juniper SRX 利用虚拟路由器实现多链路冗余以及双向接入案例
- 格式:docx
- 大小:82.22 KB
- 文档页数:30
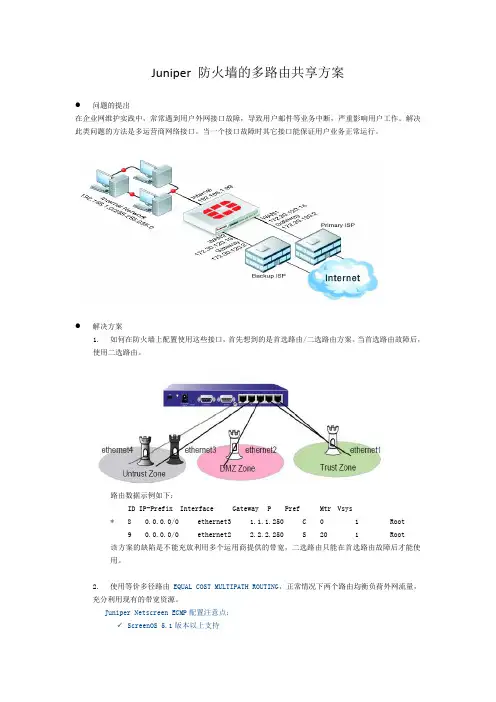
Juniper 防火墙的多路由共享方案●问题的提出在企业网维护实践中,常常遇到用户外网接口故障,导致用户邮件等业务中断,严重影响用户工作。
解决此类问题的方法是多运营商网络接口。
当一个接口故障时其它接口能保证用户业务正常运行。
●解决方案1.如何在防火墙上配置使用这些接口,首先想到的是首选路由/二选路由方案。
当首选路由故障后,使用二选路由。
路由数据示例如下:ID IP-Prefix Interface Gateway P Pref Mtr Vsys* 8 0.0.0.0/0 ethernet3 1.1.1.250 C 0 1 Root9 0.0.0.0/0 ethernet2 2.2.2.250 S 20 1 Root该方案的缺陷是不能充放利用多个运用商提供的带宽,二选路由只能在首选路由故障后才能使用。
2.使用等价多径路由EQUAL COST MULTIPATH ROUTING,正常情况下两个路由均衡负荷外网流量,充分利用现有的带宽资源。
Juniper Netscreen ECMP配置注意点:✓ScreenOS 5.1版本以上支持✓两条路由需具有相同的优先级和Metric值,两条路由的出接口需在同一安全区段。
✓配置的两条同一目标路由在路由表中有效(*号)。
✓启用ECMP功能路由数据示例如下:ID IP-Prefix Interface Gateway P Pref Mtr Vsys * 8 0.0.0.0/0 ethernet3 1.1.1.250 C 0 1 Root * 9 0.0.0.0/0 ethernet2 2.2.2.250 S 0 1 Root具体实施如下✓打开EQUAL COST MULTIPATH ROUTING功能✓设置静态路由的preference值为0(与连接路由的preference值相同)✓设置静态路由,保证两个共享的路由有相同的metricset route 0.0.0.0/0 interface ethernet3 gateway 1.1.1.250 metric 1set route 0.0.0.0/0 interface ethernet4 gateway 2.2.2.250 metric 1。
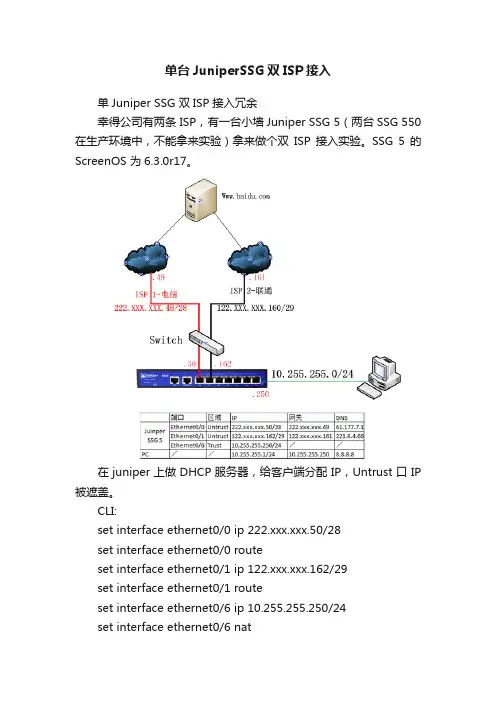
单台JuniperSSG双ISP接入单Juniper SSG 双ISP接入冗余幸得公司有两条 ISP,有一台小墙Juniper SSG 5(两台SSG 550在生产环境中,不能拿来实验)拿来做个双ISP接入实验。
SSG 5的ScreenOS 为6.3.0r17。
在juniper上做DHCP服务器,给客户端分配IP,Untrust口IP 被遮盖。
CLI:set interface ethernet0/0 ip 222.xxx.xxx.50/28set interface ethernet0/0 routeset interface ethernet0/1 ip 122.xxx.xxx.162/29set interface ethernet0/1 routeset interface ethernet0/6 ip 10.255.255.250/24set interface ethernet0/6 natset dns host dns1 61.177.7.1 src-interface ethernet0/0set dns host dns2 221.6.4.66 src-interface ethernet0/1set route 0.0.0.0/0 interface ethernet0/0 gateway 222.xxx.xxx.49(首选默认电信路由)set route 0.0.0.0/0 interface ethernet0/1 gateway 122.xxx.xxx.161 preference 30(备用默认联通路由,当电信外网出现故障时,此条路由起用)(因为环境中没有三层交换机,PC直连防火墙trust端口,所以不用设置回路路由)set address "Trust" "10.255.255.0" 10.255.255.0 255.255.255.0(设置trust区段的地址薄)set policy id 2 name "Permit Access" from "Trust" to "Untrust""10.255.255.0" "Any" "ANY" permit log(设置策略,允许内部网段10.255.255.0/24访问外网)WebUI:Network>Interface>List设置两个Untrust端口设置Trust端口,注意接口要是NAT 模式设置路由Network>Routing>Destination 默认电信路由设置完成后,如下:策略如下:以上基本设置完成后,设置Monitor,目的是当电信主线路出现故障后,在设定的时间内,路由自动转向备用联通线路。
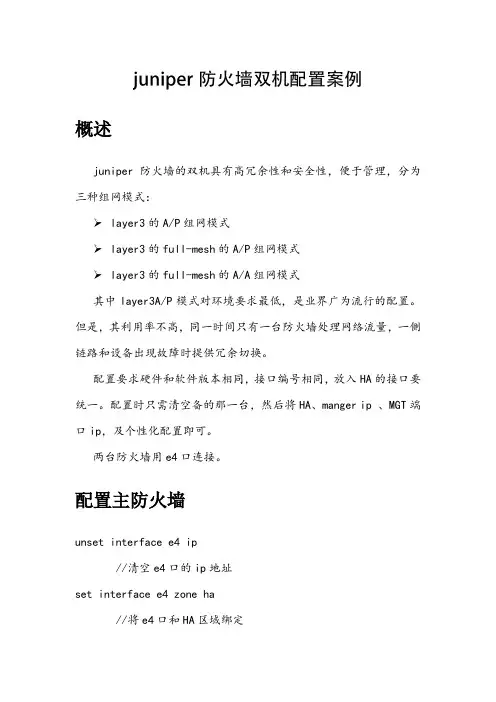
概述juniper防火墙的双机具有高冗余性和安全性,便于管理,分为三种组网模式:layer3的A/P组网模式layer3的full-mesh的A/P组网模式layer3的full-mesh的A/A组网模式其中layer3A/P模式对环境要求最低,是业界广为流行的配置。
但是,其利用率不高,同一时间只有一台防火墙处理网络流量,一侧链路和设备出现故障时提供冗余切换。
配置要求硬件和软件版本相同,接口编号相同,放入HA的接口要统一。
配置时只需清空备的那一台,然后将HA、manger ip 、MGT端口ip,及个性化配置即可。
两台防火墙用e4口连接。
配置主防火墙unset interface e4 ip//清空e4口的ip地址set interface e4 zone ha//将e4口和HA区域绑定//-----配置NSRP----set nsrp cluster id 1//设置cluster组号set nsrp vsd id 0//设置虚拟安全数据库的组号0set nsrp vsd-group id 0 priority 50//设置nsrp主设备的优先级(优先级数值越大,优先级越小)set nsrp rto syn//设置配置同步set nsrp vsd-group id 0 monitor interface ethernet3set nsrp vsd-group id 0 monitor interface ethernet1//设置防火墙监控的端口//只有当备份防火墙配置之后,主设备上才能检测到备防火墙的状态(get nsrp)set nsrp vsd-group hb-interval 200//设置心跳信息每隔200秒发送问候信息set nsrp vsd-group hb-threshold 3//设置心跳信息总共发出3次问候信息save//保存配置备防火墙unset all//恢复出厂设置set interface e4 zone ha//将e4和ha区域绑定set nsrp cluster id 1//设置cluster组号set nsrp vsd id 0//设置vsd组号set nsrp vsd-group id 0 priority 100//设置nsrp主设备的优先级(优先级数值越大,优先级越小)set nsrp rto syn//设置配置同步set nsrp vsd-group id 0 monitor interface ethernet3set nsrp vsd-group id 0 monitor interface ethernet1//设置防火墙监控的端口set nsrp vsd-group hb-interval 200//设置心跳信息每隔200秒发送问候信息set nsrp vsd-group hb-threshold 3//设置心跳信息总共发出3次问候信息save //保存同步配置在备机上操作exec nsrp sync global-config check-sum//将两台设备的配置进行校检,如有不同,备份的设备将会在重启后把主设备上的配置导入备份主机中exec nsrp sync global-config save//如有不同,备份的设备将会在重启后把主设备上的配置导入备份主机中。
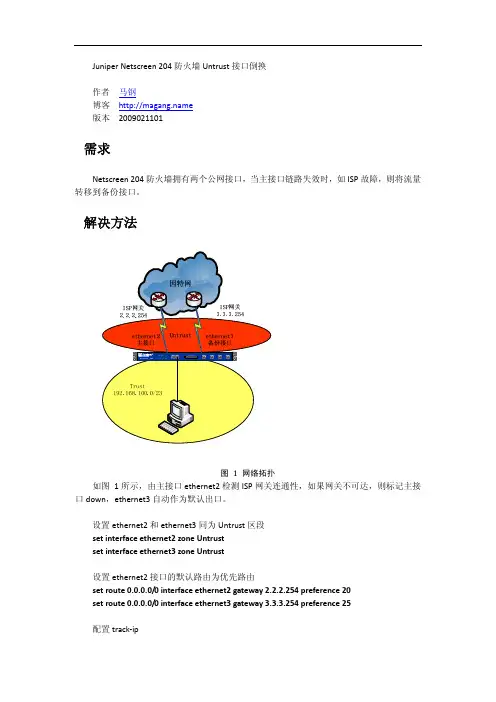
Juniper Netscreen 204防火墙Untrust接口倒换作者 马钢博客 版本 2009021101需求Netscreen 204防火墙拥有两个公网接口,当主接口链路失效时,如ISP故障,则将流量转移到备份接口。
解决方法图 1 网络拓扑如图 1所示,由主接口ethernet2检测ISP网关连通性,如果网关不可达,则标记主接口down,ethernet3自动作为默认出口。
设置ethernet2和ethernet3同为Untrust区段set interface ethernet2 zone Untrustset interface ethernet3 zone Untrust设置ethernet2接口的默认路由为优先路由set route 0.0.0.0/0 interface ethernet2 gateway 2.2.2.254 preference 20set route 0.0.0.0/0 interface ethernet3 gateway 3.3.3.254 preference 25配置track‐ipset interface ethernet2 monitor track‐ip ipset interface ethernet2 monitor track‐ip ip 2.2.2.254set interface ethernet2 track‐ip ip 2.2.2.254 interval 1set interface ethernet2 track‐ip ip 2.2.2.254 threshold 2set interface ethernet2 track‐ip ip 2.2.2.254 weight 10set interface ethernet2 track‐ip threshold 8set interface ethernet2 track‐ip weight 12set interface ethernet2 monitor threshold 5unset interface ethernet3 monitor track‐ip dynamic完成上述设置后,防火墙将在ethernet2启用IP跟踪。

Juniper SRX防火墙简明配置手册SRX系列防火墙是Juniper公司基于JUNOS操作系统的安全系列产品,JUNOS集成了路由、交换、安全性和一系列丰富的网络服务。
目前Juniper公司的全系列路由器产品、交换机产品和SRX安全产品均采用统一源代码的JUNOS操作系统,JUNOS是全球首款将转发与控制功能相隔离,并采用模块化软件架构的网络操作系统。
JUNOS作为电信级产品的精髓是Juniper 真正成功的基石,它让企业级产品同样具有电信级的不间断运营特性,更好的安全性和管理特性,JUNOS软件创新的分布式架构为高性能、高可用、高可扩展的网络奠定了基础。
基于NP架构的SRX系列产品产品同时提供性能优异的防火墙、NAT、IPSEC、IPS、SSL VPN和UTM 等全系列安全功能,其安全功能主要来源于已被广泛证明的ScreenOS操作系统。
本文旨在为熟悉Netscreen防火墙ScreenOS操作系统的工程师提供SRX防火墙参考配置,以便于大家能够快速部署和维护SRX防火墙,文档介绍JUNOS操作系统,并参考ScreenOS配置介绍SRX防火墙配置方法,最后对SRX防火墙常规操作与维护做简要说明。
一、JUNOS操作系统介绍1.1 层次化配置结构JUNOS采用基于FreeBSD内核的软件模块化操作系统,支持CLI命令行和WEBUI两种接口配置方式,本文主要对CLI命令行方式进行配置说明。
JUNOS CLI使用层次化配置结构,分为操作(operational)和配置(configure)两类模式,在操作模式下可对当前配置、设备运行状态、路由及会话表等状态进行查看及设备运维操作,并通过执行config或edit命令进入配置模式,在配置模式下可对各相关模块进行配置并能够执行操作模式下的所有命令(run)。
在配置模式下JUNOS采用分层分级模块下配置结构,如下图所示,edit命令进入下一级配置(类似unix cd命令),exit命令退回上一级,top命令回到根级。
Juniper SRX防火墙简明配置手册目录一、JUNOS操作系统介绍 (3)1.1 层次化配置结构 (3)1.2 JunOS配置管理 (4)1.3 SRX主要配置内容 (4)二、SRX防火墙配置说明 (5)2.1 初始安装 (5)2.1.1 登陆 (5)2.1.2 设置root用户口令 (9)2.1.3 JSRP初始化配置 (9)2.1.4 设置远程登陆管理用户 (14)2.1.5 远程管理SRX相关配置 (15)2.1.6 ZONE及相关接口的配置 (15)2.2 Policy (16)2.3 NAT (17)2.3.1 Interface based NAT (18)2.3.2 Pool based Source NAT (18)2.3.3 Pool base destination NAT (19)2.3.4 Pool base Static NAT (20)2.4 IPSEC VPN (21)2.5 Application and ALG (22)三、SRX防火墙常规操作与维护 (22)3.1 单机设备关机 (22)3.2单机设备重启 (23)3.3单机操作系统升级 (23)3.4双机模式下主备SRX关机 (23)3.5双机模式下主备设备重启 (24)3.6双机模式下操作系统升级 (24)3.7双机转发平面主备切换及切换后恢复 (25)3.8双机控制平面主备切换及切换后恢复 (25)3.9双机模式下更换备SRX (25)3.10双机模式下更换主SRX (26)3.11双机模式更换电源 (27)3.12双机模式更换故障板卡 (27)3.13配置备份及还原方法 (27)3.14密码修改方法 (28)3.15磁盘文件清理方法 (28)3.16密码恢复 (28)3.17常用监控维护命令 (29)四、SRX防火墙介绍 (31)Juniper SRX防火墙简明配置手册SRX系列防火墙是Juniper公司基于JUNOS操作系统的安全系列产品,JUNOS集成了路由、交换、安全性和一系列丰富的网络服务。
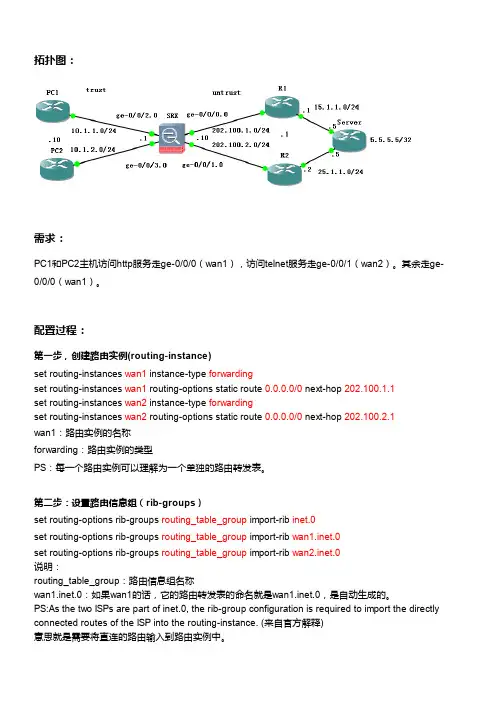
拓扑图:需求:PC1和PC2主机访问http服务走ge-0/0/0(wan1),访问telnet服务走ge-0/0/1(wan2)。
其余走ge-0/0/0(wan1)。
配置过程:第一步,创建路由实例(routing-instance)set routing-instances wan1 instance-type forwardingset routing-instances wan1 routing-options static route 0.0.0.0/0 next-hop 202.100.1.1set routing-instances wan2 instance-type forwardingset routing-instances wan2 routing-options static route 0.0.0.0/0 next-hop 202.100.2.1wan1:路由实例的名称forwarding:路由实例的类型PS:每一个路由实例可以理解为一个单独的路由转发表。
第二步:设置路由信息组(rib-groups)set routing-options rib-groups routing_table_group import-rib inet.0set routing-options rib-groups routing_table_group import-rib wan1.inet.0set routing-options rib-groups routing_table_group import-rib wan2.inet.0说明:routing_table_group:路由信息组名称wan1.inet.0:如果wan1的话,它的路由转发表的命名就是wan1.inet.0,是自动生成的。
PS:As the two ISPs are part of inet.0, the rib-group configuration is required to import the directly connected routes of the ISP into the routing-instance. (来自官方解释)意思就是需要将直连的路由输入到路由实例中。
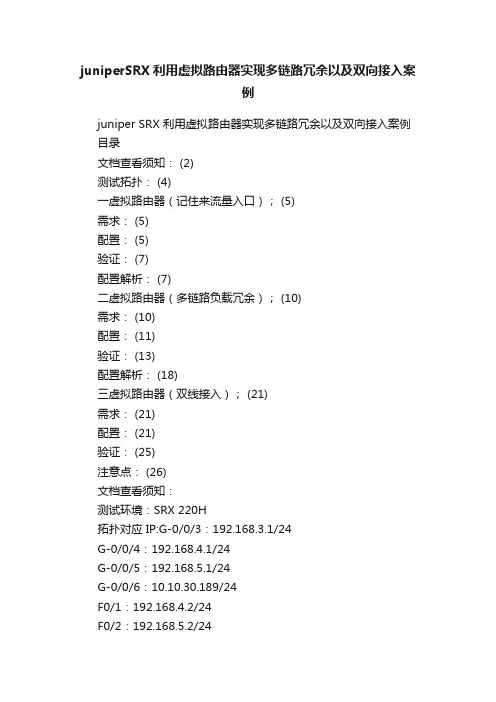
juniperSRX利用虚拟路由器实现多链路冗余以及双向接入案例juniper SRX 利用虚拟路由器实现多链路冗余以及双向接入案例目录文档查看须知: (2)测试拓扑: (4)一虚拟路由器(记住来流量入口); (5)需求: (5)配置: (5)验证: (7)配置解析: (7)二虚拟路由器(多链路负载冗余); (10)需求: (10)配置: (11)验证: (13)配置解析: (18)三虚拟路由器(双线接入); (21)需求: (21)配置: (21)验证: (25)注意点: (26)文档查看须知:测试环境:SRX 220H拓扑对应 IP:G-0/0/3:192.168.3.1/24G-0/0/4:192.168.4.1/24G-0/0/5:192.168.5.1/24G-0/0/6:10.10.30.189/24F0/1:192.168.4.2/24F0/2:192.168.5.2/24F0/3:192.168.100.1/24(模拟遥远互联网)测试拓扑:一虚拟路由器(记住来流量入口);需求:外网用户访问防火墙的外网接口3389 端口NAT 到内网服务器192.168.3.5:3389,流量按原路返回;放行所有外网用户到主机 192.168.3.5 的 3389 端口;(双线接入)配置:set routing-instances Tel instance-type virtual-routerset routing-instances Tel interface ge-0/0/4.0set routing-instances Tel routing-options interface-routes rib-group inet Big-ribset routing-instances Tel routing-options static route 0.0.0.0/0 next-hop 192.168.4.2set routing-instances CNC instance-type virtual-routerset routing-instances CNC interface ge-0/0/5.0set routing-instances CNC routing-options interface-routes rib-group inet Big-ribset routing-instances CNC routing-options static route 0.0.0.0/0 next-hop 192.168.5.2set interfaces ge-0/0/3 unit 0 family inet address 192.168.3.1/24set interfaces ge-0/0/4 unit 0 family inet address 192.168.4.1/24set interfaces ge-0/0/5 unit 0 family inet address 192.168.5.1/24set interfaces ge-0/0/6 unit 0 family inet address 10.10.30.189/24set routing-options interface-routes rib-group inet Big-rib set routing-options static route 10.0.0.0/8 next-hop 10.10.30.1set routing-options static route 0.0.0.0/0 next-hop 192.168.4.2set routing-options static route 0.0.0.0/0 installset routing-options static route 0.0.0.0/0 no-readvertiseset routing-options rib-groups Big-rib import-rib inet.0set routing-options rib-groups Big-rib import-rib CNC.inet.0 set routing-options rib-groups Big-rib import-rib Tel.inet.0 set security nat destination pool 111 address 192.168.3.5/32 set security nat destination rule-set 1 from zone Tel-trustset security nat destination rule-set 1 rule 111 match source-address 0.0.0.0/0set security nat destination rule-set 1 rule 111 match destination-address 192.168.4.1/32set security nat destination rule-set 1 rule 111 match destination-port 3389set security nat destination rule-set 1 rule 111 then destination-nat pool 111set security nat destination rule-set 2 from zone CNC-trust set security nat destination rule-set 2 rule 222 match source-address 0.0.0.0/0set security nat destination rule-set 2 rule 222 match destination-address 192.168.5.1/32set security nat destination rule-set 1 rule 111 match destination-port 3389set security nat destination rule-set 2 rule 222 then destination-nat pool 111set applications application tcp_3389 protocol tcpset applications application tcp_3389 destination-port 3389 set security zones security-zone trust address-book address H_192.168.3.5 192.168.3.5/32set security policies from-zone Tel-trust to-zone trust policy default-permit match source-address anyset security policies from-zone Tel-trust to-zone trust policy default-permit match destination-address H_192.168.3.5 set security policies from-zone Tel-trust to-zone trust policy default-permit match application tcp_3389set security policies from-zone Tel-trust to-zone trust policy default-permit then permitset security policies from-zone CNC-trust to-zone trust policy default-permit match source-address anyset security policies from-zone CNC-trust to-zone trust policy default-permit match destination-addressH_192.168.3.5set security policies from-zone CNC-trust to-zone trust policy default-permit match application tcp_3389set security policies from-zone CNC-trust to-zone trust policy default-permit then permitset security zones security-zone trust host-inbound-traffic system-services allset security zones security-zone trust host-inbound-traffic protocols allset security zones security-zone trust interfaces ge-0/0/3.0 set security zones security-zone T el-trust host-inbound-traffic system-services allset security zones security-zone T el-trust host-inbound-traffic protocols allset security zones security-zone T el-trust interfaces ge-0/0/4.0set security zones security-zone CNC-trust host-inbound-traffic system-services allset security zones security-zone CNC-trust host-inbound-traffic protocols allset security zones security-zone CNC-trust interfaces ge-0/0/5.0set security zones security-zone MGT host-inbound-traffic system-services allset security zones security-zone MGT host-inbound-traffic protocols allset security zones security-zone MGT interfaces ge-0/0/6.0 验证:root@SRX-Ipsec-A> show security flow sessionSession ID: 9696, Policy name: default-permit/5, Timeout: 1794, ValidIn: 192.168.100.211/57408 --> 192.168.5.1/3389;tcp, If: ge-0/0/5.0, Pkts: 2, Bytes: 112Out: 192.168.3.5/3389 --> 192.168.100.211/57408;tcp, If: ge-0/0/3.0, Pkts: 1, Bytes: 60====================================== ===================================== = root@SRX-Ipsec-A> show security flow sessionSession ID: 9697, Policy name: default-permit/4, Timeout: 1796, ValidIn: 192.168.100.211/57409 --> 192.168.4.1/3389;tcp, If: ge-0/0/4.0, Pkts: 2, Bytes: 112Out: 192.168.3.5/3389 --> 192.168.100.211/57409;tcp, If: ge-0/0/3.0, Pkts: 1, Bytes: 60配置解析:set routing-instances Tel instance-type virtual-router//创建虚拟 VR Telset routing-instances Tel interface ge-0/0/4.0//把逻辑接口加入虚拟 VRset routing-instances Tel routing-options interface-routes rib-group inet Big-rib//定义新增的路由表属于路由组“Big-rib”set routing-instances Tel routing-options static route 0.0.0.0/0 next-hop 192.168.4.2 //为 Tel 路由表配置路由set routing-instances CNC instance-type virtual-routerset routing-instances CNC interface ge-0/0/5.0set routing-instances CNC routing-options interface-routes rib-group inet Big-rib set routing-instances CNC routing-options static route 0.0.0.0/0 next-hop 192.168.5.2 //配置路由表 CNC 相关信息set interfaces ge-0/0/3 unit 0 family inet address 192.168.3.1/24set interfaces ge-0/0/4 unit 0 family inet address 192.168.4.1/24set interfaces ge-0/0/5 unit 0 family inet address192.168.5.1/24set interfaces ge-0/0/6 unit 0 family inet address 10.10.30.189/24//配置逻辑接口的 IP 地址set routing-options interface-routes rib-group inet Big-rib //定义路由表组,并把接口路由加入到 Big-rib 路由组中set routing-options static route 10.0.0.0/8 next-hop 10.10.30.1set routing-options static route 0.0.0.0/0 next-hop 192.168.4.2//配置全局路由表路由信息set routing-options static route 0.0.0.0/0 install//把路由表安装到转发表set routing-options static route 0.0.0.0/0 no-readvertise//set routing-options rib-groups Big-rib import-rib inet.0set routing-options rib-groups Big-rib import-rib CNC.inet.0 set routing-options rib-groups Big-rib import-rib Tel.inet.0 //导入三张路由表之间的直连路由到路由表组set security nat destination pool 111 address 192.168.3.5/32 //定义目的 NAT 后的内部服务器的 IP 地址set security nat destination rule-set 1 from zone Tel-trustset security nat destination rule-set 1 rule 111 match source-address 0.0.0.0/0set security nat destination rule-set 1 rule 111 match destination-address 192.168.4.1/32set security nat destination rule-set 1 rule 111 match destination-port 3389set security nat destination rule-set 1 rule 111 then destination-nat pool 111//配置 ZONE Tel-trust 的目的NATset security nat destination rule-set 2 from zone CNC-trust set security nat destination rule-set 2 rule 222 match source-address 0.0.0.0/0set security nat destination rule-set 2 rule 222 match destination-address 192.168.5.1/32set security nat destination rule-set 1 rule 111 match destination-port 3389set security nat destination rule-set 2 rule 222 then destination-nat pool 111//配置 ZONE CNC-trust 的目的NATset applications application tcp_3389 protocol tcpset applications application tcp_3389 destination-port 3389 set security zones security-zone trust address-book address H_192.168.3.5 192.168.3.5/32//自定义端口和配置地址表set security policies from-zone Tel-trust to-zone trust policy default-permit match source-address anyset security policies from-zone Tel-trust to-zone trust policy default-permit match destination-address H_192.168.3.5 set security policies from-zone Tel-trust to-zone trust policy default-permit match application tcp_3389set security policies from-zone Tel-trust to-zone trust policy default-permit then permit//配置 Tel-trust 到 trust 策略set security policies from-zone CNC-trust to-zone trust policy default-permit match source-address anyset security policies from-zone CNC-trust to-zone trust policy default-permit match destination-addressH_192.168.3.5set security policies from-zone CNC-trust to-zone trust policy default-permit match application tcp_3389set security policies from-zone CNC-trust to-zone trust policy default-permit then permit//配置 CNC-trust 到 trust 策略set security zones security-zone trust host-inbound-traffic system-services allset security zones security-zone trust host-inbound-traffic protocols allset security zones security-zone trust interfaces ge-0/0/3.0set security zones security-zone T el-trust host-inbound-traffic system-services all set security zones security-zone Tel-trust host-inbound-traffic protocols allset security zones security-zone T el-trust interfaces ge-0/0/4.0set security zones security-zone CNC-trust host-inbound-traffic system-services all set security zones security-zone CNC-trust host-inbound-traffic protocols allset security zones security-zone CNC-trust interfaces ge-0/0/5.0set security zones security-zone MGT host-inbound-traffic system-services allset security zones security-zone MGT host-inbound-traffic protocols allset security zones security-zone MGT interfaces ge-0/0/6.0//定义逻辑接口到ZONE,并开放所有的协议及服务来访问防火墙的直连接口二虚拟路由器(多链路负载冗余);需求:内网用户访问端口22.3389.8080,走电信,其他所有流量走CNC;所有内网访问外网的流量NAT 为对应外网接口IP 地址;实现负载冗余的功能;放行所有服务;(双线接入)配置:set routing-instances Tel instance-type virtual-routerset routing-instances Tel interface ge-0/0/4.0set routing-instances Tel routing-options interface-routes rib-group inet Big-ribset routing-instances Tel routing-options static route 0.0.0.0/0 next-hop 192.168.4.2set routing-instances Tel routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.5.2 preference 100 set routing-instances CNC instance-type virtual-routerset routing-instances CNC interface ge-0/0/5.0set routing-instances CNC routing-options interface-routes rib-group inet Big-ribset routing-instances CNC routing-options static route 0.0.0.0/0 next-hop 192.168.5.2set routing-instances CNC routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.4.2 preference 100 set interfaces ge-0/0/3 unit 0 family inet address 192.168.3.1/24 set interfaces ge-0/0/4 unit 0 family inet address 192.168.4.1/24set interfaces ge-0/0/5 unit 0 family inet address 192.168.5.1/24set interfaces ge-0/0/6 unit 0 family inet address 10.10.30.189/24set routing-options interface-routes rib-group inet Big-rib set routing-options static route 10.0.0.0/8 next-hop10.10.30.1set routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.5.2 preference 100set routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.4.2 preference 10set routing-options static route 0.0.0.0/0 installset routing-options static route 0.0.0.0/0 no-readvertiseset routing-options rib-groups Big-rib import-rib inet.0set routing-options rib-groups Big-rib import-rib CNC.inet.0 set routing-options rib-groups Big-rib import-rib Tel.inet.0 set security nat source rule-set Soure-NAT-Policy from zone trustset security nat source rule-set Soure-NAT-Policy to zone Tel-trustset security nat source rule-set Soure-NAT-Policy rule Source-nat-1 match source-address 192.168.3.0/24set security nat source rule-set Soure-NAT-Policy rule Source-nat-1 match destination-address 0.0.0.0/0 set security nat source rule-set Soure-NAT-Policy rule Source-nat-1 then source-nat interfaceset security zones security-zone trust address-book address Net_192.168.3.0 192.168.3.0/24set security policies from-zone trust to-zone Tel-trust policy 1 match source-address N et_192.168.3.0set security policies from-zone trust to-zone Tel-trust policy 1 match destination-address anyset security policies from-zone trust to-zone Tel-trust policy 1 match application anyset security policies from-zone trust to-zone Tel-trust policy 1 then permitset security policies from-zone trust to-zone Tel-trust policy 1 then log session-initset security policies from-zone trust to-zone Tel-trust policy 1 then log session-closeset security nat source rule-set Soure-NAT-Policy-2 from zone trustset security nat source rule-set Soure-NAT-Policy-2 to zone CNC-trustset security nat source rule-set Soure-NAT-Policy-2 rule Source-nat-2 match source-address 192.168.3.0/24 set security nat source rule-set Soure-NAT-Policy-2 rule Source-nat-2 match destination-address 0.0.0.0/0 set security nat source rule-set Soure-NAT-Policy-2 rule Source-nat-2 then source-nat interface set security policies from-zone trust to-zone CNC-trust policy 2 match source-address Net_192.168.3.0set security policies from-zone trust to-zone CNC-trust policy 2 match destination-address anyset security policies from-zone trust to-zone CNC-trust policy 2 match application anyset security policies from-zone trust to-zone CNC-trust policy 2 then permitset security policies from-zone trust to-zone CNC-trust policy 2 then log session-initset security policies from-zone trust to-zone CNC-trust policy 2 then log session-closeset interfaces ge-0/0/3 unit 0 family inet filter input filter-1 set firewall filter filter-1 term term-1 from destination-port 22set firewall filter filter-1 term term-1 from destination-port 3389set firewall filter filter-1 term term-1 from destination-port 8080set firewall filter filter-1 term term-1 then routing-instance Telset firewall filter filter-1 term default then routing-instance CNCset security zones security-zone trust host-inbound-traffic system-services allset security zones security-zone trust host-inbound-traffic protocols allset security zones security-zone trust interfaces ge-0/0/3.0 set security zones security-zone T el-trust host-inbound-traffic system-services allset security zones security-zone T el-trust host-inbound-traffic protocols allset security zones security-zone T el-trust interfaces ge-0/0/4.0set security zones security-zone CNC-trust host-inbound-traffic system-services allset security zones security-zone CNC-trust host-inbound-traffic protocols allset security zones security-zone CNC-trust interfaces ge-0/0/5.0set security zones security-zone MGT host-inbound-traffic system-services allset security zones security-zone MGT host-inbound-traffic protocols allset security zones security-zone MGT interfaces ge-0/0/6.0 验证:基于目标端口路由验证:Session ID: 9693, Policy name: 1121/6, Timeout: 1790, Valid In: 192.168.3.5/52562 --> 192.168.100.211/3389;tcp, If: ge-0/0/3.0, Pkts: 2, Bytes: 112 Out: 192.168.100.211/3389 --> 192.168.4.1/28262;tcp, If: ge-0/0/4.0, Pkts: 1, Bytes: 60 Session ID: 9703, Policy name: 1121/7, Timeout: 2, ValidIn: 192.168.3.5/6252 --> 192.168.100.211/1;icmp, If: ge-0/0/3.0, Pkts: 1, Bytes: 60 Out: 192.168.100.211/1 --> 192.168.5.1/4217;icmp, If: ge-0/0/5.0, Pkts: 1, Bytes: 60 当前路由表:root@SRX-Ipsec-A> show routeinet.0: 7 destinations, 8 routes (7 active, 0 holddown, 0 hidden)+ = Active Route, - = Last Active, * = Both0.0.0.0/0 *[Static/10] 00:01:26> to 192.168.4.2 via ge-0/0/4.0[Static/100] 00:01:04> to 192.168.5.2 via ge-0/0/5.0192.168.3.0/24 *[Direct/0] 00:04:31> via ge-0/0/3.0192.168.3.1/32 *[Local/0] 16:44:09Local via ge-0/0/3.0192.168.4.0/24 *[Direct/0] 00:01:26> via ge-0/0/4.0192.168.4.1/32 *[Local/0] 00:01:26Local via ge-0/0/4.0192.168.5.0/24 *[Direct/0] 00:01:04> via ge-0/0/5.0192.168.5.1/32 *[Local/0] 00:01:04Local via ge-0/0/5.0CNC.inet.0: 7 destinations, 8 routes (7 active, 0 holddown, 0hidden) + = Active Route, - = Last Active, * = Both0.0.0.0/0 *[Static/5] 00:01:04> to 192.168.5.2 via ge-0/0/5.0[Static/100] 00:01:26> to 192.168.4.2 via ge-0/0/4.0192.168.3.0/24 *[Direct/0] 00:04:31> via ge-0/0/3.0192.168.3.1/32 *[Local/0] 00:04:31Local via ge-0/0/3.0192.168.4.0/24 *[Direct/0] 00:01:26> via ge-0/0/4.0192.168.4.1/32 *[Local/0] 00:01:26Local via ge-0/0/4.0192.168.5.0/24 *[Direct/0] 00:01:04> via ge-0/0/5.0192.168.5.1/32 *[Local/0] 16:44:09Local via ge-0/0/5.0Tel.inet.0: 7 destinations, 8 routes (7 active, 0 holddown, 0 hidden) + = Active Route, - = Last Active, * = Both0.0.0.0/0 *[Static/5] 00:01:26> to 192.168.4.2 via ge-0/0/4.0[Static/100] 00:01:04> to 192.168.5.2 via ge-0/0/5.0192.168.3.0/24 *[Direct/0] 00:04:31> via ge-0/0/3.0192.168.3.1/32 *[Local/0] 00:04:31Local via ge-0/0/3.0192.168.4.0/24 *[Direct/0] 00:01:26> via ge-0/0/4.0192.168.4.1/32 *[Local/0] 16:44:09192.168.5.0/24 *[Direct/0] 00:01:04> via ge-0/0/5.0192.168.5.1/32 *[Local/0] 00:01:04Local via ge-0/0/5.0双线冗余验证:root@SRX-Ipsec-A> show security flow sessionSession ID: 10321, Policy name: 1121/7, Timeout: 48, ValidIn: 192.168.3.2/188 --> 192.168.100.211/59209;icmp, If: ge-0/0/3.0, Pkts: 1, Bytes: 84 Out: 192.168.100.211/59209 --> 192.168.5.1/13586;icmp, If: ge-0/0/5.0, Pkts: 0, Bytes: 0 Session ID: 10322, Policy name: 1121/6, Timeout: 50, Valid手动拔掉 CNC 广域网线路(模拟 CNC 线路故障)In: 192.168.3.2/189 --> 192.168.100.211/59209;icmp, If: ge-0/0/3.0, Pkts: 1, Bytes: 84 Out: 192.168.100.211/59209 --> 192.168.4.1/19350;icmp, If: ge-0/0/4.0, Pkts: 0, Bytes: 0 Session ID: 10330, Policy name: 1121/6, Timeout: 2, ValidIn: 192.168.3.2/197 --> 192.168.100.211/59209;icmp, If: ge-0/0/3.0, Pkts: 1, Bytes: 84 Out: 192.168.100.211/59209 --> 192.168.4.1/3661;icmp, If: ge-0/0/4.0, Pkts: 1, Bytes: 84 当前路由表:root@SRX-Ipsec-A> show routeinet.0: 6 destinations, 6 routes (6 active, 0 holddown, 0 hidden)+ = Active Route, - = Last Active, * = Both0.0.0.0/0 *[Static/10] 00:00:45> to 192.168.4.2 via ge-0/0/4.0192.168.3.0/24 *[Direct/0] 00:06:27> via ge-0/0/3.0192.168.3.1/32 *[Local/0] 16:46:05192.168.4.0/24 *[Direct/0] 00:00:45> via ge-0/0/4.0192.168.4.1/32 *[Local/0] 00:00:45Local via ge-0/0/4.0192.168.5.1/32 *[Local/0] 00:00:37RejectCNC.inet.0: 6 destinations, 6 routes (6 active, 0 holddown, 0 hidden)+ = Active Route, - = Last Active, * = Both0.0.0.0/0 *[Static/100] 00:00:45> to 192.168.4.2 via ge-0/0/4.0192.168.3.0/24 *[Direct/0] 00:06:27> via ge-0/0/3.0192.168.3.1/32 *[Local/0] 00:06:27Local via ge-0/0/3.0192.168.4.0/24 *[Direct/0] 00:00:45> via ge-0/0/4.0192.168.4.1/32 *[Local/0] 00:00:45Local via ge-0/0/4.0192.168.5.1/32 *[Local/0] 16:46:05RejectTel.inet.0: 6 destinations, 6 routes (6 active, 0 holddown, 0 hidden) + = Active Route, - = Last Active, * = Both0.0.0.0/0 *[Static/5] 00:00:45> to 192.168.4.2 via ge-0/0/4.0192.168.3.0/24 *[Direct/0] 00:06:27> via ge-0/0/3.0192.168.3.1/32 *[Local/0] 00:06:27Local via ge-0/0/3.0192.168.4.0/24 *[Direct/0] 00:00:45> via ge-0/0/4.0192.168.4.1/32 *[Local/0] 16:46:05Local via ge-0/0/4.0192.168.5.1/32 *[Local/0] 00:00:37Reject配置解析:set routing-instances Tel instance-type virtual-routerset routing-instances Tel interface ge-0/0/4.0set routing-instances Tel routing-options interface-routes rib-group inet Big-ribset routing-instances Tel routing-options static route 0.0.0.0/0 next-hop 192.168.4.2set routing-instances CNC routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.5.2 preference 100 //配置Tel 路由表并配置相关信息,通过优先级来实现双广域网冗余,优先级值越小,优先级越高set routing-instances CNC instance-type virtual-routerset routing-instances CNC interface ge-0/0/5.0set routing-instances CNC routing-options interface-routes rib-group inet Big-ribset routing-instances CNC routing-options static route 0.0.0.0/0 next-hop 192.168.5.2set routing-instances CNC routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.4.2 preference 100 //配置CNC 路由表并配置相关信息set interfaces ge-0/0/3 unit 0 family inet address 192.168.3.1/24set interfaces ge-0/0/4 unit 0 family inet address 192.168.4.1/24set interfaces ge-0/0/5 unit 0 family inet address 192.168.5.1/24set interfaces ge-0/0/6 unit 0 family inet address 10.10.30.189/24//配置逻辑接口对应 IP 地址set routing-options interface-routes rib-group inet Big-rib //定义路由表组,并把接口路由加入到 Big-rib 路由组中set routing-options static route 10.0.0.0/8 next-hop 10.10.30.1set routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.5.2 preference 100set routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.4.2 preference 10//配置全局路由表路由信息,通过指定优先级来实现双广域网的冗余set routing-options static route 0.0.0.0/0 install//把路由表安装到转发表set routing-options static route 0.0.0.0/0 no-readvertise//set routing-options rib-groups Big-rib import-rib inet.0set routing-options rib-groups Big-rib import-rib CNC.inet.0 set routing-options rib-groups Big-rib import-rib Tel.inet.0 //导入三张路由表之间的直连路由到路由表组set security nat source rule-set Soure-NAT-Policy from zone trustset security nat source rule-set Soure-NAT-Policy to zone Tel-trustset security nat source rule-set Soure-NAT-Policy rule Source-nat-1 match source-address 192.168.3.0/24 set security nat source rule-set Soure-NAT-Policy rule Source-nat-1 matchdestination-address 0.0.0.0/0 set security nat source rule-set Soure-NAT-Policy rule Source-nat-1 then source-nat interface //配置 ZONE Tel-trust 基于接口的源NATset security zones security-zone trust address-book address Net_192.168.3.0 192.168.3.0/24//定义地址表set security policies from-zone trust to-zone Tel-trust policy 1 match source-address N et_192.168.3.0set security policies from-zone trust to-zone Tel-trust policy 1 match destination-address anyset security policies from-zone trust to-zone Tel-trust policy 1 match application anyset security policies from-zone trust to-zone Tel-trust policy 1 then permitset security policies from-zone trust to-zone Tel-trust policy 1 then log session-initset security policies from-zone trust to-zone Tel-trust policy 1 then log session-close//根据需求配置策略并记录 LOG 信息set security nat source rule-set Soure-NAT-Policy-2 from zone trustset security nat source rule-set Soure-NAT-Policy-2 to zone CNC-trustset security nat source rule-set Soure-NAT-Policy-2 rule Source-nat-2 match source-address 192.168.3.0/24 set security nat source rule-set Soure-NAT-Policy-2 rule Source-nat-2 match destination-address 0.0.0.0/0 set security nat source rule-set Soure-NAT-Policy-2 rule Source-nat-2 then source-nat interface //配置 ZONE CNC-trust 基于接口的源NATset security policies from-zone trust to-zone CNC-trustpolicy 2 match source-address Net_192.168.3.0set security policies from-zone trust to-zone CNC-trust policy 2 match destination-address any。
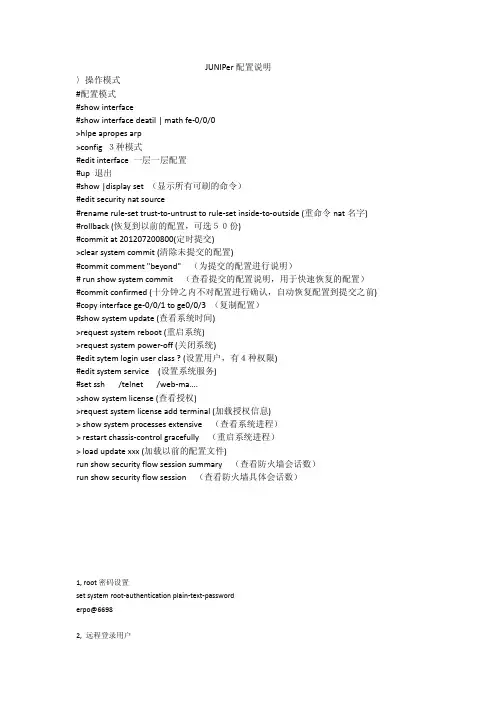
JUNIPer配置说明〉操作模式#配置模式#show interface#show interface deatil | math fe‐0/0/0>hlpe apropes arp>config 3种模式#edit interface 一层一层配置#up 退出#show |display set (显示所有可刷的命令)#edit security nat source#rename rule‐set trust‐to‐untrust to rule‐set inside‐to‐outside (重命令nat名字) #rollback (恢复到以前的配置,可选50份)#commit at 201207200800(定时提交)>clear system commit (清除未提交的配置)#commit comment "beyond"(为提交的配置进行说明)# run show system commit(查看提交的配置说明,用于快速恢复的配置) #commit confirmed (十分钟之内不对配置进行确认,自动恢复配置到提交之前) #copy interface ge‐0/0/1 to ge0/0/3 (复制配置)#show system update (查看系统时间)>request system reboot (重启系统)>request system power‐off (关闭系统)#edit sytem login user class ? (设置用户,有4种权限)#edit system service (设置系统服务)#set ssh /telnet /web‐ma….>show system license (查看授权)>request system license add terminal (加载授权信息)> show system processes extensive(查看系统进程)> restart chassis‐control gracefully(重启系统进程)> load update xxx (加载以前的配置文件)run show security flow session summary(查看防火墙会话数)run show security flow session(查看防火墙具体会话数)1, root密码设置set system root‐authentication plain‐text‐passworderpo@66982, 远程登录用户set system login user erpo class super‐user authentication plain‐text‐passworderpo66983,设置时间run set date 2012070919084,设置时区为上海set system time‐zone Asia/shanghai5,设置主机名set system host‐name FW6,设置NDS服和器Set system name‐server 208.67.222.222; 208.67.220.220;7,端口交换机属性设置root@ex2200# edit vlans test #新建vlan名称为testroot@ex2200# set vlan-id 10 #设置vlan idroot@ex2200# set description “Test VLAN” #设置vlan描述root@ex2200# set mac-limit 200 #设置mac数量,范围是(1..65535),通常可以不配置root@ex2200# set mac-table-aging-time 600 #”设置mac生存时间(秒),范围是(60-1000000) ”root@ex2200# set l3-interface vlan.10 #”将绑定三层逻辑子端口”root@ex2200# set interface ge-0/0/1.0 #”将端口加入到VLAN中”root@ex2200# set interface ge-0/0/2.0 #”将端口加入到VLAN中”(2)创建三层逻辑子端口root@ex2200# top #”回到最外层菜单”root@ex2200# set interfaces vlan unit 10 family inet address 192.168.1.1/24 #设置网关(3)将交换机端口修改为access模式并加入到新创建的VLAN中root@ex2200# top #”回到最外层菜单”root@ex2200# set interfaces ge-0/0/1 unit 0 family ethernet-switching port-mode accessroot@ex2200# set interfaces ge-0/0/1 unit 0 family ethernet-switching vlan members 10root@ex2200# set interfaces ge-0/0/2 unit 0 family ethernet-switching port-mode accessroot@ex2200# set interfaces ge-0/0/2 unit 0 family ethernet-switching vlan members 10(4)commit提交:root@ex2200#commit8, DHCP 配置(DHCP Server)set system services dhcp pool 192.168.1.0/24 address-range low 192.168.1.33set system services dhcp pool 192.168.1.0/24 address-range high 192.168.1.64et system services dhcp pool 192.168.1.0/24 domain-name set system services dhcp pool 192.168.1.0/24 name-server 192.168.1.1set system services dhcp pool 192.168.1.0/24 router 192.168.1.1set system services dhcp pool 192.168.1.0/24 default-lease-time 3600set security zones security-zone untrust interfaces fe-0/0/5.0 host-inbound-traffic system-services dhcpuser@host# set security zones security-zone untrust interfaces fe-0/0/6.0 host-inbound-traffic system-services dhcp user@host# set interfaces fe-0/0/6 unit 0 family inet address 192.168.1.1/24DHCP设置(DHCP Client)user@host# set interfaces fe‐0/0/7 unit 0 family inet dhcpuser@host# set security zones security‐zone untrust interfaces fe‐0/0/7.0 host‐inbound‐traffic system‐services dhcpDHCP设置(DHCP Relay)user@host# set forwarding‐options helpers bootp description "Global DHCP relay service"user@host# set forwarding‐options helpers bootp server 192.18.24.38user@host# set forwarding‐options helpers bootp maximum‐hop‐count 4user@host# set forwarding‐options helpers bootp interface fe‐0/0/7.0user@host# set security zones security‐zone untrust interfaces fe‐0/0/7 host‐inbound‐traffic system‐services dhcpuser@host# set security zones security‐zone untrust interfaces fe‐0/0/8 host‐inbound‐traffic system‐services dhcp9,接口设置user@host# set interfaces ge-0/0/1 unit 0 family inet address 192.168.20.2/24或者set interfaces ge-0/0/1.0 family inet address 192.168.20.2/249.2 设置区域user@host# set security zones security-zone trustuser@host# set security zones security-zone trust interfaces ge-0/0/1.0…ge-0/0/1.0 host-inbound-traffic system-services http (允许的服务)10, 静态路由user@host# set routing-options static route 10.2.2.0/24 next-hop 10.1.1.254user@host# set routing-options static route 0.0.0.0/0 next-hop 10.1.1.25411,在系统级开启ftp/telnet/http远程接入管理服务Set system services ftpSet system services sshSet system services telnetSet system services web‐management http12, 在untrust zone 打开允许远程登录管理服务Set security zones security‐zone untrnst host‐inbound‐traffic system‐services ssh13,防火墙策略安全设备的缺省行为是拒绝安全区段之间的所有信息流,允许绑定到同一区段的接口间的所有信息流。
JuniperSRX3400 Routing-instance AAA、NTP、SYSLOG实验配置手册目录1.实验需求 (3)2.实验环境 (3)3.实验拓扑 (4)3.1.创建虚拟机 (4)3.2.虚拟机之间网络连接 (4)4.防火墙配置 (7)5.AAA配置验证 (14)5.1.1.若将防火墙source-address定义为172.16.1.1 (14)5.1.2.删除环回口lo0地址 (16)6.NTP配置验证 (17)6.1.1.若将ntp源地址设为172.16.1.1, (18)6.1.2.删除环回口lo0地址 (18)7.SYSLOG配置验证 (19)7.1.1.若将SYSLOG源地址设为172.16.1.1 (19)7.1.2.删除防火墙上lo0接口地址 (20)8.最终结论 (21)为了能够充分理解Juniper SRX 防火墙在运行routing-instance 情况下配置AAA、syslog、ntp的运行机制,通过虚拟机搭建试验环境来验证。
2.实验环境Juniper 防火墙使用虚拟机来搭建,Radius服务器使用windows 2003 + ACS v4.2,将windows 2003作为ntp server, 在windows 2003上安装Kiwi_Syslog_Server 作为syslog软件。
实验工具如下:3.1.创建虚拟机创建2个虚拟机:SRX:juniper 防火墙Radius_NTP_Syslog_server:作为radius、NTP、syslog服务器;3.2.虚拟机之间网络连接各虚拟机网卡连接方式如下:1)将虚拟机SRX网卡1与物理机网卡桥接2)将虚拟机SRX网卡3采用自定义方式,用于与两台服务器连接3)服务器网卡也采用自定义的方式,用于与SRX连接:4)配置IP地址,测试联通性按照以上拓扑图对防火墙接口、服务器网口的IP地址进行配置,并测试连通性。

Juniper SRX系列防火墙配置管理手册目录一、JUNOS操作系统介绍 (3)层次化配置结构 (3)JunOS配置管理 (4)SRX主要配置内容 (4)二、SRX防火墙配置操作举例说明 (5)初始安装 (5)设备登陆 (5)设备恢复出厂介绍 (5)设置root用户口令 (5)设置远程登陆管理用户 (6)远程管理SRX相关配置 (6)配置操作实验拓扑 (7)策略相关配置说明 (7)策略地址对象定义 (8)策略服务对象定义 (8)策略时间调度对象定义 (8)添加策略配置举例 (9)策略删除 (10)调整策略顺序 (10)策略失效与激活 (10)地址转换 (10)Interface based NAT 基于接口的源地址转换 (11)Pool based Source NAT基于地址池的源地址转换 (12)Pool base destination NAT基于地址池的目标地址转换 (12)Pool base Static NAT基于地址池的静态地址转换 (13)路由协议配置 (14)静态路由配置 (14)OSPF配置 (15)交换机Firewall限制功能 (22)限制IP地 (22)限制MAC地址 (22)三、SRX防火墙常规操作与维护 (23)设备关机 (23)设备重启 (23)操作系统升级 (24)密码恢复 (24)常用监控维护命令 (25)Juniper SRX Branch系列防火墙配置管理手册说明SRX系列防火墙是Juniper公司基于JUNOS操作系统的安全系列产品,JUNOS集成了路由、交换、安全性和一系列丰富的网络服务。
目前Juniper公司的全系列路由器产品、交换机产品和SRX安全产品均采用统一源代码的JUNOS操作系统,JUNOS是全球首款将转发与控制功能相隔离,并采用模块化软件架构的网络操作系统。
JUNOS作为电信级产品的精髓是Juniper真正成功的基石,它让企业级产品同样具有电信级的不间断运营特性,更好的安全性和管理特性,JUNOS软件创新的分布式架构为高性能、高可用、高可扩展的网络奠定了基础。
产品简介产品说明瞻博网络SRX1400业务网关是市场领先的SRX 系列数据中心产品线的最新成员。
SRX1400整合了多种安全服务和网络功能,具有极高的可用性,主要为10GbE 网络环境提供保护。
它采用了模块化设计,其通用尺寸的模块可以从前面板进行维护和更换。
SRX1400利用创新的技术,增加了可靠性和网络的可用性,并提供极高的并发安全服务性能。
凭借瞻博网络的动态服务架构和Junos OS ,以及基于SRX3000业务网关成熟的电信级特性,SRX1400确立了新的价值标准,扩展了SRX 系列数据中心产品线,能够经济高效地满足更小网络环境的安全需求。
每台SRX1400业务网关都整合了多种安全服务,并执行全面的安全策略,其性能完全能满足当今10GbE 高性能网络环境的需要。
面向网络安全专业人员SRX1400是按照电信级标准从底层开始设计的高可靠设备,能够在严格的高性能数据中心网络环境中,长时间无故障地连续运行。
SRX1400的设计和生产过程都采用了TL 9000质量管理体系,无论是软件、支持服务还是硬件(包括能够分离控制和用户平面的创新芯片组)都100%由瞻博网络提供,同时,SRX1400还将性能提升到一种新的水平,能够满足高性能网络的需要。
动态服务架构利用瞻博网络的动态服务架构,高端SRX 系列能够在处理器的多个核心之间动态、快速地分配数据会话。
动态服务架构不是像其他供应商那样,将网络流量和服务固定或严格捆绑到专门的CPU 核心和处理资源,而是动态地平衡流量会话,在由所有可用资源构成的一个共享池中动态地处理工作负载。
这就避免了在一般的安全计算平台上经常出现的情况,即一些资源全负荷或接近全负荷地运行,而其它资源却闲置或低负荷地运行。
产品概述SRX1400业务网关作为专业级的安全平台,非常适合部署在中小型的数据中心、企业和电信运营商网络。
在这些环境中,客户主要考虑的问题是功能整合、10Gbps 性能、空间节省和经济性。
Juniper SRX防火墙配置手册一、JUNOS操作系统介绍1.1 层次化配置结构JUNOS采用基于FreeBSD内核的软件模块化操作系统,支持CLI命令行和WEBUI两种接口配置方式,本文主要对CLI命令行方式进行配置说明。
JUNOS CLI使用层次化配置结构,分为操作(operational)和配置(configure)两类模式,在操作模式下可对当前配置、设备运行状态、路由及会话表等状态进行查看及设备运维操作,并通过执行config或edit命令进入配置模式,在配置模式下可对各相关模块进行配置并能够执行操作模式下的所有命令(run)。
在配置模式下JUNOS采用分层分级模块下配置结构,如下图所示,edit命令进入下一级配置(类似unix cd 命令),exit命令退回上一级,top命令回到根级。
1.2 JunOS配置管理JUNOS通过set语句进行配置,配置输入后并不会立即生效,而是作为候选配置(Candidate Config)等待管理员提交确认,管理员通过输入commit命令来提交配置,配置内容在通过SRX 语法检查后才会生效,一旦commit通过后当前配置即成为有效配置(Active config)。
另外,JUNOS 允许执行commit命令时要求管理员对提交的配置进行两次确认,如执行commit confirmed 2命令要求管理员必须在输入此命令后2分钟内再次输入commit以确认提交,否则2分钟后配置将自动回退,这样可以避免远程配置变更时管理员失去对SRX的远程连接风险。
在执行commit命令前可通过配置模式下show命令查看当前候选配置(Candidate Config),在执行commit后配置模式下可通过run show config命令查看当前有效配置(Active config)。
此外可通过执行show | compare比对候选配置和有效配置的差异。
SRX上由于配备大容量硬盘存储器,缺省按先后commit顺序自动保存50份有效配置,并可通过执行rolback和commit命令返回到以前配置(如rollback 0/commit可返回到前一commit配置);也可以直接通过执行save configname.conf手动保存当前配置,并执行load override configname.conf / commit调用前期手动保存的配置。
Juniper防火墙设备虚拟路由和策略路由的应用Juniper 防火墙设备虚拟路由和策略路由的应用在Juniper防火墙设备的OS中,集成了虚拟路由和策略路由功能,在一般的情况下,这两个功能都很少使用,但是,在某些特殊的环境中就需要这两个功能的应用了。
虚拟路由在逻辑上,可以看做是一个独立的路由器,并有独立的路由列表。
在Juniper防火墙的OS 中,默认在Juniper防火墙设备的OS中,集成了虚拟路由和策略路由功能,在一般的情况下,这两个功能都很少使用,但是,在某些特殊的环境中就需要这两个功能的应用了。
虚拟路由在逻辑上,可以看做是一个独立的路由器,并有独立的路由列表。
在Juniper 防火墙的OS中,默认有两个虚拟路由:trust-vr和untrust-vr。
防火墙中的各种基于流量转发的安全区(ZONE),则默认工作在trust-vr中。
虚拟路由的功能在一些特殊的环境下,可以将一个独立的多端口防火墙,在逻辑上作为两台独立的防火墙使用(不启用虚拟系统:VSYS),则两个拥有独立路由列表的安全设备可以拥有各自独立的外网线路,并且,互相之间不受影响。
策略路由,在Juniper的防火墙中也被称为源地址路由,该路由的作用是:对内部地址外出访问互联网或其它网络时,进行外出线路选择。
策略路由一般的应用环境是:在防火墙设备实现多链路接入应用并有负载分配需求时,对内部网络IP地址的外出访问互联网时进行人为指定方式的外出链路选择。
策略路由的优先级别在默认的情况下为最高,所以在使用策略路由时,如果防火墙设备还定义了基于trust-vr 的DMZ区应用时,一定会受到策略路由优先的影响,从而导致对DMZ区访问的失败。
为了解决这个问题,则需要对防火墙的安全域进行调整,从而,应用到了另外一个虚拟路由:untrust-vr。
具体的实例说明:某客户的网络环境描述:电信和网通的两条专线连接,内部有若干台服务器,若干台内部办公计算机。
Juniper SRX HA 配置实例文档查看须知: (3)测试拓扑: (3)一路由模式HA: (4)配置: (4)验证: (4)配置解析: (5)二透明模式HA(Access接口) (6)配置: (6)验证: (7)配置解析: (8)三透明模式HA(Trunk接口) (9)配置: (9)验证: (10)配置解析: (10)注意点 (12)文档查看须知:测试环境:SRX 220H两台配置须知:SRX 220H默认带外管理口Ge-0/0/6控制口:Ge-0/0/7数据同步口:Ge-0/0/1 使用集群则集群后接口标示为:Ge-0/0/0-7; Ge-3/0/0-7不同型号集群后接口显示不同,详情见官方文档拓扑对应IP:G-0/0/3:192.168.3.1/24G-0/0/4:192.168.4.1/24G-0/0/5:192.168..5.1/24MGT:10.10.30.189-190/24F0/0:192.168.4.2/24F0/1:192.168.6.1/24 (模拟遥远互联网)测试拓扑:一路由模式HA:配置:On device A:>set chassis cluster cluster-id 1 node 0 rebootOn device B:>set chassis cluster cluster-id 1 node 1 rebootOn device A:set groups node0 system host-name SRX-Primaryset groups node0 interfaces fxp0 unit 0 family inet address 10.10.30.189/24 set groups node1 system host-name SRX-Secondbyset groups node1 interfaces fxp0 unit 0 family inet address 10.10.30.190/24 set apply-groups "${node}"set interfaces fab0 fabric-options member-interfaces ge-0/0/1set interfaces fab1 fabric-options member-interfaces ge-3/0/1set chassis cluster redundancy-group 0 node 0 priority 100set chassis cluster redundancy-group 0 node 1 priority 1set chassis cluster redundancy-group 1 node 0 priority 100set chassis cluster redundancy-group 1 node 1 priority 1set chassis cluster redundancy-group 1 interface-monitor ge-0/0/3 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-0/0/4 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-0/0/5 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-3/0/3 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-3/0/4 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-3/0/5 weight 255 set chassis cluster reth-count 3set interfaces ge-0/0/3 gigether-options redundant-parent reth0set interfaces ge-3/0/3 gigether-options redundant-parent reth0set interfaces reth0 redundant-ether-options redundancy-group 1set interfaces reth0 unit 0 family inet address 192.168.3.1/24set interfaces ge-0/0/4 gigether-options redundant-parent reth1set interfaces ge-3/0/4 gigether-options redundant-parent reth1set interfaces reth1 redundant-ether-options redundancy-group 1set interfaces reth1 unit 0 family inet address 192.168.4.1/24set interfaces ge-0/0/5 gigether-options redundant-parent reth2set interfaces ge-3/0/5 gigether-options redundant-parent reth2set interfaces reth2 redundant-ether-options redundancy-group 1set interfaces reth2 unit 0 family inet address 192.168.5.1/24set security zones security-zone trust interfaces reth0.0set security zones security-zone untrust interfaces reth1.0set security zones security-zone DMZ interfaces reth2.0验证:查看双机状态root@SRX-Primary> show chassis cluster statusCluster ID: 1Node Priority Status Preempt Manual failoverRedundancy group: 0 , Failover count: 1node0 100 primary no nonode1 1 secondary no noRedundancy group: 1 , Failover count: 1node0 100 primary no nonode1 1 secondary no no测试主备切换;查看当前设备主备情况;配置解析:On device A: >set chassis cluster cluster-id 1 node 0 reboot//定义cluster-id和node,同一个集群cluster-id必须相同,取值范围为0-15,0代表禁用集群;node取值范围为0-1,0代表主设备On device B: >set chassis cluster cluster-id 1 node 1 reboot//定义cluster-id和node,同一个集群cluster-id必须相同,取值范围为0-15,0代表禁用集群;node取值范围为0-1,0代表主设备On device A:set groups node0 system host-name SRX-Primaryset groups node0 interfaces fxp0 unit 0 family inet address 10.10.30.189/24set groups node1 system host-name SRX-Secondbyset groups node1 interfaces fxp0 unit 0 family inet address 10.10.30.190/24//为集群设备配置单独的名字和管理IP地址set apply-groups "${node}"//让以上的全局配置应用到每个独立的节点上set interfaces fab0 fabric-options member-interfaces ge-0/0/1set interfaces fab1 fabric-options member-interfaces ge-3/0/1//定义数据面板控制口并关联端口set chassis cluster redundancy-group 0 node 0 priority 100set chassis cluster redundancy-group 0 node 1 priority 1set chassis cluster redundancy-group 1 node 0 priority 100set chassis cluster redundancy-group 1 node 1 priority 1//设置冗余组的对不同节点的优先级,优先级范围1-254.值越大优先级越高,一般习惯定义2个冗余组,redundancy-group 0用于控制引擎,redundancy-group 1用于控制数据引擎,当然你也可以为每组冗余端口放在一个redundancy-group组中set chassis cluster redundancy-group 1 interface-monitor ge-0/0/3 weight 255set chassis cluster redundancy-group 1 interface-monitor ge-0/0/4 weight 255set chassis cluster redundancy-group 1 interface-monitor ge-0/0/5 weight 255set chassis cluster redundancy-group 1 interface-monitor ge-3/0/3 weight 255set chassis cluster redundancy-group 1 interface-monitor ge-3/0/4 weight 255set chassis cluster redundancy-group 1 interface-monitor ge-3/0/5 weight 255//配置接口监控在数据冗余口,不建议配置接口监控在redundancy-group 0,当监控到接口故障后优先级降255,实现数据口冗余自动切换set chassis cluster reth-count 3//定义集群最多支持多少组冗余接口,必须不低于当前配置的冗余口组数目,否则将有超过数量的冗余口不能正常工作,超过冗余组的冗余接口的路由信息都不生效set interfaces ge-0/0/3 gigether-options redundant-parent reth0set interfaces ge-3/0/3 gigether-options redundant-parent reth0set interfaces reth0 redundant-ether-options redundancy-group 1//把物理端口加入到冗余接口reth,并把接口reth0加入数据冗余组redundancy-group 1set interfaces reth0 unit 0 family inet address 192.168.3.1/24//为冗余逻辑接口配置IP地址set interfaces ge-0/0/4 gigether-options redundant-parent reth1set interfaces ge-3/0/4 gigether-options redundant-parent reth1set interfaces reth1 redundant-ether-options redundancy-group 1//把物理端口加入到冗余接口reth,并把接口reth1加入数据冗余组redundancy-group 1set interfaces reth1 unit 0 family inet address 192.168.4.1/24//为冗余逻辑接口配置IP地址set interfaces ge-0/0/5 gigether-options redundant-parent reth2set interfaces ge-3/0/5 gigether-options redundant-parent reth2set interfaces reth2 redundant-ether-options redundancy-group 1//把物理端口加入到冗余接口reth,并把接口reth2加入数据冗余组redundancy-group 1set interfaces reth2 unit 0 family inet address 192.168.5.1/24//为冗余逻辑接口配置IP地址set security zones security-zone trust interfaces reth0.0set security zones security-zone untrust interfaces reth1.0set security zones security-zone DMZ interfaces reth2.0//把集群的逻辑接口关联到ZONE二透明模式HA(Access接口);配置:On device A:>set chassis cluster cluster-id 1 node 0 rebootOn device B:>set chassis cluster cluster-id 1 node 1 rebootOn device A:set groups node0 system host-name SRX-Primaryset groups node0 interfaces fxp0 unit 0 family inet address 10.10.30.189/24set groups node1 system host-name SRX-Secondbyset groups node1 interfaces fxp0 unit 0 family inet address 10.10.30.190/24set apply-groups "${node}"set chassis cluster reth-count 3set chassis cluster redundancy-group 0 node 0 priority 100set chassis cluster redundancy-group 0 node 1 priority 1set chassis cluster redundancy-group 1 node 0 priority 100set chassis cluster redundancy-group 1 node 1 priority 1set chassis cluster redundancy-group 1 interface-monitor ge-0/0/3 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-3/0/3 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-0/0/4 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-3/0/4 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-0/0/5 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-3/0/5 weight 255 set interfaces ge-0/0/3 gigether-options redundant-parent reth0set interfaces ge-0/0/4 gigether-options redundant-parent reth1set interfaces ge-0/0/5 gigether-options redundant-parent reth2set interfaces ge-3/0/3 gigether-options redundant-parent reth0set interfaces ge-3/0/4 gigether-options redundant-parent reth1set interfaces ge-3/0/5 gigether-options redundant-parent reth2set interfaces fab0 fabric-options member-interfaces ge-0/0/1set interfaces fab1 fabric-options member-interfaces ge-3/0/1set interfaces reth0 redundant-ether-options redundancy-group 1set interfaces reth0 unit 0 family bridge interface-mode accessset interfaces reth0 unit 0 family bridge vlan-id 1set interfaces reth1 redundant-ether-options redundancy-group 1set interfaces reth1 unit 0 family bridge interface-mode accessset interfaces reth1 unit 0 family bridge vlan-id 1set interfaces reth2 redundant-ether-options redundancy-group 1set interfaces reth2 unit 0 family bridge interface-mode accessset interfaces reth2 unit 0 family bridge vlan-id 1set bridge-domains sysway domain-type bridgeset bridge-domains sysway vlan-id 1验证:查看双机状态配置解析:On device A:>set chassis cluster cluster-id 1 node 0 rebootOn device B:>set chassis cluster cluster-id 1 node 1 reboot//定义cluster-id和node,同一个集群cluster-id必须相同,取值范围为0-15,0代表禁用集群;node取值范围为0-1,0代表主设备On device A:set groups node0 system host-name SRX-Primaryset groups node0 interfaces fxp0 unit 0 family inet address 10.10.30.189/24set groups node1 system host-name SRX-Secondbyset groups node1 interfaces fxp0 unit 0 family inet address 10.10.30.190/24set apply-groups "${node}"//把以上的全局配置应用到每个独立的节点上set chassis cluster reth-count 3set chassis cluster redundancy-group 0 node 0 priority 100set chassis cluster redundancy-group 0 node 1 priority 1set chassis cluster redundancy-group 1 node 0 priority 100set chassis cluster redundancy-group 1 node 1 priority 1//设置冗余组数量及冗余组的不同节点的优先级set chassis cluster redundancy-group 1 interface-monitor ge-0/0/3 weight 255set chassis cluster redundancy-group 1 interface-monitor ge-3/0/3 weight 255set chassis cluster redundancy-group 1 interface-monitor ge-0/0/4 weight 255set chassis cluster redundancy-group 1 interface-monitor ge-3/0/4 weight 255set chassis cluster redundancy-group 1 interface-monitor ge-0/0/5 weight 255set chassis cluster redundancy-group 1 interface-monitor ge-3/0/5 weight 255//配置接口监控在数据冗余组set interfaces ge-0/0/3 gigether-options redundant-parent reth0set interfaces ge-0/0/4 gigether-options redundant-parent reth1set interfaces ge-0/0/5 gigether-options redundant-parent reth2set interfaces ge-3/0/3 gigether-options redundant-parent reth0set interfaces ge-3/0/4 gigether-options redundant-parent reth1set interfaces ge-3/0/5 gigether-options redundant-parent reth2//把物理接口关联到冗余组set interfaces fab0 fabric-options member-interfaces ge-0/0/1set interfaces fab1 fabric-options member-interfaces ge-3/0/1//定义数据面板控制口并关联端口set interfaces reth0 redundant-ether-options redundancy-group 1//定义接口reth0口关联到redundancy-group 1set interfaces reth0 unit 0 family bridge interface-mode access//设置逻辑接口为网桥模式并且接口类型为accessset interfaces reth0 unit 0 family bridge vlan-id 1//设置逻辑接口为网桥模式并允许vlan 1的数据包通过(建议VLAN ID值与直连交换机的接口属于同一个VLAN)set interfaces reth1 redundant-ether-options redundancy-group 1set interfaces reth1 unit 0 family bridge interface-mode accessset interfaces reth1 unit 0 family bridge vlan-id 1set interfaces reth2 redundant-ether-options redundancy-group 1set interfaces reth2 unit 0 family bridge interface-mode accessset interfaces reth2 unit 0 family bridge vlan-id 1//设置reth1,reth2的相关属性set bridge-domains sysway domain-type bridge//定义网桥域类型及网桥域名称set bridge-domains sysway vlan-id 1//定义网桥域的VLAN ID 建议和reth接口定义的一样三透明模式HA(Trunk接口)配置:On device A:>set chassis cluster cluster-id 1 node 0 rebootOn device B:>set chassis cluster cluster-id 1 node 1 rebootOn device A:set groups node0 system host-name SRX-Primaryset groups node0 interfaces fxp0 unit 0 family inet address 10.10.30.189/24 set groups node1 system host-name SRX-Secondbyset groups node1 interfaces fxp0 unit 0 family inet address 10.10.30.190/24 set apply-groups "${node}"set chassis cluster reth-count 3set chassis cluster redundancy-group 0 node 0 priority 100set chassis cluster redundancy-group 0 node 1 priority 1set chassis cluster redundancy-group 1 node 0 priority 100set chassis cluster redundancy-group 1 node 1 priority 1set chassis cluster redundancy-group 1 interface-monitor ge-0/0/3 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-3/0/3 weight 255 set chassis cluster redundancy-group 1 node 0 priority 100set chassis cluster redundancy-group 1 node 1 priority 1set chassis cluster redundancy-group 1 interface-monitor ge-0/0/4 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-3/0/4 weight 255 set chassis cluster redundancy-group 1 node 0 priority 100set chassis cluster redundancy-group 1 node 1 priority 1set chassis cluster redundancy-group 1 interface-monitor ge-0/0/5 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-3/0/5 weight 255 set interfaces ge-0/0/3 gigether-options redundant-parent reth0set interfaces ge-0/0/4 gigether-options redundant-parent reth1set interfaces ge-0/0/5 gigether-options redundant-parent reth2set interfaces ge-3/0/3 gigether-options redundant-parent reth0set interfaces ge-3/0/4 gigether-options redundant-parent reth1set interfaces ge-3/0/5 gigether-options redundant-parent reth2set interfaces fab0 fabric-options member-interfaces ge-0/0/1set interfaces fab1 fabric-options member-interfaces ge-3/0/1set interfaces reth0 redundant-ether-options redundancy-group 1set interfaces reth0 vlan-taggingset interfaces reth0 native-vlan-id 1set interfaces reth0 unit 0 family bridge interface-mode trunkset interfaces reth0 unit 0 family bridge vlan-id-list 1-1000set interfaces reth1 redundant-ether-options redundancy-group 1set interfaces reth1 vlan-taggingset interfaces reth1 native-vlan-id 1set interfaces reth1 unit 0 family bridge interface-mode trunkset interfaces reth1 unit 0 family bridge vlan-id-list 1-1000set interfaces reth2 redundant-ether-options redundancy-group 1set interfaces reth2 vlan-taggingset interfaces reth2 native-vlan-id 1set interfaces reth2 unit 0 family bridge interface-mode trunkset interfaces reth2 unit 0 family bridge vlan-id-list 1-1000set bridge-domains sysway vlan-id-list 1-1000验证:手动主备切换:当前双机状态配置解析:On device A:>set chassis cluster cluster-id 1 node 0 rebootOn device B:>set chassis cluster cluster-id 1 node 1 reboot//定义cluster-id和node,同一个集群cluster-id必须相同,取值范围为0-15,0代表禁用集群;node取值范围为0-1,0代表主设备On device A:set groups node0 system host-name SRX-Primaryset groups node0 interfaces fxp0 unit 0 family inet address 10.10.30.189/24set groups node1 system host-name SRX-Secondbyset groups node1 interfaces fxp0 unit 0 family inet address 10.10.30.190/24 set apply-groups "${node}"//把以上的全局配置应用到每个独立的节点上set chassis cluster reth-count 3set chassis cluster redundancy-group 0 node 0 priority 100set chassis cluster redundancy-group 0 node 1 priority 1//设置冗余组数量及控制冗余组的不同节点的优先级set chassis cluster redundancy-group 1 node 0 priority 100set chassis cluster redundancy-group 1 node 1 priority 1set chassis cluster redundancy-group 1 interface-monitor ge-0/0/3 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-3/0/3 weight 255 set chassis cluster redundancy-group 1 node 0 priority 100set chassis cluster redundancy-group 1 node 1 priority 1set chassis cluster redundancy-group 1 interface-monitor ge-0/0/4 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-3/0/4 weight 255 set chassis cluster redundancy-group 1 node 0 priority 100set chassis cluster redundancy-group 1 node 1 priority 1set chassis cluster redundancy-group 1 interface-monitor ge-0/0/5 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-3/0/5 weight 255 //配置接口监控在数据冗余组set interfaces ge-0/0/3 gigether-options redundant-parent reth0set interfaces ge-0/0/4 gigether-options redundant-parent reth1set interfaces ge-0/0/5 gigether-options redundant-parent reth2set interfaces ge-3/0/3 gigether-options redundant-parent reth0set interfaces ge-3/0/4 gigether-options redundant-parent reth1set interfaces ge-3/0/5 gigether-options redundant-parent reth2//把物理接口关联到数据冗余组set interfaces fab0 fabric-options member-interfaces ge-0/0/1set interfaces fab1 fabric-options member-interfaces ge-3/0/1//定义数据面板控制口并关联端口set interfaces reth0 redundant-ether-options redundancy-group 1//定义接口reth0口关联到redundancy-group 1set interfaces reth0 vlan-tagging//开启接口支持802.1Qset interfaces reth0 native-vlan-id 1//设置接口的本征VLAN ID为1set interfaces reth0 unit 0 family bridge interface-mode trunk//设置逻辑接口的模式为中继模式set interfaces reth0 unit 0 family bridge vlan-id-list 1-1000//设置接口允许通过的VLAN ID值set interfaces reth1 redundant-ether-options redundancy-group 1set interfaces reth1 vlan-taggingset interfaces reth1 native-vlan-id 1set interfaces reth1 unit 0 family bridge interface-mode trunkset interfaces reth1 unit 0 family bridge vlan-id-list 1-1000set interfaces reth2 redundant-ether-options redundancy-group 1set interfaces reth2 vlan-taggingset interfaces reth2 native-vlan-id 1set interfaces reth2 unit 0 family bridge interface-mode trunkset interfaces reth2 unit 0 family bridge vlan-id-list 1-1000//设置reth1,reth2的相关属性set bridge-domains sysway vlan-id-list 1-1000//定义网桥域及允许的VLAN ID 建议和reth接口定义的一样高版本的Trunk模式HA网桥域定义: set bridge-domains SRX650-CRM domain-type bridge vlan-id-list 1-1000待验证!注意点1. 桥接域(Bridge Domains):属于同一泛洪或广播域的一组逻辑接口。
Data SheetSRX1500 与瞻博网络 Contrail 服务编排结合使用,可以向企业和服务提供商提供完全自动化的 SD-WAN。
其全自动部署 (ZTP) 功能极大地简化了分支机构网络连接的初始部署和持续管理。
SRX1500的高性能和可扩展性使它可以用作 VPN 集线器,在各种 SD-WAN 拓扑结构中端接 VPN/安全叠加连接。
SRX1500 服务网关运行 Juniper Networks Junos®操作系统,这是一个已得到实践验证并且运营商可以定制加强的网络操作系统,目前在为全球前 100 强服务提供商网络提供支持。
IPv4/IPv6、OSPF、BGP 和组播经过严格测试的运营商级路由功能已在超过 15年的全球部署中久经验证。
功能与优势SRX1500 服务网关规格软件规格防火墙服务•有状态和无状态防火墙•基于区域的防火墙•筛选和分布式拒绝服务 (DDoS) 保护•抵御协议和流量异常•与 Pulse 统一访问控制 (UAC) 集成•与 Aruba Clear Pass Policy Manager 集成•基于用户角色的防火墙•SSL 检测网络地址转换 (NAT)•带有端口地址转换 (PAT) 的源 NAT•双向 1:1 静态 NAT•带有 PAT 的目标 NAT•持久 NAT•IPv6 地址转换VPN 功能•隧道:通用路由封装 (GRE)1、IP-IP1、IPsec•站点-站点 IPsec VPN、自动 VPN、组 VPN•IPsec 加密算法:数据加密标准 (DES)、三重 DES (3DES)、高级加密标准 (AES-256)、AES-GCM•IPsec 身份验证算法:MD5、SHA-1、SHA-128、SHA-256•预共享密钥和公钥基础架构 (PKI) (X.509)•完全向前保密,防重播•IPv4 和 IPv6 IPsec VPN•站点-站点 VPN 的多代理 ID•互联网密钥交换(IKEv1、IKEv2),NAT-T•虚拟路由器和服务质量 (QoS) 感知•基于标准的失效对等方检测 (DPD) 支持•VPN 监控高可用性功能•虚拟路由器冗余协议 (VRRP)•有状态的高可用性- 双机箱集群- 主动/被动- 主动/被动- 配置同步- 防火墙会话同步- 设备/链路检测- 不中断服务的软件升级 (ISSU)•采用路由与接口故障转移的 IP 监控应用程序安全性服务2•应用程序可见性和控制•基于应用程序的防火墙•应用程序 QoS•高级/基于应用程序策略的路由 (APBR)•应用程序体验质量 (AppQoE)•基于应用程序的多路径路由威胁防御和情报服务3•入侵防御•防病毒•反垃圾邮件•类别/基于信誉的 URL 过滤•SecIntel 提供威胁情报•防范僵尸网络(命令和控制)•基于 GeoIP 的自适应实施•瞻博网络 Advanced Threat Prevention(一种基于云的 SaaS产品),可检测并阻止零日攻击•瞻博网络 ATP 设备,是一种内部部署的分布式高级威胁防御解决方案,可用于检测并阻止零日攻击路由协议•IPv4、IPv6•静态路由•RIP v1/v2•OSPF/OSPF v3•具有路由反射器的 BGP•IS-IS•组播:Internet 组管理协议 (IGMP) v1/v2;协议无关组播(PIM) 稀疏模式 (SM)/密集模式 (DM)/源特定组播 (SSM);会话描述协议 (SDP);距离矢量组播路由协议 (DVMRP);组播源发现协议 (MSDP);逆向路径转发 (RPF)•封装:VLAN、通过以太网传输的点对点协议 (PPPoE)•虚拟路由器•基于策略的路由,基于源的路由•等价多路径 (ECMP)QoS 功能•支持 802.1 p、DiffServ代码点 (DSCP)、EXP•按 VLAN、数据链路连接标识符 (DLCI)、接口、束或多域过滤器分类•标记、监管和整形•分类和计划•加权随机早期检测 (WRED)•保证带宽和最大带宽•入口流量监管•虚拟通道•层次结构整形和策略制定交换功能•基于 ASIC 的第 2 层转发•MAC 地址学习•VLAN 寻址以及集成路由与桥接 (IRB) 支持•链路聚合与 LACP•LLDP 和 LLDP-MED•STP、RSTP、MSTP•MVRP•802.1X 身份验证网络服务•动态主机配置协议 (DHCP) 客户端/服务器/中继•域名系统 (DNS) 代理、动态 DNS (DDNS)•瞻博网络实时性能监控 (RPM) 和 IP 监控•瞻博网络流量监控(J 流)•双向转发检测 (BFD)•双向主动测量协议 (TWAMP)•IEEE 802.3ah 链路默认管理 (LFM)•IEEE 802.1ag 连接故障管理 (CFM)高级路由服务•分组模式•MPLS(RSVP、LDP)•电路交叉连接 (CCC)、平移交叉连接 (TCC)•L2/L2 MPLS VPN、伪线•虚拟专用 LAN 服务 (VPLS)、下一代组播 VPN (NG-MVPN)•MPLS 流量工程和 MPLS 快速重新路由管理、自动化、日志记录和报告•SSH、T elnet、SNMP•智能图像下载•瞻博网络 CLI 和 Web UI•瞻博网络 Junos Space 和 Security Director•Python•Junos OS 事件、提交和 OP 脚本•应用程序和带宽使用情况报告•自动安装•调试和故障排除工具GRE、IP-IP 和 VRRP 在有状态高可用性模式下不受支持。
juniper SRX 利用虚拟路由器实现多链路冗余以及双向接入案例目录文档查看须知: (2)测试拓扑: (4)一虚拟路由器(记住来流量入口); (5)需求: (5)配置: (5)验证: (7)配置解析: (7)二虚拟路由器(多链路负载冗余); (10)需求: (10)配置: (11)验证: (13)配置解析: (18)三虚拟路由器(双线接入); (21)需求: (21)配置: (21)验证: (25)注意点: (26)文档查看须知:测试环境:SRX 220H拓扑对应 IP:G-0/0/3:192.168.3.1/24G-0/0/4:192.168.4.1/24G-0/0/5:192.168.5.1/24G-0/0/6:10.10.30.189/24F0/1:192.168.4.2/24F0/2:192.168.5.2/24F0/3:192.168.100.1/24(模拟遥远互联网)测试拓扑:一虚拟路由器(记住来流量入口);需求:外网用户访问防火墙的外网接口 3389 端口 NAT 到内网服务器 192.168.3.5:3389,流量按原路返回;放行所有外网用户到主机 192.168.3.5 的 3389 端口;(双线接入)配置:set routing-instances Tel instance-type virtual-routerset routing-instances Tel interface ge-0/0/4.0set routing-instances Tel routing-options interface-routes rib-group inet Big-ribset routing-instances Tel routing-options static route 0.0.0.0/0 next-hop 192.168.4.2set routing-instances CNC instance-type virtual-routerset routing-instances CNC interface ge-0/0/5.0set routing-instances CNC routing-options interface-routes rib-group inet Big-ribset routing-instances CNC routing-options static route 0.0.0.0/0 next-hop 192.168.5.2set interfaces ge-0/0/3 unit 0 family inet address 192.168.3.1/24set interfaces ge-0/0/4 unit 0 family inet address 192.168.4.1/24set interfaces ge-0/0/5 unit 0 family inet address 192.168.5.1/24set interfaces ge-0/0/6 unit 0 family inet address 10.10.30.189/24set routing-options interface-routes rib-group inet Big-ribset routing-options static route 10.0.0.0/8 next-hop 10.10.30.1set routing-options static route 0.0.0.0/0 next-hop 192.168.4.2set routing-options static route 0.0.0.0/0 installset routing-options static route 0.0.0.0/0 no-readvertiseset routing-options rib-groups Big-rib import-rib inet.0set routing-options rib-groups Big-rib import-rib CNC.inet.0set routing-options rib-groups Big-rib import-rib Tel.inet.0set security nat destination pool 111 address 192.168.3.5/32set security nat destination rule-set 1 from zone Tel-trustset security nat destination rule-set 1 rule 111 match source-address 0.0.0.0/0set security nat destination rule-set 1 rule 111 match destination-address 192.168.4.1/32set security nat destination rule-set 1 rule 111 match destination-port 3389set security nat destination rule-set 1 rule 111 then destination-nat pool 111set security nat destination rule-set 2 from zone CNC-trustset security nat destination rule-set 2 rule 222 match source-address 0.0.0.0/0set security nat destination rule-set 2 rule 222 match destination-address 192.168.5.1/32set security nat destination rule-set 1 rule 111 match destination-port 3389set security nat destination rule-set 2 rule 222 then destination-nat pool 111set applications application tcp_3389 protocol tcpset applications application tcp_3389 destination-port 3389set security zones security-zone trust address-book address H_192.168.3.5 192.168.3.5/32set security policies from-zone Tel-trust to-zone trust policy default-permit match source-address anyset security policies from-zone Tel-trust to-zone trust policy default-permit match destination-address H_192.168.3.5 set security policies from-zone Tel-trust to-zone trust policy default-permit match application tcp_3389set security policies from-zone Tel-trust to-zone trust policy default-permit then permitset security policies from-zone CNC-trust to-zone trust policy default-permit match source-address anyset security policies from-zone CNC-trust to-zone trust policy default-permit match destination-addressH_192.168.3.5set security policies from-zone CNC-trust to-zone trust policy default-permit match application tcp_3389set security policies from-zone CNC-trust to-zone trust policy default-permit then permitset security zones security-zone trust host-inbound-traffic system-services allset security zones security-zone trust host-inbound-traffic protocols allset security zones security-zone trust interfaces ge-0/0/3.0set security zones security-zone Tel-trust host-inbound-traffic system-services allset security zones security-zone Tel-trust host-inbound-traffic protocols allset security zones security-zone Tel-trust interfaces ge-0/0/4.0set security zones security-zone CNC-trust host-inbound-traffic system-services allset security zones security-zone CNC-trust host-inbound-traffic protocols allset security zones security-zone CNC-trust interfaces ge-0/0/5.0set security zones security-zone MGT host-inbound-traffic system-services allset security zones security-zone MGT host-inbound-traffic protocols allset security zones security-zone MGT interfaces ge-0/0/6.0验证:root@SRX-Ipsec-A> show security flow sessionSession ID: 9696, Policy name: default-permit/5, Timeout: 1794, ValidIn: 192.168.100.211/57408 --> 192.168.5.1/3389;tcp, If: ge-0/0/5.0, Pkts: 2, Bytes: 112Out: 192.168.3.5/3389 --> 192.168.100.211/57408;tcp, If: ge-0/0/3.0, Pkts: 1, Bytes: 60=========================================================================== =root@SRX-Ipsec-A> show security flow sessionSession ID: 9697, Policy name: default-permit/4, Timeout: 1796, ValidIn: 192.168.100.211/57409 --> 192.168.4.1/3389;tcp, If: ge-0/0/4.0, Pkts: 2, Bytes: 112Out: 192.168.3.5/3389 --> 192.168.100.211/57409;tcp, If: ge-0/0/3.0, Pkts: 1, Bytes: 60配置解析:set routing-instances Tel instance-type virtual-router//创建虚拟 VR Telset routing-instances Tel interface ge-0/0/4.0//把逻辑接口加入虚拟 VRset routing-instances Tel routing-options interface-routes rib-group inet Big-rib//定义新增的路由表属于路由组“Big-rib”set routing-instances Tel routing-options static route 0.0.0.0/0 next-hop 192.168.4.2 //为 Tel 路由表配置路由set routing-instances CNC instance-type virtual-routerset routing-instances CNC interface ge-0/0/5.0set routing-instances CNC routing-options interface-routes rib-group inet Big-rib set routing-instances CNC routing-options static route 0.0.0.0/0 next-hop 192.168.5.2 //配置路由表 CNC 相关信息set interfaces ge-0/0/3 unit 0 family inet address 192.168.3.1/24set interfaces ge-0/0/4 unit 0 family inet address 192.168.4.1/24set interfaces ge-0/0/5 unit 0 family inet address 192.168.5.1/24set interfaces ge-0/0/6 unit 0 family inet address 10.10.30.189/24//配置逻辑接口的 IP 地址set routing-options interface-routes rib-group inet Big-rib//定义路由表组,并把接口路由加入到 Big-rib 路由组中set routing-options static route 10.0.0.0/8 next-hop 10.10.30.1set routing-options static route 0.0.0.0/0 next-hop 192.168.4.2//配置全局路由表路由信息set routing-options static route 0.0.0.0/0 install//把路由表安装到转发表set routing-options static route 0.0.0.0/0 no-readvertise//set routing-options rib-groups Big-rib import-rib inet.0set routing-options rib-groups Big-rib import-rib CNC.inet.0set routing-options rib-groups Big-rib import-rib Tel.inet.0//导入三张路由表之间的直连路由到路由表组set security nat destination pool 111 address 192.168.3.5/32//定义目的 NAT 后的内部服务器的 IP 地址set security nat destination rule-set 1 from zone Tel-trustset security nat destination rule-set 1 rule 111 match source-address 0.0.0.0/0set security nat destination rule-set 1 rule 111 match destination-address 192.168.4.1/32set security nat destination rule-set 1 rule 111 match destination-port 3389set security nat destination rule-set 1 rule 111 then destination-nat pool 111//配置 ZONE Tel-trust 的目的NATset security nat destination rule-set 2 from zone CNC-trustset security nat destination rule-set 2 rule 222 match source-address 0.0.0.0/0set security nat destination rule-set 2 rule 222 match destination-address 192.168.5.1/32set security nat destination rule-set 1 rule 111 match destination-port 3389set security nat destination rule-set 2 rule 222 then destination-nat pool 111//配置 ZONE CNC-trust 的目的NATset applications application tcp_3389 protocol tcpset applications application tcp_3389 destination-port 3389set security zones security-zone trust address-book address H_192.168.3.5 192.168.3.5/32//自定义端口和配置地址表set security policies from-zone Tel-trust to-zone trust policy default-permit match source-address anyset security policies from-zone Tel-trust to-zone trust policy default-permit match destination-address H_192.168.3.5 set security policies from-zone Tel-trust to-zone trust policy default-permit match application tcp_3389set security policies from-zone Tel-trust to-zone trust policy default-permit then permit//配置 Tel-trust 到 trust 策略set security policies from-zone CNC-trust to-zone trust policy default-permit match source-address anyset security policies from-zone CNC-trust to-zone trust policy default-permit match destination-addressH_192.168.3.5set security policies from-zone CNC-trust to-zone trust policy default-permit match application tcp_3389set security policies from-zone CNC-trust to-zone trust policy default-permit then permit//配置 CNC-trust 到 trust 策略set security zones security-zone trust host-inbound-traffic system-services allset security zones security-zone trust host-inbound-traffic protocols allset security zones security-zone trust interfaces ge-0/0/3.0set security zones security-zone Tel-trust host-inbound-traffic system-services all set security zones security-zone Tel-trust host-inbound-traffic protocols allset security zones security-zone Tel-trust interfaces ge-0/0/4.0set security zones security-zone CNC-trust host-inbound-traffic system-services all set security zones security-zone CNC-trust host-inbound-traffic protocols allset security zones security-zone CNC-trust interfaces ge-0/0/5.0set security zones security-zone MGT host-inbound-traffic system-services allset security zones security-zone MGT host-inbound-traffic protocols allset security zones security-zone MGT interfaces ge-0/0/6.0//定义逻辑接口到 ZONE,并开放所有的协议及服务来访问防火墙的直连接口二虚拟路由器(多链路负载冗余);需求:内网用户访问端口 22.3389.8080,走电信,其他所有流量走 CNC;所有内网访问外网的流量 NAT 为对应外网接口 IP 地址;实现负载冗余的功能;放行所有服务;(双线接入)配置:set routing-instances Tel instance-type virtual-routerset routing-instances Tel interface ge-0/0/4.0set routing-instances Tel routing-options interface-routes rib-group inet Big-ribset routing-instances Tel routing-options static route 0.0.0.0/0 next-hop 192.168.4.2set routing-instances Tel routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.5.2 preference 100 set routing-instances CNC instance-type virtual-routerset routing-instances CNC interface ge-0/0/5.0set routing-instances CNC routing-options interface-routes rib-group inet Big-ribset routing-instances CNC routing-options static route 0.0.0.0/0 next-hop 192.168.5.2set routing-instances CNC routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.4.2 preference 100 set interfaces ge-0/0/3 unit 0 family inet address 192.168.3.1/24set interfaces ge-0/0/4 unit 0 family inet address 192.168.4.1/24set interfaces ge-0/0/5 unit 0 family inet address 192.168.5.1/24set interfaces ge-0/0/6 unit 0 family inet address 10.10.30.189/24set routing-options interface-routes rib-group inet Big-ribset routing-options static route 10.0.0.0/8 next-hop 10.10.30.1set routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.5.2 preference 100set routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.4.2 preference 10set routing-options static route 0.0.0.0/0 installset routing-options static route 0.0.0.0/0 no-readvertiseset routing-options rib-groups Big-rib import-rib inet.0set routing-options rib-groups Big-rib import-rib CNC.inet.0set routing-options rib-groups Big-rib import-rib Tel.inet.0set security nat source rule-set Soure-NAT-Policy from zone trustset security nat source rule-set Soure-NAT-Policy to zone Tel-trustset security nat source rule-set Soure-NAT-Policy rule Source-nat-1 match source-address 192.168.3.0/24set security nat source rule-set Soure-NAT-Policy rule Source-nat-1 match destination-address 0.0.0.0/0 set security nat source rule-set Soure-NAT-Policy rule Source-nat-1 then source-nat interfaceset security zones security-zone trust address-book address Net_192.168.3.0 192.168.3.0/24set security policies from-zone trust to-zone Tel-trust policy 1 match source-address N et_192.168.3.0set security policies from-zone trust to-zone Tel-trust policy 1 match destination-address anyset security policies from-zone trust to-zone Tel-trust policy 1 match application anyset security policies from-zone trust to-zone Tel-trust policy 1 then permitset security policies from-zone trust to-zone Tel-trust policy 1 then log session-initset security policies from-zone trust to-zone Tel-trust policy 1 then log session-closeset security nat source rule-set Soure-NAT-Policy-2 from zone trustset security nat source rule-set Soure-NAT-Policy-2 to zone CNC-trustset security nat source rule-set Soure-NAT-Policy-2 rule Source-nat-2 match source-address 192.168.3.0/24 set security nat source rule-set Soure-NAT-Policy-2 rule Source-nat-2 match destination-address 0.0.0.0/0 set security nat source rule-set Soure-NAT-Policy-2 rule Source-nat-2 then source-nat interfaceset security policies from-zone trust to-zone CNC-trust policy 2 match source-address Net_192.168.3.0set security policies from-zone trust to-zone CNC-trust policy 2 match destination-address anyset security policies from-zone trust to-zone CNC-trust policy 2 match application anyset security policies from-zone trust to-zone CNC-trust policy 2 then permitset security policies from-zone trust to-zone CNC-trust policy 2 then log session-initset security policies from-zone trust to-zone CNC-trust policy 2 then log session-closeset interfaces ge-0/0/3 unit 0 family inet filter input filter-1set firewall filter filter-1 term term-1 from destination-port 22set firewall filter filter-1 term term-1 from destination-port 3389set firewall filter filter-1 term term-1 from destination-port 8080set firewall filter filter-1 term term-1 then routing-instance Telset firewall filter filter-1 term default then routing-instance CNCset security zones security-zone trust host-inbound-traffic system-services allset security zones security-zone trust host-inbound-traffic protocols allset security zones security-zone trust interfaces ge-0/0/3.0set security zones security-zone Tel-trust host-inbound-traffic system-services allset security zones security-zone Tel-trust host-inbound-traffic protocols allset security zones security-zone Tel-trust interfaces ge-0/0/4.0set security zones security-zone CNC-trust host-inbound-traffic system-services allset security zones security-zone CNC-trust host-inbound-traffic protocols allset security zones security-zone CNC-trust interfaces ge-0/0/5.0set security zones security-zone MGT host-inbound-traffic system-services allset security zones security-zone MGT host-inbound-traffic protocols allset security zones security-zone MGT interfaces ge-0/0/6.0验证:基于目标端口路由验证:Session ID: 9693, Policy name: 1121/6, Timeout: 1790, ValidIn: 192.168.3.5/52562 --> 192.168.100.211/3389;tcp, If: ge-0/0/3.0, Pkts: 2, Bytes: 112 Out: 192.168.100.211/3389 --> 192.168.4.1/28262;tcp, If: ge-0/0/4.0, Pkts: 1, Bytes: 60 Session ID: 9703, Policy name: 1121/7, Timeout: 2, ValidIn: 192.168.3.5/6252 --> 192.168.100.211/1;icmp, If: ge-0/0/3.0, Pkts: 1, Bytes: 60 Out: 192.168.100.211/1 --> 192.168.5.1/4217;icmp, If: ge-0/0/5.0, Pkts: 1, Bytes: 60 当前路由表:root@SRX-Ipsec-A> show routeinet.0: 7 destinations, 8 routes (7 active, 0 holddown, 0 hidden)+ = Active Route, - = Last Active, * = Both0.0.0.0/0 *[Static/10] 00:01:26> to 192.168.4.2 via ge-0/0/4.0[Static/100] 00:01:04> to 192.168.5.2 via ge-0/0/5.0192.168.3.0/24 *[Direct/0] 00:04:31> via ge-0/0/3.0192.168.3.1/32 *[Local/0] 16:44:09Local via ge-0/0/3.0192.168.4.0/24 *[Direct/0] 00:01:26> via ge-0/0/4.0192.168.4.1/32 *[Local/0] 00:01:26Local via ge-0/0/4.0192.168.5.0/24 *[Direct/0] 00:01:04> via ge-0/0/5.0192.168.5.1/32 *[Local/0] 00:01:04Local via ge-0/0/5.0CNC.inet.0: 7 destinations, 8 routes (7 active, 0 holddown, 0 hidden) + = Active Route, - = Last Active, * = Both0.0.0.0/0 *[Static/5] 00:01:04> to 192.168.5.2 via ge-0/0/5.0[Static/100] 00:01:26> to 192.168.4.2 via ge-0/0/4.0192.168.3.0/24 *[Direct/0] 00:04:31> via ge-0/0/3.0192.168.3.1/32 *[Local/0] 00:04:31Local via ge-0/0/3.0192.168.4.0/24 *[Direct/0] 00:01:26> via ge-0/0/4.0192.168.4.1/32 *[Local/0] 00:01:26Local via ge-0/0/4.0192.168.5.0/24 *[Direct/0] 00:01:04> via ge-0/0/5.0192.168.5.1/32 *[Local/0] 16:44:09Local via ge-0/0/5.0Tel.inet.0: 7 destinations, 8 routes (7 active, 0 holddown, 0 hidden) + = Active Route, - = Last Active, * = Both0.0.0.0/0 *[Static/5] 00:01:26> to 192.168.4.2 via ge-0/0/4.0[Static/100] 00:01:04> to 192.168.5.2 via ge-0/0/5.0192.168.3.0/24 *[Direct/0] 00:04:31> via ge-0/0/3.0192.168.3.1/32 *[Local/0] 00:04:31Local via ge-0/0/3.0192.168.4.0/24 *[Direct/0] 00:01:26> via ge-0/0/4.0192.168.4.1/32 *[Local/0] 16:44:09Local via ge-0/0/4.0192.168.5.0/24 *[Direct/0] 00:01:04> via ge-0/0/5.0192.168.5.1/32 *[Local/0] 00:01:04Local via ge-0/0/5.0双线冗余验证:root@SRX-Ipsec-A> show security flow sessionSession ID: 10321, Policy name: 1121/7, Timeout: 48, ValidIn: 192.168.3.2/188 --> 192.168.100.211/59209;icmp, If: ge-0/0/3.0, Pkts: 1, Bytes: 84 Out: 192.168.100.211/59209 --> 192.168.5.1/13586;icmp, If: ge-0/0/5.0, Pkts: 0, Bytes: 0 Session ID: 10322, Policy name: 1121/6, Timeout: 50, Valid手动拔掉 CNC 广域网线路(模拟 CNC 线路故障)In: 192.168.3.2/189 --> 192.168.100.211/59209;icmp, If: ge-0/0/3.0, Pkts: 1, Bytes: 84 Out: 192.168.100.211/59209 --> 192.168.4.1/19350;icmp, If: ge-0/0/4.0, Pkts: 0, Bytes: 0 Session ID: 10330, Policy name: 1121/6, Timeout: 2, ValidIn: 192.168.3.2/197 --> 192.168.100.211/59209;icmp, If: ge-0/0/3.0, Pkts: 1, Bytes: 84 Out: 192.168.100.211/59209 --> 192.168.4.1/3661;icmp, If: ge-0/0/4.0, Pkts: 1, Bytes: 84 当前路由表:root@SRX-Ipsec-A> show routeinet.0: 6 destinations, 6 routes (6 active, 0 holddown, 0 hidden)+ = Active Route, - = Last Active, * = Both0.0.0.0/0 *[Static/10] 00:00:45> to 192.168.4.2 via ge-0/0/4.0192.168.3.0/24 *[Direct/0] 00:06:27> via ge-0/0/3.0192.168.3.1/32 *[Local/0] 16:46:05Local via ge-0/0/3.0192.168.4.0/24 *[Direct/0] 00:00:45> via ge-0/0/4.0192.168.4.1/32 *[Local/0] 00:00:45Local via ge-0/0/4.0192.168.5.1/32 *[Local/0] 00:00:37RejectCNC.inet.0: 6 destinations, 6 routes (6 active, 0 holddown, 0 hidden)+ = Active Route, - = Last Active, * = Both0.0.0.0/0 *[Static/100] 00:00:45> to 192.168.4.2 via ge-0/0/4.0192.168.3.0/24 *[Direct/0] 00:06:27> via ge-0/0/3.0192.168.3.1/32 *[Local/0] 00:06:27Local via ge-0/0/3.0192.168.4.0/24 *[Direct/0] 00:00:45> via ge-0/0/4.0192.168.4.1/32 *[Local/0] 00:00:45Local via ge-0/0/4.0192.168.5.1/32 *[Local/0] 16:46:05RejectTel.inet.0: 6 destinations, 6 routes (6 active, 0 holddown, 0 hidden) + = Active Route, - = Last Active, * = Both0.0.0.0/0 *[Static/5] 00:00:45> to 192.168.4.2 via ge-0/0/4.0192.168.3.0/24 *[Direct/0] 00:06:27> via ge-0/0/3.0192.168.3.1/32 *[Local/0] 00:06:27Local via ge-0/0/3.0192.168.4.0/24 *[Direct/0] 00:00:45> via ge-0/0/4.0192.168.4.1/32 *[Local/0] 16:46:05Local via ge-0/0/4.0192.168.5.1/32 *[Local/0] 00:00:37Reject配置解析:set routing-instances Tel instance-type virtual-routerset routing-instances Tel interface ge-0/0/4.0set routing-instances Tel routing-options interface-routes rib-group inet Big-ribset routing-instances Tel routing-options static route 0.0.0.0/0 next-hop 192.168.4.2set routing-instances CNC routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.5.2 preference 100 //配置 Tel 路由表并配置相关信息,通过优先级来实现双广域网冗余,优先级值越小,优先级越高set routing-instances CNC instance-type virtual-routerset routing-instances CNC interface ge-0/0/5.0set routing-instances CNC routing-options interface-routes rib-group inet Big-ribset routing-instances CNC routing-options static route 0.0.0.0/0 next-hop 192.168.5.2set routing-instances CNC routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.4.2 preference 100 //配置 CNC 路由表并配置相关信息set interfaces ge-0/0/3 unit 0 family inet address 192.168.3.1/24set interfaces ge-0/0/4 unit 0 family inet address 192.168.4.1/24set interfaces ge-0/0/5 unit 0 family inet address 192.168.5.1/24set interfaces ge-0/0/6 unit 0 family inet address 10.10.30.189/24//配置逻辑接口对应 IP 地址set routing-options interface-routes rib-group inet Big-rib//定义路由表组,并把接口路由加入到 Big-rib 路由组中set routing-options static route 10.0.0.0/8 next-hop 10.10.30.1set routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.5.2 preference 100set routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.4.2 preference 10//配置全局路由表路由信息,通过指定优先级来实现双广域网的冗余set routing-options static route 0.0.0.0/0 install//把路由表安装到转发表set routing-options static route 0.0.0.0/0 no-readvertise//set routing-options rib-groups Big-rib import-rib inet.0set routing-options rib-groups Big-rib import-rib CNC.inet.0set routing-options rib-groups Big-rib import-rib Tel.inet.0//导入三张路由表之间的直连路由到路由表组set security nat source rule-set Soure-NAT-Policy from zone trustset security nat source rule-set Soure-NAT-Policy to zone Tel-trustset security nat source rule-set Soure-NAT-Policy rule Source-nat-1 match source-address 192.168.3.0/24 set security nat source rule-set Soure-NAT-Policy rule Source-nat-1 match destination-address 0.0.0.0/0 set security nat source rule-set Soure-NAT-Policy rule Source-nat-1 then source-nat interface//配置 ZONE Tel-trust 基于接口的源NATset security zones security-zone trust address-book address Net_192.168.3.0 192.168.3.0/24//定义地址表set security policies from-zone trust to-zone Tel-trust policy 1 match source-address N et_192.168.3.0set security policies from-zone trust to-zone Tel-trust policy 1 match destination-address anyset security policies from-zone trust to-zone Tel-trust policy 1 match application anyset security policies from-zone trust to-zone Tel-trust policy 1 then permitset security policies from-zone trust to-zone Tel-trust policy 1 then log session-initset security policies from-zone trust to-zone Tel-trust policy 1 then log session-close//根据需求配置策略并记录 LOG 信息set security nat source rule-set Soure-NAT-Policy-2 from zone trustset security nat source rule-set Soure-NAT-Policy-2 to zone CNC-trustset security nat source rule-set Soure-NAT-Policy-2 rule Source-nat-2 match source-address 192.168.3.0/24 set security nat source rule-set Soure-NAT-Policy-2 rule Source-nat-2 match destination-address 0.0.0.0/0 set security nat source rule-set Soure-NAT-Policy-2 rule Source-nat-2 then source-nat interface//配置 ZONE CNC-trust 基于接口的源NATset security policies from-zone trust to-zone CNC-trust policy 2 match source-address Net_192.168.3.0set security policies from-zone trust to-zone CNC-trust policy 2 match destination-address anyset security policies from-zone trust to-zone CNC-trust policy 2 match application anyset security policies from-zone trust to-zone CNC-trust policy 2 then permitset security policies from-zone trust to-zone CNC-trust policy 2 then log session-initset security policies from-zone trust to-zone CNC-trust policy 2 then log session-close//根据需求配置策略并记录 LOG 信息set interfaces ge-0/0/3 unit 0 family inet filter input filter-1//从接口 ge-0/0/3 进入的数据进行包过滤操作,并定义名称” filter-1”set firewall filter filter-1 term term-1 from destination-port 22set firewall filter filter-1 term term-1 from destination-port 3389set firewall filter filter-1 term term-1 from destination-port 8080//对符合包过滤名称”filter-1”的且符合目标端口 22,3389,8080 数据进行打标记,标记为 term-1set firewall filter filter-1 term term-1 then routing-instance Tel//定义标记为 term-1 的数据,使用 Tel 路由表来转发数据set firewall filter filter-1 term default then routing-instance CNC//定义符合标记 default 数据使用 CNC 路由表来转发数据(default 为自定义标记的名称,根据习惯随便取,如果没有指定符合条件则代表所有流量都匹配)set security zones security-zone trust host-inbound-traffic system-services allset security zones security-zone trust host-inbound-traffic protocols allset security zones security-zone trust interfaces ge-0/0/3.0set security zones security-zone Tel-trust host-inbound-traffic system-services allset security zones security-zone Tel-trust host-inbound-traffic protocols allset security zones security-zone Tel-trust interfaces ge-0/0/4.0set security zones security-zone CNC-trust host-inbound-traffic system-services allset security zones security-zone CNC-trust host-inbound-traffic protocols allset security zones security-zone CNC-trust interfaces ge-0/0/5.0set security zones security-zone MGT host-inbound-traffic system-services allset security zones security-zone MGT host-inbound-traffic protocols allset security zones security-zone MGT interfaces ge-0/0/6.0//定义逻辑接口到 ZONE,并开放所有的协议及服务来访问防火墙的直连接口三虚拟路由器(双线接入);需求:ZONE trust 访问目标端口为 22.3389.8080,走Tel;ZONE trust 主机 192.168.3.2 的所有流量走T el;所有未明确的指定的流量走 CNC;ZONE trust 主机 192.168.3.5 对外发布远程桌面应用 Tel-trust(192.168.4.5),CNC-trust(192.168.5.5) 实现从哪家运行商来的流量从哪家运行商返回;(主动发起的流量)放行 ZONE trust 所有主机访问外网的流量;放行所有从外网来访问内网主机 192.168.3.5 的远程桌面服务;实现负载冗余;配置:set routing-instances Tel instance-type virtual-routerset routing-instances Tel interface ge-0/0/4.0set routing-instances Tel routing-options interface-routes rib-group inet Big-ribset routing-instances Tel routing-options static route 0.0.0.0/0 next-hop 192.168.4.2set routing-instances Tel routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.5.2 preference 100set routing-instances CNC instance-type virtual-routerset routing-instances CNC interface ge-0/0/5.0set routing-instances CNC routing-options interface-routes rib-group inet Big-ribset routing-instances CNC routing-options static route 0.0.0.0/0 next-hop 192.168.5.2set routing-instances CNC routing-options static route 0.0.0.0/0 qualified-next-hop 192.168.4.2 preference 100 set interfaces ge-0/0/3 unit 0 family inet address 192.168.3.1/24set interfaces ge-0/0/4 unit 0 family inet address 192.168.4.1/24set interfaces ge-0/0/5 unit 0 family inet address 192.168.5.1/24set interfaces ge-0/0/6 unit 0 family inet address 10.10.30.189/24set routing-options interface-routes rib-group inet Big-ribset routing-options static route 10.0.0.0/8 next-hop 10.10.30.1set routing-options static route 0.0.0.0/0 next-hop 192.168.4.2set routing-options static route 0.0.0.0/0 installset routing-options static route 0.0.0.0/0 no-readvertiseset routing-options rib-groups Big-rib import-rib inet.0set routing-options rib-groups Big-rib import-rib CNC.inet.0set routing-options rib-groups Big-rib import-rib Tel.inet.0set security nat destination pool 111 address 192.168.3.5/32set security nat destination rule-set 1 from zone Tel-trustset security nat destination rule-set 1 rule 111 match source-address 0.0.0.0/0set security nat destination rule-set 1 rule 111 match destination-address 192.168.4.5/32set security nat destination rule-set 1 rule 111 match destination-port 3389set security nat destination rule-set 1 rule 111 then destination-nat pool 111set security nat destination rule-set 2 from zone CNC-trustset security nat destination rule-set 2 rule 222 match source-address 0.0.0.0/0set security nat destination rule-set 2 rule 222 match destination-address 192.168.5.5/32set security nat destination rule-set 2 rule 222 match destination-port 3389set security nat destination rule-set 2 rule 222 then destination-nat pool 111。