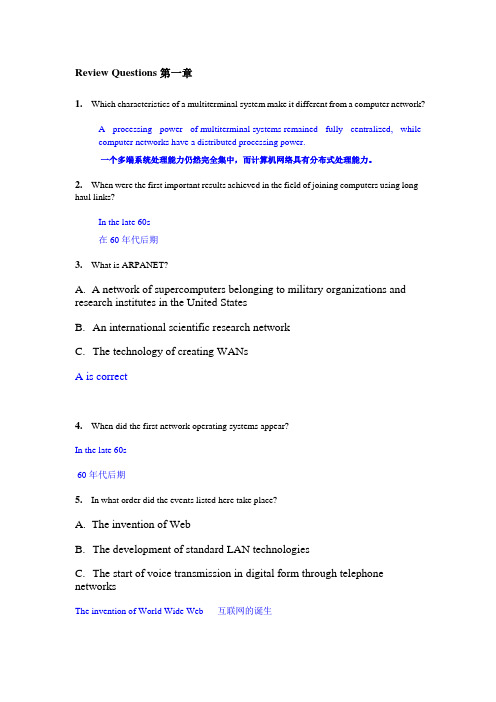
Review Questions第一章1.Which characteristics of a multiterminal system make it different from a computer network?A processing power of multiterminal systems remained fully centralized, whilecomputer networks have a distributed processing power.一个多端系统处理能力仍然完全集中,而计算机网络具有分布式处理能力。
2.When were the first important results achieved in the field of joining computers using long-haul links?In the late 60s在60年代后期3.What is ARPANET?A.A network of supercomputers belonging to military organizations and research institutes in the United StatesB.An international scientific research networkC.The technology of creating WANsA is correct4.When did the first network operating systems appear?In the late 60s60年代后期5.In what order did the events listed here take place?A.The invention of WebB.The development of standard LAN technologiesC.The start of voice transmission in digital form through telephone networksThe invention of World Wide Web互联网的诞生6.Which of the events stimulated LAN development?Appearance of large-scale integrated circuits (LSI devices) resulted in invention of microcomputers which in its turn stimulated a research activity in the area of local computer networks (LANs). The adoption of personal computers was a powerful incentive for the development of LANs.大规模集成电路(LSI器件出现)导致这反过来刺激了研究活动在本地计算机网络(LAN)的微型计算机的发明。

Solution of Selected Exercises from the End of Chapter ExercisesChapter 1 - Introduction And Overview1.4 To what aspects of networking does data communications refer? Answer: Data communications refers to the study of low-level mechanisms and technologies used to send information across a physical communication medium, such as a wire, radio wave, or light beam.b5E2RGbCAP1.5 What is packet-switching, and why is packet switching relevant tothe Internet?Answer: Packet switching divides data into small blocks, called packets, and includes an identification of the intended recipient in each packet. Packet switching changed networking in a fundamental way, and provided the basis for the modern Internet. Packet switching allows multiple senders to transmit data over a shared network. p1EanqFDPw1.8 What is a communication protocol? Conceptually, what two aspects ofcommunication does a protocol specify?Answer: A communication protocol refer to a specification for network communication.Major aspects of a protocol are syntax (format> and semantics (meaning> of the protocol. DXDiTa9E3d1.9 What is a protocol suite, and what is the advantage of a suite? Answer:protocols are designed in complete, cooperative sets called suites or families, instead of creating each protocol in isolation.Each protocol in a suite handles oneaspect of communication。

Chapter 1 Computer Networks and the Internet networks use VC. numbers to forward packets toward their1.The ( ) is a worldwide computer network, that is, a network that destination.interconnects millions of computing devices throughout the world. D datagram networks use VC. numbers and virtual-circuit networks ppt3 use destination addresses to forward packets toward their destination.A public Internet 9.In the following options, which one is not a guided media? ( )B Intranet A twisted-pair wireC switch net B fiber opticsD television net C coaxial cable2.Which kind of media is not a guided media? ( ) D satelliteA twisted-pair copper wire 10.Processing delay does not include the time to ( ).B a coaxial cable A examine the packet’s headerC fiber optics B wait to transmit the packet onto the linkD digital satellite channel C determine where to direct the packetD check bit-error in the packet3.Which kind of media is a guided media? ( )11.In the following four descriptions, which one is correct? ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN A The traffic intensity must be greater than 1.B The fraction of lost packets increases as the traffic intensity decreases.C If the traffic intensity is close to zero, the average queuing delay 4.The units of data exchanged by a link-layer protocol are called ( ).will be close to zero. A FramesD If the traffic intensity is close to one, the average queuing delay B Segmentswill be close to one. C Datagrams12.The Internet’s network layer is responsible for moving network-layer D bit streamspackets known as ( ) from one host to another. 5.Which of the following option belongs to the circuit-switched networks?A frame ( )B datagram A FDMC segment B TDMD message C VC networks13.The protocols of various layers are called ( ). D both A and BA the protocol stack 6.( )makes sure that neither side of a connection overwhelms the otherB TCP/IPside by sending too many packets too fast.C ISPA Reliable data transferD network protocolB Flow control14.There are two classes of packet-switched networks: ( ) networks andC Congestion controlvirtual-circuit networks.D Handshaking procedureA datagram7.( ) means that the switch must receive the entire packet before it canB circuit-switchedbegin to transmit the first bit of the packet onto the outbound link.C television A Store-and-forward transmissionB FDMD telephoneC End-to-end connection 15.Access networks can be loosely classified into three categories:D TDM residential access, company access and ( ) access.8.Datagram networks and virtual-circuit networks differ in that ( ).A cabledA datagram networks are circuit-switched networks, andB wirelessvirtual-circuit networks are packet-switched networks.B datagram networks are packet-switched networks, andC campusD city areavirtual-circuit networks are circuit-switched networks.Question 16~17 C datagram networks use destination addresses and virtual-circuit1D distributed applicationsSuppose, a is the average rate at which packets arrive at the queue, R is24.The Internet provides two services to its distributed applications: a the transmission rate, and all packets consist of L bits, then the trafficintensity is ( 16 ), and it should no greater than ( 17 ). connectionless unreliable service and () service.A flow control16. A LR/aB connection-oriented reliableB La/RC congestion controlC Ra/LD TCP25.It defines the format and the order of messages exchanged between twoD LR/aor more communicating entities, as well as the actions taken on the 17.A 2B 1 transmission and/or receipt of a message or other event. The sentence describes ( ).C 0A InternetD -1B protocol 18.In the Internet, the equivalent concept to end systems is ( ).C intranet A hostsD network B servers26.In the following options, which does not define in protocol? ( )C clientsA the format of messages exchanged between two or more D routerscommunicating entities 19.In the Internet, end systems are connected together by ( ).B the order of messages exchanged between two or more A copper wirecommunicating entities B coaxial cableC the actions taken on the transmission of a message or other eventC communication linksD the transmission signals are digital signals or analog signals 模拟D fiber optics信号20.End systems access to the Internet through its ( ).27.In the following options, which is defined in protocol? ( ) A modemsA the actions taken on the transmission and/or receipt of a message orB protocolsother eventC ISPB the objects exchanged between communicating entities D socketsC the content in the exchanged messages21.End systems, packet switches, and other pieces of the Internet, run ( )D the location of the hosts that control the sending and receiving of information within the28.In the following options, which does not belong to the network edge?Internet.( )A programsA end systemsB processesB routersC applicationsC clientsD protocolsD servers22.There are many private networks, such as many corporate and29.In the following options, which belongs to the network core? ( ) government networks, whose hosts cannot exchange messages withA end systemshosts outside of the private network. These private networks are oftenB routersreferred to as ( ).C clientsA internetsD serversB LAN30.In the following options, which is not the bundled with the Internet ’s C intranetsconnection-oriented service? ( ) D WANA reliable data transfer23.The internet allows ( ) running on its end systems to exchange dataB guarantee of the transmission timewith each other.C flow control***A clients applicationsD congestion-controlB server applications31.An application can rely on the connection to deliver all of its data C P2P applicationswithout error and in the proper order. The sentence describes ( ).2***A flow control C data switchingB congestion-control D message switchingC reliable data transfer 40.In ( ) networks, the resources needed along a path to provide forD connection-oriented service communication between the end system are reserved for the duration 持续of the communication session. 32.It makes sure that neither side of a connection overwhelms 淹没压倒the other side by sending too many packets too fast. The sentence A packet-switcheddescribes ( ). B data-switchedA flow control C circuit-switchedB congestion-control D message-switchedC connection-oriented service 41.In ( ) networks, the resources are not reserved; a session’s messagesD reliable data transfer use the resources on demand, and as a consequence, may have to wait 33.It helps prevent the Internet from entering a state of gridlock. When a for access to communication link.packet switch becomes congested, its buffers can overflow and packet A packet-switchedloss can occur. The sentence describes ( ). B data-switchedA flow control C circuit-switchedB congestion-control D message-switchedC connection-oriented service 42.In a circuit-switched network, if each link has n circuits, for each linkD reliable data transfer used by the end-to-end connection, the connection gets ( ) of the 34.The Internet’s connection-oriented service has a name, it is ( ). link ’s bandwidth for the duration of the connection.A TCP A a fraction 1/nB UDP B allC TCP/IP C 1/2D IP D n times35.In the following options, which service does not be provided to an 43.For ( ), the transmission rate of a circuit is equal to the frame rate application by TCP?( ) multiplied by the number of bits in a slot.A reliable transport A CDMAB flow control B packet-switched networkC video conferencing C TDMD congestion control D FDM36.The Internet’s connectionless service is called ( ). 44.( ) means that the switch must receive the entire packet before it canA TCP begin to transmit the first bit of the packet onto the outbound link.B UDP A Queuing delayC TCP/IP B Store-and-forward transmissionD IP C Packet loss37.In the following options, which does not use TCP?( ) D PropagationA SMTP 45.The network that forwards packets according to host destinationB internet telephone addresses is called ( ) network.C FTP A circuit-switchedD HTTP B packet-switched38.In the following options, which does not use UDP?( ) C virtual-circuitA Internet phone D datagramB video conferencing 46.The network that forwards packets according to virtual-circuit numbersC streaming multimedia is called ( ) network.D telnet A circuit-switched39.There are two fundamental approaches to building a network core, ( ) B packet-switchedand packet switching. C virtual-circuitA electrical current switching D datagramB circuit switching3。

计算机网络双语试题及答案一、选择题(共20题,每题2分,共40分)1. 当使用HTTP协议进行通信时,下列哪个是无连接的协议?A. TCPB. IPC. UDPD. FTP2. 在计算机网络中,IP地址的作用是什么?A. 标识主机在网络中的唯一地址B. 实现数据的可靠传输C. 进行主机之间的通信D. 提供远程访问服务3. 下列哪个不属于网络拓扑结构的类型?A. 总线型拓扑B. 环形拓扑C. 星型拓扑D. 布线型拓扑4. 在TCP/IP协议中,下列哪个协议用于将IP地址转换为物理地址?B. DHCPC. FTPD. ICMP5. 在计算机网络中,HTTP和HTTPS协议之间的区别是?A. HTTP使用明文传输,HTTPS使用加密传输B. HTTP使用UDP传输,HTTPS使用TCP传输C. HTTP使用IP地址,HTTPS使用域名D. HTTP使用GET请求,HTTPS使用POST请求6. 某计算机的IP地址是192.168.0.1,子网掩码是255.255.255.0,那么该计算机所在的网络号是?A. 192.168.0B. 192.168.0.1C. 192.168.0.255D. 192.168.0.07. 在计算机网络中,下列哪个协议用于将域名解析为IP地址?A. DNSB. FTPC. DHCP8. 在TCP/IP协议中,下列哪个协议用于控制数据传输的可靠性?A. ICMPB. UDPC. FTPD. TCP9. 在计算机网络中,什么是反向代理服务器(Reverse Proxy Server)?A. 将外部网络请求转发给内部服务器的服务器B. 将内部网络请求转发给外部服务器的服务器C. 将HTTP请求转发给HTTPS服务器的服务器D. 将HTTPS请求转发给HTTP服务器的服务器10. 在计算机网络中,下列哪个协议用于电子邮件的发送和接收?A. SMTPB. POP3C. HTTPD. FTP11. 在计算机网络中,下列哪个协议用于文件传输?B. SMTPC. UDPD. TCP12. 以下哪个不是IPv6地址的特点?A. 128位长度B. 冒号分隔的十六进制C. 有固定的网络号和主机号D. 全球唯一的地址13. 在计算机网络中,下列哪个技术不属于无线局域网技术?A. Wi-FiB. BluetoothC. NFCD. 4G14. 在网络中,下列哪个设备用于将不同网段的数据转发到目的主机?A. 集线器B. 路由器D. 网关15. 下列哪个网络拓扑结构具有较高的可容错性和可拓展性?A. 星型拓扑B. 总线型拓扑C. 环形拓扑D. 树型拓扑16. 在计算机网络中,下列哪个协议用于互联网上的主机进行网络配置?A. DHCPB. DNSC. HTTPD. FTP17. 在TCP/IP协议中,下列哪个协议用于检测并纠正数据传输中的错误?A. TCPB. ARPC. ICMPD. UDP18. 下列哪个是网络安全的常见攻击方式之一?A. DDoS攻击B. 数据库攻击C. 剪贴板攻击D. 社会工程学攻击19. 下列哪个不是局域网(LAN)的特点?A. 覆盖范围较小B. 速度较快C. 价格较高D. 结构较简单20. 在计算机网络中,下列哪个协议用于向局域网中的所有主机广播消息?A. UDPB. TCPC. DHCPD. ICMP二、问答题(共5题,每题10分,共50分)1. 请简要介绍HTTP协议的工作原理。

Chapter 5 ProblemsProblem 1The rightmost column and bottom row are for parity bits.1 0 1 0 01 0 1 0 01 0 1 0 01 0 1 1 10 0 0 1 1Problem 2Suppose we begin with the initial two-dimensional parity matrix:0 0 0 01 1 1 10 1 0 11 0 1 0With a bit error in row 2, column 3, the parity of row 2 and column 3 is now wrong in the matrix below:0 0 0 01 1 0 10 1 0 11 0 1 0Now suppose there is a bit error in row 2, column 2 and column 3. The parity of row 2 is now correct! The parity of columns 2 and 3 is wrong, but we can't detect in which rows the error occurred!0 0 0 01 0 0 10 1 0 11 0 1 0The above example shows that a double bit error can be detected (if not corrected). Problem 3To compute the Internet checksum, we add up the values at 16-bit quantities: 00000000 0000000100000010 0000001100000100 0000010100000110 0000011100001000 00001001-------------------------00010100 00011001The one's complement of the sum is 11101011 11100110.Problem 4a) To compute the Internet checksum, we add up the values at 16-bit quantities: 00000001 0000001000000011 0000010000000101 0000011000000111 0000100000001001 00001010-------------------------00011001 00011110The one's complement of the sum is 11100110 11100001.b) To compute the Internet checksum, we add up the values at 16-bit quantities: 01000001 0100001001000011 0100010001000101 0100011001000111 0100100001001001 01001010-------------------------01011000 01011111The one's complement of the sum is 10100111 10100000c) To compute the Internet checksum, we add up the values at 16-bit quantities: 01100001 0110001001100011 0110010001100101 0110011001100111 0110011101101000 01101001-------------------------11111001 11111101The one's complement of the sum is 00000110 00000010.Problem 5If we divide 1001 into 10101010000 we get 10111101, with a remainder of R = 101.Problem 6a) If we divide 1001 into 10010001000 we get 10000001, with a remainder of R =001.b) If we divide 1001 into we get 10100011000 we get 10110101, with a remainderof R = 101.c) If we divide 1001 into 010********* we get 010111101, with a remainder of R =101.Problem 7 a)1)1()(--=N p Np p E21)1)(1()1()('------=N N p N Np p N p E ))1()1(()1(2----=-N p p p N NNp p E 1*0)('=⇒=b)NN NN N Np E NN N 11)11()11()11(1*)(11--=-=-=--1)11(lim =-∞→NN eNNN 1)11(lim =-∞→Thusep E N 1*)(lim =∞→Problem 8)1(2)1()(--=N p Np p E)3(2)2(2)1)(1(2)1()('------=N N p N Np p N p E))1(2)1(()1()3(2----=-N p p p N N121*0)('-=⇒=N p p E)1(2)1211(12*)(----=N N N N p Eee p E N 21121*)(lim =⋅=∞→Problem 9a) (1 – p(a))3 p(A) where,p(A) = probability that A succeeds in a slotp(A) = p(A transmits and B does not and C does not)= p(A transmits) p(B does not transmit) p(C does not transmit) = p(1 – p) (1 – p) = p(1 – p)2Hence, p(A succeeds for first time in slot 4) = (1 – p(a))3 p(A) = (1 – p(1 – p)2)3 p(1 – p)2b) p(A succeeds in slot 2) = p(1-p)2 p(B succeeds in slot 2) = p(1-p)2p(C succeeds in slot 2) = p(1-p)2p(either A or B or C succeeds in slot 2) = 3 p(1-p)2 (because these events are mutually exclusive)c) p(some node succeeds in a slot) = 3 p(1-p)2 p(no node succeeds in a slot) = 1 - 3 p(1-p)2Hence, p(first success occurs in slot 4) = p(no node succeeds in first 3 slots) p(some node succeeds in 4th slot) = (1 - 3 p(1-p)2)3 3 p(1-p)2d) efficiency = p(success in a slot) = 3 p(1-p)2Problem 10Problem 11The length of a polling round is)/(poll d R Q N +.The number of bits transmitted in a polling round is NQ . The maximum throughput therefore isQR d R d R Q N NQ poll poll +=+1)/(Problem 12a), b), c) See figure below.d)1. Forwarding table in A determines that the datagram should be routed to interface111.111.111.002.2. The adapter in A creates and Ethernet packet with Ethernet destination address22-22-22-22-22-22.3. The first router receives the packet and extracts the datagram. The forwardingtable in this router indicates that the datagram is to be routed to 122.222.222.003. 4. The first router then sends the Ethernet packet with the destination address of 55-55-55-55-55-55 and source address of 33-33-33-33-33-33 via its interface with IP address of 122.222.222.002.5. The process continues until the packet has reached Host F .e)ARP in A must now determine the LAN address of 111.111.111.002. Host A sends out an ARP query packet within a broadcast Ethernet frame. The first router receives the query packet and sends to Host A an ARP response packet. This ARP response packet is carried by an Ethernet frame with Ethernet destination address 00-00-00-00-00-00.Problem 13a) b) c) See figure below:d)1. Forwarding table in A determines that the datagram should be routed to interface111.111.111.002.2. The adapter in A creates and Ethernet packet with Ethernet destination address22-22-22-22-22-22.3. The router receives the packet and extracts the datagram. The forwarding table inthis router indicates that the datagram is to be routed via interface 122.222.222.002.4. The router then replaces the destination MAC address in the datagram it receivedfrom host A, with the MAC address of F (77-77-77-77-77-77) and sends the datagram over the interface 122.222.222.002.5. The switch (that is connected to the interface 122.222.222.002 of the router)forwards the datagram to its interface where F is connected. The datagram then reaches F.e) ARP in A must now determine the MAC address of 111.111.111.002. Host A sends out an ARP query packet within a broadcast Ethernet frame. The router receives the query packet and sends to Host A an ARP response packet. This ARP response packet is carried by an Ethernet frame with Ethernet destination address 00-00-00-00-00-00.Problem 14Wait for 51,200 bit times. For 10 Mbps, this wait is12.51010102.5163=⨯⨯bpsbits msecFor 100 Mbps, the wait is 512 μsec.Problem 15At 0=t A transmits. At 576=t , A would finish transmitting. In the worst case, B begins transmitting at time 224=t . At time 449225224=+=t B 's first bit arrives at A . Because 576449<, A aborts before completing the transmission of the packet, as it is supposed to do.Thus A cannot finish transmitting before it detects that B transmitted. This implies that if A does not detect the presence of a host, then no other host begins transmitting while A is transmitting.Problem 16Because A 's retransmission reaches B before B 's scheduled retransmission time, B refrains from transmitting while A retransmits. Thus A and B do not collide. Thus the factor 512 appearing in the exponential backoff algorithm is sufficiently large.Problem 17We want 5.)51/(1=+a or, equivalently, trans prop t t a /2.==. )108.1/(8⨯=d t prop m/sec and 576(=trans t bits 810/()bits/sec μ76.5)=sec. Solving for d we obtain 265=d meters. For the 100 Mbps Ethernet standard, the maximum distance between two hosts is 200 m.For transmitting station A to detect whether any other station transmitted during A 's interval, trans t must be greater than 26522⋅=prop t m 8108.1/⨯m/sec μ94.2=sec. Because76.594.2<, A will detect B 's signal before the end of its transmission.a)Let Y be a random variable denoting the number of slots until a success:1)1()(--==m m Y P ββ, where β is the probability of a success.This is a geometric distribution, which has mean β/1. The number of consecutive wasted slots is 1-=Y X thatββ-=-==11][][Y E X E x1)1(--=N p Np β11)1()1(1-----=N N p Np p Np xefficiency 11)1()1(1-----+=+=N N p Np p Np k kxk kb)Maximizing efficiency is equivalent to minimizing x , which is equivalent to maximizingβ. We know from the text that β is maximized at Np 1=.c)efficiency 11)11()11(1-----+=N N N N k k∞→N limefficiency 1/1/11-+=-+=e k k ee k kd) Clearly, 1-+e k k approaches 1 as ∞→k .a)bpsbits m m 681010204sec/102900⨯⋅+⋅sec5.12sec)108105.4(66μ=⨯+⨯=--b)∙ At time 0=t , both A and B transmit.∙ At time sec 5.12μ=t , A detects a collision.∙ At time sec25μ=t last bit of B 's aborted transmission arrives at A .∙At time sec 5.37μ=tfirst bit of A 's retransmission arrives at B .∙ At time sec 5.137********sec 5.376μμ=⨯+=bpsbits t A 's packet is completelydelivered at B .c) sec 5.512sec 1005sec 5.12μμμ=⋅+Problem 20i) from A to left router: Source MAC address: 00-00-00-00-00-00 Destination MAC address: 22-22-22-22-22-22 Source IP: 111.111.111.001 Destination IP: 133.333.333.003ii) from the left router to the right router: Source MAC address: 33-33-33-33-33-33 Destination MAC address: 55-55-55-55-55-55 Source IP: 111.111.111.001 Destination IP: 133.333.333.003iii) from the right router to F: Source MAC address: 88-88-88-88-88-88Destination MAC address: 99-99-99-99-99-99Source IP: 111.111.111.001Destination IP: 133.333.333.003Problem 21i) from A to switch: Source MAC address: 00-00-00-00-00-00Destination MAC address: 55-55-55-55-55-55Source IP: 111.111.111.001Destination IP: 133.333.333.003ii) from switch to right router: Source MAC address: 00-00-00-00-00-00Destination MAC address: 55-55-55-55-55-55Source IP: 111.111.111.001Destination IP: 133.333.333.003iii) from right router to F: Source MAC address: 88-88-88-88-88-88Destination MAC address: 99-99-99-99-99-99Source IP: 111.111.111.001Destination IP: 133.333.333.003Problem 22If all the 14 nodes send out data at the maximum possible rate of 100 Mbps, a total aggregate throughput of 14*100 = 1400 Mbps is possible.Problem 23Each departmental hub is a single collision domain that can have a maximum throughput of 100 Mbps. The links connecting the web server and the mail server has a maximum throughput of 100 Mbps. Hence, if the three collision domains and the web server and mail server send out data at their maximum possible rates of 100 Mbps each, a maximum total aggregate throughput of 500 Mbps can be achieved among the 14 end systems.Problem 24All of the 14 end systems will lie in the same collision domain. In this case, the maximum total aggregate throughput of 100 Mbps is possible among the 14 end sytems.Problem 25Problem 26The time required to fill 8⋅L bits is.sec 8sec 106483m L L =⨯⋅b) For ,500,1=L the packetization delay is.sec 5.187sec 81500m m =For ,48=L the packetization delay is.sec 6sec 848m m =c)Store-and-forward delay R L 408+⋅=For 500,1=L , the delay issec 77sec 15512sec 1015540815006μ≈≈⨯+⋅mFor ,48=L store-and-forward delay sec 1μ<.d) Store-and-forward delay is small for both cases for typical ATM link speeds. However, packetization delay for 1500=L is too large for real-time voice applications.Problem 27Problem 28Chapter 6 Review Questions1.In infrastructure mode of operation, each wireless host is connected to the largernetwork via a base station (access point). If not operating in infrastructure mode, a network operates in ad-hoc mode. In ad-hoc mode, wireless hosts have noinfrastructure with which to connect. In the absence of such infrastructure, thehosts themselves must provide for services such as routing, address assignment,DNS-like name translation, and more.2.a) Single hop, infrastructure-basedb) Single hop, infrastructure-lessc) Multi-hop, infrastructure-basedd) Multi-hop, infrastructure-less3.Path loss is due to the attenuation of the electromagnetic signal when it travelsthrough matter. Multipath propagation results in blurring of the received signal at the receiver and occurs when portions of the electromagnetic wave reflect offobjects and ground, taking paths of different lengths between a sender andreceiver. Interference from other sources occurs when the other source is alsotransmitting in the same frequency range as the wireless network.4.a) Increasing the transmission powerb) Reducing the transmission rate5.APs transmit beacon frames. An AP‟s beacon frames will be transmitted over oneof the 11 channels. The beacon frames permit nearby wireless stations to discover and identify the AP.6.False7.APs transmit beacon frames. An AP‟s beacon frames will be transmitted over oneof the 11 channels. The beacon frames permit nearby wireless stations to discover and identify the AP.8.False9.Each wireless station can set an RTS threshold such that the RTS/CTS sequenceis used only when the data frame to be transmitted is longer than the threshold.This ensures that RTS/CTS mechanism is used only for large frames.10.No, there would n‟t be any advantage. Suppose there are two stations that want totransmit at the same time, and they both use RTS/CTS. If the RTS frame is as long as a DATA frames, the channel would be wasted for as long as it would have been wasted for two colliding DATA frames. Thus, the RTS/CTS exchange is only useful when the RTS/CTS frames are significantly smaller than the DATA frames.11.Initially the switch has an entry in its forwarding table which associates thewireless station with the earlier AP. When the wireless station associates with the new AP, the new AP creates a frame with the wireless station‟s MAC address and broadcasts the frame. The frame is received by the switch. This forces the switch to update its forwarding table, so that frames destined to the wireless station are sent via the new AP.12.Any ordinary Bluetooth node can be a master node whereas access points in802.11 networks are special devices (normal wireless devices like laptops cannot be used as access points).13.False14.“Opportunistic Scheduling” refers to matching the physical layer protocol tochannel conditions between the sender and the receiver, and choosing the receivers to which packets will be sent based on channel condition. This allows the base station to make best use of the wireless medium.15.UMTS to GSM and CDMA-2000 to IS-95.16.No. A node can remain connected to the same access point throughout itsconnection to the Internet (hence, not be mobile). A mobile node is the one that changes its point of attachment into the network over time. Since the user is always accessing the Internet through the same access point, she is not mobile. 17.A permanent address for a mobile node is its IP address when it is at its homenetwork. A care-of-address is the one its gets when it is visiting a foreign network.The COA is assigned by the foreign agent (which can be the edge router in the foreign network or the mobile node itself).18.False19.The home network in GSM maintains a database called the home location register(HLR), which contains the permanent cell phone number and subscriber profile information about each of its subscribers. The HLR also contains information about the current locations of these subscribers. The visited network maintains a database known as the visitor location register (VLR) that contains an entry for each mobile user that is currently in the portion of the network served by the VLR.VLR entries thus come and go as mobile users enter and leave the network.The edge router in home network in mobile IP is similar to the HLR in GSM and the edge router in foreign network is similar to the VLR in GSM.20. Anchor MSC is the MSC visited by the mobile when a call first begins; anchorMSC thus remains unchanged during the call. Throughout the call‟s duration and regardless of the number of inter-MSC transfers performed by the mobile, the call is routed from the home MSC to the anchor MSC, and then from the anchor MSC to the visited MSC where the mobile is currently located.21. a) Local recoveryb) TCP sender awareness of wireless linksc) Split-connection approachesChapter 6 ProblemsProblem 1.Output corresponding to bit d 1 = [-1,1,-1,1,-1,1,-1,1]Output corresponding to bit d 0 = [1,-1,1,-1,1,-1,1,-1]Problem 2.Sender 2 output = [1,-1,1,1,1,-1,1,1]; [ 1,-1,1,1,1,-1,1,1]Problem 3.181111)1()1(111111)1()1(1112=⨯+⨯+-⨯-+⨯+⨯+⨯+-⨯-+⨯=d 181111)1()1(111111)1()1(1122=⨯+⨯+-⨯-+⨯+⨯+⨯+-⨯-+⨯=dProblem 4Sender 1: (1, 1, 1, -1, 1, -1, -1, -1)Sender 2: (1, -1, 1, 1, 1, 1, 1, 1)Problem 5a) The two APs will typically have different SSIDs and MAC addresses. A wirelessstation arriving to the café will associate with one of the SSIDs (that is, one of the APs). After association, there is a virtual link between the new station and the AP. Label the APs AP1 and AP2. Suppose the new station associates with AP1. When the new station sends a frame, it will be addressed to AP1. Although AP2 will also receive the frame, it will not process the frame because the frame is not addressed to it. Thus, the two ISPs can work in parallel over the same channel. However, the two ISPs will be sharing the same wireless bandwidth. If wireless stations in different ISPs transmit at the same time, there will be a collision. For 802.11b, the maximum aggregate transmission rate for the two ISPs is 11 Mbps.b)Now if two wireless stations in different ISPs (and hence different channels)transmit at the same time, there will not be a collision. Thus, the maximum aggregate transmission rate for the two ISPs is 22 Mbps for 802.11b.Problem 6Suppose that wireless station H1 has 1000 long frames to transmit. (H1 may be an AP that is forwarding an MP3 to some other wireless station.) Suppose initially H1 is the only station that wants to transmit, but that while half-way through transmitting its first frame, H2 wants to transmit a frame. For simplicity, also suppose every sta tion can hear every other station‟s signal (that is, no hidden terminals). Before transmitting, H2 will sense that the channel is busy, and therefore choose a random backoff value.Now suppose that after sending its first frame, H1 returns to step 1; that is, it waits a short period of times (DIFS) and then starts to transmit the second frame. H1‟s second frame will then be transmitted while H2 is stuck in backoff, waiting for an idle channel. Thus, H1 should get to transmit all of its 1000 frames before H2 has a chance to access the channel. On the other hand, if H1 goes to step 2 after transmitting a frame, then it too chooses a random backoff value, thereby giving a fair chance to H2. Thus, fairness was the rationale behind this design choice.Problem 7A frame without data is 32 bytes long. Assuming a transmission rate of 11 Mbps, thetime to transmit a control frame (such as an RTS frame, a CTS frame, or an ACK frame) is (256 bits)/(11 Mbps) = 23 usec. The time required to transmit the data frame is (8256 bits)/(11 Mbps) = 751DIFS + RTS + SIFS + CTS + SIFS + FRAME + SIFS + ACK= DIFS + 3SIFS + (3*23 + 751) usec = DIFS + 3SIFS + 820 usecProblem 8a) 1 message/ 2 slotsb) 2 messages/slotc) 1 message/slotd)i) 1 message/slotii) 2 messages/slotiii) 2 messages/slote)i) 1 message/4 slotsii) slot 1: Message A→ B, message D→ Cslot 2: Ack B→ Aslot 3: Ack C→ D= 2 messages/ 3 slotsiii)slot 1: Message C→ Dslot 2: Ack D→C, message A→ BRepeatslot 3: Ack B→ A= 2 messages/3 slotsProblem 10a)10 Mbps if it only transmits to node A. This solution is not fair since only A isgetting served. By “fair” it means that each of the four nodes should be allotted equal number of slots.b)For the fairness requirement such that each node receives an equal amount of dataduring each downstream sub-frame, let n1, n2, n3, and n4 respectively represent the number of slots that A, B, C and D get.Now,data transmitted to A in 1 slot = 10t Mbits(assuming the duration of each slot to be t)Hence,Total amount of data transmitted to A (in n1 slots) = 10t n1Similarly total amounts of data transmitted to B, C, and D equal to 5t n2, 2.5t n3, and t n4 respectively.Now, to fulfill the given fairness requirement, we have the following condition:10t n1 = 5t n2 = 2.5t n3 = t n4Hence,n2 = 2 n1n3 = 4 n1n4 = 10 n1Now, the total number of slots is N. Hence,n1+ n2+ n3+ n4 = Ni.e. n1+ 2 n1 + 4 n1 + 10 n1 = Ni.e. n1 = N/17Hence,n2 = 2N/17n3 = 4N/17n4 = 10N/17The average transmission rate is given by:(10t n1+5t n2+ 2.5t n3+t n4)/tN= (10N/17 + 5 * 2N/17 + 2.5 * 4N/17 + 1 * 10N/17)/N= 40/17 = 2.35 Mbpsc)Let node A receives twice as much data as nodes B, C, and D during the sub-frame.Hence,10tn1 = 2 * 5tn2 = 2 * 2.5tn3 = 2 * tn4i.e. n2 = n1n3 = 2n1n4 = 5n1Again,n1 + n2 + n3 + n4 = Ni.e. n 1+ n1 + 2n1 + 5n1 = Ni.e. n1 = N/9Now, average transmission rate is given by:(10t n1+5t n2+ 2.5t n3+t n4)/tN= 25/9 = 2.78 MbpsSimilarly, considering nodes B, C, or D receive twice as much data as any othernodes, different values for the average transmission rate can be calculated. Problem 11a)No. All the routers might not be able to route the datagram immediately. This isbecause the Distance Vector algorithm (as well as the inter-AS routing protocols like BGP) is decentralized and takes some time to terminate. So, during the time when the algorithm is still running as a result of advertisements from the new foreign network, some of the routers may not be able to route datagrams destined to the mobile node.b)Yes. This might happen when one of the nodes has just left a foreign network andjoined a new foreign network. In this situation, the routing entries from the oldforeign network might not have been completely withdrawn when the entries from the new network are being propagated.c)The time it takes for a router to learn a path to the mobile node depends on thenumber of hops between the router and the edge router of the foreign network for the node.Problem 12If the correspondent is mobile, then any datagrams destined to the correspondent would have to pass through the correspondent’s home agent. The foreign agent in the network being visited would also need to be involved, since it is this foreign agent that notifies the correspondent‟s home agent of the location of the correspond ent. Datagrams received by the correspondent‟s home agent would need to be encapsulated/tunneled between the correspondent‟s home agent and foreign agent, (as in the case of the encapsulated diagram at the top of Figure 6.23.Problem 13Because datagrams must be first forward to the home agent, and from there to the mobile, the delays will generally be longer than via direct routing. Note that it is possible, however, that the direct delay from the correspondent to the mobile (i.e., if the datagram is not routed through the home agent) could actually be smaller than the sum of the delayfrom the correspondent to the home agent and from there to the mobile. It would depend on the delays on these various path segments. Note that indirect routing also adds a home agent processing (e.g., encapsulation) delay.Problem 14First, we note that chaining was discussed at the end of section 6.5. In the case of chaining using indirect routing through a home agent, the following events would happen: ∙The mobile node arrives at A, A notifies the home agent that the mobile is now visiting A and that datagrams to the mobile should now be forwarded to thespecified care-of-address (COA) in A.∙The mobile node moves to B. The foreign agent at B must notify the foreign agent at A that the mobile is no longer resident in A but in fact is resident in Band has the specified COA in B. From then on, the foreign agent in A willforward datagrams it receives that are addressed to the mobile‟s COA in A to themobile‟s COA in B.∙The mobile node moves to C. The foreign agent at C must notify the foreign agent at B that the mobile is no longer resident in B but in fact is resident in C and has the specified COA in C. From then on, the foreign agent in B will forwarddatagrams it receives (from the foreign agent in A) that are addressed to themobile‟s COA in B to the mobile‟s COA in C.Note that when the mobile goes offline (i.e., has no address) or returns to its home network, the datagram-forwarding state maintained by the foreign agents in A, B and C must be removed. This teardown must also be done through signaling messages. Note that the home agent is not aware of the mobile‟s mobility beyond A, and that the correspondent is not at all aware of the mobile‟s mobility.In the case that chaining is not used, the following events would happen: ∙ The mobile node arrives at A, A notifies the home agent that the mobile is now visiting A and that datagrams to the mobile should now be forwarded to thespecified care-of-address (COA) in A.∙The mobile node moves to B. The foreign agent at B must notify the foreign agent at A and the home agent that the mobile is no longer resident in A but infact is resident in B and has the specified COA in B. The foreign agent in A canremove its state about the mobile, since it is no longer in A. From then on, thehome agent will forward datagrams it receives that are addressed to the mobile‟sCOA in B.∙The mobile node moves to C. The foreign agent at C must notify the foreign agent at B and the home agent that the mobile is no longer resident in B but in fact is resident in C and has the specified COA in C. The foreign agent in B canremove its state about the mobile, since it is no longer in B. From then on, thehome agent will forward datagrams it receives that are addressed to the mobile‟sCOA in C.When the mobile goes offline or returns to its home network, the datagram-forwarding state maintained by the foreign agent in C must be removed. This teardown must also bedone through signaling messages. Note that the home agent is always aware of the mobile‟s current foreign network. However, the correspondent is still blissfully unaware of the mobile‟s mobility.Problem 15Two mobiles could certainly have the same care-of-address in the same visited network. Indeed, if the care-of-address is the address of the foreign agent, then this address would be the same. Once the foreign agent decapsulates the tunneled datagram and determines the address of the mobile, then separate addresses would need to be used to send the datagrams separately to their different destinations (mobiles) within the visited network.Problem 16If the MSRN is provided to the HLR, then the value of the MSRN must be updated in the HLR whenever the MSRN changes (e.g., when there is a handoff that requires the MSRN to change). The advantage of having the MSRN in the HLR is that the value can be provided quickly, without querying the VLR. By providing the address of the VLR Rather than the MSRN), there is no need to be refreshing the MSRN in the HLR.Chapter 7 Review Questions1.Streaming stored audio/video: pause/resume, re-positioning, fast-forward; real-timeinteractive audio and video: people communicating and responding in real time.2.Camp 1: No fundamental changes in TCP/IP protocols; add bandwidth where needed;also use caching, content distribution networks, and multicast overlay networks.Camp 2: Provide a network service that allows applications to reserve bandwidth in the network. Camp 3, differentiated service: introduce simple classifying and policing schemes at the edge of the network, and give different datagrams different levels of service according to their class in the router queues.3.Uncompressed audio stored on CD has a bit rate of 1411.2 Kbps. mp3 files aretypically encoded in 128 Kbps or less, thereby giving them a compression ratio of almost 11. Image compression ratios are in the range of 10 to 100.4.Figure 6.1: simple, doesn‟t require meta file or streaming server; Figure 6.2: allowsmedia player t o interact directly with the web server, doesn‟t require a streaming server; Figure 6.3: media player interacts directly with a streaming server, which has been designed for the specific streaming application.5.End-to-end delay is the time it takes a packet to travel across the network from sourceto destination. Delay jitter is the fluctuation of end-to-end delay from packet to the next packet.6. A packet that arrives after its scheduled play out time can not be played out.Therefore, from the perspective of the application, the packet has been lost.7.First scheme: send a redundant encoded chunk after every n chunks; the redundantchunk is obtained by exclusive OR-ing the n original chunks. Second scheme: send a lower-resolution low-bit rate scheme along with the original stream. Interleaving does not increase the bandwidth requirements of a stream.8.The role of the DNS is to forward HTTP requests to DNS server managed by theCDN, which in turn redirects the request to an appropriate CDN server. The DNS does not have to be modified to support a CDN. A CDN should provide DNS with the host name and IP address of its authoritative name server (See Section 2.5.3).9.a)Models of traffic demand between network end pointsb)Well-defined performance requirementsc)Models to predict end-end performance for a given workload model, andtechniques to find a minimal high cost bandwidth allocation that will result in all user requirements being met.。

计算机⽹络英⽂版——提供给学⽣部分习题答案Solution of Selected Exercises from the End of Chapter ExercisesChapter 1 - Introduction And Overview1.4 To what aspects of networking does data communications refer?Answer:Data communications refers to the study of low-level mechanisms and technologies used to send information acrossa physical communication medium, such as a wire, radio wave, or light beam.1.5 What is packet-switching, and why is packet switching relevant to the Internet?Answer: Packet switching divides data into small blocks, called packets, and includes an identification of the intended recipient in each packet. Packet switching changed networking in a fundamental way, and provided the basis for the modern Internet. Packet switching allows multiple senders to transmit data over a shared network.1.8 What is a communication protocol? Conceptually, what two aspects of communication does a protocol specify? Answer: A communication protocol refer to a specification for network communication.Major aspects of a protocol are syntax (format) and semantics (meaning) of the protocol.1.9 What is a protocol suite, and what is the advantage of a suite?Answer:protocols are designed in complete, cooperative sets called suites or families, instead of creating each protocol in isolation. Each protocol in a suite handles one aspect of communication; together, the protocols in a suite cover all aspects of communication. The entire suite is designed to allow the protocols to work together efficiently. 1.11 List the layers in the TCP/IP model, and give a brief explanation of each.(See Textbook)1.14 Give a brief explain of the layers in the ISO Open System Interconnection model.(See Textbook)Chapter 3 - Internet Applications And Network Programming3.1 What are the two basic communication paradigms used in the Internet?Answer: There are various approaches, but according to textbook, we can specify them as Stream Paradigm and Message Paradigm.3.2 Give six characteristics of Internet stream communication.(See Textbook)3.3 Give six characteristics of Internet message communication.(See Textbook)3.4 If a sender uses the stream paradigm and always sends 1024 bytes at a time, what size blocks can the Internet deliverto a receiver?Answer: stream paradigm does not provide any guarantees for block sizes, so all depends on individual transfer.3.6 What are the three surprising aspects of the Internet’s message delivery semantics?Answer:The Internet’s message delivery has the followi ng undesirable characteristics:* Messages can be lost* Messages can be duplicated* Messages can be delivered out-of-order3.8 When two applications communicate over the Internet, which one is the server?Answer: T he application that waits for some other applications to contact is called server, and the application that contact other one is called client.3.14 What two identifiers are used to specify a particular server?Answer: A particular server is identified by the following identifiers:* An identifier for the computer on which a server runs (IP Address)* An identifier for a particular service on the computer (Port Number)Chapter 4 - Traditional Internet Applications4.1 What details does an application protocol specify?(See Textbook)4.3 What are the two key aspects of application protocols, and what does each include?(See Textbook)4.6 What are the four parts of a URL, and what punctuation is used to separate the parts?Answer: The URL into four components: a protocol, a computer name, a document name, and parameters. The computer name and protocol port are used to form a connection to the server on which the page resides. And the document name and parameters are used to request a specific page.4.7 What are the four HTTP request types, and when is each used?(See Textbook)4.12 When a user requests an FTP directory listing, how many TCP connections are formed? Explain.Answer: FTP uses two types of connections to perform its functionality, namely* A control connection is reserved for commands. Each time the server needs to download or upload a file, the server opens a new connection.* A data connection is used to transfer files.4.16 List the three types of protocols used with email, and describe each.(See Textbook)4.17 What are the characteristics of SMTP?(See Textbook)4.20 What are the two main email access protocols?Answer: Two major email access protocols are:* Post Office Protocol (POP)* Internet Mail Access Protocol (IMAP)Chapter 6- Information Sources and Signals6.4 State and describe the four fundamental characteristics of a sine wave.(See Textbook)6.9 What is the analog bandwidth of a signal?Answer: Analog bandwidth of signal can be defined as to be the difference between the highest and lowest frequencies of the constituent parts (i.e., the highest and lowest frequencies obtained by Fourier analysis)6.11 Suppose an engineer increases the number of possible signal levels from two to four. How many more bits can be sent in the same amount of time? Explain.Answer: The number of levels that can be represented by n bits is given by 2n . So if number of levels changes from 2→4, it means number of bits goes from 1→2612. What is the definition of baud?Answer: Baud is defined as the number of times that a signal can change per second.6.14 What is the bandwidth of a digital signal? Explain.Answer: According to the definition of analog bandwidth, a digital signal has infinite bandwidth because Fourier analysis of a digital signal produces an infinite set of sine waves with frequencies that grow to infinity.6.18 What is the chief advantage of a Differential Manchester Encoding?Answer: The most important property of differential encoding is that the encoding works correctly even if the two wires carrying the signal are accidentally reversed.6.20 If the maximum frequency audible to a human ear is 20,000 Hz, at what rate must the analog signal from a microphone be sampled when converting it to digital?Answer: The sampling rate = 2 × f max, so the signal should be sampled at 2x20,000 = 40,000 HzChapter 7 - Transmission Media7.2 What are the three energy types used when classifying physical media according to energy used?Answer: Three types of energy used when classifying physical media are electrical, electromechanical (radio), and light7.4 What three types of wiring are used to reduce interference form noise?(See Textbook)7.10 List the three forms of optical fiber, and give the general properties of each.(See Textbook)7.21 What is the relationship between bandwidth, signal levels, and data rate?Answer: If a transmission system uses K possible signal levels and has an anal og bandwidth B, Nyquist’s Theorem states that the maximum data rate in bits per second, D, is: D = 2 B log2K7.22 If two signal levels are used, what is the data rate that can be sent over a coaxial cable that has an analog bandwidthof 6.2 MHz?Answer: Using the D= 2 B log2 K relationship, D = 2*6.2*log22 = 2*6.2*1 = 12.4 Mbps7.24 If a system has an input power level of 9000, and an output power level of 3000, what is the difference when expressed in dB?Answer: Decibel is expressed as 10log10(P out/P in) → 10log10(3,000/9,000) = to be determined by reader7.23 If a system has an average power level of 100, an average noise level of 33.33, and a bandwidth of 100 MHz, whatis the effective limit on channel capacity?Answer: Shannon theorem specify the maximum data rate that could be achieved over a transmission system that experiences noise: C = Blog2 (1 + S/N) = 100,000,000 * log2 (1 + 100/33.33) = 100,000,000 * log24 = 200,000,000 = 200 Mbps7.25 If a telephone system can be created with a signal-to-noise ratio of 40 dB and an analog bandwidth of 3000 Hz, how many bits per second could be transmitted?Answer: First we should convert 40 dB to a real number, namely if 40 = 10 log10S/N→S/N = 10,000 , Using the Shannon’s capacity expression C = B log2(1 + S/N) → C = 3,000 log2 (1+ 10,000) = to be determined by readerCh 8 - Reliability And Channel Coding8.1 List and explain the three main sources of transmission errors.(See Textbook)8.3 In a burst error, how is burst length measured?Answer: For a burst error, the burst size, or length, is defined as the number of bits from the start of the corruption to the end of the corruption.8.4 What is a codeword?Answer: We can define the set of all possible messages to be a set of datawords, and define the set of all possible encoded versions to be a set of codewords. So each possible code sequence is considered to be a codeword.8.8 Compute the Hamming distance for the following pairs: (0000, 0001), (0101, 0001), (1111, 1001), and ( 0001, 1110). (See Textbook)8.11 Generate a RAC parity matrix for a (20, 12) coding of the dataword 100011011111.(See Textbook)8.15 Express the two values in the previous exercise as polynomials.Answer:X10+ X7 + X5 + X3 + XX4+ X2+ 1Ch 9 - Transmission Modes9.1 Describe the difference between serial and parallel transmission.Answer: Transmission modes can be divided into two fundamental categories:* Serial: one bit is sent at a time* Parallel: multiple bits are sent at the same time9.2 What are the advantages of parallel transmission? What is the chief disadvantage?Answer: A parallel mode of transmission has two chief advantages:* High speed: Because it can send N bits at the same time, a parallel interface can operate N times faster than an equivalent serial interface.* Match to underlying hardware: Internally, computer and communication hardware uses parallel circuitry.Thus, a parallel interface matches the internal hardware well.The main disadvantage of parallel transmission is number of cables required, for long distance communication, this is an important consideration.9.4 What is the chief characteristic of asynchronous transmission?Answer:Asynchronous transmission can occur at any time, with an arbitrary delay between the transmission of two data items, it allows the physical medium to be idle for an arbitrary time between two transmissions.Chapter 11 - Multiplexing And Demultiplexing11.2 What are the four basic types of multiplexing?(See Textbook)11.4 What is a guard band?Answer: For proper communication without interference, we should choose a set of carrier frequencies with a gap between them known as a guard band. The guard band reduces or eliminates the possible interference between neighboring carrier signals.11.8 Explain how a range of frequencies can be used to increase data rate.Answer:To increase the overall data rate, a sender divides the frequency range of the channel into K carriers, and sends 1 /K of the data over each carrier.11.12 Suppose N users compete using a statistical TDM system, and suppose the underlying physical transport can sendK bits per second. What is the minimum and maximum data rate that an individual user can experience?Answer: If we neglect the overhead generated by statistical TDM, a system will have two possibilities: * Minimum: If all channels have equal data then the rate will be K/N bps* Maximum: If only one channel active and the others are passive, then rate will be K bpsChapter 13 - Local Area Networks: Packets, Frames, And Topologies13.1 What is circuit switching, and what are its chief characteristics?Answer: The term circuit switching refers to a communication mechanism that establishes a path between a sender and receiver with guaranteed isolation from paths used by other pairs of senders and receivers. The circuit switching has the following main characteristics:* Point-to-point communication* Separate steps for circuit creation, use, and termination* Performance equivalent to an isolated physical path13.3 In a packet switching system, how does a sender transfer a large file?Answer: The packet switching system requires a sender to divide each message into blocks of data that are known as packets . The size of a packet varies; each packet switching technology defines a maximum packet size. So, a large file will be divided into smaller pieces and sent.13.5 What are the characteristics of LANs, MANs, and W ANs?Answer: There are lots of details that can be said and discussed for categorization of network types based on geography, few points are highlighted below:* Local Area Network (LAN): Least expensive; spans a single room or a single building* Metropolitan Area Network (MAN) Medium expense; spans a major city or a metroplex* Wide Area Network (WAN) Most expensive; spans sites in multiple cities13.6 Name the two sublayers of Layer 2 protocols defined by IEEE, and give the purpose of each.Answer: The Layer 2 protocols defined by IEEE defines two sub-layers as mentioned below:* Logical Link Control (LLC) Addressing and demultiplexing* Media Access Control (MAC) Access to shared media13.8 What are the four basic LAN topologies?Answer: The four basic LAN topologies are star, ring, mesh and bus.13.10 In a mesh network, how many connections are required among 20 computers?Answer: The expression to calculate number of connections in a mesh network is given by n (n-1)/2. So for 20 computers then number of connections required will be = 20 (20 – 1)/2 =19013.15 Give a definition of the term frame .Answer: In a packet-switched network, each frame corresponds to a packet processed at data link layer.Chapter 14 - The IEEE MAC Sub-Layer14.1 Explain the three basic approaches used to arbitrate access to a shared medium.(See Textbook)14.3 List the three main types of channelization and the characteristics of each.(See Textbook)14.6 What is a token, and how are tokens used to control network access?Answer: A special control message is called a token. In a token passing system, when no station has any packets to send, the token circulates among all stations continuously. When a station captures the token, it sends its data, and when transmission completed, it releases the token.14.8 Expand the acronym CSMA/CD, and explain each part.Answer: The acronym CSMA/CD stands for Carrier Sense Multi-Access with Collision Detection, which means the following: * Carrier Sense: Instead of allowing a station to transmit whenever a packet becomes ready, Ethernet requires each station to monitor the cable to detect whether another transmission is already in progress.* Multiple Access: The system allows multiple users/hosts to make use of a common/shared media* Collision Detection. A collision can occur if two stations wait for a transmission to stop, find the cable idle, and both start transmitting.14.10 Why does CSMA/CD use a random delay? (Hint: think of many identical computers on a network.)Answer: Randomization is used to avoid having multiple stations transmit simultaneously as soon as the cable is idle.That is, the standard specifies a maximum delay, d, and requires each station to choose a random delay less than d after a collision occurs. In most cases, when two stations each choose a random value, the station that chooses the smallest delay willChapter 15 - Wired LAN Technology (Ethernet And 802.3)15.1 How large is the maximum Ethernet frame, including the CRC?Answer: According to Fig. 15.1 a conventional Ethernet frame has the following fields:* Header: 14 bytes (fixed)* Payload: 46-1500 bytes (there is a minimum frame size because of collision detection)* CRC: 4 bytes (fixed)Accordingly an Ethernet frame will be maximum 1518 bytes and minimum 64 bytes15.3 In an 802.3 Ethernet frame, what is the maximum payload size?Answer: The 802.3 Ethernet makes use of 8-bytes of the original/conventional Ethernet for Logical Link Control / Sub-Network Attachment Point (LLC / SNAP) header instead of extending/increasing the header. This is for sake of backward compatibility. So the maximum pay load is reduced from 1500 bytes to 1492 bytes.15.6 How did a computer attach to a Thicknet Ethernet?Answer: Hardware used with Thicknet was divided into two major parts:* Transceiver: A network interface card (NIC) handled the digital aspects of communication, and a separate electronic device called a transceiver connected to the Ethernet cable and handled carrier detection, conversion of bits into appropriate voltages for transmission, and conversion of incoming signals to bits.* AUI: A physical cable known as an Attachment Unit Interface (AUI) connected a transceiver to a NIC in a computer. A transceiver was usually remote from a computer.15.7 How were computers attached to a Thinnet Ethernet?Answer: Thinnet Ethernet (formally named 10Base2) uses a thinner coaxial cable that was more flexible than Thicknet. The wiring scheme differed dramatically from Thicknet. Instead of using AUI connections between a computer and a transceiver, Thinnet integrates a transceiver directly on the NIC, and runs a coaxial cable from one computer to another.15.8 What is an Ethernet hub, and what wiring is used with a hub?Answer: An electronic device that serves as the central interconnection is known as a hub. Hubs were available in a variety of sizes, with the cost proportional to size. The hubs are becoming old-fashioned, and being replaced with switches.15.3 What category of twisted pair wiring is needed for a 10 Mbps network? 100 Mbps? 1000 Mbps?Answer: The three major categories of Ethernet and their wiring is listed below:* 10 Mbps: 10BaseT (Ethernet) Category 5* 100 Mbps: 100BaseT (Ethernet Fast) Category 5E* 1 Gbps: 1000BaseT (Gigabit Ethernet) Category 6Chapter 20 - Internetworking: Concepts, Architecture, and Protocols20.2 Will the Internet be replaced by a single networking technology? Why or why not?Answer: Incompatibilities make it impossible to form a large network merely by interconnecting the wires among networks. The beauty of the Internet is interconnection of wide range of technologies from various manufacturers.Diversity of the products and solutions is a richness instead of limitation as long as they all adopt the same set of protocols.20.3 What are the two reasons an organization does not use a single router to connect all its networks?Answer:An organization seldom uses a single router to connect all of its networks. There are two major reasons: * Because the router must forward each packet, the processor in a given router is insufficient to handle the traffic passing among an arbitrary number of networks.* Redundancy improves internet reliability. To avoid a single point of failure, protocol software continuously monitors internet connections and instructs routers to send traffic along alternative paths when a network or router fails.20.6 In the 5-layer reference model used with the TCP/IP Internet protocols, what is the purpose of each of the five layers?(See 1.11)Chapter 21- IP: Internet Addressing21.3 In the original classful address scheme, was it possible to determine the class of an address from the address itself? Explain.Answer:Yes, since in the classful addressing scheme initial bit(s) gives indication about the class being used.21.7 If an ISP assigned you a /28 address block, how many computers could you assign an address?Answer: When an organization is assigned /28 CIDR address, it means 28 bits out of 32 bits are fixed, so 32-28 = 4 bits available for user space. So number of users 24-2 = 4, since the all 0s and all 1s address are having special use and can’t be assigned to a user.21.8 If an ISP offers a / 17 address block for N dollars per month and a / 16 address block for 1.5 N dollars per month,which has the cheapest cost per computer?Answer: Number of addresses in /17 block 232-17 = 215Price per address: N /215 = N / 215Number of addresses in /16 block 232-16 = 216Price per address: 1.5N /216 = 0.75N/215 So /16 address block will be cheaper in comparison with the price given for /17 block.21.10 Suppose you are an ISP with a / 24 address block. Explain whether you accommodate a request from a customer who needs addresses for 255 computers. (Hint: consider the special addresses.)Answer: For a/24 address block, number of available addresses will be 232-24 = 28 = 256. However, a suffix with all 0s address is reserved for network ID and a suffix with all 1s address is reserved for broadcast address, so number of addresses that can be assigned to computers/hosts will be 256 -2 = 254.21.11 Suppose you are an ISP that owns a / 22 address block. Show the CIDR allocation you would use to allocateaddress blocks to four customers who need addresses for 60 computers each.Answer: The /22 address block can be assigned as follows:ddd.ddd.ddd.00/26ddd.ddd.ddd.01/26ddd.ddd.ddd.10/26ddd.ddd.ddd.11/26Chapter 22- Datagram Forwarding22.1 What are the two basic communication paradigms that designers consider when designing an internet?Answer:* Connection-oriented service * Connectionless service22.2 How does the Internet design accommodate heterogeneous networks that each have their own packet format?Answer: To overcome heterogeneity, the Internet Protocol defines a packet format that is independent of the underlying hardware. The result is a universal, virtual packet that can be transferred across the underlying hardware intact. The Internet packet format is not tied directly to any hardware. The underlying hardware does not understand or recognize an Internet packet.22.5 What is the maximum length of an IP datagram?In the current version of the Internet Protocol (IP version 4), a datagram can contain at most 64 K (65535) octets, including the header.22.7 If a datagram contains one 8-bit data value and no header options, what values will be found in header fields H.LEN and TOTAL LENGTH?Answer: H. LEN indicated header in 32-quantities, since no options, then this value will be 5. The TOTAL LENGTH indicated the number of bytes in a datagram including the header. This means 5x4 bytes + 1 (8-bits) = 21 bytesChapter 23 - Support Protocols And Technologies23.1 When a router uses a forwarding table to look up a next-hop address, the result is an IP address. What must happenbefore the datagram can be sent?Answer: Each router along the path uses the destination IP address in the datagram to select a next-hop address, encapsulates the datagram in a hardware frame, and transmits the frame across one network. A crucial step of the forwarding process requires a translation: forwarding uses IP addresses, and a frame transmitted across a physical network must contain the MAC address of the next hop.23.2 What term is used to describe the mapping between a protocol address and a hardware address?Answer: Translation from a computer’s IP address to an equivalent hardware address is known as address resolution, and an IP address is said to be resolved to the correct MAC address. The TCP/IP protocol being used for this is called Address Resolution Protocol (ARP). Address resolution is local to a network.23.5 How many octets does an ARP message occupy when used with IP and Ethernet addresses?Answer: According to Fig 23.3 an ARP message has 7-lines of each being 32-bit (4 bytes or octets), therefore,number of octets in an ARP can be determined as 7x4 = 28 octets23.10 What types of addresses are used in layers below ARP?Answer:ARP forms a conceptual boundary in the protocol stack; layers above ARP use IP addresses, and layers below ARP use MAC addresses.23.17 What is the chief difference between BOOTP and DHCP?Answer:The main difference is that the BOOTP protocol required manual administration. So before a computer could use BOOTP to obtain an address, a network administrator had to configure a BOOTP server to know the computer’s I P address. Chapter 24 - The Future IP (IPv6)24.3 List the major features of IPv6, and give a short description of each.(See Textbook)24.4 How large is the smallest IPv6 datagram header?Answer: IPv6 datagram header consists of a base header + zero or more extension header. Since, smallest header is being asked, we assume zero extension header and consider IPv6 will have only base header. If we look at IPv6 header format in Fig. 24.3, it shows that 10x4 bytes = 40 bytes.Chapter 26 - TCP: Reliable Transport Service26.2 List the features of TCP.(See Textbook)26.6 When using a sliding window of size N, how many packets can be sent without requiring a single ACK to be received?Answer: If the size of the window is N, then it means a sender can transmit up to N packets without waiting for an ACK, as long as other controls are in place.26.9 What is the chief cause of packet delay and loss in the Internet?Answer: The main cause of packet delay and loss in the Internet is congestion.Chapter 28 - Network Performance (QoS and DiffServ)28.1 List and describe the three primary measures of network performance.(See Textbook)28.2 Give five types of delay along with an explanation of each.(See Textbook)Chapter 30 - Network Security30.1 List the major security problems on the Internet, and give a short description of each.(See Textbook)30.2 Name the technique used in security attacks.(See Textbook)30.8 List and describe the eight basic security techniques.(See Textbook)。

ANDREW S. TANENBAUM由于请求和应答都必须通过卫星,因此传输总路径长度为和真空中的光速为300,000 公里/秒,因此最佳的传播延迟为160,000/300,000medium-speed line, a low-speed line, or no line. If it takes 100 ms of computer timeto generate and inspect each topology, how long will it take to inspect all ofthem?(E)将路由器称为A,B,C,D 和 E.则有10 条可能的线路;AB, AC, AD, AE, BC, BD, BE, CD, CE,和DE每条线路有 4 种可能性(3 速度或者不是线路),拓扑的总数为410 = 1,048,576。
检查每个拓扑需要100 ms,全部检查总共需要104,857. 6 秒,或者稍微超过29 个小时。
9. A group of 2n - 1 routers are interconnected in a centralized binary tree, with a router at each tree node. Router i communicates with router j by sending a message to the root of the tree. The root then sends the message back down to j. Derive an approximate expression for the mean number of hops per message for large n, assuming that all router pairs are equally likely.(H)这意味着,从路由器到路由器的路径长度相当于路由器到根的两倍。

《计算机网络》中英文对照表Chapter 11.1Internet:因特网Computer network :计算机网络Host: 主机End system: 终端系统Packet switching: 分组交换Route: 路径Internet service provider (ISP): 因特网服务提供商Protocol: 协议Transmission Control Protocol (TCP):传输控制协议1.2Client: 客户端Server: 服务器Peer: 对等机Reliable data transfer: 可靠数据传输Flow control: 流量控制Congestion-control: 拥塞控制User Datagram Protocol (UDP): 用户数据报协议1.3Circuit switching: 电路交换/线路交换Packet switching: 分组交换Frequency-division multiplexing (FDM): 频分多路复用Time-division multiplexing (TDM): 时分多路复用Bandwidth: 带宽Time slot: 时隙Frame: 帧Message: 报文:Packet: 分组Store-and-forward: 存储转发Datagram network: 数据报网络Virtual-circuit network: 虚电路网络1.4Router: 路由器Modem: 调制解调器Local area network (LAN): 局域网Ethernet: 以太网Wireless LAN: 无线局域网Guided media: 导向型介质Unguided media: 非导向型介质Twisted-pair copper wire: 双绞线Unshielded twisted pair(UTP): 非屏蔽双绞线Coaxial cable: 同轴电缆Fiber optics: 光线/光缆1.6Nodal processing delay: 结点处理延迟Queuing delay: 排队延迟Transmission delay: 发送延迟Propagation delay: 传播延迟Traffic intensity: 流通强度End-to-end delay: 端到端延迟1.7Layer: 层次Protocol stack: 协议栈Application layer: 应用层Transport layer: 传输层Network layer: 网络层Link layer: 链路层Physical layer: 物理层Encapsulation: 封装Message: 报文Segment: 报文段Datagram: 数据报Frame: 帧Chapter 22.1Client-server architecture: 客户端-服务器体系结构;C/S结构P2P architecture: 对等结构Processes: 进程Socket: 套接字Application programming interface (API): 应用程序编程接口IP address: IP地址Prot number: 端口号Syntax: 语法Semantics: 语义Full-duplex: 全双工Handshaking: 握手Real-time application: 实时应用2.2The World Wide Web: 万维网HyperText Transfer Protocol (HTTP): 超文本传输协议Web page: 网页Object: 对象HyperText Markup Language (HTML): 超文本标记语言URL:统一资源定位符Browser: 浏览器Persistent connection: 持久连接Non-persistent connection: 非持久连接Round-trip time (RTT): 往返时间Without pipelining: 非流水线方式With pipelining: 流水线方式Web cache: web 缓存Proxy server: 代理服务器2.3File Transfer Protocol (FTP): 文件传输协议Control connection: 控制连接Data connection: 数据连接Out-of-band: 带外In-band: 带内2.4Electronic Mail: 电子邮件User agent: 用户代理Mail server: 邮件服务器Simple Mail Transfer Protocol (SMTP): 简单邮件传输协议Mailbox: 邮箱Multipurpose Internet Mail Extensions (MIME): 多用途因特网邮件扩展协议Post Office Protocol (POP): 邮局协议Internet Mail Access Protocol (IMAP): Internet 邮件访问协议2.5Domain Name System (DNS): 域名系统Hostname: 主机名Host aliasing: 主机别名Mail server aliasing: 邮件服务器别名Load distribution: 负载分配Root DNS server: 根DNS服务器Top-Level Domain (TLD) servers: 顶级域DNS服务器Authoritative DNS servers: 授权DNS服务器;权威DNS服务器Local DNS server: 本地DNS服务器Database: 数据库Chapter 33.1Logical communication: 逻辑通讯3.2Multiplexing: 多路复用Demultiplexing: 多路分解Well-known port number: 众所周知的端口号3.3UDP segment: UDP报文段Checksum: 校验和;检查和Wrapped around: 回卷3.4Channel: 通道;信道Positive acknowledgement : 肯定应答Negative acknowledgement: 否定应答ARQ (automatic repeat request): 自动重传请求Feedback: 反馈Retransmission: 重传Stop-and-wait protocol: 停止-等待协议Duplicate packets: 冗余分组Sequence number: 顺序号Timer: 定时器Alternating-bit protocol: 比特交替协议Utilization: 利用率Go-back-N (GBN): 回退N步Window size: 窗口大小Sliding-window protocol: 滑动窗口协议Cumulative acknowledgement: 累积确认Timeout: 超时Selective Repeat (SR): 选择重传3.5Connection-oriented: 面向连接Point-to-point: 点到点Three-way handshake: 三次握手Maximum segment size (MSS): 最大报文段大小Maximum transmission unit (MTU): 最大传输单元Piggybacked: 捎带Sample RTT: 样本RTTFast retransmit: 快速重传Selective acknowledgement: 选择确认Flow-control: 流量控制Receive window: 接收窗口3.7Congestion control: 拥塞窗口Self-clocking: 自定时的Additive-increase, multiplicative-decrease: 加性增,乘性减Slow star: 慢启动Congestion avoidance: 拥塞避免Threshold: 阈值Fast recovery: 快速恢复Bottleneck: 瓶颈Latency: 延迟Chapter 44.1Forwarding: 转发Routing: 路由Routing algorithm: 路由算法Forwarding table: 转发表Router: 路由器Jitter: 抖动Best-effort service: 尽力而为的服务4.2Virtual-circuit (VC) network: 虚电路网络Datagram network: 数据报网络Prefix: 前缀Longest prefix matching rule: 最长前缀匹配规则4.3Input port: 输入端口Switching fabric: 交换结构Routing processor: 路由处理器Crossbar: 交叉结构4.4Time-to-live (TTL) :生存时间Fragmentation: 分片;片段Dotted-decimal notation: 点分十进制表示法Subnet: 子网Subnet mask: 子网掩码Classless Interdomain Routing (CIDR): 无类别域际路由选择Dynamic Host Configuration Protocol(DHCP):动态主机配置协议Plug-and-play: 即插即用Network address translation (NA T): 网络地址转换Internet Control Message Protocol (ICMP): 因特网控制报文协议Dual-stack: 双栈Tunneling: 隧道4.5Default router: 默认路由器Graph: 图A global routing algorithm : 全局路由算法A decentralized routing algorithm : 分布式路由算法Static routing algorithm: 静态路由算法Dynamic routing algorithm : 动态路由算法Link-State (LS): 链路状态Distance-Vector(DV): 距离向量Routing table: 路由表Autonomous system (AS): 自治系统Intra-autonomous system routing protocol: 自治系统内路由协议Inter-AS routing protocol: 自治系统间路由协议4.6Interior gateway protocol: 内部网关协议Routing Information Protocol (RIP): 路由信息协议Open Shortest Path First (OSPF): 开放最短路径优先协议Advertisement: 公告Hop: 跳Border Gateway Protocol (BGP): 边界网关协议4.7Broadcast: 广播Multicast: 多播Chapter 55.1Node: 结点Link: 链路Frame: 帧Medium access control (MAC): 介质访问控制Full-duplex: 全双工Half-duplex: 半双工Adapter: 适配器Network interface card (NIC): 网卡Interface: 接口5.2Parity check: 奇偶校验Odd: 奇数Even: 偶数Cyclic redundancy check (CRC): 循环冗余校验Polynomial: 多项式5.3Collide: 冲突Multiple access protocol: 多路访问协议Channel partitioning protocol: 信道划分协议Random access protocol: 随机访问协议Taking-turns protocol: 轮转协议Code division multiple access (CDMA): 码分多址访问Carrier sensing: 载波侦听Collision detection: 冲突检测Polling protocol: 轮询协议Token-passing protocol: 令牌传递协议Token: 令牌Local Area Network (LAN): 局域网Token-ring: 令牌环Fiber distributed data interface (FDDI): 光纤分布式数据接口Metropolitan Area Network (MAN): 城域网5.4Address Resolution Protocol (ARP): 地址解析协议Dynamic Host Configuration Protocol (DHCP): 动态主机配置协议5.5Ethernet: 以太网Preamble: 前导码Manchester encoding: 曼彻斯特编码5.6Hub: 集线器Collision domain: 冲突域Switch: 交换机Filtering: 过滤Forwarding: 转发Switch table: 交换表Self-learning: 自学习Plug-and-play devices: 即插即用设备Cut-through switching: 直通式交换5.7Point-to-point: (PPP): 点到点。

Computer Networking: A Top-Down Approach,7th EditionSolutions to Review Questions and Problems Version Date: December 2016This document contains the solutions to review questions and problems for the 7th edition of Computer Networking: A Top-Down Approach by Jim Kurose and Keith Ross. These solutions are being made available to instructors ONLY. Please do NOT copy or distribute this document to others (even other instructors). Please do not post any solutions on a publicly-available Web site. We’ll be happy to provide a copy (up-to-date) of this solution manual ourselves to anyone who asks.Acknowledgments:Over the years, several students and colleagues have helped us prepare this solutions manual. Special thanks goes to Honggang Zhang, Rakesh Kumar, Prithula Dhungel, and Vijay Annapureddy. Also thanks to all the readers who have made suggestions and corrected errors.All material © copyright 1996-2016 by J.F. Kurose and K.W. Ross. All rights reserved Chapter 1 Review Questions1.There is no difference. Throughout this text, the words “host” and “end system” areused interchangeably. End systems include PCs, workstations, Web servers, mail servers, PDAs, Internet-connected game consoles, etc.2.From Wikipedia: Diplomatic protocol is commonly described as a set of internationalcourtesy rules. These well-established and time-honored rules have made it easier for nations and people to live and work together. Part of protocol has always been the acknowledgment of the hierarchical standing of all present. Protocol rules are based on the principles of civility.3.Standards are important for protocols so that people can create networking systemsand products that interoperate.4. 1. Dial-up modem over telephone line: home; 2. DSL over telephone line: home orsmall office; 3. Cable to HFC: home; 4. 100 Mbps switched Ethernet: enterprise; 5.Wifi (802.11): home and enterprise: 6. 3G and 4G: wide-area wireless.5.HFC bandwidth is shared among the users. On the downstream channel, all packetsemanate from a single source, namely, the head end. Thus, there are no collisions in the downstream channel.6.In most American cities, the current possibilities include: dial-up; DSL; cable modem;fiber-to-the-home.7. Ethernet LANs have transmission rates of 10 Mbps, 100 Mbps, 1 Gbps and 10 Gbps.8. Today, Ethernet most commonly runs over twisted-pair copper wire. It also can runover fibers optic links.9. Dial up modems: up to 56 Kbps, bandwidth is dedicated; ADSL: up to 24 Mbpsdownstream and 2.5 Mbps upstream, bandwidth is dedicated; HFC, rates up to 42.8 Mbps and upstream rates of up to 30.7 Mbps, bandwidth is shared. FTTH: 2-10Mbps upload; 10-20 Mbps download; bandwidth is not shared.10. There are two popular wireless Internet access technologies today:a)Wifi (802.11) In a wireless LAN, wireless users transmit/receive packets to/from anbase station (i.e., wireless access point) within a radius of few tens of meters. The base station is typically connected to the wired Internet and thus serves to connect wireless users to the wired network.b)3G and 4G wide-area wireless access networks. In these systems, packets aretransmitted over the same wireless infrastructure used for cellular telephony, with the base station thus being managed by a telecommunications provider. This provides wireless access to users within a radius of tens of kilometers of the base station.11. At time t0the sending host begins to transmit. At time t1 = L/R1, the sending hostcompletes transmission and the entire packet is received at the router (no propagationdelay). Because the router has the entire packet at time t 1, it can begin to transmit the packet to the receiving host at time t 1. At time t 2 = t 1 + L/R 2, the router completes transmission and the entire packet is received at the receiving host (again, no propagation delay). Thus, the end-to-end delay is L/R 1 + L/R 2.12. A circuit-switched network can guarantee a certain amount of end-to-end bandwidth for the duration of a call. Most packet-switched networks today (including the Internet) cannot make any end-to-end guarantees for bandwidth. FDM requires sophisticated analog hardware to shift signal into appropriate frequency bands .13. a) 2 users can be supported because each user requires half of the link bandwidth.b) Since each user requires 1Mbps when transmitting, if two or fewer users transmit simultaneously, a maximum of 2Mbps will be required. Since the available bandwidth of the shared link is 2Mbps, there will be no queuing delay before the link. Whereas, if three users transmit simultaneously, the bandwidth required will be 3Mbps which is more than the available bandwidth of the shared link. In this case, there will be queuing delay before the link.c) Probability that a given user is transmitting = 0.2d) Probability that all three users are transmitting simultaneously = ()333133--⎪⎪⎭⎫ ⎝⎛p p = (0.2)3 = 0.008. Since the queue grows when all the users are transmitting, thefraction of time during which the queue grows (which is equal to the probability that all three users are transmitting simultaneously) is 0.008.14. If the two ISPs do not peer with each other, then when they send traffic to each other they have to send the traffic through a provider ISP (intermediary), to which they have to pay for carrying the traffic. By peering with each other directly, the two ISPs can reduce their payments to their provider ISPs. An Internet Exchange Points (IXP) (typically in a standalone building with its own switches) is a meeting point where multiple ISPs can connect and/or peer together. An ISP earns its money by charging each of the the ISPs that connect to the IXP a relatively small fee, which may depend on the amount of traffic sent to or received from the IXP.15. Google's private network connects together all its data centers, big and small. Traffic between the Google data centers passes over its private network rather than over the public Internet. Many of these data centers are located in, or close to, lower tier ISPs. Therefore, when Google delivers content to a user, it often can bypass higher tier ISPs. What motivates content providers to create these networks? First, the content provider has more control over the user experience, since it has to use few intermediary ISPs. Second, it can save money by sending less traffic into provider networks. Third, if ISPs decide to charge more money to highly profitable content providers (in countries where net neutrality doesn't apply), the content providers can avoid these extra payments.16. The delay components are processing delays, transmission delays, propagation delays,and queuing delays. All of these delays are fixed, except for the queuing delays, which are variable.17. a) 1000 km, 1 Mbps, 100 bytesb) 100 km, 1 Mbps, 100 bytes18. 10msec; d/s; no; no19. a) 500 kbpsb) 64 secondsc) 100kbps; 320 seconds20. End system A breaks the large file into chunks. It adds header to each chunk, therebygenerating multiple packets from the file. The header in each packet includes the IP address of the destination (end system B). The packet switch uses the destination IP address in the packet to determine the outgoing link. Asking which road to take is analogous to a packet asking which outgoing link it should be forwarded on, given the packet’s destination address.21. The maximum emission rate is 500 packets/sec and the maximum transmission rate is350 packets/sec. The corresponding traffic intensity is 500/350 =1.43 > 1.Loss will eventually occur for each experiment;but the time when loss first occurs will be different from one experiment to the next due to the randomness in the emission process.22. Five generic tasks are error control, flow control, segmentation and reassembly,multiplexing, and connection setup. Yes, these tasks can be duplicated at different layers. For example, error control is often provided at more than one layer.23. The five layers in the Internet protocol stack are –from top to bottom –theapplication layer, the transport layer, the network layer, the link layer, and the physical layer. The principal responsibilities are outlined in Section 1.5.1.24. Application-layer message: data which an application wants to send and passed ontothe transport layer; transport-layer segment: generated by the transport layer and encapsulates application-layer message with transport layer header; network-layer datagram: encapsulates transport-layer segment with a network-layer header; link-layer frame: encapsulates network-layer datagram with a link-layer header.25. Routers process network, link and physical layers (layers 1 through 3). (This is a littlebit of a white lie, as modern routers sometimes act as firewalls or caching components, and process Transport layer as well.) Link layer switches process link and physical layers (layers 1 through2). Hosts process all five layers.26. a) VirusRequires some form of human interaction to spread. Classic example: E-mail viruses.b) WormsNo user replication needed. Worm in infected host scans IP addresses and portnumbers, looking for vulnerable processes to infect.27. Creation of a botnet requires an attacker to find vulnerability in some application orsystem (e.g. exploiting the buffer overflow vulnerability that might exist in an application). After finding the vulnerability, the attacker needs to scan for hosts that are vulnerable. The target is basically to compromise a series of systems by exploiting that particular vulnerability. Any system that is part of the botnet can automatically scan its environment and propagate by exploiting the vulnerability. An important property of such botnets is that the originator of the botnet can remotely control and issue commands to all the nodes in the botnet. Hence, it becomes possible for the attacker to issue a command to all the nodes, that target a single node (for example, all nodes in the botnet might be commanded by the attacker to send a TCP SYN message to the target, which might result in a TCP SYN flood attack at the target).28. Trudy can pretend to be Bob to Alice (and vice-versa) and partially or completelymodify the message(s) being sent from Bob to Alice. For example, she can easily change the phrase “Alice, I owe you $1000” to “Alice, I owe you $10,000”.Furthermore, Trudy can even drop the packets that are being sent by Bob to Alice (and vise-versa), even if the packets from Bob to Alice are encrypted.Chapter 1 ProblemsProblem 1There is no single right answer to this question. Many protocols would do the trick. Here's a simple answer below:Messages from ATM machine to ServerMsg name purpose-------- -------HELO <userid> Let server know that there is a card in theATM machineATM card transmits user ID to ServerPASSWD <passwd> User enters PIN, which is sent to server BALANCE User requests balanceWITHDRAWL <amount> User asks to withdraw moneyBYE user all doneMessages from Server to ATM machine (display)Msg name purpose-------- -------PASSWD Ask user for PIN (password)OK last requested operation (PASSWD, WITHDRAWL)OKERR last requested operation (PASSWD, WITHDRAWL)in ERRORAMOUNT <amt> sent in response to BALANCE requestBYE user done, display welcome screen at ATM Correct operation:client serverHELO (userid) --------------> (check if valid userid)<------------- PASSWDPASSWD <passwd> --------------> (check password)<------------- OK (password is OK)BALANCE --------------><------------- AMOUNT <amt>WITHDRAWL <amt> --------------> check if enough $ to coverwithdrawl<------------- OKATM dispenses $BYE --------------><------------- BYEIn situation when there's not enough money:HELO (userid) --------------> (check if valid userid)<------------- PASSWDPASSWD <passwd> --------------> (check password)<------------- OK (password is OK)BALANCE --------------><------------- AMOUNT <amt>WITHDRAWL <amt> --------------> check if enough $ to cover withdrawl<------------- ERR (not enough funds)error msg displayedno $ given outBYE --------------><------------- BYEProblem 2At time N*(L/R) the first packet has reached the destination, the second packet is stored in the last router, the third packet is stored in the next-to-last router, etc. At time N*(L/R) + L/R, the second packet has reached the destination, the third packet is stored in the last router, etc. Continuing with this logic, we see that at time N*(L/R) + (P-1)*(L/R) = (N+P-1)*(L/R) all packets have reached the destination.Problem 3a) A circuit-switched network would be well suited to the application, because theapplication involves long sessions with predictable smooth bandwidth requirements.Since the transmission rate is known and not bursty, bandwidth can be reserved for each application session without significant waste. In addition, the overhead costs of setting up and tearing down connections are amortized over the lengthy duration of a typical application session.b) In the worst case, all the applications simultaneously transmit over one or morenetwork links. However, since each link has sufficient bandwidth to handle the sum of all of the applications' data rates, no congestion (very little queuing) will occur.Given such generous link capacities, the network does not need congestion control mechanisms.Problem 4a)Between the switch in the upper left and the switch in the upper right we can have 4connections. Similarly we can have four connections between each of the 3 other pairs of adjacent switches. Thus, this network can support up to 16 connections.b)We can 4 connections passing through the switch in the upper-right-hand corner andanother 4connections passing through the switch in the lower-left-hand corner, giving a total of 8 connections.c) Yes. For the connections between A and C, we route two connections through B and two connections through D. For the connections between B and D, we route two connections through A and two connections through C. In this manner, there are at most 4 connections passing through any link.Problem 5Tollbooths are 75 km apart, and the cars propagate at 100km/hr. A tollbooth services a car at a rate of one car every 12 seconds.a) There are ten cars. It takes 120 seconds, or 2 minutes, for the first tollbooth to service the 10 cars. Each of these cars has a propagation delay of 45 minutes (travel 75 km) before arriving at the second tollbooth. Thus, all the cars are lined up before the second tollbooth after 47 minutes. The whole process repeats itself for traveling between the second and third tollbooths. It also takes 2 minutes for the third tollbooth to service the 10 cars. Thus the total delay is 96 minutes.b) Delay between tollbooths is 8*12 seconds plus 45 minutes, i.e., 46 minutes and 36 seconds. The total delay is twice this amount plus 8*12 seconds, i.e., 94 minutes and 48 seconds.Problem 6a) s m d prop /= seconds.b) R L d trans /= seconds.c) )//(R L s m d end to end +=-- seconds.d) The bit is just leaving Host A.e) The first bit is in the link and has not reached Host B.f) The first bit has reached Host B. g) Want()536105.2105612083=⨯⨯==s R L m km.Problem 7Consider the first bit in a packet. Before this bit can be transmitted, all of the bits in the packet must be generated. This requires31064856⨯⋅sec=7msec.The time required to transmit the packet is6102856⨯⋅sec=μ224sec.Propagation delay = 10 msec.The delay until decoding is7msec +μ224sec + 10msec = 17.224msecA similar analysis shows that all bits experience a delay of 17.224 msec.Problem 8a) 20 users can be supported.b) 1.0=p .c) ()n n p p n --⎪⎪⎭⎫ ⎝⎛1201120. d) ()∑=--⎪⎪⎭⎫ ⎝⎛-20012011201n n n p p n . We use the central limit theorem to approximate this probability. Let j X be independentrandom variables such that ()p X P j ==1.(P “21 or more users”)⎪⎪⎭⎫ ⎝⎛≤-=∑=2111201j j X P⎪⎪⎪⎭⎫ ⎝⎛⋅⋅≤⋅⋅-=⎪⎪⎭⎫ ⎝⎛≤∑∑==9.01.012099.01.0120122112011201j j j j X P X P ()74.2286.39≤=⎪⎭⎫ ⎝⎛≤≈Z P Z P 997.0=when Z is a standard normal r.v. Thus (P “21 or more users”)003.0≈.Problem 9a) 10,000b) ()∑+=--⎪⎪⎭⎫ ⎝⎛M N n n M n p p n M 11Problem 10The first end system requires L/R1 to transmit the packet onto the first link; the packet propagates over the first link in d1/s1; the packet switch adds a processing delay of d proc; after receiving the entire packet, the packet switch connecting the first and the second link requires L/R2 to transmit the packet onto the second link; the packet propagates over the second link in d2/s2. Similarly, we can find the delay caused by the second switch and the third link: L/R3, d proc, and d3/s3.Adding these five delays givesd end-end = L/R1 + L/R2 + L/R3 + d1/s1 + d2/s2 + d3/s3+ d proc+ d procTo answer the second question, we simply plug the values into the equation to get 6 + 6 + 6 + 20+16 + 4 + 3 + 3 = 64 msec.Problem 11Because bits are immediately transmitted, the packet switch does not introduce any delay; in particular, it does not introduce a transmission delay. Thus,d end-end = L/R + d1/s1 + d2/s2+ d3/s3For the values in Problem 10, we get 6 + 20 + 16 + 4 = 46 msec.Problem 12The arriving packet must first wait for the link to transmit 4.5 *1,500 bytes = 6,750 bytes or 54,000 bits. Since these bits are transmitted at 2 Mbps, the queuing delay is 27 msec. Generally, the queuing delay is (nL + (L - x))/R.Problem 13a)The queuing delay is 0 for the first transmitted packet, L/R for the second transmittedpacket, and generally, (n-1)L/R for the n th transmitted packet. Thus, the average delay for the N packets is:(L/R + 2L/R + ....... + (N-1)L/R)/N= L/(RN) * (1 + 2 + ..... + (N-1))= L/(RN) * N(N-1)/2= LN(N-1)/(2RN)= (N-1)L/(2R)Note that here we used the well-known fact:1 +2 + ....... + N = N(N+1)/2b) It takes R LN / seconds to transmit the N packets. Thus, the buffer is empty when a each batch of N packets arrive. Thus, the average delay of a packet across all batches is the average delay within one batch, i.e., (N-1)L /2R .Problem 14a) The transmission delay is R L /. The total delay isI RL R L I R IL -=+-1/)1(b) Let R L x /=.Total delay = axx-1For x=0, the total delay =0; as we increase x, total delay increases, approaching infinity as x approaches 1/a.Problem 15Total delay aa R aL R L I R L -=-=-=-=μμμ1/1/1/1/1/.Problem 16The total number of packets in the system includes those in the buffer and the packet that is being transmitted. So, N=10+1.Because d a N ⋅=, so (10+1)=a*(queuing delay + transmission delay). That is, 11=a*(0.01+1/100)=a*(0.01+0.01). Thus, a=550 packets/sec.Problem 17a) There are Q nodes (the source host and the 1-Q routers). Let qproc d denote the processing delay at the q th node. Let q R be the transmission rate of the q th link and letq qtrans R L d /=. Let q prop d be the propagation delay across the q th link. Then[]∑=--++=Qq qprop q trans q proc end to end d d d d 1.b) Let qqueue d denote the average queuing delay at node q . Then[]∑=--+++=Qq qqueue q prop q trans q proc end to end d d d d d 1.Problem 18On linux you can use the commandtraceroute and in the Windows command prompt you can usetracert In either case, you will get three delay measurements. For those three measurements you can calculate the mean and standard deviation. Repeat the experiment at different times of the day and comment on any changes .Here is an example solution:Traceroutes between San Diego Super Computer Center and a)The average (mean) of the round-trip delays at each of the three hours is 71.18 ms,71.38 ms and 71.55 ms, respectively. The standard deviations are 0.075 ms, 0.21 ms,0.05 ms, respectively.b)In this example, the traceroutes have 12 routers in the path at each of the three hours.No, the paths didn’t change during any of the hours.c)Traceroute packets passed through four ISP networks from source to destination. Yes,in this experiment the largest delays occurred at peering interfaces between adjacent ISPs.Traceroutes from (France) to (USA).d)The average round-trip delays at each of the three hours are 87.09 ms, 86.35 ms and86.48 ms, respectively. The standard deviations are 0.53 ms, 0.18 ms, 0.23 ms,respectively. In this example, there are 11 routers in the path at each of the three hours. No, the paths didn’t change during any of the hours. Traceroute packets passed three ISP networks from source to destination. Yes, in this experiment the largest delays occurred at peering interfaces between adjacent ISPs.Problem 19An example solution:Traceroutes from two different cities in France to New York City in United States a)In these traceroutes from two different cities in France to the same destination host inUnited States, seven links are in common including the transatlantic link.b)In this example of traceroutes from one city in France and from another city inGermany to the same host in United States, three links are in common including the transatlantic link.Traceroutes to two different cities in China from same host in United Statesc) Five links are common in the two traceroutes. The two traceroutes diverge before reaching ChinaProblem 20Throughput = min{R s , R c , R/M}Problem 21If only use one path, the max throughput is given by:}},,,m in{,},,,,min{},,,,m ax {m in{212222111211MN M M N N R R R R R R R R R .If use all paths, the max throughput is given by ∑=Mk kN k k R R R 121},,,min{ .Problem 22Probability of successfully receiving a packet is: p s = (1-p)N .The number of transmissions needed to be performed until the packet is successfully received by the client is a geometric random variable with success probability p s . Thus, the average number of transmissions needed is given by: 1/p s . Then, the average number of re-transmissions needed is given by: 1/p s -1.Problem 23Let’s call the first packet A and call the second packet B.a) If the bottleneck link is the first link, then packet B is queued at the first link waiting for the transmission of packet A. So the packet inter-arrival time at the destination is simply L/R s .b) If the second link is the bottleneck link and both packets are sent back to back, it must be true that the second packet arrives at the input queue of the second link before the second link finishes the transmission of the first packet. That is,L/R s + L/R s + d prop < L/R s + d prop + L/R cThe left hand side of the above inequality represents the time needed by the second packet to arrive at the input queue of the second link (the second link has not startedtransmitting the second packet yet). The right hand side represents the time needed by the first packet to finish its transmission onto the second link.If we send the second packet T seconds later, we will ensure that there is no queuing delay for the second packet at the second link if we have:L/R s + L/R s + d prop + T >= L/R s + d prop + L/R cThus, the minimum value of T is L/R c L/R s .Problem 2440 terabytes = 40 * 1012 * 8 bits. So, if using the dedicated link, it will take 40 * 1012 * 8 / (100 *106 ) =3200000 seconds = 37 days. But with FedEx overnight delivery, you can guarantee the data arrives in one day, and it should cost less than $100.Problem 25a)160,000 bitsb)160,000 bitsc)The bandwidth-delay product of a link is the maximum number of bits that can be inthe link.d)the width of a bit = length of link / bandwidth-delay product, so 1 bit is 125 meterslong, which is longer than a football fielde) s/RProblem 26s/R=20000km, then R=s/20000km= 2.5*108/(2*107)= 12.5 bpsProblem 27a)80,000,000 bitsb)800,000 bits, this is because that the maximum number of bits that will be in the linkat any given time = min(bandwidth delay product, packet size) = 800,000 bits.c).25 metersProblem 28a)t trans + t prop = 400 msec + 80 msec = 480 msec.b)20 * (t trans + 2 t prop) = 20*(20 msec + 80 msec) = 2 sec.c) Breaking up a file takes longer to transmit because each data packet and its corresponding acknowledgement packet add their own propagation delays.Problem 29Recall geostationary satellite is 36,000 kilometers away from earth surface. a) 150 msec b) 1,500,000 bits c) 600,000,000 bitsProblem 30Let’s suppose the passenger and his/her bags correspond to the data unit arriving to the top of the protocol stack. When the passenger checks in, his/her bags are checked, and a tag is attached to the bags and ticket. This is additional information added in the Baggage layer if Figure 1.20 that allows the Baggage layer to implement the service or separating the passengers and baggage on the sending side, and then reuniting them (hopefully!) on the destination side. When a passenger then passes through security and additional stamp is often added to his/her ticket, indicating that the passenger has passed through a security check. This information is used to ensure (e.g., by later checks for the security information) secure transfer of people.Problem 31a)Time to send message from source host to first packet switch = sec 4sec 10210866=⨯⨯With store-and-forward switching, the total time to move message from source host to destination host = sec 123sec 4=⨯hopsb)Time to send 1st packet from source host to first packet switch = . sec 5sec 10210164m =⨯⨯. Time at which 2nd packet is received at the first switch = time at which 1st packet is received at the second switch = sec 10sec 52m m =⨯c)Time at which 1st packet is received at the destination host = sec 153sec 5m hops m =⨯. After this, every 5msec one packet will be received; thus time at which last (800th ) packet is received = sec 01.4sec 5*799sec 15=+m m . It can be seen that delay in using message segmentation is significantly less (almost 1/3rd ). d)i. Without message segmentation, if bit errors are not tolerated, if there is asingle bit error, the whole message has to be retransmitted (rather than a single packet).ii. Without message segmentation, huge packets (containing HD videos, forexample) are sent into the network. Routers have to accommodate these hugepackets. Smaller packets have to queue behind enormous packets and suffer unfair delays.e)i. Packets have to be put in sequence at the destination.ii. Message segmentation results in many smaller packets. Since header size is usually the same for all packets regardless of their size, with message segmentation the total amount of header bytes is more.Problem 32Yes, the delays in the applet correspond to the delays in the Problem 31.The propagation delays affect the overall end-to-end delays both for packet switching and message switching equally.Problem 33There are F /S packets. Each packet is S=80 bits. Time at which the last packet is receivedat the first router is SFR S ⨯+80sec. At this time, the first F/S-2 packets are at thedestination, and the F/S-1 packet is at the second router. The last packet must then be transmitted by the first router and the second router, with each transmission taking R S 80+sec. Thus delay in sending the whole file is )2(80+⨯+=S FR S delay To calculate the value of S which leads to the minimum delay, F S delay dS d400=⇒=Problem 34The circuit-switched telephone networks and the Internet are connected together at "gateways". When a Skype user (connected to the Internet) calls an ordinary telephone, a circuit is established between a gateway and the telephone user over the circuit switched network. The skype user's voice is sent in packets over the Internet to the gateway. At the gateway, the voice signal is reconstructed and then sent over the circuit. In the other direction, the voice signal is sent over the circuit switched network to the gateway. The gateway packetizes the voice signal and sends the voice packets to the Skype user.。

计算机网络英文题库附答案c h a p t e r精编W O R D版IBM system office room 【A0816H-A0912AAAHH-GX8Q8-GNTHHJ8】Chapter 1 Computer Networks and the Internet 1.The ( ) is a worldwide computer network, that is, a network that interconnects millions of computing devices throughout the world.ppt3A public InternetB IntranetC switch netD television net2.Which kind of media is not a guided media ( )A twisted-pair copper wireB a coaxial cableC fiber opticsD digital satellite channel3.Which kind of media is a guided media ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN4.The units of data exchanged by a link-layer protocol are called ( ).A FramesB SegmentsC DatagramsD bit streams5.Which of the following option belongs to the circuit-switched networks ( )A FDMB TDMC VC networksD both A and B6.( )makes sure that neither side of aconnection overwhelms the other side bysending too many packets too fast.A Reliable data transferB Flow controlC Congestion controlD Handshaking procedure7.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Store-and-forward transmissionB FDMC End-to-end connectionD TDM8.Datagram networks and virtual-circuit networks differ in that ( ).A datagram networks are circuit-switchednetworks, and virtual-circuit networks arepacket-switched networks.B datagram networks are packet-switchednetworks, and virtual-circuit networks arecircuit-switched networks.C datagram networks use destinationaddresses and virtual-circuit networks useVC. numbers to forward packets towardtheir destination.D datagram networks use VC. numbersand virtual-circuit networks use destinationaddresses to forward packets toward theirdestination.9.In the following options, which one is not a guided media ( )A twisted-pair wireB fiber opticsC coaxial cableD satellite10.Processing delay does not include the time to ( ).A examine the packet’s headerB wait to transmit the packet onto the linkC determine where to direct the packetD check bit-error in the packet11.In the following four descriptions, which one is correct ( )A The traffic intensity must be greaterthan 1.B The fraction of lost packets increases asthe traffic intensity decreases.C If the traffic intensity is close to zero,the average queuing delay will be close tozero.D If the traffic intensity is close to one, theaverage queuing delay will be close to one.12.The Internet’s network layer isresponsible for moving network-layerpackets known as ( ) from one host toanother.A frameB datagramC segmentD message13.The protocols of various layers are called ( ).A the protocol stackB TCP/IPC ISPD network protocol14.There are two classes of packet-switched networks: ( ) networks and virtual-circuitnetworks.A datagramB circuit-switchedC televisionD telephone15.Access networks can be loosely classified into three categories: residential access,company access and ( ) access.A cabledB wirelessC campusD city areaQuestion 16~17Suppose, a is the average rate at which packets arrive at the queue, R is the transmission rate, and all packets consist of L bits, then the traffic intensity is ( 16 ), and it should no greater than ( 17 ).16.A LR/aB La/RC Ra/LD LR/a 17.A 2B 1C 0D -118.In the Internet, the equivalent concept to end systems is ( ).A hostsB serversC clientsD routers19.In the Internet, end systems are connected together by ( ).A copper wireB coaxial cableC communication linksD fiber optics20.End systems access to the Internet through its ( ).A modemsB protocolsC ISPD sockets21.End systems, packet switches, and other pieces of the Internet, run ( ) that controlthe sending and receiving of informationwithin the Internet.A programsB processesC applicationsD protocols22.There are many private networks, such as many corporate and government networks,whose hosts cannot exchange messageswith hosts outside of the private network.These private networks are often referredto as ( ).A internetsB LANC intranetsD WAN23.The internet allows ( ) running on its end systems to exchange data with each other.A clients applicationsB server applicationsC P2P applicationsD distributed applications24.The Internet provides two services to its distributed applications: a connectionlessunreliable service and () service.A flow controlB connection-oriented reliableC congestion controlD TCP25.It defines the format and the order of messages exchanged between two or morecommunicating entities, as well as theactions taken on the transmission and/orreceipt of a message or other event. Thesentence describes ( ).A InternetB protocolC intranetD network26.In the following options, which does not define in protocol ( )A the format of messages exchangedbetween two or more communicatingentitiesB the order of messages exchangedbetween two or more communicatingentitiesC the actions taken on the transmission ofa message or other eventD the transmission signals are digitalsignals or analog signals27.In the following options, which is defined in protocol ( )A the actions taken on the transmissionand/or receipt of a message or othereventB the objects exchanged between communicating entitiesC the content in the exchanged messagesD the location of the hosts28.In the following options, which does not belong to the network edge ( )A end systemsB routersC clientsD servers29.In the following options, which belongs to the network core ( )A end systemsB routersC clientsD servers30.In the following options, which is not the bundled with the Internet’s connection-oriented service( )A reliable data transferB guarantee of the transmission timeC flow controlD congestion-control31.An application can rely on the connection to deliver all of its data without error andin the proper order. The sentencedescribes ( ).A flow controlB congestion-controlC reliable data transferD connection-oriented service32.It makes sure that neither side of aconnection overwhelms the other side bysending too many packets too fast. Thesentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer33.It helps prevent the Internet from enteringa state of gridlock. When a packet switchbecomes congested, its buffers canoverflow and packet loss can occur. Thesentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer34.The Internet’s connection-oriented service has a name, it is ( ).A TCPB UDPC TCP/IPD IP 35.In the following options, which service does not be provided to an application by TCP( )A reliable transportB flow controlC video conferencingD congestion control36.The Internet’s connectionless service is called ( ).A TCPB UDPC TCP/IPD IP37.In the following options, which does not use TCP()A SMTPB internet telephoneC FTPD HTTP38.In the following options, which does not use UDP( )A Internet phoneB video conferencingC streaming multimediaD telnet39.There are two fundamental approaches to building a network core, ( ) and packetswitching.A electrical current switchingB circuit switchingC data switchingD message switching40.In ( ) networks, the resources needed along a path to provide forcommunication between the end systemare reserved for the duration of thecommunication session.A packet-switchedB data-switchedC circuit-switchedD message-switched41.In ( ) networks, the resources are not reserved; a session’s messages use theresources on demand, and as aconsequence, may have to wait for accessto communication link.A packet-switchedB data-switchedC circuit-switchedD message-switched42.In a circuit-switched network, if each link has n circuits, for each link used by theend-to-end connection, the connectiongets ( ) of the link’s bandwidth for theduration of the connection.A a fraction 1/nB allC 1/2D n times43.For ( ), the transmission rate of a circuit is equal to the frame rate multiplied by thenumber of bits in a slot.A CDMAB packet-switched networkC TDMD FDM 44.( ) means that the switch must receive the entire packet before it can begin totransmit the first bit of the packet onto theoutbound link.A Queuing delayB Store-and-forward transmissionC Packet lossD Propagation45.The network that forwards packetsaccording to host destination addresses iscalled ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram46.The network that forwards packetsaccording to virtual-circuit numbers iscalled ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram47.In the following entries, which is not a kind of access network()A residential accessB company accessC wireless accessD local access48.Suppose there is exactly one packet switch between a sending host and a receivinghost. The transmission rates between thesending host and the switch and betweenthe switch and the receiving host are R1and R2, respectively. Assuming that theswitch uses store-and-forward packetswitching, what is the total end-to-enddelay to send a packet of length L (Ignorequeuing delay, propagation delay, andprocessing delay.) ( )A L/R1+L/R2B L/R1C L/R2D none of the above49.The time required to examine thepacket’s header and determine where todirect the packet is part of the ( ).A queuing delayB processing delayC propagation delayD transmission delay50.The time required to propagate from the beginning of the link to the next router is( ).A queuing delayB processing delayC propagation delayD transmission delay51.Consider sending a packet of 3000bits over a path of 5 links. Each link transmits at 1000bps. Queuing delays, propagation delay and processing delay are negligible. (6 points) (1).Suppose the network is a packet-switched virtual circuit network. VC setup time is 0.1 seconds. Suppose the sending layers add a total of 500 bits of header to each packet. How long does it take to send the file from source to destination?(2).Suppose the network is a packet-switched datagram network and a connectionless serviceis used. Now suppose each packet has 200 bitsof header. How long does it take to send the file?(3).Suppose that the network is a circuit-switched network. Further suppose that the transmission rate of the circuit between sourceand destination is 200bps. Assuming 0.02s setuptime and 200 bits of header appended to the packet, how long does it take to send the packet?So lution:(1).t=5*(3000+500)/1000+0.1=17.6s( 2).t=5*(3000+200)/1000=16s( 3).t=(3000+200)/200+0.02=16.02s。

计算机网络英文题库(附答案)c h a p t e r2本页仅作为文档封面,使用时可以删除This document is for reference only-rar21year.MarchChapter 2 Application Layer1. In the following four descriptions, which one is correctA In C/S architecture, clients communicate with each other directly.B In C/S architecture, client has a fixed well-known address.C In P2P architecture, peers communicate with each other directly.D In P2P architecture, peer has a fixed well-known address.2. In the context of a communication session between a pair of process, the process that initiates the communication is labeled as the , the process that waits to be contacted to begin the session is labeled as the .A client process, server processB sending process, receiving processC input process, output processD communicating process, connecting process3. A socket is the interface between within a host.A the network layer and the link layerB the link layer and the physical layerC the application layer and the transport layerD the transport layer and the network layer4. In the following applications, which one is a loss-tolerant applicationA E-mailB file transferC instant messagingD real-time audio5. In the following applications, which one is a bandwidth-sensitive applicationA E-mailB web applicationC real-time audioD file transfer6. The service of TCP can’t guarantee .A delivery of all data without errorB delivery of all data in the proper orderC the rate of deliveryD congestion control7. In the following applications, which one uses UDPA E-mailB web applicationC file transferD DNS8. In the following descriptions about HTTP, which one is not correctA HTTP uses non-persistent connections in its default mode.B HTTP uses TCP as its underlying transport protocol.C HTTP is a stateless protocol.D HTTP is client-server architecture.9. Suppose a web page consists of a base HTML file, 5 JEPG images and a java applet, and also suppose HTTP uses persistent connection without pipelining, the total response timeis .A 2RTTB 8RTTC 12 RTTD 14RTT10. In HTTP response message, if the requested HTTP protocol version is not supported, the status code is .A 200B 301C 400D 5051~5 CACDC 6~10 CDABD11. The port number of web application is .A 25B 20C 80D 5312. A network entity that satisfies HTTP requests on the behalf of an origin web server is .A server farmB server stackC proxy serverD edge server13. In the following descriptions about persistent connection, which one is not correctA The server leaves the TCP connection open after sending a response.B Each TCP connection is closed after the server sending one object.C There are two versions of persistent connection: without pipelining and with pipelining.D The default mode of HTTP uses persistent connection with pipelining.14. FTP uses two parallel TCP connections to transfer a file, there are .A control connection and data connectionB receiving connection and sending connectionC client connection and sever connectionD program connection and process connection15. In the following descriptions about FTP, which one is correctA FTP is p2p architecture.B FTP sends its control information out-of-band.C FTP uses persistent connection.D FTP is a stateless protocol.16. In the commands of FTP, which one does not have parameterA USERB PASSC LISTD STOR17. The Internet mail system has three components which they are .A user agent, SMTP, POP3B SMTP, POP3, IMAPC user agent, SMTP, IMAPD user agent, SMTP, mail server18. If the status code in HTTP response message is 404, it means .A Request succeeded.B The requested document doesn’t exit on this server.C This is a generic error code indicating that the request could not be understood by the server.D Requested object has been permanently mover.19. Comparison HTTP with SMTP, the correct is .A HTTP is a push protocol, and SMTP is a pull protocol.B In the default mode, both of them use persistent connection.C HTTP places all of the message’s objects into one message, and SMTP sends every object one by one.D HTTP requires each message to be in 7-bit ASCII format, and SMTP doesn’t impose this restriction.20. The headers in the MIME message must include except .A FromB Content-typeC Content-transfer-encodingD MIME version11~15CCBAB 16~20 DDBBD21. In the following protocol, which one is statelessA POP3B SMTPC FTPD IMAP22. DNS means .A Data Name SystemB Data National SystemC Domain Name SystemD Domain National System23. There are three classes of DNS server except .A Root DNS serverB Local DNS serverC TLD server D Authoritative DNS server24. DNS provides some services except .A Host aliasingB Mail server aliasingC Load distributionD A single point of failure25. There are three architectures for locating content in P2P file sharing, KaZaA uses .A Centralized Directory (Napster)B Query Flooding(Gnutella)C Exploiting Heterogeneity (p141)D Incentive Priorities26. There are three architectures for locating content in P2P file sharing, Napster uses .A Centralized Directory (p137)B Query FloodingC Exploiting HeterogeneityD Incentive Priorities27. The following architectures in P2P file sharing, which is an overlay networkA Centralized DirectoryB Query Flooding(p139)C Exploiting HeterogeneityD Incentive Priorities28. The time it takes for a small packet to travel from client to server and then back to the client is .A round-travel timeB next-hop timeC round-trip timeD prefix-matching time29. Suppose A ( with a Web-based e-mail account ) sends a message to B ( who accesses his mail server using POP3), which application-layer protocol is not usedA HTTPB SMTPC POP3D IMAP30. In the four following options, which protocol is included in Mail Access ProtocolA SMTPB DHCPC IMAPD FTP31. In FTP commands, is used to send user password to the server.A UserB PassC RetrD Stor32. The function of the additional header field in MIME Content-Type is .A to convert the message body to its origin non-ASCII formB to determine what actions it should take on message bodyC to send an E-mail to the receiving user agentD to indicate what type the message is33. In the four following options, which application is organized as hybrid of C/S and P2P architectureA E-mailB OICQC File transferD Web application34. In the four following options, which is not a centralized DNS design’s problemA a single point of failureB traffic volumeC distant centralized databaseD slow (maintenance)35.In t he following options, from the application developer’s perspective, which is not correctA the network architecture is fixedB the network architecture provides a specific set of services to applicationsC the application architecture is designed by the physical devicesD the application architecture dictates how the application is organized over the various end systems36. There are three predominant architectures used in modern network applications, which one is not includedA the client-server architectureB the P2P architectureC a hybrid of the client-server and P2P architectureD a hybrid of the client-server and browser-server architecture37. In the following options about C/S architecture, which is not correctA In C/S architecture, there is an always-on host, called the server.B In C/S architecture, there is an always-on host, called the client.C The server has a fixed, well-known address, called IP address.D Clients do not directly communicate with each other.38. are often used to create a powerful virtual server in C/S architecture.A PeersB Server farmC server stackD local server39. A process sends messages into, and receives messages from, the network through its .A socketB programC clientD peer40. Which one is not defined by an application-layer protocolA the types of messages exchangedB the syntax of various message typesC the semantics of the fieldsD rules for determining when and how to translate the socket41. HTTP can use two types of connections, which are .A persistent and non-persistent connectionB connection with pipelining and without pipeliningC TCP and UDPD parallel and serial connection42. takes for a small packet to travel from client to server and then back to the client.A RDTB thresholdC RTTD overhead43. The default mode of HTTP uses .A non-persistent connection with pipeliningB non-persistent connection without pipeliningC persistent connection with pipeliningD persistent connection without pipelining44. In HTTP request messages, the request line has three fields, there are .A the method field, the URL field and the HTTP version fieldB the method, the connection and URL fieldC the user-agent, the method and HTTP version fieldD the user-agent, the URL and the HTTP version field45. In the header lines of HTTP request message, if the field of Connection is close, it specifies .A the host on which object residesB what type of the user agentC that the browser wants the server to close the connection after sending the requested objectD which language can the browser receive46. In HTTP response message, if the status code is 404, it means .A request succeeded and the information is returned in the responseB requested object has been permanently movedC the requested HTTP protocol version is not supported by the serverD the requested document does not exist on this server47. is a network entity that satisfies HTTP requests on the behalf of an origin Web server.A proxy serverB local serverC DNS serverD Web server48. In the following four options about web cache, which one is not correctA A web cache is both a server and a client at the same time.B A web cache is purchased and installed by an ISP.C A web cache can raise the response time for a client request.D A web cache can reduce traffic on an institution’s access link to the Internet.49. The request message in the conditional GET must include the header line.A Last-ModifiedB Last-ReferencedC If-Modified-SinceD If –Referenced-Since50. FTP uses two parallel connections to transfer a file, they are .A TCP and UDP connectionB connection with pipelining and without pipeliningC control an data connectionD client-server and browser-server connection51. In FTP commands, which one is used to ask the server to send back a list of all files in the current remote directoryA USERB PASSC LISTD RETR52. In the Internet mail system, allow users to read, reply to, forward, save and compose message.A User agentsB mail serversC SMTPD TCP53. The two key MIME headers for supporting multimedia are .A Content-Type and MIME-VersionB Content-Type and Content-Transfer-EncodingC Content-Transfer-Encoding and MIME-VersionD MIME-Version and MIME-Type54. For Internet mail, the mail access protocol is used to .A transfer mail from the recipient’s mail server to the recipient’s user agentB transfer mail from the sender’s mail server to the recipient’s mail serverC translate the mail from the sender’s mail serverD translate the mail into the recipient’s mail server55. POP3 progresses through three phases, which they are .A authorization, translation and transactionB authorization, translation and updateC authorization, transaction and updateD translation, transaction and update56. In the following four services, which one can not provide by DNSA Host aliasingB Mail server aliasingC translate hostname to IP addressesD translate MAC addresses to IP addresses57. There are three classes of DNS servers, there are .A root DNS server, top-level domain DNS server and local DNS serverB root DNS server, top-level domain DNS server and authoritative DNS serverC root DNS server, local DNS server and authoritative DNS serverD root DNS server, local DNS server and top-level domain DNS server58. In the following four options about POP3, which one is not correctA The user agent employed only three commands: List, Retr and QuitB The server does not carry state information across POP3 sessionsC The port number is 110D The POP3 protocol does not provide any means for a user to create remote folders and assign messages to folders.59. A resource record in DNS distributed database is a four-tuple, which field can be ignored(p132) A Name B Value C Type D TTL 60. In the following four options about DNSresource record, which one is correctA The meaning of Name and Value depend on Type.B The meaning of Value and Type depend on Name.C If Type=A, then Name is a domain and Value is the IP address for the hostname.D If Type=MX, then Name is domain and Value is the IP address for the hostname.61. In the following four options about DNS messages, which one is not correctA There are only two kinds of DNS message.(p133)B Both query and reply message have the same format.C The header section in DNS message has 12 bytes.D The authority section contains the resource records for the same that was originally queri ed.62. In DNS message, contains information about the query that is being made.(p133)A authority sectionB question sectionC answer sectionD additional section63. There are three techniques are employed in most any P2P file-sharing systems, which one is not include (p144)A Request queuingB incentive prioritiesC parallel downloadingD Response queuing64. In the following four options about P2P file-sharing, which one is not correctA P2P file-sharing is highly scalable.B P2P file-sharing relies on P2P architecture.C The means for locating content in different P2P file-sharing are different.D P2P file-sharing systems not only share MP3s,but also videos, software, documents and images.65. In MIME header lines, specifies the name of the SMTP server that sent the message (f rom),the name of the SMTP server that received the message (by), and the time an which the rec eiving server received the message.A ReceivedB FromC ToD MIME-Version66. If the header line Connection is close, it means that the client wants .A persistent connection with pipeliningB persistent connection without pipeliningC nonpersistent connectionD not connection67. In HTTP request message, the entity body is empty with the method, but is used with the method.A GET, POSTB POST,GETC GET, HEAD D POST, HEAD68. In HTTP response message, if the Date: header ;one indicates the time Fri. 08 Aug. 2008 12:00:00 GMT, the Last-Modified: header line can not be .A Fri. 08 Aug. 2008 11:00:00 GMTB Fri. 08 Aug. 2008 11:30:00 GMTC Fri. 08 Aug. 2008 12:00:00 GMTD Fri. 08 Aug. 2008 12:30:00 GMT69. In the following four options, which one is not the part of cookie technologyA Cookie header lines in the HTTP response message and request message.B One cookie header file kept on the user’s end system and managed by the user’s browser.C A network entity that satisfies HTTP requests on the behalf of an origin Web server.D A back-end database at the Web site70. On-top of stateless HTTP, can be used to create a user session layer.A proxy serverB Web cacheC cookieD socket71. Processes communicate with each other by reading from and writing to .A programsB threadsC socketsD channels72. In the following four options about network architecture, which one is not correctA The network architecture is fixed.B The network architecture provides a specific set of services to application.C The network architecture is designed by application developer.D The network architecture dictates how the application is organized over special server.73. In Client-Server architecture, the clients visit the server’s through .A client’s socketB client’s IP addressC server’s socketD server’s IP address74. can be thought of as a program that is running within end system.A processB threadC socketD context75. API means .A Application Program InterfaceB Application Process InterfaceC Appellation Program InterfaceD Appellation Process Interface76. One host can be running many network applications, so the system assigns them differentto distinguish each other.A IP addressB port numberC hostnameD section77. In the following four applications, which one is both bandwith-sensitive and require tight timing constraintsA real-time audioB file transferC E-mailD Web documents78. The port number of the Web server is .A 25B 20C 80D 808079. The port number of the mail server is .A 25B 20C 80D 808080. Look the URL the object’s path name is .A B /rjxy/ D81. Each URL has components, they are .A transport protocol and object’s path nameB host name and object’s path nameC transport protocol and host nameD client name and server name1. Consider an HTTP client will request a WEB page from a WEB server. Suppose the URL of the page is /somedir/. The client does not want to use persistent connections and want to receive French version of the object. The user agent is Windows NT . Give the request message according to the given format.2. Telnet into a Web server and send a multiline request message. Include in the request message the If-modified-since: header line to force a response message with the 304 Not Modified status code.Solution:Request line:Header lines:3. Suppose within you Web browser you click on a link to obtain a Web page. The IP address for the associated URL is not cached in your local host, so a DNS look-up is necessary to obtain the IP address. Suppose that n DNS servers are visited before your host receives the IP address from DNS; the successive visits incur an RTT of RTT1,…,RTT n. Further suppose that the Web page associated with the link contains exactly one object, consisting of a small HTML text. Let RTT0 denote the RTT between the local host and the server containing the object. Assuming zero transmission time of the object, how much time elapses from when the client clicks on the link until the client receives the object5. Suppose that you send an e-mail message whose only data is a microsoft excell attachment. What might the header lines (including MIME lines) look like。

第一章(1.2 1.3节)5.Calculate the total time required to transfer a 1,000-KB file in the following cases, assuming an RTT of 100 ms, a packet size of 1-KB data, and an initial 2 ×RTT of “handshaking” before data is sent.(a) The bandwidth is 1.5 Mbps, and data packets can be sent continuously.(b) The bandwidth is 1.5 Mbps, but after we finish sending each data packetwe must wait one RTT before sending the next.(c) The bandwidth is “infinite,”meaning that we take transmit time to bezero, and up to 20 packets can be sent per RTT.(d) The bandwidth is infinite, and during the first RTT we can send onepacket (21−1), during the second RTT we can send two packets (22−1),during the third we can send four (23−1), and so on. (A justification forsuch an exponential increase will be given in Chapter 6.)7. Consider a point-to-point link 2 km in length. At what bandwidth would propagation delay (at a speed of 2 × 108m/sec) equal transmit delay for 100-byte packets? What about 512-byte packets?13.How “wide” is a bit on a 1-Gbps link? How long is a bit in copper wire, where the speed of propagation is 2.3 × 108 m/s?15.Suppose a 100-Mbps point-to-point link is being set up between Earth and a new lunar colony. The distance from the moon to Earth is approximately 385,000 km, and data travels over the link at the speed of light—3 × 108 m/s.(a) Calculate the minimum RTT for the link.(b) Using the RTT as the delay, calculate the delay × bandwidth product forthe link.(c) What is the significance of he delay × bandwidth product computedin (b)?(d) A camera on the lunar base takes pictures of Earth and saves them in digitalformat to disk. Suppose Mission Control on Earth wishes to download themost current image, which is 25 MB. What is the minimum amount of time that will elapse between when the request for the data goes out andthe transfer is finished?18. Calculate the latency (from first bit sent to last bit received) for the following:(a) A 10-Mbps Ethernet with a single store-and-forward switch in the path,and a packet size of 5,000 bits. Assume that each link introduces a propaga-tion delay of 10 µs, and that the switch begins retransmitting immediatelyafter it has finished receiving the packet.(b) Same as (a) but with three switches.(c) Same as (a) but assume the switch implements “cut-through”switching: itis able to begin retransmitting the packet after the first 200 bits have beenreceived.第二章(除2.7 2.9 节)1.Show the NRZ, Manchester, and NRZI encodings for the bit pattern shown in Figure2.46. Assume that the NRZI signal starts out low.23.Consider an ARQ algorithm running over a 20-km point-to-point fiber link.(a) Compute the propagation delay for this link, assuming that the speed oflight is 2 × 108 m/s in the fiber.(b) Suggest a suitable timeout value for the ARQ algorithm to use.(c) Why might it still be possible for the ARQ algorithm to time out andretransmit a frame, given this timeout value?26.The text suggests that the sliding window protocol can be used to implement flow control. We can imagine doing this by having the receiver delay ACKs, that is, not send the ACK until there is free buffer space to hold the next frame. In doing so, each ACK would simultaneously acknowledge the receipt of the last frame and tell the source that there is now free buffer space available to hold the next frame. Explain why implementing flow control in this way is not a good idea.44.Let A and B be two stations attempting to transmit on an Ethernet. Each has steady queue of frames ready to send; A’s frames will be numbered A 1, A2 , and so on, and B’s similarly. Let T = 51.2 µs be the exponential backoff base unit. SupposeA andB simultaneously attempt to send frame 1, collide, and happen to choose backoff times of 0 × T and 1 × T, respectively, meaning A wins the race and transmits A 1 while B waits. At the end of this transmission, B will attempt to retransmit B1 while A will attempt to transmit A2 . These first attempts will collide, but now A backs off for either 0 × T or 1 × T, while B backs off for time equal to one of 0 × T, . . . , 3 × T.(a) Give the probability that A wins this second backoff race immediately after this firstcollision , that is, A’s first choice of backoff time k × 51.2 is less than B’s.(b) Suppose A wins this second backoff race. A transmits A 3 , and when it isfinished, A and B collide again as A tries to transmit A4 and B tries once more to transmit B1. Give the probability that A wins this third backoff race immediately after the first collision.(c) Give a reasonable lower bound for the probability that A wins all the re- maining backoff races.(d) What then happens to the frame B1?This scenario is known as the Ethernet capture effect.48. Repeat the previous exercise, now with the assumption that Ethernet is p -persistent with p = 0.33 (that is, a waiting station transmits immediately with probability p when the line goes idle, and otherwise defers one 51.2-µs slot time and repeats the process). Your timeline should meet criterion (1) of the previous problem, but in lieu of criterion (2), you should show at least one collision and at least one run of four deferrals on an idle line. Again, note that many solutions are possible.第三章(3.1 3.2节)ing the example network given in Figure 3.30, give the virtual circuit tables for all the switches after each of the following connections is established. Assume that the sequence of connections is cumulative, that is, the first connection is still up when the second connection is established, and so on. Also assume that the VCI assignment always picks the lowest unused VCI on each link, starting with 0.(a) Host A connects to host B.(b) Host C connects to host G.(c) Host E connects to host I.(d) Host D connects to host B.(e) Host F connects to host J.(f) Host H connects to host A.3.For the network given in Figure 3.31, give the datagram forwarding table for each node. The links are labeled with relative costs; your tables should forward each packet via the lowest-cost path to its destination.5. Consider the virtual circuit switches in Figure 3.33. Table 3.6 lists, for each switch, what port, VCI (or VCI, interface) pairs are connected to other. Connections are bidirectional. List all endpoint-to-endpoint connections.13. Given the extended LAN shown in Figure 3.34, indicate which ports are not selected by the spanning tree algorithm.15. Consider the arrangement of learning bridges shown in Figure 3.35. Assuming all are initially empty, give the forwarding tables for each of the bridges B1–B4 after the following transmissions:■ A sends to C.■ C sends to A.■ D sends to C.Identify ports with the unique neighbor reached directly from that port, thatis, the ports for B1 are to be labeled “A” and “B2.”17.Consider hosts X, Y, Z, W and learning bridges B1, B2, B3, with initially empty forwarding tables, as in Figure 3.36.(a) Suppose X sends to Z. Which bridges learn where X is? Does Y’s networkinterface see this packet?(b) Suppose Z now sends to X. Which bridges learn where Z is? Does Y’s network interface see this packet?(c) Suppose Y now sends to X. Which bridges learn where Y is? Does Z’s net-work interface see this packet?(d) Finally, suppose Z sends to Y. Which bridges learn where Z is? Does W’snetwork interface see this packet?第四章(4.1 4.2 4.3.1 4.3.5 4.5 节)4.Suppose a TCP message that contains 2,048 bytes of data and 20 bytes of TCP header is passed to IP for delivery across two networks of the Internet (i.e., from the source host to a router to the destination host). The first network uses 14-byte headers and has an MTU of 1,024 bytes; the second uses 8-byte headers with an MTU of 512 bytes. Each network’s MTU gives the size of the largest IP datagram that can be carried in a link layer frame. Give the sizes and offsets of the sequence of fragments delivered to the network layer at the destination host. Assume all IP headers are 20 bytes.21.Suppose a router has built up the routing table shown in Table 4.14. The router can deliver packets directly over interfaces 0 and 1, or it can forward packets to routers R2, R3, or R4. Describe what the router does with a packet addressed to each of the following destinations:(a) 128.96.39.10.(b) 128.96.40.12.(c) 128.96.40.151.(d) 192.4.153.17.(e) 192.4.153.90.45.Table 4.16 is a routing table using CIDR. Address bytes are in hexadecimal. The notation “/12” in C4.50.0.0/12 denotes a netmask with 12 leading 1 bits, that is, FF.F0.0.0. Note that the last three entries cover every address and thus serve in lieu of a default route. State to what next hop the following will be delivered.(a) C4.5E.13.87.(b) C4.5E.22.09.(c) C3.41.80.02.(d) 5E.43.91.12.(e) C4.6D.31.2E.(f) C4.6B.31.2E.第五章(5.1 5.2节)10. You are hired to design a reliable byte-stream protocol that uses a sliding window (like TCP). This protocol will run over a 1-Gbps network. The RTT of the network is 140 ms, and the maximum segment lifetime is 60 seconds. How many bits would you include in the AdvertisedWindow and SequenceNum fields of your protocol header?第六章(6.5节)第九章(9.1节)。

计算机网络课后作业答案1. OSI参考模型计算机网络通常使用开放系统互联参考模型(Open System Interconnection,简称OSI模型)作为标准。
它将通信过程分为七个层次,每个层次都负责特定的功能。
下面是对每个层次的解释:1) 物理层(Physical Layer):主要负责传输比特流,将数字数据转化为电信号传输。
常见的物理层协议有以太网(Ethernet)和无线传输技术。
2) 数据链路层(Data Link Layer):负责将原始的比特流转化为数据帧,并通过物理层传输。
数据链路层还负责错误检测和纠正。
常见的数据链路层协议有以太网协议、点对点协议(PPP)和局域网协议(LAN)。
3) 网络层(Network Layer):负责将数据包从源主机传输到目标主机。
该层主要处理路由选择和分组转发。
常见的网络层协议有互联网协议(IP)和网际控制报文协议(ICMP)。
4) 传输层(Transport Layer):负责在通信端点之间建立可靠的数据传输连接。
传输层协议一般分为面向连接的传输协议(如传输控制协议TCP)和无连接传输协议(如用户数据报协议UDP)。
5) 会话层(Session Layer):负责建立、管理和终止会话连接。
这些会话连接可以是单向的或双向的。
6) 表示层(Presentation Layer):负责数据格式的转换和数据加密解密。
该层的功能确保应用层可读格式的交换数据。
7) 应用层(Application Layer):最顶层的应用层负责处理特定的网络应用,例如电子邮件、文件传输和远程登录。
常见的应用层协议有超文本传输协议(HTTP)、文件传输协议(FTP)和域名系统(DNS)。
2. TCP/IP协议族TCP/IP协议族是互联网通信的基础,它由许多协议组成,其中最重要的是传输控制协议(TCP)和互联网协议(IP)。
1) 互联网协议(IP)是TCP/IP协议族的核心协议,负责为数据包提供路由功能,将数据包从源主机传输到目标主机。

第一章(1.2 1.3节)5.Calculate the total time required to transfer a 1,000-KB file in the following cases, assuming an RTT of 100 ms, a packet size of 1-KB data, and an initial 2 ×RTT of “handshaking”before data is sent.(a) The bandwidth is 1.5 Mbps, and data packets can be sent continuously.(b) The bandwidth is 1.5 Mbps, but after we finish sending each data packetwe must wait one RTT before sending the next.(c) The bandwidth is “infinite,”meaning that we take transmit time to bezero, and up to 20 packets can be sent per RTT.(d) The bandwidth is infinite, and during the first RTT we can send onepacket (21−1), during the second RTT we can send two packets (22−1),during the third we can send four (23−1), and so on. (A justification forsuch an exponential increase will be given in Chapter 6.)7. Consider a point-to-point link 2 km in length. At what bandwidth would propagation delay (at a speed of 2 ×108m/sec) equal transmit delay for 100-byte packets? What about 512-byte packets?13.How “wide”is a bit on a 1-Gbps link? How long is a bit in copper wire, where the speed of propagation is 2.3 ×108 m/s?15.Suppose a 100-Mbps point-to-point link is being set up between Earth and a new lunar colony. The distance from the moon to Earth is approximately 385,000 km, and data travels over the link at the speed of light—3 ×108 m/s.(a) Calculate the minimum RTT for the link.(b) Using the RTT as the delay, calculate the delay ×bandwidth product forthe link.(c) What is the significance of he delay ×bandwidth product computedin (b)?(d) A camera on the lunar base takes pictures of Earth and saves them in digitalformat to disk. Suppose Mission Control on Earth wishes to download themost current image, which is 25 MB. What is the minimum amount oftime that will elapse between when the request for the data goes out andthe transfer is finished?18. Calculate the latency (from first bit sent to last bit received) for the following:(a) A 10-Mbps Ethernet with a single store-and-forward switch in the path,and a packet size of 5,000 bits. Assume that each link introduces a propaga-tion delay of 10 µs, and that the switch begins retransmitting immediatelyafter it has finished receiving the packet.(b) Same as (a) but with three switches.(c) Same as (a) but assume the switch implements “cut-through”switching: itis able to begin retransmitting the packet after the first 200 bits have beenreceived.第二章(除2.7 2.9 节)1.Show the NRZ, Manchester, and NRZI encodings for the bit pattern shown in Figure2.46. Assume that the NRZI signal starts out low.23.Consider an ARQ algorithm running over a 20-km point-to-point fiber link.(a) Compute the propagation delay for this link, assuming that the speed oflight is 2 ×108 m/s in the fiber.(b) Suggest a suitable timeout value for the ARQ algorithm to use.(c) Why might it still be possible for the ARQ algorithm to time out andretransmit a frame, given this timeout value?26.The text suggests that the sliding window protocol can be used to implement flow control. We can imagine doing this by having the receiver delay ACKs, that is, not send the ACK until there is free buffer space to hold the next frame. In doing so, each ACK would simultaneously acknowledge the receipt of the last frame and tell the source that there is now free buffer space available to hold the next frame. Explain why implementing flow control in this way is not a good idea.44.Let A and B be two stations attempting to transmit on an Ethernet. Each has steady queue of frames ready to send; A’s frames will be numbered A 1, A2 , and so on, and B’s similarly. Let T = 51.2 µs be the exponential backoff base unit. Suppose A and B simultaneously attempt to send frame 1, collide, and happen to choose backoff times of 0 ×T and 1 ×T, respectively, meaning A wins the race and transmits A 1 while B waits. At the end of this transmission, B will attempt to retransmit B1 while A will attempt to transmit A2 . These first attempts will collide, but now A backs off for either 0 ×T or 1 ×T, while B backs off for time equal to one of 0 ×T, . . . , 3 ×T.(a) Give the probability that A wins this second backoff race immediately after this firstcollision , that is, A’s first choice of backoff time k ×51.2 is less than B’s.(b) Suppose A wins this second backoff race. A transmits A 3 , and when it isfinished, A and B collide again as A tries to transmit A4 and B tries oncemore to transmit B1. Give the probability that A wins this third backoffrace immediately after the first collision.(c) Give a reasonable lower bound for the probability that A wins all the re-maining backoff races.(d) What then happens to the frame B1?This scenario is known as the Ethernet capture effect.48. Repeat the previous exercise, now with the assumption that Ethernet is p -persistent with p = 0.33 (that is, a waiting station transmits immediately with probability p when the line goes idle, and otherwise defers one 51.2-µs slot time and repeats the process). Your timeline should meet criterion (1) of the previous problem, but in lieu of criterion (2), you should show at least one collision and at least one run of four deferrals on an idle line. Again, note that many solutions are possible.第三章(3.1 3.2节)ing the example network given in Figure 3.30, give the virtual circuit tables for all the switches after each of the following connections is established. Assume that the sequence of connections is cumulative, that is, the first connection is still up when the second connection is established, and so on. Also assume that the VCI assignment always picks the lowest unused VCI on each link, starting with 0.(a) Host A connects to host B.(b) Host C connects to host G.(c) Host E connects to host I.(d) Host D connects to host B.(e) Host F connects to host J.(f) Host H connects to host A.3.For the network given in Figure 3.31, give the datagram forwarding table for each node. The links are labeled with relative costs; your tables should forward each packet via the lowest-cost path to its destination.5. Consider the virtual circuit switches in Figure 3.33. Table 3.6 lists, for each switch, what port, VCI (or VCI, interface) pairs are connected to other. Connections are bidirectional. List all endpoint-to-endpoint connections.13. Given the extended LAN shown in Figure 3.34, indicate which ports are not selected bythe spanning tree algorithm.15. Consider the arrangement of learning bridges shown in Figure 3.35. Assuming all are initially empty, give the forwarding tables for each of the bridges B1–B4 after the following transmissions:■ A sends to C.■ C sends to A.■ D sends to C.Identify ports with the unique neighbor reached directly from that port, thatis, the ports for B1 are to be labeled “A”and “B2.”17.Consider hosts X, Y, Z, W and learning bridges B1, B2, B3, with initially empty forwarding tables, as in Figure 3.36.(a) Suppose X sends to Z. Which bridges learn where X is? Does Y’s networkinterface see this packet?(b) Suppose Z now sends to X. Which bridges learn where Zis? Does Y’s network interface see this packet?(c) Suppose Y now sends to X. Which bridges learn where Y is? Does Z’s net-work interface see this packet?(d) Finally, suppose Z sends to Y. Which bridges learn where Z is? Does W’snetwork interface see this packet?第四章(4.1 4.2 4.3.1 4.3.5 4.5 节)4.Suppose a TCP message that contains 2,048 bytes of data and 20 bytes of TCP header is passed to IP for delivery across two networks of the Internet (i.e., from the source host to a router to the destination host). The first network uses 14-byte headers and has an MTU of 1,024 bytes; the second uses 8-byte headers with an MTU of 512 bytes. Each network’s MTU gives the size of the largest IP datagram that can be carried in a link layer frame. Give the sizes and offsets of the sequence of fragments delivered to the network layer at the destination host. Assume all IP headers are 20 bytes.21.Suppose a router has built up the routing table shown in Table 4.14. The router can deliver packets directly over interfaces 0 and 1, or it can forward packets to routers R2, R3, or R4. Describe what the router does with a packet addressed to each of the following destinations:(a) 128.96.39.10.(b) 128.96.40.12.(c) 128.96.40.151.(d) 192.4.153.17.(e) 192.4.153.90.45.Table 4.16 is a routing table using CIDR. Address bytes are in hexadecimal. The notation “/12”in C4.50.0.0/12 denotes a netmask with 12 leading 1 bits, that is, FF.F0.0.0. Note that the last three entries cover every address and thus serve in lieu of a default route. State to what next hop the following will be delivered.(a) C4.5E.13.87.(b) C4.5E.22.09.(c) C3.41.80.02.(d) 5E.43.91.12.(e) C4.6D.31.2E.(f) C4.6B.31.2E.第五章(5.1 5.2节)10. You are hired to design a reliable byte-stream protocol that uses a sliding window (like TCP). This protocol will run over a 1-Gbps network. The RTT of the network is 140 ms, and the maximum segment lifetime is 60 seconds. How many bits would you include in the AdvertisedWindow and SequenceNum fields of your protocol header?第六章(6.5节)第九章(9.1节)。
Chapter11-11.What are two reasons for using layered protocols?(请说出使用分层协议的两个理由)答:通过协议分层可以把设计问题划分成较小的易于处理的片段。
分层意味着某一层的协议的改变不会影响高层或低层的协议。
1-13. What is the principal difference between connectionless communication and connection-oriented communication?(在无连接通信和面向连接的通信两者之间,最主要的区别是什么?)答:主要的区别有两条。
其一:面向连接通信分为三个阶段,第一是建立连接,在此阶段,发出一个建立连接的请求。
只有在连接成功建立之后,才能开始数据传输,这是第二阶段。
接着,当数据传输完毕,必须释放连接。
而无连接通信没有这么多阶段,它直接进行数据传输。
其二:面向连接的通信具有数据的保序性,而无连接的通信不能保证接收数据的顺序与发送数据的顺序一致。
1-20. A system has an n-layer protocol hierarchy. Applications generate messages of length M bytes. At each of the layers, an h-byte header is added. What fraction of the network bandwidth is filled with headers?(一个系统有n层协议的层次结构。
应用程序产生的消息的长度为M字节。
在每一层上需要加上一个h字节的头。
请问,这些头需要占用多少比例的网络带宽)答:hn/(hn+m)*100%1-28. An image is 1024 x 768 pixels with 3 bytes/pixel. Assume the image is uncompressed. How long does it take to transmit it over a 56-kbps modem channel? Over a 1-Mbps cable modem? Over a 10-Mbps Ethernet? Over 100-Mbps Ethernet?(一幅图像的分辨率为1024 x 768像素,每个像素用3字节来表示。
假设该图像没有被压缩。
请问,通过56kbps的调制解调器信道来传输这幅图像需要多长时间?通过1Mbps的电缆调制解调器呢?通过10Mbps的以太网呢?通过100Mbps的以太网呢?)答:The image is 1024*768*3 bytes or 2359296 bytes.This is 18874368 bit. At 56,000 bits/sec, it takes about 337.042 sec. At 1,000,000 bits/sec, it takes about 18.874 sec. At 10,000,000 bits/sec, it takes about 1.887 sec. At 100,000,000 bits/sec, it takes about 0.189 sec.Chapter22-2. A noiseless 4-kHz channel is sampled every 1 msec. What is the maximum data rate?(一条无噪声4kHz信道按照每1ms一次进行采样,请问最大数据传输率是多少?)答:无噪声信道最大数据传输率公式:最大数据传输率=2Hlog2V b/s。
因此最大数据传输率决定于每次采样所产生的比特数,如果每次采样产生16bits,那么数据传输率可达128kbps;如果每次采样产生1024bits,那么可达8.2Mbps。
注意这是对无噪声信道而言的,实际信道总是有噪声的,其最大数据传输率由香农定律给出。
2-4. If a binary signal is sent over a 3-kHz channel whose signal-to-noise ratio is 20 dB, what is the maximum achievable data rate?(如果在一条3kHz的信道上发送一个二进制信号,该信道的信噪比为20dB,则最大可达到的数据传输率为多少?)答:信噪比为20 dB 即S/N =100由于log2101≈6.658,由香农定理,该信道的信道容量为3log2(1+100)=19.98kbps。
又根据乃奎斯特定理,发送二进制信号的3kHz 信道的最大数据传输速率为2*3*log22=6kbps。
所以可以取得的最大数据传输速率为6kbps。
2-5. What signal-to-noise ratio is needed to put a T1 carrier on a 50-kHz line?(在50kHz的线路上使用1T线路需要多大的信噪比?)答:为发送T1 信号,我们需要所以,在50kHz 线路上使用T1 载波需要93dB 的信噪比。
2-34. A signal is transmitted digitally over a 4-kHz noiseless channel with one sample every 125 µsec. How many bits per second are actually sent for each of these encoding methods?(a) CCITT 2.048 Mbps standard.(b) DPCM with a 4-bit relative signal value.(c) Delta modulation.(一个信号在4kHz的无噪声信道上以数字方式进行传输,没125us采样一次。
请问,按照以下的编码方法,每秒钟实际发送多少位?(a)CCITT 2.048Mbps标准。
(b)有4位相对信号值的DPCM。
(c)增量调制。
)答:a.CCITT 2.048Mbps 标准用32 个8 位数据样本组成一个125的基本帧,30 个信道用于传信息,2 个信道用于传控制信号。
在每一个4kHz 信道上发送的数据率就是8*8000=64kbps。
b.差分脉码调制(DPCM)是一种压缩传输信息量的方法,它发送的不是每一次抽样的二进制编码值,而是两次抽样的差值的二进制编码。
现在相对差值是4 位,所以对应每个4kHz 信道实际发送的比特速率为4*8000=32bps。
c.增量调制的基本思想是:当抽样时间间隔s t 很短时,模拟数据在两次抽样之间的变化很小,可以选择一个合适的量化值作为阶距。
把两次抽样的差别近似为不是增加一个就是减少一个。
这样只需用1bit 二进制信息就可以表示一次抽样结果,而不会引入很大误差。
因此,此时对应每个4kHz 信道实际发送的数据速率为1*8000=8kHz。
2-43. Suppose that x bits of user data are to be transmitted over a k-hop path in a packet-switched network as a series of packets, each containingp data bits and h header bits,with x >> p+h.The bit rate of the lines is b bps and the propagation delay is negligible.What value of p minimizes the total delay?(假定x位用户数据将以一系列分组形式,在一个分组交换网络中沿着一条共有k跳的路径向前传播,每个分组包含p位数据和h位的头,这里x>>p+h。
线路的传输率为b bps,传播延迟忽略不计。
请问,什么样的p值使总延迟最小?)答:所需要的分组总数是x /p,因此总的数据加上头信息交通量为(p+h)*x/p 位。
源端发送这些位需要时间为(p+h)*x/pb中间的路由器重传最后一个分组所花的总时间为(k-1)*(p+h)/ b因此我们得到的总的延迟为对该函数求p 的导数,得到令得到因为p>0,所以故时能使总的延迟最小。
2-53. A CDMA receiver gets the following chips: (-1 +1 -3 +1 -1 -3 +1 +1). Assuming the chip sequences defined in Fig. 2-45(b), which stations transmitted, and which bits did each one send?(一个CDMA接收器得到了下面的时间片:(-1 +1 -3 +1 -1 -3 +1 +1)。
假设时间片序列如图2.45(b)中所定义,请问哪些移动站传输了数据?每个站发送了什么位?)答:Just compute the four normalized inner products:(1+1 3+1 1 3+1+1)d(1 1 1+1+1 1+1+1)/8=1(1+1 3+1 1 3+1+1)d(1 1+1 1+1+1+1 1)/8=1(1+1 3+1 1 3+1+1)d(1+1 1+1+1+1 1 1)/8=0(1+1 3+1 1 3+1+1)d(1+1 1 1 1 1+1 1)/8=1The result is that A and D sent 1 bits, B sent a 0 bit, and C was silent.Chapter33-3.The following data fragment occurs in the middle of a data stream for which the byte-stuffing algorithm described in the text is used: A B ESC C ESC FLAG FLAG D. What is the output after stuffing?(数据片断(A B ESC C ESC FLAG FLAG D)出现在一个数据流的中间,而成帧方式采用的是本章介绍的字节填充算法,请问经过填充之后的输出时什么?)答:After stuffing, we get A B ESC ESC C ESC ESC ESC FLAG ESC FLAG D.3-15. A bit stream 10011101 is transmitted using the standard CRC method described in the text. The generator polynomial is x3 + 1. Show the actual bit string transmitted. Suppose the third bit from the left is inverted during transmission. Show that this error is detected at the receiver's end.(利用本章中介绍的标准多项式CRC方法来传输位流1001101。