7506E安全配置指导-ARP攻击防御配置
- 格式:pdf
- 大小:253.25 KB
- 文档页数:14

如何设置ARP防护ARP是IP与MAC地址的解析协议,对网络通信至关重要。
但是,由于ARP没有保护机制,所以伪造的ARP数据包会欺骗通信终端或设备,导致出现通信异常。
常见的ARP欺骗软件有“网络执法官”、“P2P终结者”、“QQ第六感”等,这些软件中,有些是人为手工操作来破坏网络,有些是作为病毒或者木马出现,使用者可能根本不知道它的存在,所以更加扩大了ARP攻击的危害。
下面店铺就教大家如何设置ARP防护功能。
无线企业路由器的ARP防护功能的设置方法:在设置ARP绑定之前,请给需要绑定的电脑手动指定IP地址。
同时,建议查看对应电脑的MAC地址,制作IP、MAC、电脑的表格,便于后续维护,如下:注意:以上表格仅供参考,具体信息请根据实际需要记录。
登录路由器的管理界面,点击安全管理 >> ARP防护,在ARP防护界面添加绑定条目。
有两种添加方法:手动逐条添加和扫描添加,具体方法请根据实际需要选择,方法如下:手动添加方法:手动添加操作复杂,但是安全性高。
在网络中已经存在ARP欺骗或者不确定网络中是否存在ARP欺骗的情况下,建议使用手动添加的方式。
手工进行添加,点击增加单个条目,填写对应的IP和MAC地址,填写备注信息。
出接口:指绑定电脑所在网络连接的路由器的接口。
扫描添加方法:简单快捷,但是要确定网络中没有ARP欺骗,否则绑定错误的IP/MAC条目可能导致内网部分主机无法上网。
点击ARP扫描,点击开始扫描,此时等待一会,路由器会自动查找当前内网的主机,并显示主机的IP和MAC地址信息,如下图所示:点击全选,再点击导入,所有的绑定条目就设置完成了。
注意:ARP扫描的功能也可以扫描WAN口的网段,可以通过扫描绑定WAN口网关地址防止前端ARP欺骗(宽带拨号无需绑定)。
局域网中电脑的IP与MAC全部绑定完成后,在功能设置中,勾选启用ARP防欺骗功能,点击设置。
注意:如果勾选仅允许IP MAC绑定的数据包通过路由器,则不在绑定列表或与绑定列表冲突的电脑不能上网及管理路由器。

arp攻击与防护措施及解决方案为有效防范 ARP 攻击,确保网络安全,特制定ARP 攻击与防护措施及解决方案如下:1.安装杀毒软件安装杀毒软件是防范 ARP 攻击的第一步。
杀毒软件可以帮助检测和清除 ARP 病毒,保护网络免受 ARP 攻击。
在选择杀毒软件时,应确保其具有实时监控和防御 ARP 攻击的功能。
2.设置静态 ARP设置静态 ARP 是一种有效的防护措施。
通过在计算机上手动设置静态 ARP 表,可以避免网络中的 ARP 欺骗。
在设置静态ARP 时,需要将计算机的 MAC 地址与 IP 地址绑定,以便在接收到 ARP 请求时进行正确响应。
3.绑定 MAC 地址绑定 MAC 地址可以防止 ARP 攻击。
在路由器或交换机上,将特定设备的 MAC 地址与 IP 地址绑定,可以确保只有该设备能够通过 ARP 协议解析 IP 地址。
这种绑定可以提高网络安全性,避免未经授权的设备接入网络。
4.限制 IP 访问限制 IP 访问可以防止 ARP 攻击。
通过设置访问控制列表( ACL ),可以限制特定 IP 地址的网络访问权限。
这样可以避免网络中的恶意节点发送 ARP 请求,确保网络通信的安全性。
5.使用安全协议使用安全协议可以进一步提高网络安全性。
例如,使用 IEEE 802.1X协议可以验证接入网络的设备身份,确保只有授权用户可以访问网络。
此外,还可以使用其他安全协议,如 SSH 或 VPN 等,以加密网络通信,防止 A RP 攻击。
6.配置网络设备配置网络设备是防范 ARP 攻击的重要环节。
在路由器、交换机等网络设备上,可以设置 ARP 防护功能,例如 ARP 欺骗防御、 ARP 安全映射等。
这些功能可以帮助识别并防御 A RP 攻击,保护网络免受 ARP 病毒的侵害。
7.定期监控网络定期监控网络是确保网络安全的有效手段。
通过监控网络流量、异常 IP 连接等指标,可以及时发现 ARP 攻击的迹象。
一旦发现 ARP 攻击,应立即采取措施清除病毒,修复漏洞,并重新配置网络设备以确保安全性。

ARP攻击的原理及防御方法!网络管理员必备技能ARPARP(Address Resolution Protocol,地址解析协议)是一个位于TCP/IP协议栈中的网络层,负责将某个IP地址解析成对应的MAC 地址。
ARP攻击特点•ARP协议的基本功能就是通过目标设备的IP地址,查询目标设备的MAC地址,以保证通信的进行•ARP攻击的局限性•ARP攻击仅能在以太网(局域网如:机房、内网、公司网络等)进行•无法对外网(互联网、非本区域内的局域网)进行攻击攻击原理ARP攻击就是通过伪造IP地址和MAC地址实现ARP欺骗,能够在网络中产生大量的ARP通信量使网络阻塞,攻击者只要持续不断的发出伪造的ARP响应包就能更改目标主机ARP缓存中的IP-MAC条目,造成网络中断或中间人攻击。
ARP攻击主要是存在于局域网网络中,局域网中若有一台计算机感染ARP木马,则感染该ARP木马的系统将会试图通过“ARP欺骗”手段截获所在网络内其它计算机的通信信息,并因此造成网内其它计算机的通信故障。
攻击者向电脑A发送一个伪造的ARP响应,告诉电脑A:电脑B 的IP地址192.168.0.2对应的MAC地址是00-aa-00-62-c6-03,电脑A信以为真,将这个对应关系写入自己的ARP缓存表中,以后发送数据时,将本应该发往电脑B的数据发送给了攻击者。
同样的,攻击者向电脑B也发送一个伪造的ARP响应,告诉电脑B:电脑A的IP地址192.168.0.1对应的MAC地址是00-aa-00-62-c6-03,电脑B也会将数据发送给攻击者。
至此攻击者就控制了电脑A和电脑B之间的流量,他可以选择被动地监测流量,获取密码和其他涉密信息,也可以伪造数据,改变电脑A和电脑B之间的通信内容。
为了解决ARP攻击问题,可以在网络中的交换机上配置802.1x协议。
IEEE 802.1x是基于端口的访问控制协议,它对连接到交换机的用户进行认证和授权。

ARP攻击防范与解决方案一、背景介绍ARP(Address Resolution Protocol)是用于在局域网中将IP地址转换为物理MAC地址的协议。
然而,ARP协议的设计缺陷使得攻击者可以通过ARP欺骗攻击(ARP Spoofing)来进行网络攻击。
ARP攻击会导致网络中的主机无法正常通信,甚至造成敏感信息泄露和网络瘫痪。
因此,为了保护网络安全,我们需要采取一系列的防范措施和解决方案来应对ARP攻击。
二、防范措施1. 使用静态ARP表静态ARP表是一种手动配置的ARP表,将IP地址与MAC地址进行绑定,使得ARP欺骗攻击者无法篡改ARP表。
管理员可以在网络设备上手动添加静态ARP 表项,确保网络中的主机只能与正确的MAC地址通信。
2. 使用ARP防火墙ARP防火墙可以监控网络中的ARP请求和响应,并根据事先设定的策略进行过滤。
当检测到ARP欺骗攻击时,ARP防火墙可以阻止异常的ARP请求和响应,保护网络中的主机免受攻击。
3. 使用网络入侵检测系统(NIDS)网络入侵检测系统可以监测网络流量中的异常ARP活动,如大量的ARP请求、多个主机使用相同的MAC地址等。
一旦检测到ARP攻击,NIDS可以及时发出警报并采取相应的防御措施,阻止攻击者进一步侵入网络。
4. 使用虚拟局域网(VLAN)虚拟局域网可以将网络划分为多个逻辑上的子网,不同子网之间的通信需要经过路由器进行转发。
通过使用VLAN,可以限制ARP欺骗攻击者的攻击范围,提高网络的安全性。
5. 使用加密通信协议使用加密通信协议(如SSL、IPsec等)可以加密通信过程中的数据,防止敏感信息在网络中被攻击者窃取。
即使遭受ARP攻击,攻击者也无法获取到加密的数据,保护网络中的通信安全。
三、解决方案1. 及时更新操作系统和应用程序操作系统和应用程序的漏洞是攻击者进行ARP攻击的入口之一。
及时更新操作系统和应用程序,安装最新的安全补丁,可以修复已知的漏洞,减少被攻击的风险。

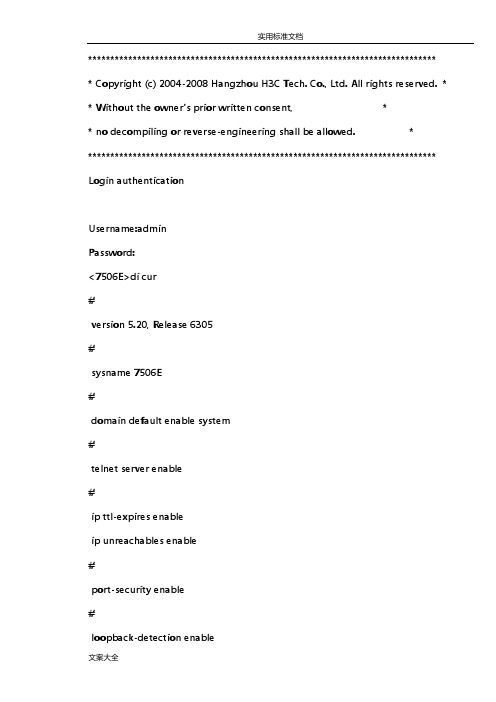
****************************************************************************** * Copyright (c) 2004-2008 Hangzhou H3C Tech. Co., Ltd. All rights reserved. * * Without the owner's prior written consent, ** no decompiling or reverse-engineering shall be allowed. ******************************************************************************* Login authenticationUsername:adminPassword:<7506E>di cur#version 5.20, Release 6305#sysname 7506E#domain default enable system#telnet server enable#ip ttl-expires enableip unreachables enable#port-security enable#loopback-detection enable#mirroring-group 1 localmirroring-group 2 local#switch-mode standard#acl number 3010description to UTM200rule 0 permit ip source 192.168.128.0 0.0.15.255 rule 1 permit ip source 192.168.160.0 0.0.31.255 acl number 3011rule 0 permit ip source 192.168.34.0 0.0.0.255 rule 1 permit ip source 192.168.37.0 0.0.0.255 rule 2 permit ip source 192.168.31.0 0.0.0.255 rule 3 permit ip source 192.168.39.0 0.0.0.255 rule 4 permit ip source 192.168.254.0 0.0.0.255 acl number 3500#vlan 1#vlan 2 to 2221#vlan 2222description wireless_guest#vlan 2223 to 2500#vlan 3000description test#vlan 3901description dianxin ap#vlan 3902description test#vlan 3985description dhcp for temp guest meeting supervlansubvlan 36#vlan 3986description dianxin wirelesssupervlansubvlan 3901#vlan 3987description huisuo vlan 33supervlansubvlan 33vlan 3988description wireless supervlansubvlan 2222#vlan 3989supervlansubvlan 3 to 29#vlan 3990supervlansubvlan 1226 to 1250 #vlan 3991supervlansubvlan 1200 to 1225 #vlan 3992supervlansubvlan 100 to 111 #vlan 3993supervlansubvlan 1032 to 1150vlan 3994supervlansubvlan 911 to 1031#vlan 3995supervlansubvlan 791 to 910#vlan 3996supervlansubvlan 351 to 421 747 to 790 #vlan 3997supervlansubvlan 231 to 350#vlan 3998supervlansubvlan 112 to 230#vlan 3999description to UTM200#vlan 4000 to 4001ftth#domain systemaccess-limit disablestate activeidle-cut disableself-service-url disable#traffic classifier kefang operator andif-match acl 3010traffic classifier denyvlanclass operator and if-match acl 3500#traffic behavior kefangredirect next-hop 192.168.145.2traffic behavior dengvlanfilter deny#qos policy kefangclassifier kefang behavior kefangqos policy denyvlanclassifier denyvlanclass behavior dengvlan #dhcp server ip-pool 3985network 192.168.36.0 mask 255.255.255.0 gateway-list 192.168.36.254dns-list 202.96.128.86 202.96.128.166 8.8.8.8 expired day 0 hour 8#dhcp server ip-pool 3986network 192.168.160.0 mask 255.255.224.0 gateway-list 192.168.160.1dns-list 202.96.128.86 8.8.8.8 202.96.128.166 expired day 0 hour 2#dhcp server ip-pool 3987network 192.168.33.0 mask 255.255.255.0 gateway-list 192.168.33.254dns-list 202.96.128.86 202.96.128.166 8.8.8.8 expired day 0 hour 8#dhcp server ip-pool 3988network 192.168.142.0 mask 255.255.254.0 gateway-list 192.168.142.1dns-list 202.96.128.86 202.96.128.166 8.8.8.8 expired day 0 hour 4#dhcp server ip-pool 3989network 192.168.140.0 mask 255.255.254.0gateway-list 192.168.140.1dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3990network 192.168..0 mask 255.255.254.0gateway-list 192.168..1dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3991network 192.168.136.0 mask 255.255.254.0gateway-list 192.168.136.1dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3992network 192.168.134.0 mask 255.255.254.0gateway-list 192.168.134.1dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3993network 192.168.132.128 mask 255.255.255.128 gateway-list 192.168.132.129dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3994network 192.168.132.0 mask 255.255.255.128 gateway-list 192.168.132.1dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3995network 192.168.131.128 mask 255.255.255.128 gateway-list 192.168.131.129dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3996network 192.168.131.0 mask 255.255.255.128 gateway-list 192.168.131.1dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3997network 192.168.130.128 mask 255.255.255.128 gateway-list 192.168.130.129dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3998network 192.168.130.0 mask 255.255.255.128 gateway-list 192.168.130.1dns-list 202.96.128.86 202.96.128.166 8.8.8.8 expired day 0 hour 4#dhcp server ip-pool 3999#local-user adminpassword cipher _PW\RO>8';4.[DN#`U3;6Q!! -type telnetlevel 3#stp instance 0 root primarystp enable#monitor-link group 1#interface NULL0#interface Vlan-interface1ip address 192.168.39.2 255.255.255.0#interface Vlan-interface2ip address 192.168.31.227 255.255.255.0 #interface Vlan-interface30ip address 192.168.30.254 255.255.255.0 #interface Vlan-interface32ip address 192.168.32.254 255.255.255.0 #interface Vlan-interface34ip address 192.168.34.254 255.255.255.0 #interface Vlan-interface35ip address 192.168.35.254 255.255.255.0 #interface Vlan-interface37ip address 192.168.37.254 255.255.255.0 #interface Vlan-interface38ip address 192.168.38.254 255.255.255.0 #interface Vlan-interface3985ip address 192.168.36.254 255.255.255.0 #ip address 192.168.160.1 255.255.224.0 local-proxy-arp enable#interface Vlan-interface3987ip address 192.168.33.254 255.255.255.0 #interface Vlan-interface3988ip address 192.168.142.1 255.255.254.0 #interface Vlan-interface3989ip address 192.168.140.1 255.255.254.0 local-proxy-arp enable#interface Vlan-interface3990ip address 192.168..1 255.255.254.0local-proxy-arp enable#interface Vlan-interface3991ip address 192.168.136.1 255.255.254.0 local-proxy-arp enable#interface Vlan-interface3992ip address 192.168.134.1 255.255.254.0 local-proxy-arp enableinterface Vlan-interface3993ip address 192.168.132.129 255.255.255.128 local-proxy-arp enable#interface Vlan-interface3994ip address 192.168.132.1 255.255.255.128 local-proxy-arp enable#interface Vlan-interface3995ip address 192.168.131.129 255.255.255.128 local-proxy-arp enable#interface Vlan-interface3996ip address 192.168.131.1 255.255.255.128 local-proxy-arp enable#interface Vlan-interface3997ip address 192.168.130.129 255.255.255.128 local-proxy-arp enable#interface Vlan-interface3998ip address 192.168.130.1 255.255.255.128 local-proxy-arp enable#description to UTM200ip address 192.168.145.1 255.255.255.0#interface Vlan-interface4000description to f1000-sip address 192.168.254.1 255.255.255.0#interface Vlan-interface4001ip address 192.168.254.101 255.255.255.252 #interface GigabitEthernet2/0/1port link-type trunkport trunk permit vlan 1 to 3984 3999 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/2port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/3port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inboundport link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/5port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/6port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/7port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/8port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inboundport link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/10port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/11port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/12port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet3/0/1port access vlan 4000qos apply policy kefang inbound#port link-type trunkundo port trunk permit vlan 1port trunk permit vlan 3 to 29 39 50 to 99 101 to 3984 4001 to 4094 port trunk pvid vlan 39qos apply policy kefang inboundmirroring-group 1 mirroring-port both#interface GigabitEthernet3/0/3port access vlan 2qos apply policy kefang inbound#interface GigabitEthernet3/0/4port access vlan 1227qos apply policy kefang inboundmirroring-group 2 monitor-port#interface GigabitEthernet3/0/5port access vlan 3901qos apply policy kefang inbound#interface GigabitEthernet3/0/6port access vlan 8#interface GigabitEthernet3/0/7description to UTM-200_G 0/0 qos apply policy kefang inbound #interface GigabitEthernet3/0/8 port access vlan 8qos apply policy kefang inbound #interface GigabitEthernet3/0/9 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/10 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/11 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/12 port access vlan 2#interface GigabitEthernet3/0/13 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/14 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/15 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/16 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/17 port access vlan 2#interface GigabitEthernet3/0/18 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/19 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/20 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/21 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/22 port access vlan 2#interface GigabitEthernet3/0/23 port access vlan 35stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/24 port access vlan 34stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/25 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/26 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/27 port link-type trunkmirroring-group 1 monitor-port#interface GigabitEthernet3/0/28port access vlan 2qos apply policy kefang inbound#interface GigabitEthernet3/0/29port access vlan 29qos apply policy kefang inbound#interface GigabitEthernet3/0/30port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet3/0/31port access vlan 4000qos apply policy kefang inbound#interface GigabitEthernet3/0/32port access vlan 2qos apply policy kefang inbound#port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/34 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/35 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/36 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/37 port access vlan 37qos apply policy kefang inbound #interface GigabitEthernet3/0/38 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/39qos apply policy kefang inbound #interface GigabitEthernet3/0/40 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/41 port access vlan 2stp disablestp loop-protectionqos apply policy kefang inbound #interface GigabitEthernet3/0/42 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/43 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/44 port access vlan 34qos apply policy kefang inbound #port access vlan 2qos apply policy kefang inbound#interface GigabitEthernet3/0/46port access vlan 35qos apply policy kefang inbound#interface GigabitEthernet3/0/47port link-type trunkport trunk permit vlan 1 30qos apply policy kefang inbound#interface GigabitEthernet3/0/48port access vlan 34qos apply policy kefang inbound#interface GigabitEthernet4/0/1port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/2port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094#interface GigabitEthernet4/0/3port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/4port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/5port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/6port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/7port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094interface GigabitEthernet4/0/8port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/9port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/10port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/11port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/12port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094interface GigabitEthernet4/0/13port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/14port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/15port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/16port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/17port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094interface GigabitEthernet4/0/18port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/19port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/20port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/21port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/22port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094interface GigabitEthernet4/0/23port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/24port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/25port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/26port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/27port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094interface GigabitEthernet4/0/28port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/29port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/30port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/31port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/32port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094interface GigabitEthernet4/0/33port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/34port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/35port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/36port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/37port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094interface GigabitEthernet4/0/38port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/39port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/40port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/41port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/42port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094interface GigabitEthernet4/0/43port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/44port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/45port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/46port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/47port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094interface GigabitEthernet4/0/48port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/1port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 loopback-detection enableqos apply policy kefang inbound#interface GigabitEthernet8/0/2port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/3port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/4port link-type trunk#interface GigabitEthernet8/0/5port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/6port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/7port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/8port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/9port link-type trunk#interface GigabitEthernet8/0/10port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/11port link-type trunkundo port trunk permit vlan 1port trunk permit vlan 3901qos apply policy kefang inboundmirroring-group 2 mirroring-port both#interface GigabitEthernet8/0/12port access vlan 30description 到集团综合楼qos apply policy kefang inbound#interface GigabitEthernet9/0/1port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#port trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/3port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/4port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/5port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/6port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#port trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/8port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/9port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/10port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/11port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#port trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface M-Ethernet0/0/0#interface Ten-GigabitEthernet5/0/1port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface Ten-GigabitEthernet5/0/2port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface Ten-GigabitEthernet6/0/1port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface Ten-GigabitEthernet6/0/2port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094#route-policy kefang permit node 0if-match acl 3010apply ip-address next-hop 192.168.129.1#ip route-static 0.0.0.0 0.0.0.0 192.168.254.2ip route-static 10.0.0.0 255.255.255.0 192.168.30.253ip route-static 10.0.18.0 255.255.255.0 192.168.30.253ip route-static 10.0.24.0 255.255.255.0 192.168.30.253ip route-static 10.0.25.0 255.255.255.0 192.168.30.253ip route-static 10.0.29.0 255.255.255.0 192.168.30.253ip route-static 10.0.97.0 255.255.255.0 192.168.30.253ip route-static 10.10.0.0 255.255.0.0 192.168.30.253ip route-static 10.11.2.0 255.255.255.0 192.168.30.253ip route-static 10.11.30.0 255.255.255.0 192.168.30.253ip route-static 10.11.70.0 255.255.255.0 192.168.30.253ip route-static 10.11.72.0 255.255.255.0 192.168.30.253ip route-static 10.12.41.0 255.255.255.0 192.168.30.253ip route-static 10.100.1.0 255.255.255.0 192.168.30.253ip route-static 116.6.69.101 255.255.255.255 192.168.30.253 ip route-static 172.16.1.0 255.255.255.0 61.144.43.216ip route-static 172.16.1.0 255.255.255.0 192.168.145.2ip route-static 192.168.0.0 255.255.255.0 192.168.30.253ip route-static 192.168.4.0 255.255.255.0 192.168.30.253ip route-static 192.168.5.0 255.255.255.0 192.168.30.253ip route-static 192.168.7.0 255.255.255.0 192.168.30.253ip route-static 192.168.8.0 255.255.255.0 192.168.30.253ip route-static 192.168.9.0 255.255.255.0 192.168.30.253ip route-static 192.168.19.0 255.255.255.0 192.168.30.253 ip route-static 192.168.21.0 255.255.255.0 192.168.30.253 ip route-static 192.168.22.0 255.255.255.0 192.168.30.253 ip route-static 192.168.23.0 255.255.255.0 192.168.30.253 ip route-static 192.168.24.0 255.255.255.0 192.168.30.253 ip route-static 192.168.26.0 255.255.255.0 192.168.30.253 ip route-static 192.168.28.0 255.255.255.0 192.168.30.253 ip route-static 192.168.29.0 255.255.255.0 192.168.30.253 ip route-static 192.168.41.0 255.255.255.0 192.168.30.253 ip route-static 192.168.46.0 255.255.255.0 192.168.30.253 ip route-static 192.168.68.0 255.255.255.0 192.168.30.253 ip route-static 192.168.76.0 255.255.255.0 192.168.30.253 ip route-static 192.168.82.0 255.255.255.0 192.168.30.253 ip route-static 192.168.84.0 255.255.255.0 192.168.30.253 ip route-static 192.168.86.0 255.255.255.0 192.168.30.253 ip route-static 192.168.88.0 255.255.255.0 192.168.30.253 ip route-static 192.168.91.0 255.255.255.0 192.168.30.253 ip route-static 192.168.96.0 255.255.255.0 192.168.30.253 ip route-static 192.168.103.0 255.255.255.0 192.168.30.253 ip route-static 192.168.202.0 255.255.255.0 192.168.30.253 ip route-static 192.168.253.0 255.255.255.0 192.168.253.1 ip route-static 192.168.254.4 255.255.255.252 192.168.254.2#snmp-agentsnmp-agent local-engineid 800063A203000FE22EDA1Csnmp-agent community write q-ideasnmp-agent sys-info version allsnmp-agent target-host trap address udp-domain 192.168.34.120 udp-port 5000 params securityname q-idea#dhcp server detect#dhcp enable#user-interface aux 0idle-timeout 0 0user-interface vty 0 4acl 3011 inboundauthentication-mode schemeuser privilege level 3#return<7506E>。
网络设备维护手册第一章交换机操作手册此部分档使用本项目交换机型号如下:S7506E/S5120/S5130/WX3024E1.1设备登陆1.1.1Console登陆1、通过交换机Console口进行本地登录是登录交换机的最基本的方式,也是配置通过其他方式登录交换机的基础。
连接示意图如下:2、把电脑和交换机连接好后,交换机上电开机,然后在电脑上进行如下操作,首先点击开始->程序->附件->通讯->超级终端打开后出现下面图示,输入名称,可以任意输入。
输入完成点击确定,出现下面界面,连接时使用选择COM口,一般台式机为COM1或COM2,而笔记本经过转接,可能会产生COM3或COM4,也有可能是其他的,你可以在下面的选择项里看到,选择完成后点击确定。
通过上面的选择,现在到了对端口属性进行设置,一般情况下没有进行过修改,默认只要点击还原为默认值就可以了,然后再单击确定。
之后敲回车即可,会出现H3C>提示符,说明已经与交换机连接,可以进行配置了,如果没有可以重启交换机或检查连接是否正确。
1.1.2telnet登陆1、新建用户名密码local-useradmin/admin为用户名passwordcipherh3c@123/h3c@123为密码authorization-attributelevel3/授权admin用户的等级为3,3为最高级service-typetelnet/授权admin用户的登陆方式,可以为ftp、telnet等#telnetserverenable/开启telnet服务使用电脑连接至交换机:开始菜单-输入cmd,如下图,输入telnet1.2交换机加电开机显示sarting......****************************************************************H3CS5510-24PBOOTROM,Version142****************************************************************Copyright(c)2004-2008HangzhouH3CTech.Co.,Ltd.Creationdate:Mar122008,11:17:30CPUClockSpeed:200MHzBUSClockSpeed:33MHzMemorySize:128MBTheswitchMacis:000F-E2B1-BD60PressCtrl-BtoenterBootMenu...1 0Auto-booting...DecompressImage.................................................................................................................................................................... .................................................................................................................................................................................................. .................................................................................................................................................................................................. .................................................................................................................................................................................................. ...........................................................................................................................................................................................OK!Starting...*******************************************************************************Copyright(c)2004-2008HangzhouH3CTech.Co.,Ltd.Allrightsreserved.**Withouttheowner'spriorwrittenconsent,**nodecompilingorreverse-engineeringshallbeallowed.******************************************************************************* Itwilltakealongtimetogetconfigurationfile,pleasewait...Startupconfigurationfiledoesnotexist.Userinterfaceaux0isavailable.//开机自检过程1.3交换机常用PressENTERtogetstarted.<H3C>%Apr2612:03:53:6112000H3CSHELL/4/LOGIN:Consoleloginfromaux0<H3C><H3C>sys//进入视图模式SystemView:returntoUserViewwithCtrl+Z. [H3C][H3C]sysnameneiwang//对交换机进行命名[neiwang]discu//查看交换机配置#version5.20,Release5303#sysnameneiwang#domaindefaultenablesystem#domainsystemaccess-limitdisablestateactiveidle-cutdisableself-service-urldisable#interfaceNULL0#interfaceGigabitEthernet1/0/1#interfaceGigabitEthernet1/0/2#interfaceGigabitEthernet1/0/3#interfaceGigabitEthernet1/0/4#interfaceGigabitEthernet1/0/5#interfaceGigabitEthernet1/0/6#interfaceGigabitEthernet1/0/7#interfaceGigabitEthernet1/0/8#interfaceGigabitEthernet1/0/9#interfaceGigabitEthernet1/0/10#interfaceGigabitEthernet1/0/11#interfaceGigabitEthernet1/0/12#interfaceGigabitEthernet1/0/13#interfaceGigabitEthernet1/0/14interfaceGigabitEthernet1/0/15#interfaceGigabitEthernet1/0/16#interfaceGigabitEthernet1/0/17#interfaceGigabitEthernet1/0/18#interfaceGigabitEthernet1/0/19#interfaceGigabitEthernet1/0/20#interfaceGigabitEthernet1/0/21#interfaceGigabitEthernet1/0/22#interfaceGigabitEthernet1/0/23#interfaceGigabitEthernet1/0/24#interfaceGigabitEthernet1/0/25shutdown#interfaceGigabitEthernet1/0/26shutdown#interfaceGigabitEthernet1/0/27shutdown#interfaceGigabitEthernet1/0/28shutdown#user-interfaceaux0user-interfacevty04#return[neiwang][neiwangvlan25//创建VLAN[neiwang-vlan25]portGigabitEthernet1/0/1toGigabitEthernet1/0/10//给VLAN批量添加端口[neiwang-vlan25]qu//退出VLAN视图[neiwang]interfacevlan25//进入VLAN接口视图[neiwang-Vlan-interface25]ipaddress24//给VLAN添加IP地址[neiwang-Vlan-interface25]qu//退出VLAn接口视图[neiwang]discu//再次查看交换机配置,可以看到多了一个VLAN及这个VLAN的IP地址version5.20,Release5303#sysnameneiwang# domaindefaultenablesystem #vlan1#vlan25#domainsystemaccess-limitdisable stateactiveidle-cutdisableself-service-urldisable#interfaceNULL0#interfaceVlan-interface25 ipaddress# interfaceGigabitEthernet1/0/1 portaccessvlan25# interfaceGigabitEthernet1/0/2 portaccessvlan25# interfaceGigabitEthernet1/0/3 portaccessvlan25# interfaceGigabitEthernet1/0/4 portaccessvlan25# interfaceGigabitEthernet1/0/5 portaccessvlan25# interfaceGigabitEthernet1/0/6 portaccessvlan25# interfaceGigabitEthernet1/0/7 portaccessvlan25# interfaceGigabitEthernet1/0/8 portaccessvlan25# interfaceGigabitEthernet1/0/9 portaccessvlan25interfaceGigabitEthernet1/0/10 portaccessvlan25# interfaceGigabitEthernet1/0/11 # interfaceGigabitEthernet1/0/12 # interfaceGigabitEthernet1/0/13 # interfaceGigabitEthernet1/0/14 # interfaceGigabitEthernet1/0/15 # interfaceGigabitEthernet1/0/16 # interfaceGigabitEthernet1/0/17 # interfaceGigabitEthernet1/0/18 # interfaceGigabitEthernet1/0/19 # interfaceGigabitEthernet1/0/20 # interfaceGigabitEthernet1/0/21 # interfaceGigabitEthernet1/0/22 # interfaceGigabitEthernet1/0/23 # interfaceGigabitEthernet1/0/24 # interfaceGigabitEthernet1/0/25 shutdown# interfaceGigabitEthernet1/0/26 shutdown# interfaceGigabitEthernet1/0/27 shutdown# interfaceGigabitEthernet1/0/28 shutdown#user-interfaceaux0user-interfacevty04#return[neiwang]telnetserverenable%StartTelnetserver//下面是为交换机添加一个新用户操作[neiwang]local-useradmin//添加新用户Newlocaluseradded.[neiwang-luser-admin]pasinadmin//为新用户设置密码[neiwang-luser-admin]service-typetelnetlevel3//为新用户设置服务及权限[neiwang-luser-admin]qu//下面为该用户配置telnet服务[neiwang]user-interfacevty?INTEGER<0-4>Firstuserterminalinterfacenumbertobeconfigured [neiwang]user-interfacevty04//进入telnet视图模式[neiwang-ui-vty0-4]authentication-modescheme?//认证模式设置noneLoginwithoutchecking passwordAuthenticationusepasswordofuserterminalinterface schemeAuthenticationuseAAA[neiwang-ui-vty0-4]authentication-modes[neiwang-ui-vty0-4]authentication-modescheme//设备认证模式为用户名密码[neiwang-ui-vty0-4]qu[neiwang]telnetserverenable//开启telnet服务[neiwang]save?STRINGThenameofspecificfile(*.cfg) safelySavecurrentconfigurationsafely<cr>[neiwang]saves[neiwang]savesafely//保存交换机设置,以防断电交换机配置丢失[neiwang]saves?savesftpshutdown-intervalsnmp-agentsshsslstpsuperswitch-modesysname[neiwang]savesafely Thecurrentconfigurationwillbewrittentothedevice.Areyousure?[Y/N]:y Pleaseinputthefilename(*.cfg)[flash:/startup.cfg] (Toleavetheexistingfilenameunchanged,presstheenterkey):Validatingfile.Pleasewait... Nowsavingcurrentconfigurationtothedevice. Savingconfigurationflash:/startup.cfg.Pleasewait... .................Configurationissavedtoflashsuccessfully.[neiwang]qu<neiwang>saveThecurrentconfigurationwillbewrittentothedevice.Areyousure?[Y/N]:n<neiwang>sysSystemView:returntoUserViewwithCtrl+Z.[neiwang]DHCPSnoopingwasenabled.//下面为对VLAN及端口增加删除进行操作先输入sys进入全局模式,必须输,然后输命令前面字母按TAB [neiwang][neiwang][neiwang]int[neiwang]interfaceg[neiwang]interfaceGigabitEthernet1/0/15//进入交换机端口模式[neiwang-GigabitEthernet1/0/15]portacc[neiwang-GigabitEthernet1/0/15]portaccessvlan25//单一端口添加到VLAN [neiwang-GigabitEthernet1/0/15]portaccessvlan26//如果VLAN没有创建,提示如下Error:ThisVLANdoesnotexist.[neiwang-GigabitEthernet1/0/15]qu[neiwang]vlan26[neiwang-vlan26][neiwang-GigabitEthernet1/0/15]portaccessvlan26[neiwang-GigabitEthernet1/0/15]qu//下面为对单一端口属性进行设置[neiwang]intg1/0/25[neiwang-GigabitEthernet1/0/25]sp[neiwang-GigabitEthernet1/0/25]speed1000//把25号端口强制为1000M [neiwang-GigabitEthernet1/0/25]du[neiwang-GigabitEthernet1/0/25]duplexful[neiwang-GigabitEthernet1/0/25]duplexfull//把25号端口强制为全双工[neiwang-GigabitEthernet1/0/25]port[neiwang-GigabitEthernet1/0/25]portlink-t[neiwang-GigabitEthernet1/0/25]portlink-type?accessAccesslink-typehybridHybridVLANlink-typetrunkVLANTrunklink-type[neiwang-GigabitEthernet1/0/25]portlink-typetr[neiwang-GigabitEthernet1/0/25]portlink-typetrunk//定义该端口为trunk属性<cr>[neiwang-GigabitEthernet1/0/25]porttrunkpermitall?^%Unrecognizedcommandfoundat'^'position.[neiwang-GigabitEthernet1/0/25]porttrunkpermitall?//允许所有VLAN通过该端口INTEGER<1-4094>VLANIDallAlltheVLANs[neiwang-GigabitEthernet1/0/25]porttrunkpermitvlanall?<cr>[neiwang-GigabitEthernet1/0/25]porttrunkpermitvlanall Pleasewait...........Done.<cr>[neiwang-GigabitEthernet1/0/25]undoportlink-type//取消该端口属性前面加undo Pleasewait...........Done.[neiwang-GigabitEthernet1/0/25]sp[neiwang-GigabitEthernet1/0/25]speed?10Specifyspeedofcurrentport10Mb/s100Specifyspeedofcurrentport100Mb/s1000Specifyspeedofcurrentport1000Mb/sautoEnableport'sspeednegotiationautomatically[neiwang-GigabitEthernet1/0/25]speedau[neiwang-GigabitEthernet1/0/25]speedauto[neiwang-GigabitEthernet1/0/25]du[neiwang-GigabitEthernet1/0/25]duplexau[neiwang-GigabitEthernet1/0/25]duplexauto[neiwang-GigabitEthernet1/0/25]qu[neiwang]dhcp[neiwang]dhcp-snooping?<cr>[neiwang]dhcp-snoopingDHCPSnoopinghasalreadybeenenabled.[neiwang]intg1/0/25[neiwang-GigabitEthernet1/0/25]dhcp[neiwang-GigabitEthernet1/0/25]dhcp-snooping?informationSpecifyOption82servicetrustTrustedport[neiwang-GigabitEthernet1/0/25]dhcp-snoopingtr[neiwang-GigabitEthernet1/0/25]dhcp-snoopingtrust?<cr>[neiwang-GigabitEthernet1/0/25]dhcp-snoopingtrust[neiwang-GigabitEthernet1/0/25]qu[neiwang]disvaln?INTEGER<1-4094>VLANIDallAlltheVLANsdynamicDynamicVLANIDreservedReservedVLANIDstaticStaticVLANID<cr>[neiwang]disvlanall//查看显示VLANVLANID:1VLANType:staticRouteInterface:notconfiguredDescription:VLAN0001TaggedPorts:noneUntaggedPorts:GigabitEthernet1/0/11GigabitEthernet1/0/12GigabitEthernet1/0/13 GigabitEthernet1/0/14GigabitEthernet1/0/15GigabitEthernet1/0/16 GigabitEthernet1/0/17GigabitEthernet1/0/18GigabitEthernet1/0/19 GigabitEthernet1/0/20GigabitEthernet1/0/21GigabitEthernet1/0/22 GigabitEthernet1/0/23GigabitEthernet1/0/24GigabitEthernet1/0/25GigabitEthernet1/0/26GigabitEthernet1/0/27GigabitEthernet1/0/28 VLANID:25VLANType:staticRouteInterface:configuredIPAddress:SubnetMask:Description:VLAN0025TaggedPorts:noneUntaggedPorts:GigabitEthernet1/0/1GigabitEthernet1/0/2GigabitEthernet1/0/3 GigabitEthernet1/0/4GigabitEthernet1/0/5GigabitEthernet1/0/6 GigabitEthernet1/0/7GigabitEthernet1/0/8GigabitEthernet1/0/9 GigabitEthernet1/0/10[neiwang]disvlanall%Apr2612:28:45:142000neiwangIFNET/4/LINKUPDOWN: GigabitEthernet1/0/13:linkstatusisDOWN%Apr2612:28:46:9042000neiwangIFNET/4/LINKUPDOWN: GigabitEthernet1/0/9:linkstatusisUP%Apr2612:28:46:9142000neiwangIFNET/4/LINKUPDOWN: Vlan-interface25:linkstatusisUP%Apr2612:28:46:9172000neiwangIFNET/4/UPDOWN: LineprotocolontheinterfaceVlan-interface25isUP DHCPSnoopinghasalreadybeenenabled.[neiwang]disarp//三层交换机查看arp列表^%Incompletecommandfoundat'^'position.[neiwang]disarp?DisplayARPentrybyspecialIPaddressallDisplaystatic&dynamicARPentry dynamicDisplaydynamicARPentry interfaceDisplaybyInterfacesource-suppressionDisplayARPsourcesuppression staticDisplaystaticARPentrytimerDisplayARPtimervlanDisplaybyVLANvpn-instanceDisplayARPentriesbyVPNname[neiwang]disarpallType:S-StaticD-Dynamic IPAddressMACAddressVLANIDInterfaceAgingType [neiwang]dismac-a[neiwang]dismac-address?//查看交换机mac地址列表H-H-HMACaddressaging-timeGlobalagingtimeblackholeBlackholeentry,withoutaging,canbeadded/deleted,savedto theconfigurationfilecountMACentriescountdynamicDynamicentry,withaging,canbeadded/deleted,lostafter resetinterfaceChooseoneinterfacetodisplaystaticStaticentry,withoutaging,canbeadded/deleted,savedtothe configurationfilevlanVLAN<cr>[neiwang]dismac-addressNoMulticastMacaddressesfound.[neiwang]%Apr2612:30:36:5272000neiwangSHELL/4/LOGIN:adminloginfrom%Apr2612:31:14:1412000neiwangSHELL/4/LOGOUT:adminlogoutfrom #interfaceVlan-interface4000//路由添加管理口vlanipaddress//路由添加管理地址IP#interfaceGigabitEthernet1/0/52//回程路由#iproute-static//指定要回跳的路由第二章无线维护手册2.1设备登陆此步骤参考1.1设备登陆2.2设备常用操作2.2.1注册APwlanapAP1modelWA2620i-AGN/MODEL的型号一定要和实际一样serial-id219801A0CNC149002626/手工注册方式序列号一定要正确radio1/2620i是双频APservice-template10/调用服务模板radioenable/启用射频口radio2service-template10radioenable2.2.2配置SSID名称wlanservice-template10/新建服务模板10ssidTAXZFWZX/ssid为TAXZFWZXbindWLAN-ESS10/绑定无线接口10authentication-methodopen-system/以下为加密方案cipher-suitetkipsecurity-iewpaservice-templateenable/启用服务模板#interfaceWLAN-ESS10/新建无线接口10,供服务模板调用port-securityport-modepsk/以下为认证信息port-securitytx-key-type11keyport-securitypreshared-keypass-phrasesih3c@123。
ARP攻击的防范与解决方案目录1.故障现象 (1)2.故障原理 (1)3.在局域网内查找病毒主机方法 (2)3.1在PC上绑定路由器的IP和MAC地址 (3)3.2在路由器上绑定用户主机的IP和MAC地址 (3)3.3关闭并重启端口检测功能 (4)“Trojan.PSW.LMir.qh”传奇杀手木马病毒,俗称“ARP欺骗攻击”,其主要通过伪造IP 地址和MAC地址实现ARP欺骗,能够在网络中产生大量的ARP通信量使网络阻塞或者实现“man in the middle”进行ARP重定向和嗅探攻击。
1. 故障现象间断性断网,网速变慢,本机IP地址和MAC地址发生变化。
当局域网内某台主机运行ARP欺骗的木马程序时,会欺骗局域网内所有主机和路由器,让所有上网的流量必须经过病毒主机。
其他用户原来直接通过路由器上网现在转由通过病毒主机上网,切换的时候用户会断一次线。
切换到病毒主机上网后,如果用户已经登陆了服务器,那么病毒主机就会经常伪造断线的假像,那么用户就得重新登录服务器,这样病毒主机就可以盗号了。
由于ARP欺骗的木马程序发作的时候会发出大量的数据包导致局域网通讯拥塞以及其自身处理能力的限制,用户会感觉上网速度越来越慢。
当ARP欺骗的木马程序停止运行时,用户会恢复从路由器上网,切换过程中用户会再断一次线。
2. 故障原理要了解故障原理,我们先来了解一下ARP协议。
在局域网中,通过ARP协议来完成IP地址转换为第二层物理地址(即MAC地址)的。
ARP 协议对网络安全具有重要的意义。
通过伪造IP地址和MAC地址实现ARP欺骗,能够在网络中产生大量的ARP通信量使网络阻塞。
ARP协议是“Address Resolution Protocol”(地址解析协议)的缩写。
在局域网中,网络中实际传输的是“帧”,帧里面是有目标主机的MAC地址的。
在以太网中,一个主机要和另一个主机进行直接通信,必须要知道目标主机的MAC地址。
***************************************************************** ************** Copyright (c) 2004-2008 Hangzhou H3C Tech. Co., Ltd. All rights reserved. ** Without the owner's prior written consent, ** no decompiling or reverse-engineering shall be allowed. ****************************************************************** *************Login authenticationUsername:adminPassword:<7506E>di cur#version 5.20, Release 6305#sysname 7506E#domain default enable system#telnet server enable#ip ttl-expires enableip unreachables enable#port-security enable#loopback-detection enable#mirroring-group 1 localmirroring-group 2 local#switch-mode standard#acl number 3010description to UTM200rule 0 permit ip source 192.168.128.0 0.0.15.255 rule 1 permit ip source 192.168.160.0 0.0.31.255 acl number 3011rule 0 permit ip source 192.168.34.0 0.0.0.255 rule 1 permit ip source 192.168.37.0 0.0.0.255 rule 2 permit ip source 192.168.31.0 0.0.0.255 rule 3 permit ip source 192.168.39.0 0.0.0.255 rule 4 permit ip source 192.168.254.0 0.0.0.255 acl number 3500#vlan 1#vlan 2 to 2221#vlan 2222description wireless_guest#vlan 2223 to 2500#vlan 3000description test#vlan 3901description dianxin ap#vlan 3902description test#vlan 3985description dhcp for temp guest meeting supervlansubvlan 36#vlan 3986description dianxin wirelesssupervlansubvlan 3901#vlan 3987description huisuo vlan 33supervlansubvlan 33#vlan 3988description wirelesssupervlansubvlan 2222#vlan 3989supervlansubvlan 3 to 29#vlan 3990supervlansubvlan 1226 to 1250#vlan 3991supervlansubvlan 1200 to 1225#vlan 3992supervlansubvlan 100 to 111#vlan 3993supervlansubvlan 1032 to 1150#vlan 3994supervlansubvlan 911 to 1031#vlan 3995supervlansubvlan 791 to 910#vlan 3996supervlansubvlan 351 to 421 747 to 790 #vlan 3997supervlansubvlan 231 to 350#vlan 3998supervlansubvlan 112 to 230#vlan 3999description to UTM200#vlan 4000 to 4001#ftth#domain systemaccess-limit disablestate activeidle-cut disableself-service-url disable#traffic classifier kefang operator andif-match acl 3010traffic classifier denyvlanclass operator andif-match acl 3500#traffic behavior kefangredirect next-hop 192.168.145.2traffic behavior dengvlanfilter deny#qos policy kefangclassifier kefang behavior kefangqos policy denyvlanclassifier denyvlanclass behavior dengvlan#dhcp server ip-pool 3985network 192.168.36.0 mask 255.255.255.0gateway-list 192.168.36.254dns-list 202.96.128.86 202.96.128.166 8.8.8.8 expired day 0 hour 8#dhcp server ip-pool 3986network 192.168.160.0 mask 255.255.224.0 gateway-list 192.168.160.1dns-list 202.96.128.86 8.8.8.8 202.96.128.166 expired day 0 hour 2#dhcp server ip-pool 3987network 192.168.33.0 mask 255.255.255.0gateway-list 192.168.33.254dns-list 202.96.128.86 202.96.128.166 8.8.8.8 expired day 0 hour 8#dhcp server ip-pool 3988network 192.168.142.0 mask 255.255.254.0 gateway-list 192.168.142.1dns-list 202.96.128.86 202.96.128.166 8.8.8.8 expired day 0 hour 4#dhcp server ip-pool 3989network 192.168.140.0 mask 255.255.254.0 gateway-list 192.168.140.1dns-list 202.96.128.86 202.96.128.166 8.8.8.8 expired day 0 hour 4#dhcp server ip-pool 3990network 192.168.138.0 mask 255.255.254.0 gateway-list 192.168.138.1dns-list 202.96.128.86 202.96.128.166 8.8.8.8 expired day 0 hour 4#dhcp server ip-pool 3991network 192.168.136.0 mask 255.255.254.0 gateway-list 192.168.136.1dns-list 202.96.128.86 202.96.128.166 8.8.8.8 expired day 0 hour 4#dhcp server ip-pool 3992network 192.168.134.0 mask 255.255.254.0gateway-list 192.168.134.1dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3993network 192.168.132.128 mask 255.255.255.128 gateway-list 192.168.132.129dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3994network 192.168.132.0 mask 255.255.255.128 gateway-list 192.168.132.1dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3995network 192.168.131.128 mask 255.255.255.128 gateway-list 192.168.131.129dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3996network 192.168.131.0 mask 255.255.255.128 gateway-list 192.168.131.1dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3997network 192.168.130.128 mask 255.255.255.128 gateway-list 192.168.130.129dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3998network 192.168.130.0 mask 255.255.255.128 gateway-list 192.168.130.1dns-list 202.96.128.86 202.96.128.166 8.8.8.8expired day 0 hour 4#dhcp server ip-pool 3999#local-user adminpassword cipher _PW\RO>8';4.[DN#`U3;6Q!!service-type telnetlevel 3#stp instance 0 root primarystp enable#monitor-link group 1#interface NULL0#interface Vlan-interface1ip address 192.168.39.2 255.255.255.0#interface Vlan-interface2ip address 192.168.31.227 255.255.255.0#interface Vlan-interface30#interface Vlan-interface32ip address 192.168.32.254 255.255.255.0 #interface Vlan-interface34ip address 192.168.34.254 255.255.255.0 #interface Vlan-interface35ip address 192.168.35.254 255.255.255.0 #interface Vlan-interface37ip address 192.168.37.254 255.255.255.0 #interface Vlan-interface38ip address 192.168.38.254 255.255.255.0 #interface Vlan-interface3985ip address 192.168.36.254 255.255.255.0 #interface Vlan-interface3986 (分配网关)ip address 192.168.160.1 255.255.224.0 local-proxy-arp enable#interface Vlan-interface3987ip address 192.168.33.254 255.255.255.0 #interface Vlan-interface3988ip address 192.168.142.1 255.255.254.0 #interface Vlan-interface3989local-proxy-arp enable#interface Vlan-interface3990ip address 192.168.138.1 255.255.254.0local-proxy-arp enable#interface Vlan-interface3991ip address 192.168.136.1 255.255.254.0local-proxy-arp enable#interface Vlan-interface3992ip address 192.168.134.1 255.255.254.0local-proxy-arp enable#interface Vlan-interface3993ip address 192.168.132.129 255.255.255.128 local-proxy-arp enable#interface Vlan-interface3994ip address 192.168.132.1 255.255.255.128 local-proxy-arp enable#interface Vlan-interface3995ip address 192.168.131.129 255.255.255.128 local-proxy-arp enable#interface Vlan-interface3996ip address 192.168.131.1 255.255.255.128 local-proxy-arp enable#interface Vlan-interface3997ip address 192.168.130.129 255.255.255.128 local-proxy-arp enable#interface Vlan-interface3998ip address 192.168.130.1 255.255.255.128local-proxy-arp enable#interface Vlan-interface3999description to UTM200ip address 192.168.145.1 255.255.255.0#interface Vlan-interface4000description to f1000-sip address 192.168.254.1 255.255.255.0#interface Vlan-interface4001ip address 192.168.254.101 255.255.255.252 #interface GigabitEthernet2/0/1port link-type trunkport trunk permit vlan 1 to 3984 3999 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/2port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/3port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/4port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/5port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/6port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/7port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/8port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/9port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet2/0/10port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094qos apply policy kefang inbound#interface GigabitEthernet2/0/11port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094qos apply policy kefang inbound#interface GigabitEthernet2/0/12port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094qos apply policy kefang inbound#interface GigabitEthernet3/0/1port access vlan 4000qos apply policy kefang inbound#interface GigabitEthernet3/0/2port link-type trunkundo port trunk permit vlan 1port trunk permit vlan 3 to 29 39 50 to 99 101 to 3984 4001 to 4094 port trunk pvid vlan 39qos apply policy kefang inboundmirroring-group 1 mirroring-port both#interface GigabitEthernet3/0/3port access vlan 2qos apply policy kefang inbound#interface GigabitEthernet3/0/4port access vlan 1227mirroring-group 2 monitor-port #interface GigabitEthernet3/0/5 port access vlan 3901qos apply policy kefang inbound #interface GigabitEthernet3/0/6 port access vlan 8#interface GigabitEthernet3/0/7 port access vlan 3999description to UTM-200_G 0/0 qos apply policy kefang inbound #interface GigabitEthernet3/0/8 port access vlan 8qos apply policy kefang inbound #interface GigabitEthernet3/0/9 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/10 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/11 port access vlan 2stp edged-port enable#interface GigabitEthernet3/0/12 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/13 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/14 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/15 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/16 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/17 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/18 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/19 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/20 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/21 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/22 port access vlan 2stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/23 port access vlan 35stp edged-port enableqos apply policy kefang inbound #interface GigabitEthernet3/0/24 port access vlan 34stp edged-port enableqos apply policy kefang inbound#interface GigabitEthernet3/0/25port access vlan 2stp edged-port enableqos apply policy kefang inbound#interface GigabitEthernet3/0/26port access vlan 2stp edged-port enableqos apply policy kefang inbound#interface GigabitEthernet3/0/27port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inboundmirroring-group 1 monitor-port#interface GigabitEthernet3/0/28port access vlan 2qos apply policy kefang inbound#interface GigabitEthernet3/0/29port access vlan 29qos apply policy kefang inbound#interface GigabitEthernet3/0/30port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound##interface GigabitEthernet3/0/32 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/33 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/34 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/35 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/36 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/37 port access vlan 37qos apply policy kefang inbound #interface GigabitEthernet3/0/38 port access vlan 2qos apply policy kefang inbound ##interface GigabitEthernet3/0/40 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/41 port access vlan 2stp disablestp loop-protectionqos apply policy kefang inbound #interface GigabitEthernet3/0/42 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/43 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/44 port access vlan 34qos apply policy kefang inbound #interface GigabitEthernet3/0/45 port access vlan 2qos apply policy kefang inbound #interface GigabitEthernet3/0/46 port access vlan 35qos apply policy kefang inbound#interface GigabitEthernet3/0/47port link-type trunkport trunk permit vlan 1 30qos apply policy kefang inbound#interface GigabitEthernet3/0/48port access vlan 34qos apply policy kefang inbound#interface GigabitEthernet4/0/1port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/2port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/3port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/4port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/5port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/6port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/7port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/8port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/9port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/10port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/11port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094qos apply policy kefang inbound#interface GigabitEthernet4/0/12port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/13port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/14port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/15port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/16port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/17port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/18port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/19port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/20port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/21port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/22port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/23port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/24port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/25port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/26port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/27port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/28port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/29port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/30port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/31port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/32port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/33port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/34port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/35port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/36port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/37port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/38port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/39port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/40port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/41port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/42port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/43port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094qos apply policy kefang inbound#interface GigabitEthernet4/0/44port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/45port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/46port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/47port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet4/0/48port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/1port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 loopback-detection enableqos apply policy kefang inbound#interface GigabitEthernet8/0/2port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/3port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/4port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/5port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/6port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/7port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/8port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/9port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/10port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet8/0/11port link-type trunkundo port trunk permit vlan 1port trunk permit vlan 3901qos apply policy kefang inboundmirroring-group 2 mirroring-port both#interface GigabitEthernet8/0/12port access vlan 30description 到集团综合楼qos apply policy kefang inbound#interface GigabitEthernet9/0/1port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/2port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/3port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/4port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/5port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/6port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/7port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/8port link-type trunkinterface GigabitEthernet9/0/9port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/10port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/11port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface GigabitEthernet9/0/12port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface M-Ethernet0/0/0#interface Ten-GigabitEthernet5/0/1port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094 qos apply policy kefang inbound#interface Ten-GigabitEthernet5/0/2port link-type trunkinterface Ten-GigabitEthernet6/0/1port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094qos apply policy kefang inbound#interface Ten-GigabitEthernet6/0/2port link-type trunkport trunk permit vlan 1 to 3984 4000 to 4094qos apply policy kefang inbound#route-policy kefang permit node 0if-match acl 3010apply ip-address next-hop 192.168.129.1#ip route-static 0.0.0.0 0.0.0.0 192.168.254.2ip route-static 10.0.0.0 255.255.255.0 192.168.30.253ip route-static 10.0.18.0 255.255.255.0 192.168.30.253ip route-static 10.0.24.0 255.255.255.0 192.168.30.253ip route-static 10.0.25.0 255.255.255.0 192.168.30.253ip route-static 10.0.29.0 255.255.255.0 192.168.30.253ip route-static 10.0.97.0 255.255.255.0 192.168.30.253ip route-static 10.10.0.0 255.255.0.0 192.168.30.253ip route-static 10.11.2.0 255.255.255.0 192.168.30.253ip route-static 10.11.30.0 255.255.255.0 192.168.30.253ip route-static 10.11.70.0 255.255.255.0 192.168.30.253ip route-static 10.11.72.0 255.255.255.0 192.168.30.253ip route-static 10.12.41.0 255.255.255.0 192.168.30.253ip route-static 10.100.1.0 255.255.255.0 192.168.30.253ip route-static 116.6.69.101 255.255.255.255 192.168.30.253ip route-static 172.16.1.0 255.255.255.0 61.144.43.216ip route-static 172.16.1.0 255.255.255.0 192.168.145.2ip route-static 192.168.0.0 255.255.255.0 192.168.30.253ip route-static 192.168.4.0 255.255.255.0 192.168.30.253ip route-static 192.168.5.0 255.255.255.0 192.168.30.253ip route-static 192.168.7.0 255.255.255.0 192.168.30.253ip route-static 192.168.8.0 255.255.255.0 192.168.30.253ip route-static 192.168.9.0 255.255.255.0 192.168.30.253ip route-static 192.168.19.0 255.255.255.0 192.168.30.253 ip route-static 192.168.21.0 255.255.255.0 192.168.30.253 ip route-static 192.168.22.0 255.255.255.0 192.168.30.253 ip route-static 192.168.23.0 255.255.255.0 192.168.30.253 ip route-static 192.168.24.0 255.255.255.0 192.168.30.253 ip route-static 192.168.26.0 255.255.255.0 192.168.30.253 ip route-static 192.168.28.0 255.255.255.0 192.168.30.253 ip route-static 192.168.29.0 255.255.255.0 192.168.30.253 ip route-static 192.168.41.0 255.255.255.0 192.168.30.253 ip route-static 192.168.46.0 255.255.255.0 192.168.30.253 ip route-static 192.168.68.0 255.255.255.0 192.168.30.253 ip route-static 192.168.76.0 255.255.255.0 192.168.30.253 ip route-static 192.168.82.0 255.255.255.0 192.168.30.253 ip route-static 192.168.84.0 255.255.255.0 192.168.30.253 ip route-static 192.168.86.0 255.255.255.0 192.168.30.253 ip route-static 192.168.88.0 255.255.255.0 192.168.30.253 ip route-static 192.168.91.0 255.255.255.0 192.168.30.253 ip route-static 192.168.96.0 255.255.255.0 192.168.30.253 ip route-static 192.168.103.0 255.255.255.0 192.168.30.253 ip route-static 192.168.202.0 255.255.255.0 192.168.30.253 ip route-static 192.168.253.0 255.255.255.0 192.168.253.1 ip route-static 192.168.254.4 255.255.255.252 192.168.254.2 #snmp-agent。
arp中毒防御措施一、配置静态ARP表静态ARP表是一种有效的防御ARP中毒的方法。
通过手动配置静态ARP表,可以确保计算机不会受到动态ARP更新的影响,从而避免了被恶意ARP数据包欺骗。
静态ARP表中的条目是固定的,不会受到网络中其他计算机发送的ARP请求的影响。
二、启用ARP防火墙ARP防火墙是一种用于防止ARP欺骗的软件工具。
它能够检测和拦截来自网络中的恶意ARP数据包,从而保护计算机不会受到ARP中毒的影响。
启用ARP防火墙可以有效地防御ARP攻击,并且可以定期更新防火墙规则以应对新的ARP攻击方式。
三、定期检查ARP缓存定期检查ARP缓存可以及时发现并清除恶意ARP条目。
通过定期检查ARP缓存,可以确保计算机不会受到已经过期的或错误的ARP条目的影响。
在大多数操作系统中,可以使用命令行工具或网络管理软件来检查和清除ARP缓存。
四、使用加密技术加密技术是一种保护数据传输安全的有效方法。
通过使用加密技术,可以确保在网络中传输的数据不会被窃取或篡改。
在局域网中,可以使用加密技术来保护数据传输,从而避免ARP攻击者截获和篡改数据包。
五、限制ARP流量限制ARP流量可以减少计算机受到ARP攻击的可能性。
通过配置网络设备或交换机来限制ARP流量,可以减少网络中恶意ARP数据包的数量。
限制ARP流量的方法包括使用访问控制列表(ACL)或配置交换机端口安全功能等。
六、及时更新系统和软件及时更新系统和软件可以避免受到已知的漏洞和恶意攻击的影响。
操作系统和软件供应商会定期发布安全更新和补丁程序,以修复已知漏洞。
及时安装这些更新和补丁程序可以保护计算机不受ARP攻击和其他网络攻击的影响。
七、监控网络流量监控网络流量可以及时发现和应对ARP攻击。
通过使用网络分析工具或交换机上的监控功能,可以实时监控网络中的ARP流量。
如果发现异常流量或恶意ARP数据包,可以及时采取措施进行清除和防御。
八、建立备份机制建立备份机制可以在ARP攻击造成严重后果时进行恢复和重建。