Abstract Interest Management Middleware for Networked Games
- 格式:pdf
- 大小:279.12 KB
- 文档页数:7
17© Shreekant W Shiralkar 2016S. W. Shiralkar, IT Through Experiential Learning , DOI 10.1007/978-1-4842-2421-2_3C ontext:C ollaborative Learning and Collective Understanding of E RPDuring our school days, my friends and I frequently engaged in discussing specific topics from our textbooks. Each one of us comprehended a specific aspect of the larger subject, and when we shared understanding or knowledge of the topic, we found that our collective understanding helped us raise each individual’s understanding much faster and deeper than individually struggling to comprehend the subject. Later, we even formalized the process during the examination period as we found the process helping learn quickly. During my college days, we practiced the technique further by forming study groups, and when having difficulty understanding a topic, we broke it into subtopics and distributed among the group for learning parts individually and then collectively sharing it with the rest of the group. The process helped each one of us in comprehending knowledge which appeared difficult and complex to us as individuals. The results of learning through a process of discussion were impressive and gave me insight into a few aspects of the concept formally known as “cooperative learning,” which defines the process of learning together rather than being passive individual receivers of knowledge (e.g., teacher lecturing and students hearing). This process allows learners to use cognitive skills of questioning and clarifying, extrapolating and summarizing.I n one of my assignments, I was engaged to train the top management of an organization on ERP and the impact of its implementation. I anticipated that it would be a huge challenge to engage top executives in this training, as most would have had some understanding already, and applying a conventional training process risked losing their attention if my co-trainer or I fell short of their expectations. While individually each top executive may have had generic knowledge of ERP , they certainly lacked comprehensive knowledge, and more specifically a seamless collective understanding of the subject, without any gaps due to individual interpretations or exposures. The task, therefore, was multifaceted: on one hand, I had to get them interested in learning aspects of which they lacked knowledge, and on the other, I had to encourage them to share their individual understandings of the subject, facilitating development of a collective learning.CHAPTER 3 ■ BIDDING GAME18F or a top executive, it is expected that he or she needs to take calculated risks inalmost every key decision, whether it’s bidding for a large contract or establishing price point while taking a privately held organization for public trading. The process of bidding involves awareness of collective knowledge of capability, assessment about competition, and expertise to apply judgment based on rational (and some irrational) criteria. In the knowledge-driven economy, the contributions of each employee, regardless of level, add up to the collective capability of the organization.W ith a view to facilitate collective learning in the shortest possible time for these top executives, I conceived a “Bidding Game” that leveraged cooperative learning to teach the ERP solution and the impact of its implementation in one session. The result in of Bidding Game was outstanding.T his is the premise of the game that will be explained in this chapter. The game also helps induce elements of social skills like effective communication and interpersonal and group skills in learning an otherwise abstract and complex subject.T he Bidding Game is a game played by all the participants divided into two or more teams. Teams compete on the strength of their collective knowledge of the subject. The game concludes after the collective learning on a specific subject is acquired to the appropriate level on all the essential aspects. The game format provides encouragement to each participant to contribute his or her knowledge of the subject and helps the team to win. A notional value attached to the correct and complete response helps measure the level of knowledge among participants. The competition is premised on the accuracy of the initial bid, which adds a flavor of bidding.F igure 3-1will help you visualize the setting created for the participants of the Bidding Game.F igure 3-1.I nstructor inviting b idsCHAPTER 3 ■ BIDDING GAME19In a hall, participants will be seated in a U-shaped arrangement, facing the projector screen. The hall will have two whiteboards on either side of the projector screen. One of the whiteboards will be titled “Knowledge Bid” and will display the bids by participating t eams.T he second whiteboard will record the actual earnings or the SCORE for each of the teams. The projector screen will be used to publish the question for each of the bid, and the instructor will allow the teams to respond in sequence and will record the score on the whiteboard on the basis of the accuracy and completeness of response by the team (Figure 3-2).F igure 3-2.I nstructor inviting response to q uestion In designing the Bidding Game, the elements of competition and encouraging discussion on each aspect form the core theme. The competitive aspect triggers speed, the game element induces interest without force or pressure, and finally discussions and sharing of knowledge facilitate desired coverage of the subject—for instance, technical nuances and features offered by new technology and/or processes, channelling an accelerated Learning and Collective Understanding new technology and/or p rocesses .B idding Game Design To design the Bidding Game, I recommend ensuring that the pace of learning is accelerated gradually, and that learning begins with basic aspects and moves on to the advanced and complex aspects in sequence instead of beginning with complex subjects and then concluding with basics. In the design of the sequence, care has to be exercised in segregating the basic and must-learn aspects from the “nice-to-know” aspects, andCHAPTER 3 ■ BIDDING GAME20design should ensure accomplishing learning of basic and must-learn ones whileprovisioning for nice-to-know types based on the interest and appetite of the participants. Design the sequence in such a way that initially the participant need to spend less time and are encouraged toward the game and competition, while later parts of the sequence should ensure that participants spend more time in discussions and staying ahead of competition.T he objective—rapid development of collective learning of technology and/or new processes—necessitates a short duration of the Bidding Game.L et us now examine the task-level details of the Bidding Game beginning with preparation/planning, recommended rules, and then the process for its execution,including steps to consolidate learning after conclusion. An overview of the entire game is depicted in Figure 3-3 .C omplete details of the activities in the process flow are described in detail in the following sections.P reparation/Planning •D ivide the subject into 20 subtopics that cover the subject comprehensively. • C reate a question for each of the subtopics.•C reate a sequence of questions in a way that gradually raises the level of knowledge. •S egment the questions into three levels: Rookie, Advanced, and Expert.•A ssign different values to questions from the three sets, for example, $100 per question from the Rookie level, $200 perquestion from the Advanced level, and $300 per question from the Expert level. •D evelop a clear rule set for the Bidding Game that can be used to explain the game to the participants.F igure 3-3.B idding Game p rocess flowCHAPTER 3 ■ BIDDING GAME • H ave a scoreboard that displays the bid value of the team and alsotheir score during the progress of the game (use the whiteboardmarker pens).• H ave a large clock for monitoring time and identify assistants forkeeping time and recording the score.R ecommended Rules• T he winner is chosen on the basis of two parameters: high scoreas well as that which is closest to its bid.• E ach wrong or incomplete response has a loss of value (i.e.,negative marking); for example, a $50 penalty for each wrong orincomplete response.• $50 is deducted from the value of a passed-over question or apartly answered question.• T he completeness of the response to a question can be challengedby competing teams to apply penalty and reduce the score.• T here’s a limit of 5 minutes for responding to each question. Eachround could begin sequence in a way that provides a fair chanceto all the teams.O nce all the preparation is completed, the game can begin.E xecution1. A ll the participants are told the context and rationale for thegame (i.e., what ERP is and the importance of each of themhaving a collective understanding of the subject, which wouldmaximize benefit from its implementation). Also, it shouldbe explained how playing a game such as this can increaseindividual understanding much faster and more deeply thanindividually struggling to comprehend the subject in isolation.2. P articipants are divided into teams. Team formation canbe done in any way that generates nearly equal numbers ofparticipants for each team (dividing the room, counting off bytwos, etc.)3. T he instructor/quiz master (QM) invites bids from each of theteams, which are recorded on the whiteboard for everyone tosee.4. T he instructor launches the first question on the screen andinvites the first team to take its chance, while the timekeepermonitors the time taken by the responding team.21CHAPTER 3 ■ BIDDING GAME225. O n the basis of correctness and completeness of the response,the instructor assigns a score to the team, which is recordedon the second whiteboard.6. I n case the question is passed to the second team and they areable to respond correctly and completely, the reduced score isrecorded.7. I n case the question is not answered or is incompletelyresponded by any of the teams, the instructor shares the correctand complete answer and the subject is discussed and clarified.8. T he process continues until the subject is completely covered.9. T he instructor tallies the scores for the teams and announcesthe winner on the basis of the high score and the bid a ccuracy .O nce the game is over, observations from experience are collected and crystallized inlearning in the next section.C onclusion• T he learning gained through the game needs to be articulatedand consolidated. Debrief is a process that will aid in articulatinglearning that participants gained during the game.• T he process of debrief begins with each participant sharinglearning, specifically something that has changed theirunderstanding about the subject during the game.• E ach participant would have learned something new, be it a verybasic addition to earlier knowledge of the subject or very complexinformation that the participant hadn’t ever known before.• T he individual learnings are recorded on a whiteboard, whichhelps in crystallizing and consolidating collective understandingon the subject.• O nce the game is over, the learning can be consolidated bypresenting additional material by way of slides, videos, and so on.S ample ArtifactsW ith a view to facilitate the immediate application of the approach in the chapter, a sample list of questions on ERP and Big Data along with an illustrative score sheet with result, are provided in the following section. The correct responses from multiple choices, are identified in bold.CHAPTER 3 ■ BIDDING GAMES ample Question Cards:ERP1. W hat is the extended form of ERP?a. E nterprise Retail Processb. E nterprise Resource Planningc. E arning Revenue and Profitd. N one of the above2. R eal time in the context of ERP relates to which of thefollowing?a. T ime shown in the computer system synchs with yourwatchb. P rocesses/events happen per transaction at the sameinstantc. B oth of the aboved. N one of the above3. W hat does “SOA” stand for in relation to ERP systemarchitecture?a. S ervice-Oriented Architectureb. S ystem of Accountsc. S tatement of Accountd. N one of the above4. W hich of these is not a packaged ERP?a. S APb. O raclec. W indowsd. J D Edwards5. I n the context of packaged ERP, do “Customization” and“Configuration” refer to the same process, or are theydifferent?a. S ameb. D ifferentc.D on’t know23CHAPTER 3 ■ BIDDING GAME246. M aterials Management in ERP helps to/esnure ?a. I ncrease of inventoryb. I nventory is well balancedc. B oth of the aboved. N one of the above7. S ales and Distribution Module in ERP helps in which of thefollowing?a. I ncreased customer serviceb. R educed customer servicec. B oth of the aboved. N one of the above8. F inancial and Controlling Module in ERP helps in which ofthe following?a. E valuating and responding to changing businessconditions with accurate, timely financial datab. E asy compliance with financial reporting requirementsc. S tandardizing and streamlining operationsd. A ll of the abovee. N one of the above9. G ain from implementation of ERP results in which of thefollowing?a. I mproved business performanceb. I mproved decision makingc. I ncreased ability to plan and growd. A ll of the aboveS ample Question Cards:B ig Data1. W hat is Big Data?a. D ata about big thingsb. D ata which is extremely large in size (in petabytes)c. D ata about datad. N one of the aboveCHAPTER 3 ■ BIDDING GAME2. W hich are not characteristics of Big Data?a. V olumeb.V elocityc. V irtualityd.V ariety3. W hich are key inputs for Big Data?a.I ncreased processing powerb. A vailability of tools and techniques for Big Datac. I ncreased storage capacitiesd. A ll of the above4. W hich are applications of Big Data?a. T argeted advertisingb.M onitoring telecom networkc. C ustomer sentimentsd. A ll of the above5. W hich tools are used for Big Data?a. N oSQLb. M apReducec. H adoop Distributed File Systemd. A ll of the above6. S ocial media and mobility are key contributors to Big Data:true or false?a. T rueb. F alse7. W hich is not a term related to Big Data?a. D atabasesMongoDBb. D ata T riggerc. P igd. S PARK25CHAPTER 3 ■ BIDDING GAME26B enefit Assessment After consolidation of the learning, it’s recommended to conduct a benefit assessment exercise to measure the gains from application of the game-based approach. Theassessment could be in form of a written quiz on the subject with multiple-choice answers.。

多用户MIMO-MEC网络中基于APSO的任务卸载研究顾敏;徐雅男;王辛迪;花敏;周雯【期刊名称】《无线电工程》【年(卷),期】2024(54)3【摘要】在移动边缘计算(Mobile Edge Computing,MEC)系统中引入多输入多输出(Multiple Input Multiple Output,MIMO)技术与数据压缩技术,能够降低数据冗余度和提高数据传输速率,从而降低任务的执行时延与能耗。
针对具备数据压缩功能的多用户MIMO-MEC网络,研究了多用户任务卸载问题。
通过联合优化任务卸载比例、数据压缩比例、发送功率、计算频率和信道带宽,来最小化系统总时延。
在能耗、功率和带宽等约束条件下,将任务卸载归纳为一个非凸优化问题。
由于能耗约束较为复杂,构造罚函数将其归并,得到一个相对简单的等价问题。
将所有优化变量视为一个粒子,基于自适应粒子群优化(Adaptive Particle Swarm Optimization,APSO)框架提出多用户的任务卸载方法。
由于粒子更新时可能违反约束条件,提出的方法对粒子越界的情形进行了特别处理。
该方法能自适应地调整惯性权重来提高寻优能力和收敛性,通过不断迭代最终获得最优或者次优解。
仿真实验评估了所提卸载方法的性能,分析了用户数、任务计算强度等参数对系统性能的影响。
结果表明,提出的方法优于本地计算、传统粒子群优化(Particle Swarm Optimization,PSO)算法等对比方案,能够有效降低系统的任务执行时延。
【总页数】8页(P711-718)【作者】顾敏;徐雅男;王辛迪;花敏;周雯【作者单位】南京林业大学信息科学技术学院;安徽大学互联网学院【正文语种】中文【中图分类】TN929.5;TP18【相关文献】1.基于延迟接受的多用户任务卸载策略2.基于稳定匹配的多用户任务卸载策略3.基于深度强化学习多用户移动边缘计算轻量任务卸载优化4.基于深度强化学习的多用户边缘计算任务卸载调度与资源分配算法5.基于博弈论的多服务器多用户视频分析任务卸载算法因版权原因,仅展示原文概要,查看原文内容请购买。
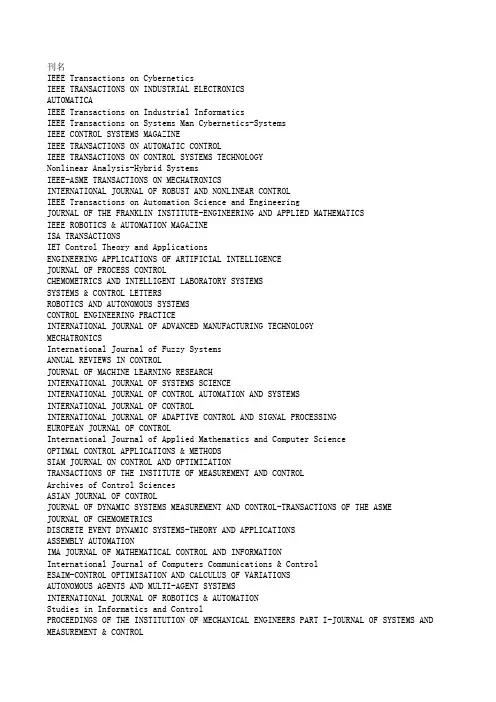
刊名IEEE Transactions on CyberneticsIEEE TRANSACTIONS ON INDUSTRIAL ELECTRONICSAUTOMATICAIEEE Transactions on Industrial InformaticsIEEE Transactions on Systems Man Cybernetics-SystemsIEEE CONTROL SYSTEMS MAGAZINEIEEE TRANSACTIONS ON AUTOMATIC CONTROLIEEE TRANSACTIONS ON CONTROL SYSTEMS TECHNOLOGYNonlinear Analysis-Hybrid SystemsIEEE-ASME TRANSACTIONS ON MECHATRONICSINTERNATIONAL JOURNAL OF ROBUST AND NONLINEAR CONTROLIEEE Transactions on Automation Science and EngineeringJOURNAL OF THE FRANKLIN INSTITUTE-ENGINEERING AND APPLIED MATHEMATICSIEEE ROBOTICS & AUTOMATION MAGAZINEISA TRANSACTIONSIET Control Theory and ApplicationsENGINEERING APPLICATIONS OF ARTIFICIAL INTELLIGENCEJOURNAL OF PROCESS CONTROLCHEMOMETRICS AND INTELLIGENT LABORATORY SYSTEMSSYSTEMS & CONTROL LETTERSROBOTICS AND AUTONOMOUS SYSTEMSCONTROL ENGINEERING PRACTICEINTERNATIONAL JOURNAL OF ADVANCED MANUFACTURING TECHNOLOGYMECHATRONICSInternational Journal of Fuzzy SystemsANNUAL REVIEWS IN CONTROLJOURNAL OF MACHINE LEARNING RESEARCHINTERNATIONAL JOURNAL OF SYSTEMS SCIENCEINTERNATIONAL JOURNAL OF CONTROL AUTOMATION AND SYSTEMSINTERNATIONAL JOURNAL OF CONTROLINTERNATIONAL JOURNAL OF ADAPTIVE CONTROL AND SIGNAL PROCESSINGEUROPEAN JOURNAL OF CONTROLInternational Journal of Applied Mathematics and Computer ScienceOPTIMAL CONTROL APPLICATIONS & METHODSSIAM JOURNAL ON CONTROL AND OPTIMIZATIONTRANSACTIONS OF THE INSTITUTE OF MEASUREMENT AND CONTROLArchives of Control SciencesASIAN JOURNAL OF CONTROLJOURNAL OF DYNAMIC SYSTEMS MEASUREMENT AND CONTROL-TRANSACTIONS OF THE ASME JOURNAL OF CHEMOMETRICSDISCRETE EVENT DYNAMIC SYSTEMS-THEORY AND APPLICATIONSASSEMBLY AUTOMATIONIMA JOURNAL OF MATHEMATICAL CONTROL AND INFORMATIONInternational Journal of Computers Communications & ControlESAIM-CONTROL OPTIMISATION AND CALCULUS OF VARIATIONSAUTONOMOUS AGENTS AND MULTI-AGENT SYSTEMSINTERNATIONAL JOURNAL OF ROBOTICS & AUTOMATIONStudies in Informatics and ControlPROCEEDINGS OF THE INSTITUTION OF MECHANICAL ENGINEERS PART I-JOURNAL OF SYSTEMS AND MEASUREMENT & CONTROLMATHEMATICS OF CONTROL SIGNALS AND SYSTEMSInformation Technology and ControlControl Engineering and Applied InformaticsJOURNAL OF DYNAMICAL AND CONTROL SYSTEMSMODELING IDENTIFICATION AND CONTROLINTELLIGENT AUTOMATION AND SOFT COMPUTINGJournal of Systems Engineering and ElectronicsAUTOMATION AND REMOTE CONTROLAT-AutomatisierungstechnikRevista Iberoamericana de Automatica e Informatica Industrial AutomatikaSLAS DiscoveryINTERNATIONAL JOURNAL OF COMPUTER VISIONIEEE TRANSACTIONS ON PATTERN ANALYSIS AND MACHINE INTELLIGENCE IEEE Transactions on CyberneticsIEEE TRANSACTIONS ON FUZZY SYSTEMSIEEE TRANSACTIONS ON EVOLUTIONARY COMPUTATIONIEEE Transactions on Neural Networks and Learning Systems NEURAL NETWORKSInformation FusionIEEE Computational Intelligence MagazineMEDICAL IMAGE ANALYSISIEEE TRANSACTIONS ON IMAGE PROCESSINGIEEE Transactions on Affective ComputingInternational Journal of Neural SystemsKNOWLEDGE-BASED SYSTEMSNEURAL COMPUTING & APPLICATIONSPATTERN RECOGNITIONAPPLIED SOFT COMPUTINGSwarm and Evolutionary ComputationARTIFICIAL INTELLIGENCE REVIEWEXPERT SYSTEMS WITH APPLICATIONSINTEGRATED COMPUTER-AIDED ENGINEERINGJOURNAL OF INTELLIGENT MANUFACTURINGDECISION SUPPORT SYSTEMSCognitive ComputationINTERNATIONAL JOURNAL OF INTELLIGENT SYSTEMSADVANCED ENGINEERING INFORMATICSNEUROCOMPUTINGARTIFICIAL INTELLIGENCEACM Transactions on Intelligent Systems and TechnologyIEEE Transactions on Autonomous Mental Development ARTIFICIAL INTELLIGENCE IN MEDICINEENGINEERING APPLICATIONS OF ARTIFICIAL INTELLIGENCEIEEE TRANSACTIONS ON KNOWLEDGE AND DATA ENGINEERING CHEMOMETRICS AND INTELLIGENT LABORATORY SYSTEMSInternational Journal of Machine Learning and CyberneticsROBOTICS AND AUTONOMOUS SYSTEMSFrontiers in NeuroroboticsIEEE INTELLIGENT SYSTEMSIEEE Transactions on Human-Machine SystemsDATA MINING AND KNOWLEDGE DISCOVERYMECHATRONICSInternational Journal of Fuzzy SystemsCOMPUTER VISION AND IMAGE UNDERSTANDINGEVOLUTIONARY COMPUTATIONSOFT COMPUTINGSIAM Journal on Imaging SciencesJOURNAL OF MACHINE LEARNING RESEARCHInternational Journal of Bio-Inspired ComputationKNOWLEDGE AND INFORMATION SYSTEMSAUTONOMOUS ROBOTSSemantic WebIMAGE AND VISION COMPUTINGFuzzy Optimization and Decision MakingInternational Journal of Computational Intelligence Systems APPLIED INTELLIGENCEIEEE Transactions on Cognitive and Developmental SystemsPATTERN RECOGNITION LETTERSWiley Interdisciplinary Reviews-Data Mining and Knowledge Discovery JOURNAL OF MATHEMATICAL IMAGING AND VISIONMemetic ComputingMACHINE LEARNINGIET BiometricsNEURAL PROCESSING LETTERSCOMPUTER SPEECH AND LANGUAGEINTERNATIONAL JOURNAL OF APPROXIMATE REASONINGINTERNATIONAL JOURNAL OF INFORMATION TECHNOLOGY & DECISION MAKING International Journal of Applied Mathematics and Computer Science NEURAL COMPUTATIONJOURNAL OF INTELLIGENT & ROBOTIC SYSTEMSJournal of Real-Time Image ProcessingSwarm IntelligenceJOURNAL OF CHEMOMETRICSDATA & KNOWLEDGE ENGINEERINGGenetic Programming and Evolvable MachinesEXPERT SYSTEMSJOURNAL OF INTELLIGENT & FUZZY SYSTEMSCognitive Systems ResearchJournal of Ambient Intelligence and Humanized ComputingIET Image ProcessingCOMPUTATIONAL INTELLIGENCEJournal of Web SemanticsJOURNAL OF AUTOMATED REASONINGCOMPUTATIONAL LINGUISTICSMACHINE VISION AND APPLICATIONSInternational Journal on Document Analysis and Recognition PATTERN ANALYSIS AND APPLICATIONSJOURNAL OF ARTIFICIAL INTELLIGENCE RESEARCHACM Transactions on Autonomous and Adaptive SystemsAUTONOMOUS AGENTS AND MULTI-AGENT SYSTEMSINTERNATIONAL JOURNAL OF UNCERTAINTY FUZZINESS AND KNOWLEDGE-BASED SYSTEMS Journal on Multimodal User InterfacesJOURNAL OF HEURISTICSJOURNAL OF INTELLIGENT INFORMATION SYSTEMSIET Computer VisionKNOWLEDGE ENGINEERING REVIEWAI EDAM-ARTIFICIAL INTELLIGENCE FOR ENGINEERING DESIGN ANALYSIS AND MANUFACTURING AI MAGAZINEINTERNATIONAL JOURNAL OF PATTERN RECOGNITION AND ARTIFICIAL INTELLIGENCE JOURNAL OF EXPERIMENTAL & THEORETICAL ARTIFICIAL INTELLIGENCEADAPTIVE BEHAVIORCONNECTION SCIENCEANNALS OF MATHEMATICS AND ARTIFICIAL INTELLIGENCEARTIFICIAL LIFEIEEE Transactions on Computational Intelligence and AI in GamesJournal of Ambient Intelligence and Smart EnvironmentsStatistical Analysis and Data MiningNatural ComputingMINDS AND MACHINESInformation Technology and ControlNatural Language EngineeringInternational Journal on Semantic Web and Information SystemsBiologically Inspired Cognitive ArchitecturesApplied OntologyNETWORK-COMPUTATION IN NEURAL SYSTEMSAdvances in Electrical and Computer EngineeringIntelligent Data AnalysisCONSTRAINTSINTELLIGENT AUTOMATION AND SOFT COMPUTINGMalaysian Journal of Computer ScienceAPPLIED ARTIFICIAL INTELLIGENCETurkish Journal of Electrical Engineering and Computer SciencesInternational Journal on Artificial Intelligence ToolsJOURNAL OF COMPUTER AND SYSTEMS SCIENCES INTERNATIONALJournal of Logic Language and InformationNeural Network WorldInternational Arab Journal of Information TechnologyAI COMMUNICATIONSJOURNAL OF MULTIPLE-VALUED LOGIC AND SOFT COMPUTINGCOMPUTING AND INFORMATICSINTERNATIONAL JOURNAL OF SOFTWARE ENGINEERING AND KNOWLEDGE ENGINEERINGACM Transactions on Asian and Low-Resource Language Information Processing Traitement du SignalIEEE Transactions on CyberneticsIEEE Transactions on Systems Man Cybernetics-SystemsIEEE Transactions on Affective ComputingHUMAN-COMPUTER INTERACTIONUSER MODELING AND USER-ADAPTED INTERACTIONIEEE Transactions on Human-Machine SystemsINTERNATIONAL JOURNAL OF HUMAN-COMPUTER STUDIESIEEE Transactions on HapticsBIOLOGICAL CYBERNETICSBEHAVIOUR & INFORMATION TECHNOLOGYMACHINE VISION AND APPLICATIONSINTERNATIONAL JOURNAL OF HUMAN-COMPUTER INTERACTIONCYBERNETICS AND SYSTEMSUniversal Access in the Information SocietyJournal on Multimodal User InterfacesKYBERNETESACM Transactions on Computer-Human InteractionINTERACTING WITH COMPUTERSMODELING IDENTIFICATION AND CONTROLKYBERNETIKAJOURNAL OF COMPUTER AND SYSTEMS SCIENCES INTERNATIONALPRESENCE-TELEOPERATORS AND VIRTUAL ENVIRONMENTSIEEE WIRELESS COMMUNICATIONSIEEE Transactions on Neural Networks and Learning SystemsIEEE NETWORKIEEE Transactions on Dependable and Secure ComputingJOURNAL OF NETWORK AND COMPUTER APPLICATIONSIEEE-ACM TRANSACTIONS ON NETWORKINGCOMMUNICATIONS OF THE ACMIEEE TRANSACTIONS ON COMPUTERSJournal of Optical Communications and NetworkingIEEE TRANSACTIONS ON RELIABILITYVLDB JOURNALComputer NetworksMOBILE NETWORKS & APPLICATIONSIEEE TRANSACTIONS ON COMPUTER-AIDED DESIGN OF INTEGRATED CIRCUITS AND SYSTEMS INTERNATIONAL JOURNAL OF HIGH PERFORMANCE COMPUTING APPLICATIONSCOMPUTERIEEE MICROIEEE MULTIMEDIAPERFORMANCE EVALUATIONCOMPUTERS & ELECTRICAL ENGINEERINGIEEE TRANSACTIONS ON VERY LARGE SCALE INTEGRATION (VLSI) SYSTEMSJOURNAL OF THE ACMACM Journal on Emerging Technologies in Computing SystemsIEEE Design & TestJOURNAL OF SUPERCOMPUTINGIEEE Computer Architecture LettersAdvances in ComputersJOURNAL OF COMPUTER AND SYSTEM SCIENCESCOMPUTER STANDARDS & INTERFACESIEEE Consumer Electronics MagazineSustainable Computing-Informatics & SystemsDISPLAYSACM Transactions on Embedded Computing SystemsACM Transactions on Architecture and Code OptimizationNETWORKSMICROPROCESSORS AND MICROSYSTEMSACM Transactions on Reconfigurable Technology and SystemsCANADIAN JOURNAL OF ELECTRICAL AND COMPUTER ENGINEERING-REVUE CANADIENNE DE GENIEIBM JOURNAL OF RESEARCH AND DEVELOPMENTACM Transactions on StorageJOURNAL OF SYSTEMS ARCHITECTUREINTEGRATION-THE VLSI JOURNALJOURNAL OF COMPUTER SCIENCE AND TECHNOLOGYACM TRANSACTIONS ON DESIGN AUTOMATION OF ELECTRONIC SYSTEMSCOMPUTER SYSTEMS SCIENCE AND ENGINEERINGANALOG INTEGRATED CIRCUITS AND SIGNAL PROCESSINGCOMPUTER JOURNALNEW GENERATION COMPUTINGIET Computers and Digital TechniquesJOURNAL OF CIRCUITS SYSTEMS AND COMPUTERSDESIGN AUTOMATION FOR EMBEDDED SYSTEMSIEICE TRANSACTIONS ON FUNDAMENTALS OF ELECTRONICS COMMUNICATIONS AND COMPUTER SCIENCES IEEE Communications Surveys and TutorialsIEEE WIRELESS COMMUNICATIONSIEEE Transactions on Cloud ComputingIEEE NETWORKIEEE Internet of Things JournalMIS QUARTERLYJOURNAL OF INFORMATION TECHNOLOGYIEEE Transactions on Services ComputingIEEE Transactions on Dependable and Secure ComputingIEEE Systems JournalJOURNAL OF STRATEGIC INFORMATION SYSTEMSINFORMATION SCIENCESJOURNAL OF THE AMERICAN MEDICAL INFORMATICS ASSOCIATIONIEEE TRANSACTIONS ON MOBILE COMPUTINGIEEE TRANSACTIONS ON MULTIMEDIAJournal of CheminformaticsINFORMATION & MANAGEMENTIEEE Journal of Biomedical and Health InformaticsInternet ResearchJournal of Chemical Information and ModelingIEEE Transactions on Emerging Topics in ComputingACM SIGCOMM Computer Communication ReviewDECISION SUPPORT SYSTEMSIEEE AccessINFORMATION PROCESSING & MANAGEMENTIEEE Transactions on Network and Service ManagementINFORMATION SYSTEMS FRONTIERSEUROPEAN JOURNAL OF INFORMATION SYSTEMSAd Hoc NetworksFoundations and Trends in Information RetrievalIEEE Wireless Communications LettersIEEE PERVASIVE COMPUTINGPervasive and Mobile ComputingACM Transactions on Intelligent Systems and TechnologyINTERNATIONAL JOURNAL OF MEDICAL INFORMATICSIEEE Cloud ComputingJournal of the Association for Information SystemsJournal of the Association for Information Science and TechnologyJournal of Grid ComputingIEEE TRANSACTIONS ON KNOWLEDGE AND DATA ENGINEERINGJOURNAL OF MANAGEMENT INFORMATION SYSTEMSJournal of Optical Communications and NetworkingVLDB JOURNALCOMPUTERS & SECURITYINFORMATION AND SOFTWARE TECHNOLOGYCOMPUTER COMMUNICATIONSBusiness & Information Systems EngineeringACM Transactions on Information and System SecurityElectronic Commerce Research and ApplicationsINFORMATION SYSTEMSComputer NetworksMOBILE NETWORKS & APPLICATIONSDATA MINING AND KNOWLEDGE DISCOVERYINTERNATIONAL JOURNAL OF GEOGRAPHICAL INFORMATION SCIENCEACM Transactions on Sensor NetworksKNOWLEDGE AND INFORMATION SYSTEMSSemantic WebScience China-Information SciencesIEEE TRANSACTIONS ON INFORMATION THEORYInternational Journal of Critical Infrastructure Protection GEOINFORMATICAACM Transactions on Multimedia Computing Communications and Applications WIRELESS NETWORKSHuman-centric Computing and Information SciencesJOURNAL OF INFORMATION SCIENCEPersonal and Ubiquitous ComputingIEEE MULTIMEDIAJOURNAL OF VISUAL COMMUNICATION AND IMAGE REPRESENTATIONInternational Journal of Distributed Sensor NetworksDigital InvestigationACM TRANSACTIONS ON INFORMATION SYSTEMSINTERNATIONAL JOURNAL OF INFORMATION TECHNOLOGY & DECISION MAKINGJournal of Network and Systems ManagementREQUIREMENTS ENGINEERINGJOURNAL OF THE ACMACM Transactions on Internet TechnologyMULTIMEDIA SYSTEMSEnterprise Information SystemsONLINE INFORMATION REVIEWInternational Journal of Information SecurityIT ProfessionalCluster Computing-The Journal of Networks Software Tools and Applications JOURNAL OF COMPUTER INFORMATION SYSTEMSMULTIMEDIA TOOLS AND APPLICATIONSMETHODS OF INFORMATION IN MEDICINEPeer-to-Peer Networking and ApplicationsACM Transactions on Knowledge Discovery from DataInformation Retrieval JournalDATA & KNOWLEDGE ENGINEERINGAslib Journal of Information ManagementJournal of Ambient Intelligence and Humanized ComputingJOURNAL OF ORGANIZATIONAL COMPUTING AND ELECTRONIC COMMERCE INFORMATICATSINGHUA SCIENCE AND TECHNOLOGYJournal of Web SemanticsInternational Journal of Network ManagementJournal of Internet TechnologyInternational Journal of Computers Communications & ControlSIGMOD RECORDINFORMATION SYSTEMS MANAGEMENTJOURNAL OF COMMUNICATIONS AND NETWORKSIEEE SECURITY & PRIVACYACM Transactions on Autonomous and Adaptive SystemsPHOTONIC NETWORK COMMUNICATIONSSustainable Computing-Informatics & SystemsPROGRAM-ELECTRONIC LIBRARY AND INFORMATION SYSTEMSACM Transactions on the WebWORLD WIDE WEB-INTERNET AND WEB INFORMATION SYSTEMSOptical Switching and NetworkingJOURNAL OF INTELLIGENT INFORMATION SYSTEMSFrontiers of Computer ScienceJournal of Signal Processing Systems for Signal Image and Video Technology International Journal of Web and Grid ServicesACM TRANSACTIONS ON DATABASE SYSTEMSNew Review of Hypermedia and MultimediaACM Transactions on Computer-Human InteractionINFORMATION TECHNOLOGY AND LIBRARIESIBM JOURNAL OF RESEARCH AND DEVELOPMENTMobile Information SystemsDISTRIBUTED AND PARALLEL DATABASESFrontiers of Information Technology & Electronic EngineeringSecurity and Communication NetworksIET Information SecurityACTA INFORMATICAInternational Journal of Sensor NetworksJournal of Ambient Intelligence and Smart EnvironmentsWIRELESS COMMUNICATIONS & MOBILE COMPUTINGInformation Technology and ControlINFORMATION PROCESSING LETTERSInternational Journal on Semantic Web and Information SystemsCOMPUTER JOURNALApplied OntologyAd Hoc & Sensor Wireless NetworksJournal of Organizational and End User ComputingInternational Journal of Ad Hoc and Ubiquitous ComputingComputer Science and Information SystemsKSII Transactions on Internet and Information SystemsIEEE Latin America TransactionsIEICE TRANSACTIONS ON INFORMATION AND SYSTEMSInternational Arab Journal of Information TechnologyACM Transactions on Privacy and SecurityInternational Journal of Web Services ResearchRAIRO-THEORETICAL INFORMATICS AND APPLICATIONSIEICE TRANSACTIONS ON FUNDAMENTALS OF ELECTRONICS COMMUNICATIONS AND COMPUTER SCIENCES JOURNAL OF INFORMATION SCIENCE AND ENGINEERINGINFORJOURNAL OF DATABASE MANAGEMENTINTERNATIONAL JOURNAL OF COOPERATIVE INFORMATION SYSTEMSJournal of Statistical SoftwareARCHIVES OF COMPUTATIONAL METHODS IN ENGINEERINGIEEE TRANSACTIONS ON MEDICAL IMAGINGCOMPUTER-AIDED CIVIL AND INFRASTRUCTURE ENGINEERINGIEEE Transactions on Industrial InformaticsMEDICAL IMAGE ANALYSISCOMPUTERS & EDUCATIONJOURNAL OF THE AMERICAN MEDICAL INFORMATICS ASSOCIATIONENVIRONMENTAL MODELLING & SOFTWAREJOURNAL OF NETWORK AND COMPUTER APPLICATIONSAPPLIED SOFT COMPUTINGJournal of CheminformaticsNEUROINFORMATICSIEEE Journal of Biomedical and Health InformaticsJournal of Chemical Information and ModelingCOMPUTER PHYSICS COMMUNICATIONSINTEGRATED COMPUTER-AIDED ENGINEERINGJournal of InformetricsROBOTICS AND COMPUTER-INTEGRATED MANUFACTURINGSOCIAL SCIENCE COMPUTER REVIEWADVANCES IN ENGINEERING SOFTWARECOMPUTERS & INDUSTRIAL ENGINEERINGCOMPUTERS AND GEOTECHNICSCOMPUTERS & CHEMICAL ENGINEERINGCOMPUTERS & OPERATIONS RESEARCHINDUSTRIAL MANAGEMENT & DATA SYSTEMSCOMPUTERS & STRUCTURESJOURNAL OF BIOMEDICAL INFORMATICSSTRUCTURAL AND MULTIDISCIPLINARY OPTIMIZATIONJOURNAL OF COMPUTATIONAL PHYSICSCOMPUTERS IN INDUSTRYAstronomy and ComputingCOMPUTATIONAL GEOSCIENCESCOMPUTER METHODS AND PROGRAMS IN BIOMEDICINEElectronic Commerce Research and ApplicationsMATCH-COMMUNICATIONS IN MATHEMATICAL AND IN COMPUTER CHEMISTRYCOMPUTERS & GEOSCIENCESIEEE-ACM Transactions on Computational Biology and BioinformaticsCOMPUTERS AND ELECTRONICS IN AGRICULTURESOFT COMPUTINGJOURNAL OF COMPUTER-AIDED MOLECULAR DESIGNSAR AND QSAR IN ENVIRONMENTAL RESEARCHCOMPUTERS & FLUIDSSCIENTOMETRICSCOMPUTERS IN BIOLOGY AND MEDICINESIMULATION MODELLING PRACTICE AND THEORYIEEE TRANSACTIONS ON COMPUTER-AIDED DESIGN OF INTEGRATED CIRCUITS AND SYSTEMS INTERNATIONAL JOURNAL OF HIGH PERFORMANCE COMPUTING APPLICATIONSInternational Journal of Computational Intelligence SystemsINTERNATIONAL JOURNAL OF COMPUTER INTEGRATED MANUFACTURINGCOMPUTER METHODS IN BIOMECHANICS AND BIOMEDICAL ENGINEERINGMEDICAL & BIOLOGICAL ENGINEERING & COMPUTINGMolecular InformaticsENGINEERING WITH COMPUTERSJournal of Computational ScienceJOURNAL OF MOLECULAR GRAPHICS & MODELLINGIEEE Transactions on Learning TechnologiesJOURNAL OF COMPUTING IN CIVIL ENGINEERINGJOURNAL OF HYDROINFORMATICSDigital InvestigationINTERNATIONAL JOURNAL OF INFORMATION TECHNOLOGY & DECISION MAKINGCOMPUTERS & ELECTRICAL ENGINEERINGINTERNATIONAL JOURNAL FOR NUMERICAL METHODS IN FLUIDSComputers and ConcreteEarth Science InformaticsJOURNAL OF COMPUTING AND INFORMATION SCIENCE IN ENGINEERINGSPEECH COMMUNICATIONJOURNAL OF MOLECULAR MODELINGBig DataMATHEMATICS AND COMPUTERS IN SIMULATIONCONCURRENT ENGINEERING-RESEARCH AND APPLICATIONSJOURNAL OF ORGANIZATIONAL COMPUTING AND ELECTRONIC COMMERCECOMPUTATIONAL BIOLOGY AND CHEMISTRYINFORMS JOURNAL ON COMPUTINGVIRTUAL REALITYR JournalCOMPUTATIONAL LINGUISTICSINTERNATIONAL JOURNAL OF RF AND MICROWAVE COMPUTER-AIDED ENGINEERINGJournal of SimulationJOURNAL OF COMPUTATIONAL BIOLOGYCOMPUTATIONAL STATISTICS & DATA ANALYSISENGINEERING COMPUTATIONSQUEUEING SYSTEMSCOMPUTER APPLICATIONS IN ENGINEERING EDUCATIONCOMPUTING IN SCIENCE & ENGINEERINGCIN-COMPUTERS INFORMATICS NURSINGAI EDAM-ARTIFICIAL INTELLIGENCE FOR ENGINEERING DESIGN ANALYSIS AND MANUFACTURING JOURNAL OF NEW MUSIC RESEARCHJOURNAL OF VISUALIZATIONSIMULATION-TRANSACTIONS OF THE SOCIETY FOR MODELING AND SIMULATION INTERNATIONAL ACM Transactions on Modeling and Computer SimulationJOURNAL OF COMBINATORIAL OPTIMIZATIONINTERNATIONAL JOURNAL OF MODERN PHYSICS CJOURNAL OF STATISTICAL COMPUTATION AND SIMULATIONStatistical Analysis and Data MiningCurrent Computer-Aided Drug DesignComputer Supported Cooperative Work-The Journal of Collaborative Computing Language Resources and EvaluationComputational and Mathematical Organization TheoryMATHEMATICAL AND COMPUTER MODELLING OF DYNAMICAL SYSTEMSCOMPUTER MUSIC JOURNALInternational Journal on Artificial Intelligence ToolsCOMPEL-THE INTERNATIONAL JOURNAL FOR COMPUTATION AND MATHEMATICS IN ELECTRICAL AND ACM Journal on Computing and Cultural HeritageAPPLICABLE ALGEBRA IN ENGINEERING COMMUNICATION AND COMPUTINGIEEE Transactions on Services ComputingIEEE Transactions on Dependable and Secure ComputingACM TRANSACTIONS ON GRAPHICSJOURNAL OF NETWORK AND COMPUTER APPLICATIONSIEEE TRANSACTIONS ON MULTIMEDIAIEEE TRANSACTIONS ON SOFTWARE ENGINEERINGADVANCES IN ENGINEERING SOFTWAREIEEE TRANSACTIONS ON VISUALIZATION AND COMPUTER GRAPHICSCOMMUNICATIONS OF THE ACMCOMPUTER-AIDED DESIGNEMPIRICAL SOFTWARE ENGINEERINGACM TRANSACTIONS ON MATHEMATICAL SOFTWAREIEEE SOFTWAREIEEE TRANSACTIONS ON RELIABILITYMATHEMATICAL PROGRAMMINGINFORMATION AND SOFTWARE TECHNOLOGYINTERNATIONAL JOURNAL OF ELECTRONIC COMMERCESIAM Journal on Imaging SciencesJOURNAL OF SYSTEMS AND SOFTWAREIMAGE AND VISION COMPUTINGSIMULATION MODELLING PRACTICE AND THEORYCOMPUTER GRAPHICS FORUMACM Transactions on Multimedia Computing Communications and ApplicationsACM TRANSACTIONS ON SOFTWARE ENGINEERING AND METHODOLOGYCOMPUTERIEEE INTERNET COMPUTINGJOURNAL OF MATHEMATICAL IMAGING AND VISIONIEEE MICROIEEE MULTIMEDIACOMPUTER LANGUAGES SYSTEMS & STRUCTURESJOURNAL OF VISUAL COMMUNICATION AND IMAGE REPRESENTATIONAutomated Software EngineeringREQUIREMENTS ENGINEERINGJOURNAL OF THE ACMACM Transactions on Internet TechnologySoftware and Systems ModelingInternational Journal of Information SecurityIEEE COMPUTER GRAPHICS AND APPLICATIONSIT ProfessionalSOFTWARE QUALITY JOURNALSOFTWARE TESTING VERIFICATION & RELIABILITYMULTIMEDIA TOOLS AND APPLICATIONSCOMPUTER AIDED GEOMETRIC DESIGNAdvances in ComputersACM Transactions on Knowledge Discovery from DataMATHEMATICS AND COMPUTERS IN SIMULATIONCOMPUTER STANDARDS & INTERFACESBIT NUMERICAL MATHEMATICSVIRTUAL REALITYTSINGHUA SCIENCE AND TECHNOLOGYJournal of Web SemanticsScientific ProgrammingSOFTWARE-PRACTICE & EXPERIENCESIGMOD RECORDIEEE SECURITY & PRIVACYCOMPUTERS & GRAPHICS-UKOPTIMIZATION METHODS & SOFTWAREJournal of Software-Evolution and ProcessACM Transactions on the WebACM Transactions on Embedded Computing SystemsWORLD WIDE WEB-INTERNET AND WEB INFORMATION SYSTEMSCONCURRENCY AND COMPUTATION-PRACTICE & EXPERIENCEFrontiers of Computer ScienceInternational Journal on Software Tools for Technology TransferInternational Journal of Web and Grid ServicesJOURNAL OF UNIVERSAL COMPUTER SCIENCEVISUAL COMPUTERGRAPHICAL MODELSACM TRANSACTIONS ON DATABASE SYSTEMSRANDOM STRUCTURES & ALGORITHMSJOURNAL OF VISUAL LANGUAGES AND COMPUTINGACM Transactions on Applied PerceptionIBM JOURNAL OF RESEARCH AND DEVELOPMENTIET SoftwareSIMULATION-TRANSACTIONS OF THE SOCIETY FOR MODELING AND SIMULATION INTERNATIONAL ACM Transactions on StorageInformation VisualizationJOURNAL OF SYSTEMS ARCHITECTUREFrontiers of Information Technology & Electronic EngineeringIEEE Transactions on Computational Intelligence and AI in GamesJOURNAL OF COMPUTER SCIENCE AND TECHNOLOGYTHEORY AND PRACTICE OF LOGIC PROGRAMMINGACM TRANSACTIONS ON DESIGN AUTOMATION OF ELECTRONIC SYSTEMSFORMAL ASPECTS OF COMPUTINGCOMPUTER JOURNALInternational Journal of Data Warehousing and MiningACM TRANSACTIONS ON PROGRAMMING LANGUAGES AND SYSTEMSSCIENCE OF COMPUTER PROGRAMMINGFUNDAMENTA INFORMATICAEJOURNAL OF FUNCTIONAL PROGRAMMINGCOMPUTER ANIMATION AND VIRTUAL WORLDSALGORITHMICAComputer Science and Information SystemsDISCRETE MATHEMATICS AND THEORETICAL COMPUTER SCIENCEInternational Journal of Wavelets Multiresolution and Information Processing DESIGN AUTOMATION FOR EMBEDDED SYSTEMSIEICE TRANSACTIONS ON INFORMATION AND SYSTEMSPRESENCE-TELEOPERATORS AND VIRTUAL ENVIRONMENTSInternational Journal of Web Services ResearchINTERNATIONAL JOURNAL OF SOFTWARE ENGINEERING AND KNOWLEDGE ENGINEERING ICGA JOURNALJournal of Web EngineeringPROGRAMMING AND COMPUTER SOFTWAREJOURNAL OF DATABASE MANAGEMENTIEEE TRANSACTIONS ON EVOLUTIONARY COMPUTATIONIEEE Transactions on Neural Networks and Learning SystemsIEEE Transactions on Cloud ComputingInformation FusionIEEE Transactions on Information Forensics and SecurityACM COMPUTING SURVEYSFuture Generation Computer Systems-The International Journal of eScience IEEE TRANSACTIONS ON PARALLEL AND DISTRIBUTED SYSTEMSSwarm and Evolutionary ComputationHUMAN-COMPUTER INTERACTIONINFORMATION SYSTEMS FRONTIERSIEEE-ACM TRANSACTIONS ON NETWORKINGCOMMUNICATIONS OF THE ACMFOUNDATIONS OF COMPUTATIONAL MATHEMATICSINTERNATIONAL JOURNAL OF GENERAL SYSTEMSIEEE Cloud ComputingJournal of Grid ComputingFUZZY SETS AND SYSTEMSCOMPUTER METHODS AND PROGRAMS IN BIOMEDICINEEVOLUTIONARY COMPUTATIONJOURNAL OF SYSTEMS AND SOFTWAREInternational Journal of Bio-Inspired ComputationSemantic WebINTERNATIONAL JOURNAL OF SYSTEMS SCIENCEIMAGE AND VISION COMPUTINGMULTIDIMENSIONAL SYSTEMS AND SIGNAL PROCESSINGACM Transactions on Multimedia Computing Communications and Applications INTERNATIONAL JOURNAL OF HIGH PERFORMANCE COMPUTING APPLICATIONSWiley Interdisciplinary Reviews-Data Mining and Knowledge DiscoveryJournal of Computational ScienceIEEE MULTIMEDIASTATISTICS AND COMPUTINGJOURNAL OF PARALLEL AND DISTRIBUTED COMPUTINGPERFORMANCE EVALUATIONACM TRANSACTIONS ON COMPUTER SYSTEMSJOURNAL OF THE ACMMULTIMEDIA SYSTEMSInternational Journal of Information SecurityCOMPUTINGCluster Computing-The Journal of Networks Software Tools and Applications QUANTUM INFORMATION & COMPUTATIONREAL-TIME SYSTEMSMULTIMEDIA TOOLS AND APPLICATIONSJOURNAL OF SUPERCOMPUTINGJOURNAL OF COMPUTER AND SYSTEM SCIENCESBig DataGenetic Programming and Evolvable MachinesEXPERT SYSTEMSACM Transactions on Autonomous and Adaptive SystemsCryptography and Communications-Discrete-Structures Boolean Functions and Sequences ACM Transactions on Architecture and Code OptimizationJOURNAL OF HEURISTICSCONCURRENCY AND COMPUTATION-PRACTICE & EXPERIENCEDESIGNS CODES AND CRYPTOGRAPHYFrontiers of Computer ScienceMATHEMATICAL STRUCTURES IN COMPUTER SCIENCEINFORMATION AND COMPUTATIONJOURNAL OF UNIVERSAL COMPUTER SCIENCEJOURNAL OF CRYPTOLOGYMICROPROCESSORS AND MICROSYSTEMSInternational Journal of Unconventional ComputingIBM JOURNAL OF RESEARCH AND DEVELOPMENTPARALLEL COMPUTINGCONNECTION SCIENCEDISTRIBUTED AND PARALLEL DATABASESSIAM JOURNAL ON COMPUTINGARTIFICIAL LIFEINTERNATIONAL JOURNAL OF PARALLEL PROGRAMMINGIET Information SecurityTHEORY AND PRACTICE OF LOGIC PROGRAMMINGNatural ComputingCOMPUTER SYSTEMS SCIENCE AND ENGINEERINGDISTRIBUTED COMPUTINGFORMAL METHODS IN SYSTEM DESIGNCOMPUTER JOURNALApplied OntologyTHEORETICAL COMPUTER SCIENCEJOURNAL OF SYMBOLIC COMPUTATIONJOURNAL OF LOGIC AND COMPUTATIONINTERNATIONAL JOURNAL OF QUANTUM INFORMATIONACM Transactions on Computational LogicNEW GENERATION COMPUTINGCOMBINATORICS PROBABILITY & COMPUTINGDISCRETE & COMPUTATIONAL GEOMETRY。
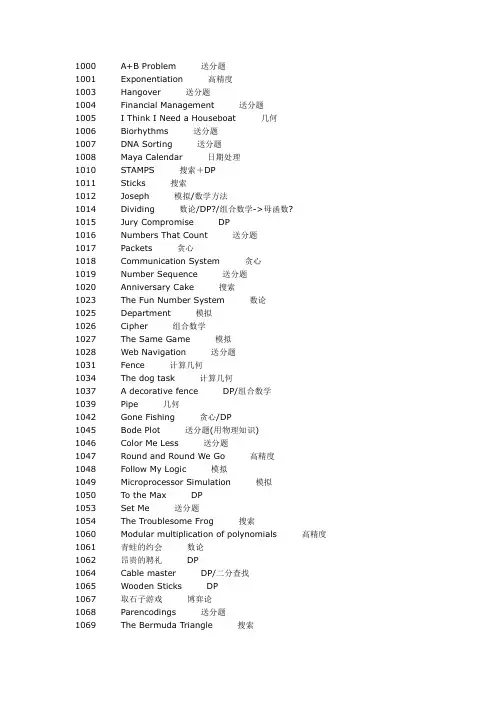
1000 A+B Problem 送分题1001 Exponentiation 高精度1003 Hangover 送分题1004 Financial Management 送分题1005 I Think I Need a Houseboat 几何1006 Biorhythms 送分题1007 DNA Sorting 送分题1008 Maya Calendar 日期处理1010 STAMPS 搜索+DP1011 Sticks 搜索1012 Joseph 模拟/数学方法1014 Dividing 数论/DP?/组合数学->母函数?1015 Jury Compromise DP1016 Numbers That Count 送分题1017 Packets 贪心1018 Communication System 贪心1019 Number Sequence 送分题1020 Anniversary Cake 搜索1023 The Fun Number System 数论1025 Department 模拟1026 Cipher 组合数学1027 The Same Game 模拟1028 Web Navigation 送分题1031 Fence 计算几何1034 The dog task 计算几何1037 A decorative fence DP/组合数学1039 Pipe 几何1042 Gone Fishing 贪心/DP1045 Bode Plot 送分题(用物理知识)1046 Color Me Less 送分题1047 Round and Round We Go 高精度1048 Follow My Logic 模拟1049 Microprocessor Simulation 模拟1050 To the Max DP1053 Set Me 送分题1054 The Troublesome Frog 搜索1060 Modular multiplication of polynomials 高精度1061 青蛙的约会数论1062 昂贵的聘礼DP1064 Cable master DP/二分查找1065 Wooden Sticks DP1067 取石子游戏博弈论1068 Parencodings 送分题1069 The Bermuda Triangle 搜索1070 Deformed Wheel 几何1071 Illusive Chase 送分题1072 Puzzle Out 搜索1073 The Willy Memorial Program 模拟1074 Parallel Expectations DP1075 University Entrance Examination 模拟1080 Human Gene Functions DP->LCS变形1082 Calendar Game 博弈论1084 Square Destroyer 搜索?1085 Triangle War 博弈论1086 Unscrambling Images 模拟?1087 A Plug for UNIX 图论->最大流1088 滑雪DFS/DP1090 Chain ->格雷码和二进制码的转换1091 跳蚤数论1092 Farmland 几何1093 Formatting Text DP1094 Sorting It All Out 图论->拓扑排序1095 Trees Made to Order 组合数学1096 Space Station Shielding 送分题1097 Roads Scholar 图论1098 Robots 模拟1099 Square Ice 送分题1100 Dreisam Equations 搜索1101 The Game 搜索->BFS1102 LC-Display 送分题1103 Maze 模拟1104 Robbery 递推1106 Transmitters 几何1107 W's Cipher 送分题1110 Double Vision 搜索1111 Image Perimeters 搜索1112 Team Them Up! DP1113 Wall 计算几何->convex hull1119 Start Up the Startup 送分题1120 A New Growth Industry 模拟1122 FDNY to the Rescue! 图论->Dijkstra 1125 Stockbroker Grapevine 图论->Dijkstra 1128 Frame Stacking 搜索1129 Channel Allocation 搜索(图的最大独立集)1131 Octal Fractions 高精度1135 Domino Effect 图论->Dijkstra1137 The New Villa 搜索->BFS1141 Brackets Sequence DP1142 Smith Numbers 搜索1143 Number Game 博弈论1147 Binary codes 构造1148 Utopia Divided 构造1149 PIGS 图论->网络流1151 Atlantis 计算几何->同等安置矩形的并的面积->离散化1152 An Easy Problem! 数论1157 LITTLE SHOP OF FLOWERS DP1158 TRAFFIC LIGHTS 图论->Dijkstra变形1159 Palindrome DP->LCS1160 Post Office DP1161 Walls 图论1162 Building with Blocks 搜索1163 The Triangle DP1170 Shopping Offers DP1177 Picture 计算几何->同等安置矩形的并的周长->线段树1179 Polygon DP1180 Batch Scheduling DP1182 食物链数据结构->并查集1183 反正切函数的应用搜索1184 聪明的打字员搜索1185 炮兵阵地DP->数据压缩1187 陨石的秘密DP(BalkanOI99 Par的拓展)1189 钉子和小球递推?1190 生日蛋糕搜索/DP1191 棋盘分割DP1192 最优连通子集图论->无负权回路的有向图的最长路->BellmanFord 1193 内存分配模拟1194 HIDDEN CODES 搜索+DP1197 Depot 数据结构->Young T ableau1201 Intervals 贪心/图论->最长路->差分约束系统1202 Family 高精度1209 Calendar 日期处理1217 FOUR QUARTERS 递推1218 THE DRUNK JAILER 送分题1233 Street Crossing 搜索->BFS1245 Programmer, Rank Thyself 送分题1247 Magnificent Meatballs 送分题1248 Safecracker 搜索1250 T anning Salon 送分题1251 Jungle Roads 图论->最小生成树1271 Nice Milk 计算几何1273 Drainage Ditches 图论->最大流1274 The Perfect Stall 图论->二分图的最大匹配1275 Cashier Employment 图论->差分约束系统->无负权回路的有向图的最长路->Bellman-Ford1280 Game 递推1281 MANAGER 模拟1286 Necklace of Beads 组合数学->Polya定理1288 Sly Number 数论->解模线性方程组1293 Duty Free Shop DP1298 The Hardest Problem Ever 送分题1316 Self Numbers 递推同Humble Number一样1322 Chocolate 递推/组合数学1323 Game Prediction 贪心1324 Holedox Moving BFS+压缩储存1325 Machine Schedule 图论->二分图的最大匹配1326 Mileage Bank 送分题1327 Moving Object Recognition 模拟?1328 Radar Installation 贪心(差分约束系统的特例)1338 Ugly Numbers 递推(有O(n)算法)1364 King 图论->无负权回路的有向图的最长路->BellmanFord1370 Gossiping (数论->模线性方程有无解的判断)+(图论->DFS)2184 Cow Exhibition DP2190 ISBN 送分题2191 Mersenne Composite Numbers 数论2192 Zipper DP->LCS变形2193 Lenny's Lucky Lotto Lists DP2194 Stacking Cylinders 几何2195 Going Home 图论->二分图的最大权匹配2196 Specialized Four-Digit Numbers 送分题2197 Jill's Tour Paths 图论->2199 Rate of Return 高精度2200 A Card Trick 模拟2210 Metric Time 日期处理2239 Selecting Courses 图论->二分图的最大匹配2243 Knight Moves 搜索->BFS2247 Humble Numbers 递推(最优O(n)算法)2253 Frogger 图论->Dijkstra变形(和1295是一样的)2254 Globetrotter 几何2261 France '98 递推2275 Flipping Pancake 构造2284 That Nice Euler Circuit 计算几何2289 Jamie's Contact Groups 图论->网络流?2291 Rotten Ropes 送分题2292 Optimal Keypad DP2299 Ultra-QuickSort 排序->归并排序2304 Combination Lock 送分题2309 BST 送分题2311 Cutting Game 博弈论2312 Battle City 搜索->BFS2314 POJ language 模拟2315 Football Game 几何2346 Lucky tickets 组合数学2351 Time Zones 时间处理2379 ACM Rank T able 模拟+排序2381 Random Gap 数论2385 Apple Catching DP(像NOI98“免费馅饼”)2388 Who's in the Middle 送分题(排序)2390 Bank Interest 送分题2395 Out of Hay 图论->Dijkstra变形2400 Supervisor, Supervisee 图论->二分图的最大权匹配?2403 Hay Points 送分题2409 Let it Bead 组合数学->Polya定理2416 Return of the Jedi 图论->2417 Discrete Logging 数论2418 Hardwood Species 二分查找2419 Forests 枚举2421 Constructing Roads 图论->最小生成树2423 The Parallel Challenge Ballgame 几何2424 Flo's Restaurant 数据结构->堆2425 A Chess Game 博弈论2426 Remainder BFS2430 Lazy Cows DP->数据压缩1375 Intervals 几何1379 Run Away 计算几何->1380 Equipment Box 几何1383 Labyrinth 图论->树的最长路1394 Railroad 图论->Dijkstra1395 Cog-Wheels 数学->解正系数的线性方程组1408 Fishnet 几何1411 Calling Extraterrestrial Intelligence Again 送分题1430 Binary Stirling Numbers 日期处理1431 Calendar of Maya 模拟1432 Decoding Morse Sequences DP1434 Fill the Cisterns! 计算几何->离散化/1445 Random number 数据结构->碓1447 Ambiguous Dates 日期处理1450 Gridland 图论(本来TSP问题是NP难的,但这个图比较特殊,由现成的构造方法)1458 Common Subsequence DP->LCS1459 Power Network 图论->最大流1462 Random Walk 模拟+解线性方程组1463 Strategic game 贪心1466 Girls and Boys 图论->n/a1469 COURSES 贪心1475 Pushing Boxes DP1476 Always On the Run 搜索->BFS1480 Optimal Programs 搜索->BFS1481 The Die Is Cast 送分题1482 It's not a Bug, It's a Feature! 搜索->BFS1483 Going in Circles on Alpha Centauri 模拟1484 Blowing Fuses 送分题1485 Fast Food DP(似乎就是ioi2000的postoffice)1486 Sorting Slides 图论->拓扑排序1505 Copying Books DP+二分查找1510 Hares and Foxes 数论1512 Keeps Going and Going and ... 模拟1513 Scheduling Lectures DP1514 Metal Cutting 几何1515 Street Directions 图论->把一个无向连通图改造成为有向强连通图1517 u Calculate e 送分题1518 Problem Bee 几何1519 Digital Roots 送分题(位数可能很大)1520 Scramble Sort 排序1547 Clay Bully 送分题1555 Polynomial Showdown 送分题(非常阴险)1563 The Snail 送分题1601 Pizza Anyone? 搜索1604 Just the Facts 送分题1605 Horse Shoe Scoring 几何1606 Jugs 数论/搜索1631 Bridging signals DP+二分查找1632 Vase collection 图论->最大完全图1633 Gladiators DP1634 Who's the boss? 排序1635 Subway tree systems 图论->不同表示法的二叉树判同1637 Sightseeing tour 图论->欧拉回路1638 A number game 博弈论1639 Picnic Planning 图论->1641 Rational Approximation 数论1646 Double Trouble 高精度1654 Area 几何1657 Distance on Chessboard 送分题1658 Eva's Problem 送分题1660 Princess FroG 构造1661 Help Jimmy DP1663 Number Steps 送分题1664 放苹果组合数学->递推1677 Girls' Day 送分题1688 Dolphin Pool 计算几何1690 (Your)((Term)((Project))) 送分题1691 Painting A Board 搜索/DP1692 Crossed Matchings DP1693 Counting Rectangles 几何1694 An Old Stone Game 博弈论?1695 Magazine Delivery 图论->1712 Flying Stars DP1713 Divide et unita 搜索1714 The Cave 搜索/DP1717 Dominoes DP1718 River Crossing DP1719 Shooting Contest 贪心1729 Jack and Jill 图论->1730 Perfect Pth Powers 数论1732 Phone numbers DP1734 Sightseeing trip 图论->Euler回路1738 An old Stone Game 博弈论?1741 Tree 博弈论?1745 Divisibility DP1751 Highways 图论->1752 Advertisement 贪心/图论->差分约束系统1753 Flip Game 搜索->BFS1755 Triathlon 计算几何?1770 Special Experiment 树形DP1771 Elevator Stopping Plan DP1772 New Go Game 构造?1773 Outernet 模拟1774 Fold Paper Strips 几何1775 Sum of Factorials 送分题1776 T ask Sequences DP1777 Vivian's Problem 数论1870 Bee Breeding 送分题1871 Bullet Hole 几何1872 A Dicey Problem BFS1873 The Fortified Forest 几何+回溯1874 Trade on Verweggistan DP1875 Robot 几何1876 The Letter Carrier's Rounds 模拟1877 Flooded! 数据结构->堆1879 Tempus et mobilius Time and motion 模拟+组合数学->Polya定理1882 Stamps 搜索+DP1883 Theseus and the Minotaur 模拟1887 Testing the CATCHER DP1889 Package Pricing DP1893 Monitoring Wheelchair Patients 模拟+几何1915 Knight Moves 搜索->BFS1916 Rat Attack 数据结构->?1936 All in All DP?1946 Cow Cycling DP1947 Rebuilding Roads 二分1985 Cow Marathon 图论->有向无环图的最长路1995 Raising Modulo Numbers 数论->大数的幂求余2049 Finding Nemo 图论->最短路2050 Searching the Web 模拟(需要高效实现)2051 Argus 送分题(最好用堆,不用也可以过)2054 Color a Tree 贪心2061 Pseudo-random Numbers 数论2080 Calendar 日期处理2082 Terrible Sets 分治/2083 Fractal 递归2084 Game of Connections 递推(不必高精度)2105 IP Address 送分题2115 C Looooops 数论->解模线性方程2136 Vertical Histogram 送分题2165 Gunman 计算几何2179 Inlay Cutters 枚举2181 Jumping Cows 递推2182 Lost Cows ->线段树/=============================================1370 Gossiping (数论->模线性方程有无解的判断)+(图论->DFS)1090 Chain ->格雷码和二进制码的转换2182 Lost Cows ->线段树/2426 Remainder BFS1872 A Dicey Problem BFS1324 Holedox Moving BFS+压缩储存1088 滑雪DFS/DP1015 Jury Compromise DP1050 To the Max DP1062 昂贵的聘礼DP1065 Wooden Sticks DP1074 Parallel Expectations DP1093 Formatting Text DP1112 Team Them Up! DP1141 Brackets Sequence DP1157 LITTLE SHOP OF FLOWERS DP1160 Post Office DP1163 The Triangle DP1170 Shopping Offers DP1179 Polygon DP1180 Batch Scheduling DP1191 棋盘分割DP1293 Duty Free Shop DP2184 Cow Exhibition DP2193 Lenny's Lucky Lotto Lists DP2292 Optimal Keypad DP1432 Decoding Morse Sequences DP1475 Pushing Boxes DP1513 Scheduling Lectures DP1633 Gladiators DP1661 Help Jimmy DP1692 Crossed Matchings DP1712 Flying Stars DP1717 Dominoes DP1718 River Crossing DP1732 Phone numbers DP1745 Divisibility DP1771 Elevator Stopping Plan DP1776 T ask Sequences DP1874 Trade on Verweggistan DP1887 Testing the CATCHER DP1889 Package Pricing DP1946 Cow Cycling DP1187 陨石的秘密DP(BalkanOI99 Par的拓展)1485 Fast Food DP(似乎就是ioi2000的postoffice) 2385 Apple Catching DP(像NOI98“免费馅饼”) 1064 Cable master DP/二分查找1037 A decorative fence DP/组合数学1936 All in All DP?1505 Copying Books DP+二分查找1631 Bridging signals DP+二分查找1159 Palindrome DP->LCS1458 Common Subsequence DP->LCS1080 Human Gene Functions DP->LCS变形2192 Zipper DP->LCS变形1185 炮兵阵地DP->数据压缩2430 Lazy Cows DP->数据压缩1067 取石子游戏博弈论1082 Calendar Game 博弈论1085 Triangle War 博弈论1143 Number Game 博弈论2311 Cutting Game 博弈论2425 A Chess Game 博弈论1638 A number game 博弈论1694 An Old Stone Game 博弈论?1738 An old Stone Game 博弈论?1741 Tree 博弈论?2083 Fractal 递归1104 Robbery 递推1217 FOUR QUARTERS 递推1280 Game 递推2261 France '98 递推2181 Jumping Cows 递推1316 Self Numbers 递推同Humble Number一样2084 Game of Connections 递推(不必高精度) 1338 Ugly Numbers 递推(有O(n)算法)2247 Humble Numbers 递推(最优O(n)算法)1322 Chocolate 递推/组合数学1189 钉子和小球递推?1947 Rebuilding Roads 二分2418 Hardwood Species 二分查找2082 Terrible Sets 分治/1001 Exponentiation 高精度1047 Round and Round We Go 高精度1060 Modular multiplication of polynomials 高精度1131 Octal Fractions 高精度1202 Family 高精度2199 Rate of Return 高精度1646 Double Trouble 高精度1147 Binary codes 构造1148 Utopia Divided 构造2275 Flipping Pancake 构造1660 Princess FroG 构造1772 New Go Game 构造?1005 I Think I Need a Houseboat 几何1039 Pipe 几何1070 Deformed Wheel 几何1092 Farmland 几何1106 Transmitters 几何2194 Stacking Cylinders 几何2254 Globetrotter 几何2315 Football Game 几何2423 The Parallel Challenge Ballgame 几何1375 Intervals 几何1380 Equipment Box 几何1408 Fishnet 几何1514 Metal Cutting 几何1518 Problem Bee 几何1605 Horse Shoe Scoring 几何1654 Area 几何1693 Counting Rectangles 几何1774 Fold Paper Strips 几何1871 Bullet Hole 几何1875 Robot 几何1873 The Fortified Forest 几何+回溯1031 Fence 计算几何1034 The dog task 计算几何1271 Nice Milk 计算几何2284 That Nice Euler Circuit 计算几何1688 Dolphin Pool 计算几何2165 Gunman 计算几何1755 Triathlon 计算几何?1379 Run Away 计算几何->1113 Wall 计算几何->convex hull1434 Fill the Cisterns! 计算几何->离散化/1151 Atlantis 计算几何->同等安置矩形的并的面积->离散化1177 Picture 计算几何->同等安置矩形的并的周长->线段树2419 Forests 枚举2179 Inlay Cutters 枚举1025 Department 模拟1027 The Same Game 模拟1048 Follow My Logic 模拟1049 Microprocessor Simulation 模拟1073 The Willy Memorial Program 模拟1075 University Entrance Examination 模拟1098 Robots 模拟1103 Maze 模拟1120 A New Growth Industry 模拟1193 内存分配模拟1281 MANAGER 模拟2200 A Card Trick 模拟2314 POJ language 模拟1431 Calendar of Maya 模拟1483 Going in Circles on Alpha Centauri 模拟1512 Keeps Going and Going and ... 模拟1773 Outernet 模拟1876 The Letter Carrier's Rounds 模拟1883 Theseus and the Minotaur 模拟2050 Searching the Web 模拟(需要高效实现)1012 Joseph 模拟/数学方法1086 Unscrambling Images 模拟?1327 Moving Object Recognition 模拟?1893 Monitoring Wheelchair Patients 模拟+几何1462 Random Walk 模拟+解线性方程组2379 ACM Rank T able 模拟+排序1879 Tempus et mobilius Time and motion 模拟+组合数学->Polya定理1520 Scramble Sort 排序1634 Who's the boss? 排序2299 Ultra-QuickSort 排序->归并排序1008 Maya Calendar 日期处理1209 Calendar 日期处理2210 Metric Time 日期处理1430 Binary Stirling Numbers 日期处理1447 Ambiguous Dates 日期处理2080 Calendar 日期处理2351 Time Zones 时间处理1770 Special Experiment 树形DP1916 Rat Attack 数据结构->?1197 Depot 数据结构->Young T ableau1182 食物链数据结构->并查集2424 Flo's Restaurant 数据结构->堆1877 Flooded! 数据结构->堆1445 Random number 数据结构->碓1023 The Fun Number System 数论1061 青蛙的约会数论1091 跳蚤数论1152 An Easy Problem! 数论2191 Mersenne Composite Numbers 数论2381 Random Gap 数论2417 Discrete Logging 数论1510 Hares and Foxes 数论1641 Rational Approximation 数论1730 Perfect Pth Powers 数论1777 Vivian's Problem 数论2061 Pseudo-random Numbers 数论1014 Dividing 数论/DP?/组合数学->母函数?1606 Jugs 数论/搜索1995 Raising Modulo Numbers 数论->大数的幂求余2115 C Looooops 数论->解模线性方程1288 Sly Number 数论->解模线性方程组1395 Cog-Wheels 数学->解正系数的线性方程组1000 A+B Problem 送分题1003 Hangover 送分题1004 Financial Management 送分题1006 Biorhythms 送分题1007 DNA Sorting 送分题1016 Numbers That Count 送分题1019 Number Sequence 送分题1028 Web Navigation 送分题1046 Color Me Less 送分题1053 Set Me 送分题1068 Parencodings 送分题1071 Illusive Chase 送分题1096 Space Station Shielding 送分题1099 Square Ice 送分题1102 LC-Display 送分题1107 W's Cipher 送分题1119 Start Up the Startup 送分题1218 THE DRUNK JAILER 送分题1245 Programmer, Rank Thyself 送分题1247 Magnificent Meatballs 送分题1250 T anning Salon 送分题1298 The Hardest Problem Ever 送分题1326 Mileage Bank 送分题2190 ISBN 送分题2196 Specialized Four-Digit Numbers 送分题2291 Rotten Ropes 送分题2304 Combination Lock 送分题2309 BST 送分题2390 Bank Interest 送分题2403 Hay Points 送分题1411 Calling Extraterrestrial Intelligence Again 送分题1481 The Die Is Cast 送分题1484 Blowing Fuses 送分题1517 u Calculate e 送分题1547 Clay Bully 送分题1563 The Snail 送分题1604 Just the Facts 送分题1657 Distance on Chessboard 送分题1658 Eva's Problem 送分题1663 Number Steps 送分题1677 Girls' Day 送分题1690 (Your)((Term)((Project))) 送分题1775 Sum of Factorials 送分题1870 Bee Breeding 送分题2105 IP Address 送分题2136 Vertical Histogram 送分题1555 Polynomial Showdown 送分题(非常阴险) 2388 Who's in the Middle 送分题(排序)1519 Digital Roots 送分题(位数可能很大)1045 Bode Plot 送分题(用物理知识)2051 Argus 送分题(最好用堆,不用也可以过) 1011 Sticks 搜索1020 Anniversary Cake 搜索1054 The Troublesome Frog 搜索1069 The Bermuda Triangle 搜索1072 Puzzle Out 搜索1100 Dreisam Equations 搜索1110 Double Vision 搜索1111 Image Perimeters 搜索1128 Frame Stacking 搜索1142 Smith Numbers 搜索1162 Building with Blocks 搜索1183 反正切函数的应用搜索1184 聪明的打字员搜索1248 Safecracker 搜索1601 Pizza Anyone? 搜索1713 Divide et unita 搜索1129 Channel Allocation 搜索(图的最大独立集)1190 生日蛋糕搜索/DP1691 Painting A Board 搜索/DP1714 The Cave 搜索/DP1084 Square Destroyer 搜索?1010 STAMPS 搜索+DP1194 HIDDEN CODES 搜索+DP1882 Stamps 搜索+DP1101 The Game 搜索->BFS1137 The New Villa 搜索->BFS1233 Street Crossing 搜索->BFS2243 Knight Moves 搜索->BFS2312 Battle City 搜索->BFS1476 Always On the Run 搜索->BFS1480 Optimal Programs 搜索->BFS1482 It's not a Bug, It's a Feature! 搜索->BFS 1753 Flip Game 搜索->BFS1915 Knight Moves 搜索->BFS1017 Packets 贪心1018 Communication System 贪心1323 Game Prediction 贪心1463 Strategic game 贪心1469 COURSES 贪心1719 Shooting Contest 贪心2054 Color a Tree 贪心1328 Radar Installation 贪心(差分约束系统的特例)1042 Gone Fishing 贪心/DP1752 Advertisement 贪心/图论->差分约束系统1201 Intervals 贪心/图论->最长路->差分约束系统1097 Roads Scholar 图论1161 Walls 图论1450 Gridland 图论(本来TSP问题是NP难的,但这个图比较特殊,由现成的构造方法)2197 Jill's Tour Paths 图论->2416 Return of the Jedi 图论->1639 Picnic Planning 图论->1695 Magazine Delivery 图论->1729 Jack and Jill 图论->1751 Highways 图论->1122 FDNY to the Rescue! 图论->Dijkstra1125 Stockbroker Grapevine 图论->Dijkstra1135 Domino Effect 图论->Dijkstra1394 Railroad 图论->Dijkstra1158 TRAFFIC LIGHTS 图论->Dijkstra变形2395 Out of Hay 图论->Dijkstra变形2253 Frogger 图论->Dijkstra变形(和1295是一样的)1734 Sightseeing trip 图论->Euler回路1466 Girls and Boys 图论->n/a1515 Street Directions 图论->把一个无向连通图改造成为有向强连通图1635 Subway tree systems 图论->不同表示法的二叉树判同1275 Cashier Employment 图论->差分约束系统->无负权回路的有向图的最长路->Bellman-Ford1274 The Perfect Stall 图论->二分图的最大匹配1325 Machine Schedule 图论->二分图的最大匹配2239 Selecting Courses 图论->二分图的最大匹配2195 Going Home 图论->二分图的最大权匹配2400 Supervisor, Supervisee 图论->二分图的最大权匹配?1637 Sightseeing tour 图论->欧拉回路1383 Labyrinth 图论->树的最长路1094 Sorting It All Out 图论->拓扑排序1486 Sorting Slides 图论->拓扑排序1149 PIGS 图论->网络流2289 Jamie's Contact Groups 图论->网络流?1192 最优连通子集图论->无负权回路的有向图的最长路->BellmanFord 1364 King 图论->无负权回路的有向图的最长路->BellmanFord1985 Cow Marathon 图论->有向无环图的最长路1087 A Plug for UNIX 图论->最大流1273 Drainage Ditches 图论->最大流1459 Power Network 图论->最大流1632 Vase collection 图论->最大完全图2049 Finding Nemo 图论->最短路1251 Jungle Roads 图论->最小生成树2421 Constructing Roads 图论->最小生成树1026 Cipher 组合数学1095 Trees Made to Order 组合数学2346 Lucky tickets 组合数学1286 Necklace of Beads 组合数学->Polya定理2409 Let it Bead 组合数学->Polya定理1664 放苹果组合数学->递推。

2009and2010Papers:Big-4Security ConferencespvoOctober13,2010NDSS20091.Document Structure Integrity:A Robust Basis for Cross-site Scripting Defense.Y.Nadji,P.Saxena,D.Song2.An Efficient Black-box Technique for Defeating Web Application Attacks.R.Sekar3.Noncespaces:Using Randomization to Enforce Information Flow Tracking and Thwart Cross-Site Scripting Attacks.M.Van Gundy,H.Chen4.The Blind Stone Tablet:Outsourcing Durability to Untrusted Parties.P.Williams,R.Sion,D.Shasha5.Two-Party Computation Model for Privacy-Preserving Queries over Distributed Databases.S.S.M.Chow,J.-H.Lee,L.Subramanian6.SybilInfer:Detecting Sybil Nodes using Social Networks.G.Danezis,P.Mittal7.Spectrogram:A Mixture-of-Markov-Chains Model for Anomaly Detection in Web Traffic.Yingbo Song,Angelos D.Keromytis,Salvatore J.Stolfo8.Detecting Forged TCP Reset Packets.Nicholas Weaver,Robin Sommer,Vern Paxson9.Coordinated Scan Detection.Carrie Gates10.RB-Seeker:Auto-detection of Redirection Botnets.Xin Hu,Matthew Knysz,Kang G.Shin11.Scalable,Behavior-Based Malware Clustering.Ulrich Bayer,Paolo Milani Comparetti,Clemens Hlauschek,Christopher Kruegel,Engin Kirda12.K-Tracer:A System for Extracting Kernel Malware Behavior.Andrea Lanzi,Monirul I.Sharif,Wenke Lee13.RAINBOW:A Robust And Invisible Non-Blind Watermark for Network Flows.Amir Houmansadr,Negar Kiyavash,Nikita Borisov14.Traffic Morphing:An Efficient Defense Against Statistical Traffic Analysis.Charles V.Wright,Scott E.Coull,Fabian Monrose15.Recursive DNS Architectures and Vulnerability Implications.David Dagon,Manos Antonakakis,Kevin Day,Xiapu Luo,Christopher P.Lee,Wenke Lee16.Analyzing and Comparing the Protection Quality of Security Enhanced Operating Systems.Hong Chen,Ninghui Li,Ziqing Mao17.IntScope:Automatically Detecting Integer Overflow Vulnerability in X86Binary Using Symbolic Execution.Tielei Wang,Tao Wei,Zhiqiang Lin,Wei Zou18.Safe Passage for Passwords and Other Sensitive Data.Jonathan M.McCune,Adrian Perrig,Michael K.Reiter19.Conditioned-safe Ceremonies and a User Study of an Application to Web Authentication.Chris Karlof,J.Doug Tygar,David Wagner20.CSAR:A Practical and Provable Technique to Make Randomized Systems Accountable.Michael Backes,Peter Druschel,Andreas Haeberlen,Dominique UnruhOakland20091.Wirelessly Pickpocketing a Mifare Classic Card.(Best Practical Paper Award)Flavio D.Garcia,Peter van Rossum,Roel Verdult,Ronny Wichers Schreur2.Plaintext Recovery Attacks Against SSH.Martin R.Albrecht,Kenneth G.Paterson,Gaven J.Watson3.Exploiting Unix File-System Races via Algorithmic Complexity Attacks.Xiang Cai,Yuwei Gui,Rob Johnson4.Practical Mitigations for Timing-Based Side-Channel Attacks on Modern x86Processors.Bart Coppens,Ingrid Verbauwhede,Bjorn De Sutter,Koen De Bosschere5.Non-Interference for a Practical DIFC-Based Operating System.Maxwell Krohn,Eran Tromer6.Native Client:A Sandbox for Portable,Untrusted x86Native Code.(Best Paper Award)B.Yee,D.Sehr,G.Dardyk,B.Chen,R.Muth,T.Ormandy,S.Okasaka,N.Narula,N.Fullagar7.Automatic Reverse Engineering of Malware Emulators.(Best Student Paper Award)Monirul Sharif,Andrea Lanzi,Jonathon Giffin,Wenke Lee8.Prospex:Protocol Specification Extraction.Paolo Milani Comparetti,Gilbert Wondracek,Christopher Kruegel,Engin Kirda9.Quantifying Information Leaks in Outbound Web Traffic.Kevin Borders,Atul Prakash10.Automatic Discovery and Quantification of Information Leaks.Michael Backes,Boris Kopf,Andrey Rybalchenko11.CLAMP:Practical Prevention of Large-Scale Data Leaks.Bryan Parno,Jonathan M.McCune,Dan Wendlandt,David G.Andersen,Adrian Perrig12.De-anonymizing Social Networks.Arvind Narayanan,Vitaly Shmatikov13.Privacy Weaknesses in Biometric Sketches.Koen Simoens,Pim Tuyls,Bart Preneel14.The Mastermind Attack on Genomic Data.Michael T.Goodrich15.A Logic of Secure Systems and its Application to Trusted Computing.Anupam Datta,Jason Franklin,Deepak Garg,Dilsun Kaynar16.Formally Certifying the Security of Digital Signature Schemes.Santiago Zanella-Beguelin,Gilles Barthe,Benjamin Gregoire,Federico Olmedo17.An Epistemic Approach to Coercion-Resistance for Electronic Voting Protocols.Ralf Kuesters,Tomasz Truderung18.Sphinx:A Compact and Provably Secure Mix Format.George Danezis,Ian Goldberg19.DSybil:Optimal Sybil-Resistance for Recommendation Systems.Haifeng Yu,Chenwei Shi,Michael Kaminsky,Phillip B.Gibbons,Feng Xiao20.Fingerprinting Blank Paper Using Commodity Scanners.William Clarkson,Tim Weyrich,Adam Finkelstein,Nadia Heninger,Alex Halderman,Ed Felten 21.Tempest in a Teapot:Compromising Reflections Revisited.Michael Backes,Tongbo Chen,Markus Duermuth,Hendrik P.A.Lensch,Martin Welk22.Blueprint:Robust Prevention of Cross-site Scripting Attacks for Existing Browsers.Mike Ter Louw,V.N.Venkatakrishnan23.Pretty-Bad-Proxy:An Overlooked Adversary in Browsers’HTTPS Deployments.Shuo Chen,Ziqing Mao,Yi-Min Wang,Ming Zhang24.Secure Content Sniffing for Web Browsers,or How to Stop Papers from Reviewing Themselves.Adam Barth,Juan Caballero,Dawn Song25.It’s No Secret:Measuring the Security and Reliability of Authentication via’Secret’Questions.Stuart Schechter,A.J.Bernheim Brush,Serge Egelman26.Password Cracking Using Probabilistic Context-Free Grammars.Matt Weir,Sudhir Aggarwal,Bill Glodek,Breno de MedeirosUSENIX Security2009promising Electromagnetic Emanations of Wired and Wireless Keyboards.(Outstanding Student Paper)Martin Vuagnoux,Sylvain Pasini2.Peeping Tom in the Neighborhood:Keystroke Eavesdropping on Multi-User Systems.Kehuan Zhang,XiaoFeng Wang3.A Practical Congestion Attack on Tor Using Long Paths,Nathan S.Evans,Roger Dingledine,Christian Grothoff4.Baggy Bounds Checking:An Efficient and Backwards-Compatible Defense against Out-of-Bounds Errors.Periklis Akritidis,Manuel Costa,Miguel Castro,Steven Hand5.Dynamic Test Generation to Find Integer Bugs in x86Binary Linux Programs.David Molnar,Xue Cong Li,David A.Wagner6.NOZZLE:A Defense Against Heap-spraying Code Injection Attacks.Paruj Ratanaworabhan,Benjamin Livshits,Benjamin Zorn7.Detecting Spammers with SNARE:Spatio-temporal Network-level Automatic Reputation Engine.Shuang Hao,Nadeem Ahmed Syed,Nick Feamster,Alexander G.Gray,Sven Krasser8.Improving Tor using a TCP-over-DTLS Tunnel.Joel Reardon,Ian Goldberg9.Locating Prefix Hijackers using LOCK.Tongqing Qiu,Lusheng Ji,Dan Pei,Jia Wang,Jun(Jim)Xu,Hitesh Ballani10.GATEKEEPER:Mostly Static Enforcement of Security and Reliability Policies for JavaScript Code.Salvatore Guarnieri,Benjamin Livshits11.Cross-Origin JavaScript Capability Leaks:Detection,Exploitation,and Defense.Adam Barth,Joel Weinberger,Dawn Song12.Memory Safety for Low-Level Software/Hardware Interactions.John Criswell,Nicolas Geoffray,Vikram Adve13.Physical-layer Identification of RFID Devices.Boris Danev,Thomas S.Heydt-Benjamin,Srdjan CapkunCP:Secure Remote Storage for Computational RFIDs.Mastooreh Salajegheh,Shane Clark,Benjamin Ransford,Kevin Fu,Ari Juels15.Jamming-resistant Broadcast Communication without Shared Keys.Christina Popper,Mario Strasser,Srdjan Capkun16.xBook:Redesigning Privacy Control in Social Networking Platforms.Kapil Singh,Sumeer Bhola,Wenke Lee17.Nemesis:Preventing Authentication and Access Control Vulnerabilities in Web Applications.Michael Dalton,Christos Kozyrakis,Nickolai Zeldovich18.Static Enforcement of Web Application Integrity Through Strong Typing.William Robertson,Giovanni Vigna19.Vanish:Increasing Data Privacy with Self-Destructing Data.(Outstanding Student Paper)Roxana Geambasu,Tadayoshi Kohno,Amit A.Levy,Henry M.Levy20.Efficient Data Structures for Tamper-Evident Logging.Scott A.Crosby,Dan S.Wallach21.VPriv:Protecting Privacy in Location-Based Vehicular Services.Raluca Ada Popa,Hari Balakrishnan,Andrew J.Blumberg22.Effective and Efficient Malware Detection at the End Host.Clemens Kolbitsch,Paolo Milani Comparetti,Christopher Kruegel,Engin Kirda,Xiaoyong Zhou,XiaoFeng Wang 23.Protecting Confidential Data on Personal Computers with Storage Capsules.Kevin Borders,Eric Vander Weele,Billy Lau,Atul Prakash24.Return-Oriented Rootkits:Bypassing Kernel Code Integrity Protection Mechanisms.Ralf Hund,Thorsten Holz,Felix C.Freiling25.Crying Wolf:An Empirical Study of SSL Warning Effectiveness.Joshua Sunshine,Serge Egelman,Hazim Almuhimedi,Neha Atri,Lorrie Faith Cranor26.The Multi-Principal OS Construction of the Gazelle Web Browser.Helen J.Wang,Chris Grier,Alex Moshchuk,Samuel T.King,Piali Choudhury,Herman VenterACM CCS20091.Attacking cryptographic schemes based on”perturbation polynomials”.Martin Albrecht,Craig Gentry,Shai Halevi,Jonathan Katz2.Filter-resistant code injection on ARM.Yves Younan,Pieter Philippaerts,Frank Piessens,Wouter Joosen,Sven Lachmund,Thomas Walter3.False data injection attacks against state estimation in electric power grids.Yao Liu,Michael K.Reiter,Peng Ning4.EPC RFID tag security weaknesses and defenses:passport cards,enhanced drivers licenses,and beyond.Karl Koscher,Ari Juels,Vjekoslav Brajkovic,Tadayoshi Kohno5.An efficient forward private RFID protocol.Come Berbain,Olivier Billet,Jonathan Etrog,Henri Gilbert6.RFID privacy:relation between two notions,minimal condition,and efficient construction.Changshe Ma,Yingjiu Li,Robert H.Deng,Tieyan Li7.CoSP:a general framework for computational soundness proofs.Michael Backes,Dennis Hofheinz,Dominique Unruh8.Reactive noninterference.Aaron Bohannon,Benjamin C.Pierce,Vilhelm Sjoberg,Stephanie Weirich,Steve Zdancewicputational soundness for key exchange protocols with symmetric encryption.Ralf Kusters,Max Tuengerthal10.A probabilistic approach to hybrid role mining.Mario Frank,Andreas P.Streich,David A.Basin,Joachim M.Buhmann11.Efficient pseudorandom functions from the decisional linear assumption and weaker variants.Allison B.Lewko,Brent Waters12.Improving privacy and security in multi-authority attribute-based encryption.Melissa Chase,Sherman S.M.Chow13.Oblivious transfer with access control.Jan Camenisch,Maria Dubovitskaya,Gregory Neven14.NISAN:network information service for anonymization networks.Andriy Panchenko,Stefan Richter,Arne Rache15.Certificateless onion routing.Dario Catalano,Dario Fiore,Rosario Gennaro16.ShadowWalker:peer-to-peer anonymous communication using redundant structured topologies.Prateek Mittal,Nikita Borisov17.Ripley:automatically securing web2.0applications through replicated execution.K.Vikram,Abhishek Prateek,V.Benjamin Livshits18.HAIL:a high-availability and integrity layer for cloud storage.Kevin D.Bowers,Ari Juels,Alina Oprea19.Hey,you,get offof my cloud:exploring information leakage in third-party compute clouds.Thomas Ristenpart,Eran Tromer,Hovav Shacham,Stefan Savage20.Dynamic provable data possession.C.Christopher Erway,Alptekin Kupcu,Charalampos Papamanthou,Roberto Tamassia21.On cellular botnets:measuring the impact of malicious devices on a cellular network core.Patrick Traynor,Michael Lin,Machigar Ongtang,Vikhyath Rao,Trent Jaeger,Patrick Drew McDaniel,Thomas Porta 22.On lightweight mobile phone application certification.William Enck,Machigar Ongtang,Patrick Drew McDaniel23.SMILE:encounter-based trust for mobile social services.Justin Manweiler,Ryan Scudellari,Landon P.Cox24.Battle of Botcraft:fighting bots in online games with human observational proofs.Steven Gianvecchio,Zhenyu Wu,Mengjun Xie,Haining Wang25.Fides:remote anomaly-based cheat detection using client emulation.Edward C.Kaiser,Wu-chang Feng,Travis Schluessler26.Behavior based software theft detection.Xinran Wang,Yoon-chan Jhi,Sencun Zhu,Peng Liu27.The fable of the bees:incentivizing robust revocation decision making in ad hoc networks.Steffen Reidt,Mudhakar Srivatsa,Shane Balfe28.Effective implementation of the cell broadband engineTM isolation loader.Masana Murase,Kanna Shimizu,Wilfred Plouffe,Masaharu Sakamoto29.On achieving good operating points on an ROC plane using stochastic anomaly score prediction.Muhammad Qasim Ali,Hassan Khan,Ali Sajjad,Syed Ali Khayam30.On non-cooperative location privacy:a game-theoretic analysis.Julien Freudiger,Mohammad Hossein Manshaei,Jean-Pierre Hubaux,David C.Parkes31.Privacy-preserving genomic computation through program specialization.Rui Wang,XiaoFeng Wang,Zhou Li,Haixu Tang,Michael K.Reiter,Zheng Dong32.Feeling-based location privacy protection for location-based services.Toby Xu,Ying Cai33.Multi-party off-the-record messaging.Ian Goldberg,Berkant Ustaoglu,Matthew Van Gundy,Hao Chen34.The bayesian traffic analysis of mix networks.Carmela Troncoso,George Danezis35.As-awareness in Tor path selection.Matthew Edman,Paul F.Syverson36.Membership-concealing overlay networks.Eugene Y.Vasserman,Rob Jansen,James Tyra,Nicholas Hopper,Yongdae Kim37.On the difficulty of software-based attestation of embedded devices.Claude Castelluccia,Aurelien Francillon,Daniele Perito,Claudio Soriente38.Proximity-based access control for implantable medical devices.Kasper Bonne Rasmussen,Claude Castelluccia,Thomas S.Heydt-Benjamin,Srdjan Capkun39.XCS:cross channel scripting and its impact on web applications.Hristo Bojinov,Elie Bursztein,Dan Boneh40.A security-preserving compiler for distributed programs:from information-flow policies to cryptographic mechanisms.Cedric Fournet,Gurvan Le Guernic,Tamara Rezk41.Finding bugs in exceptional situations of JNI programs.Siliang Li,Gang Tan42.Secure open source collaboration:an empirical study of Linus’law.Andrew Meneely,Laurie A.Williams43.On voting machine design for verification and testability.Cynthia Sturton,Susmit Jha,Sanjit A.Seshia,David Wagner44.Secure in-VM monitoring using hardware virtualization.Monirul I.Sharif,Wenke Lee,Weidong Cui,Andrea Lanzi45.A metadata calculus for secure information sharing.Mudhakar Srivatsa,Dakshi Agrawal,Steffen Reidt46.Multiple password interference in text passwords and click-based graphical passwords.Sonia Chiasson,Alain Forget,Elizabeth Stobert,Paul C.van Oorschot,Robert Biddle47.Can they hear me now?:a security analysis of law enforcement wiretaps.Micah Sherr,Gaurav Shah,Eric Cronin,Sandy Clark,Matt Blaze48.English shellcode.Joshua Mason,Sam Small,Fabian Monrose,Greg MacManus49.Learning your identity and disease from research papers:information leaks in genome wide association study.Rui Wang,Yong Fuga Li,XiaoFeng Wang,Haixu Tang,Xiao-yong Zhou50.Countering kernel rootkits with lightweight hook protection.Zhi Wang,Xuxian Jiang,Weidong Cui,Peng Ning51.Mapping kernel objects to enable systematic integrity checking.Martim Carbone,Weidong Cui,Long Lu,Wenke Lee,Marcus Peinado,Xuxian Jiang52.Robust signatures for kernel data structures.Brendan Dolan-Gavitt,Abhinav Srivastava,Patrick Traynor,Jonathon T.Giffin53.A new cell counter based attack against tor.Zhen Ling,Junzhou Luo,Wei Yu,Xinwen Fu,Dong Xuan,Weijia Jia54.Scalable onion routing with torsk.Jon McLachlan,Andrew Tran,Nicholas Hopper,Yongdae Kim55.Anonymous credentials on a standard java card.Patrik Bichsel,Jan Camenisch,Thomas Gros,Victor Shouprge-scale malware indexing using function-call graphs.Xin Hu,Tzi-cker Chiueh,Kang G.Shin57.Dispatcher:enabling active botnet infiltration using automatic protocol reverse-engineering.Juan Caballero,Pongsin Poosankam,Christian Kreibich,Dawn Xiaodong Song58.Your botnet is my botnet:analysis of a botnet takeover.Brett Stone-Gross,Marco Cova,Lorenzo Cavallaro,Bob Gilbert,MartinSzydlowski,Richard A.Kemmerer,Christopher Kruegel,Giovanni VignaNDSS20101.Server-side Verification of Client Behavior in Online Games.Darrell Bethea,Robert Cochran and Michael Reiter2.Defeating Vanish with Low-Cost Sybil Attacks Against Large DHTs.S.Wolchok,O.S.Hofmann,N.Heninger,E.W.Felten,J.A.Halderman,C.J.Rossbach,B.Waters,E.Witchel3.Stealth DoS Attacks on Secure Channels.Amir Herzberg and Haya Shulman4.Protecting Browsers from Extension Vulnerabilities.Adam Barth,Adrienne Porter Felt,Prateek Saxena,and Aaron Boodman5.Adnostic:Privacy Preserving Targeted Advertising.Vincent Toubiana,Arvind Narayanan,Dan Boneh,Helen Nissenbaum and Solon Barocas6.FLAX:Systematic Discovery of Client-side Validation Vulnerabilities in Rich Web Applications.Prateek Saxena,Steve Hanna,Pongsin Poosankam and Dawn Song7.Effective Anomaly Detection with Scarce Training Data.William Robertson,Federico Maggi,Christopher Kruegel and Giovanni Vignarge-Scale Automatic Classification of Phishing Pages.Colin Whittaker,Brian Ryner and Marria Nazif9.A Systematic Characterization of IM Threats using Honeypots.Iasonas Polakis,Thanasis Petsas,Evangelos P.Markatos and Spiros Antonatos10.On Network-level Clusters for Spam Detection.Zhiyun Qian,Zhuoqing Mao,Yinglian Xie and Fang Yu11.Improving Spam Blacklisting Through Dynamic Thresholding and Speculative Aggregation.Sushant Sinha,Michael Bailey and Farnam Jahanian12.Botnet Judo:Fighting Spam with Itself.A.Pitsillidis,K.Levchenko,C.Kreibich,C.Kanich,G.M.Voelker,V.Paxson,N.Weaver,S.Savage13.Contractual Anonymity.Edward J.Schwartz,David Brumley and Jonathan M.McCune14.A3:An Extensible Platform for Application-Aware Anonymity.Micah Sherr,Andrew Mao,William R.Marczak,Wenchao Zhou,Boon Thau Loo,and Matt Blaze15.When Good Randomness Goes Bad:Virtual Machine Reset Vulnerabilities and Hedging Deployed Cryptography.Thomas Ristenpart and Scott Yilek16.InvisiType:Object-Oriented Security Policies.Jiwon Seo and Monica m17.A Security Evaluation of DNSSEC with NSEC3.Jason Bau and John Mitchell18.On the Safety of Enterprise Policy Deployment.Yudong Gao,Ni Pan,Xu Chen and Z.Morley Mao19.Where Do You Want to Go Today?Escalating Privileges by Pathname Manipulation.Suresh Chari,Shai Halevi and Wietse Venema20.Joe-E:A Security-Oriented Subset of Java.Adrian Mettler,David Wagner and Tyler Close21.Preventing Capability Leaks in Secure JavaScript Subsets.Matthew Finifter,Joel Weinberger and Adam Barth22.Binary Code Extraction and Interface Identification for Security Applications.Juan Caballero,Noah M.Johnson,Stephen McCamant,and Dawn Song23.Automatic Reverse Engineering of Data Structures from Binary Execution.Zhiqiang Lin,Xiangyu Zhang and Dongyan Xu24.Efficient Detection of Split Personalities in Malware.Davide Balzarotti,Marco Cova,Christoph Karlberger,Engin Kirda,Christopher Kruegel and Giovanni VignaOakland20101.Inspector Gadget:Automated Extraction of Proprietary Gadgets from Malware Binaries.Clemens Kolbitsch Thorsten Holz,Christopher Kruegel,Engin Kirda2.Synthesizing Near-Optimal Malware Specifications from Suspicious Behaviors.Matt Fredrikson,Mihai Christodorescu,Somesh Jha,Reiner Sailer,Xifeng Yan3.Identifying Dormant Functionality in Malware Programs.Paolo Milani Comparetti,Guido Salvaneschi,Clemens Kolbitsch,Engin Kirda,Christopher Kruegel,Stefano Zanero4.Reconciling Belief and Vulnerability in Information Flow.Sardaouna Hamadou,Vladimiro Sassone,Palamidessi5.Towards Static Flow-Based Declassification for Legacy and Untrusted Programs.Bruno P.S.Rocha,Sruthi Bandhakavi,Jerry I.den Hartog,William H.Winsborough,Sandro Etalle6.Non-Interference Through Secure Multi-Execution.Dominique Devriese,Frank Piessens7.Object Capabilities and Isolation of Untrusted Web Applications.Sergio Maffeis,John C.Mitchell,Ankur Taly8.TrustVisor:Efficient TCB Reduction and Attestation.Jonathan McCune,Yanlin Li,Ning Qu,Zongwei Zhou,Anupam Datta,Virgil Gligor,Adrian Perrig9.Overcoming an Untrusted Computing Base:Detecting and Removing Malicious Hardware Automatically.Matthew Hicks,Murph Finnicum,Samuel T.King,Milo M.K.Martin,Jonathan M.Smith10.Tamper Evident Microprocessors.Adam Waksman,Simha Sethumadhavan11.Side-Channel Leaks in Web Applications:a Reality Today,a Challenge Tomorrow.Shuo Chen,Rui Wang,XiaoFeng Wang Kehuan Zhang12.Investigation of Triangular Spamming:a Stealthy and Efficient Spamming Technique.Zhiyun Qian,Z.Morley Mao,Yinglian Xie,Fang Yu13.A Practical Attack to De-Anonymize Social Network Users.Gilbert Wondracek,Thorsten Holz,Engin Kirda,Christopher Kruegel14.SCiFI-A System for Secure Face Identification.(Best Paper)Margarita Osadchy,Benny Pinkas,Ayman Jarrous,Boaz Moskovich15.Round-Efficient Broadcast Authentication Protocols for Fixed Topology Classes.Haowen Chan,Adrian Perrig16.Revocation Systems with Very Small Private Keys.Allison Lewko,Amit Sahai,Brent Waters17.Authenticating Primary Users’Signals in Cognitive Radio Networks via Integrated Cryptographic and Wireless Link Signatures.Yao Liu,Peng Ning,Huaiyu Dai18.Outside the Closed World:On Using Machine Learning For Network Intrusion Detection.Robin Sommer,Vern Paxson19.All You Ever Wanted to Know about Dynamic Taint Analysis and Forward Symbolic Execution(but might have been afraid to ask).Thanassis Avgerinos,Edward Schwartz,David Brumley20.State of the Art:Automated Black-Box Web Application Vulnerability Testing.Jason Bau,Elie Bursztein,Divij Gupta,John Mitchell21.A Proof-Carrying File System.Deepak Garg,Frank Pfenning22.Scalable Parametric Verification of Secure Systems:How to Verify Ref.Monitors without Worrying about Data Structure Size.Jason Franklin,Sagar Chaki,Anupam Datta,Arvind Seshadri23.HyperSafe:A Lightweight Approach to Provide Lifetime Hypervisor Control-Flow Integrity.Zhi Wang,Xuxian Jiang24.How Good are Humans at Solving CAPTCHAs?A Large Scale Evaluation.Elie Bursztein,Steven Bethard,John C.Mitchell,Dan Jurafsky,Celine Fabry25.Bootstrapping Trust in Commodity Computers.Bryan Parno,Jonathan M.McCune,Adrian Perrig26.Chip and PIN is Broken.(Best Practical Paper)Steven J.Murdoch,Saar Drimer,Ross Anderson,Mike Bond27.Experimental Security Analysis of a Modern Automobile.K.Koscher,A.Czeskis,F.Roesner,S.Patel,T.Kohno,S.Checkoway,D.McCoy,B.Kantor,D.Anderson,H.Shacham,S.Savage 28.On the Incoherencies in Web Browser Access Control Policies.Kapil Singh,Alexander Moshchuk,Helen J.Wang,Wenke Lee29.ConScript:Specifying and Enforcing Fine-Grained Security Policies for JavaScript in the Browser.Leo Meyerovich,Benjamin Livshits30.TaintScope:A Checksum-Aware Directed Fuzzing Tool for Automatic Software Vulnerability Detection.(Best Student Paper)Tielei Wang,Tao Wei,Guofei Gu,Wei Zou31.A Symbolic Execution Framework for JavaScript.Prateek Saxena,Devdatta Akhawe,Steve Hanna,Stephen McCamant,Dawn Song,Feng MaoUSENIX Security20101.Adapting Software Fault Isolation to Contemporary CPU Architectures.David Sehr,Robert Muth,CliffBiffle,Victor Khimenko,Egor Pasko,Karl Schimpf,Bennet Yee,Brad Chen2.Making Linux Protection Mechanisms Egalitarian with UserFS.Taesoo Kim and Nickolai Zeldovich3.Capsicum:Practical Capabilities for UNIX.(Best Student Paper)Robert N.M.Watson,Jonathan Anderson,Ben Laurie,Kris Kennaway4.Structuring Protocol Implementations to Protect Sensitive Data.Petr Marchenko,Brad Karp5.PrETP:Privacy-Preserving Electronic Toll Pricing.Josep Balasch,Alfredo Rial,Carmela Troncoso,Bart Preneel,Ingrid Verbauwhede,Christophe Geuens6.An Analysis of Private Browsing Modes in Modern Browsers.Gaurav Aggarwal,Elie Bursztein,Collin Jackson,Dan Boneh7.BotGrep:Finding P2P Bots with Structured Graph Analysis.Shishir Nagaraja,Prateek Mittal,Chi-Yao Hong,Matthew Caesar,Nikita Borisov8.Fast Regular Expression Matching Using Small TCAMs for Network Intrusion Detection and Prevention Systems.Chad R.Meiners,Jignesh Patel,Eric Norige,Eric Torng,Alex X.Liu9.Searching the Searchers with SearchAudit.John P.John,Fang Yu,Yinglian Xie,Martin Abadi,Arvind Krishnamurthy10.Toward Automated Detection of Logic Vulnerabilities in Web Applications.Viktoria Felmetsger,Ludovico Cavedon,Christopher Kruegel,Giovanni Vigna11.Baaz:A System for Detecting Access Control Misconfigurations.Tathagata Das,Ranjita Bhagwan,Prasad Naldurg12.Cling:A Memory Allocator to Mitigate Dangling Pointers.Periklis Akritidis13.ZKPDL:A Language-Based System for Efficient Zero-Knowledge Proofs and Electronic Cash.Sarah Meiklejohn,C.Chris Erway,Alptekin Kupcu,Theodora Hinkle,Anna Lysyanskaya14.P4P:Practical Large-Scale Privacy-Preserving Distributed Computation Robust against Malicious Users.Yitao Duan,John Canny,Justin Zhan,15.SEPIA:Privacy-Preserving Aggregation of Multi-Domain Network Events and Statistics.Martin Burkhart,Mario Strasser,Dilip Many,Xenofontas Dimitropoulos16.Dude,Where’s That IP?Circumventing Measurement-based IP Geolocation.Phillipa Gill,Yashar Ganjali,Bernard Wong,David Lie17.Idle Port Scanning and Non-interference Analysis of Network Protocol Stacks Using Model Checking.Roya Ensafi,Jong Chun Park,Deepak Kapur,Jedidiah R.Crandall18.Building a Dynamic Reputation System for DNS.Manos Antonakakis,Roberto Perdisci,David Dagon,Wenke Lee,Nick Feamster19.Scantegrity II Municipal Election at Takoma Park:The First E2E Binding Governmental Election with Ballot Privacy.R.Carback,D.Chaum,J.Clark,J.Conway,A.Essex,P.S.Herrnson,T.Mayberry,S.Popoveniuc,R.L.Rivest,E.Shen,A.T.Sherman,P.L.Vora20.Acoustic Side-Channel Attacks on Printers.Michael Backes,Markus Durmuth,Sebastian Gerling,Manfred Pinkal,Caroline Sporleder21.Security and Privacy Vulnerabilities of In-Car Wireless Networks:A Tire Pressure Monitoring System Case Study.Ishtiaq Rouf,Rob Miller,Hossen Mustafa,Travis Taylor,Sangho Oh,Wenyuan Xu,Marco Gruteser,Wade Trappe,Ivan Seskar 22.VEX:Vetting Browser Extensions for Security Vulnerabilities.(Best Paper)Sruthi Bandhakavi,Samuel T.King,P.Madhusudan,Marianne Winslett23.Securing Script-Based Extensibility in Web Browsers.Vladan Djeric,Ashvin Goel24.AdJail:Practical Enforcement of Confidentiality and Integrity Policies on Web Advertisements.Mike Ter Louw,Karthik Thotta Ganesh,V.N.Venkatakrishnan25.Realization of RF Distance Bounding.Kasper Bonne Rasmussen,Srdjan Capkun26.The Case for Ubiquitous Transport-Level Encryption.Andrea Bittau,Michael Hamburg,Mark Handley,David Mazieres,Dan Boneh27.Automatic Generation of Remediation Procedures for Malware Infections.Roberto Paleari,Lorenzo Martignoni,Emanuele Passerini,Drew Davidson,Matt Fredrikson,Jon Giffin,Somesh Jha28.Re:CAPTCHAs-Understanding CAPTCHA-Solving Services in an Economic Context.Marti Motoyama,Kirill Levchenko,Chris Kanich,Damon McCoy,Geoffrey M.Voelker,Stefan Savage29.Chipping Away at Censorship Firewalls with User-Generated Content.Sam Burnett,Nick Feamster,Santosh Vempala30.Fighting Coercion Attacks in Key Generation using Skin Conductance.Payas Gupta,Debin GaoACM CCS20101.Security Analysis of India’s Electronic Voting Machines.Scott Wolchok,Erik Wustrow,J.Alex Halderman,Hari Prasad,Rop Gonggrijp2.Dissecting One Click Frauds.Nicolas Christin,Sally S.Yanagihara,Keisuke Kamataki3.@spam:The Underground on140Characters or Less.Chris Grier,Kurt Thomas,Vern Paxson,Michael Zhang4.HyperSentry:Enabling Stealthy In-context Measurement of Hypervisor Integrity.Ahmed M.Azab,Peng Ning,Zhi Wang,Xuxian Jiang,Xiaolan Zhang,Nathan C.Skalsky5.Trail of Bytes:Efficient Support for Forensic Analysis.Srinivas Krishnan,Kevin Z.Snow,Fabian Monrose6.Survivable Key Compromise in Software Update Systems.Justin Samuel,Nick Mathewson,Justin Cappos,Roger Dingledine7.A Methodology for Empirical Analysis of the Permission-Based Security Models and its Application to Android.David Barrera,H.Gunes Kayacik,Paul C.van Oorschot,Anil Somayaji8.Mobile Location Tracking in Metropolitan Areas:malnets and others.Nathanial Husted,Steve Myers9.On Pairing Constrained Wireless Devices Based on Secrecy of Auxiliary Channels:The Case of Acoustic Eavesdropping.Tzipora Halevi,Nitesh Saxena10.PinDr0p:Using Single-Ended Audio Features to Determine Call Provenance.Vijay A.Balasubramaniyan,Aamir Poonawalla,Mustaque Ahamad,Michael T.Hunter,Patrick Traynor11.Building Efficient Fully Collusion-Resilient Traitor Tracing and Revocation Schemes.Sanjam Garg,Abishek Kumarasubramanian,Amit Sahai,Brent Waters12.Algebraic Pseudorandom Functions with Improved Efficiency from the Augmented Cascade.Dan Boneh,Hart Montgomery,Ananth Raghunathan13.Practical Leakage-Resilient Pseudorandom Generators.Yu Yu,Francois-Xavier Standaert,Olivier Pereira,Moti Yung14.Practical Leakage-Resilient Identity-Based Encryption from Simple Assumptions.Sherman S.M.Chow,Yevgeniy Dodis,Yannis Rouselakis,Brent Waters15.Testing Metrics for Password Creation Policies by Attacking Large Sets of Revealed Passwords.Matt Weir,Sudhir Aggarwal,Michael Collins,Henry Stern16.The Security of Modern Password Expiration:An Algorithmic Framework and Empirical Analysis.Yinqian Zhang,Fabian Monrose,Michael K.Reiter17.Attacks and Design of Image Recognition CAPTCHAs.Bin Zhu,JeffYan,Chao Yang,Qiujie Li,Jiu Liu,Ning Xu,Meng Yi18.Robusta:Taming the Native Beast of the JVM.Joseph Siefers,Gang Tan,Greg Morrisett19.Retaining Sandbox Containment Despite Bugs in Privileged Memory-Safe Code.Justin Cappos,Armon Dadgar,JeffRasley,Justin Samuel,Ivan Beschastnikh,Cosmin Barsan,Arvind Krishnamurthy,Thomas Anderson20.A Control Point for Reducing Root Abuse of File-System Privileges.Glenn Wurster,Paul C.van Oorschot21.Modeling Attacks on Physical Unclonable Functions.Ulrich Ruehrmair,Frank Sehnke,Jan Soelter,Gideon Dror,Srinivas Devadas,Juergen Schmidhuber22.Dismantling SecureMemory,CryptoMemory and CryptoRF.Flavio D.Garcia,Peter van Rossum,Roel Verdult,Ronny Wichers Schreur23.Attacking and Fixing PKCS#11Security Tokens.Matteo Bortolozzo,Matteo Centenaro,Riccardo Focardi,Graham Steel24.An Empirical Study of Privacy-Violating Information Flows in JavaScript Web Applications.Dongseok Jang,Ranjit Jhala,Sorin Lerner,Hovav Shacham25.DIFC Programs by Automatic Instrumentation.William Harris,Somesh Jha,Thomas Reps26.Predictive Black-box Mitigation of Timing Channels.Aslan Askarov,Danfeng Zhang,Andrew Myers27.In Search of an Anonymous and Secure Lookup:Attacks on Structured Peer-to-peer Anonymous Communication Systems.Qiyan Wang,Prateek Mittal,Nikita Borisov28.Recruiting New Tor Relays with BRAIDS.Rob Jansen,Nicholas Hopper,Yongdae Kim29.An Improved Algorithm for Tor Circuit Scheduling.Can Tang,Ian Goldberg30.Dissent:Accountable Anonymous Group Messaging.Henry Corrigan-Gibbs,Bryan Ford31.Abstraction by Set-Membership—Verifying Security Protocols and Web Services with Databases.Sebastian Moedersheim。
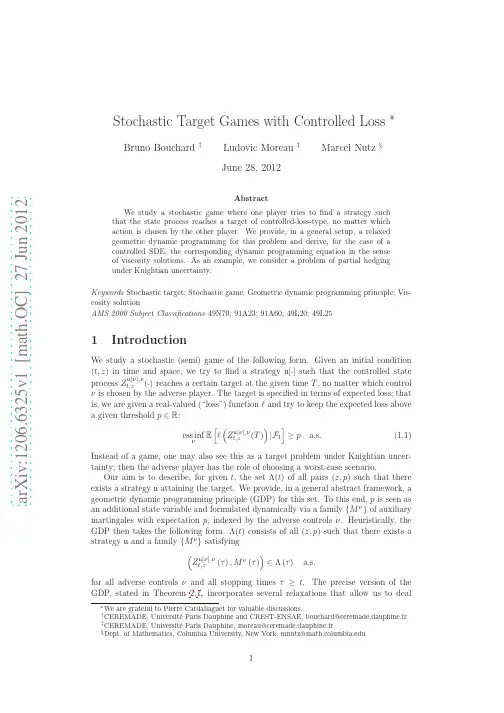

Rapid prototyping of Matlab/Java Distributed Applications using theJavaPorts components frameworkElias S. ManolakosElectrical and Computer Engineering DepartmentCountry of Citizenship: USAAreas:Networked Embedded SystemsSoftware Architecture, Reusablity, Scalability, and StandardsMiddleware Libraries and Application Programming InterfacesPreference: Oral PresentationOverviewAlthough PC clusters have become a commodity, there is still a lack of software technologies for the rapid prototyping and evaluation of end-to-end distributed computation strategies for heterogeneous clusters. Such applications may involve a large number of tasks (depicted as small circles in the task graph of Figure 1) which interact while running in the different nodes of a heterogeneous network, that possibly includes smart sensors, embedded controllers, various types of PCs, compute/data servers etc.At Northeastern University we are developing JavaPorts (JP) [1] [2], a novel component-based distributed processing framework which provides to application developers:• The capability to create, modify and reuse across applications and platforms softwareJavaPorts makes it easy for a team of collaborators with limited expertise in distributed processing to: (a) define an application in a top-down fashion, (b) to generate software components (for each task), (c) to execute the components at any node in the network without having to change any part of the source code. The high level of task location transparency supported by JP minimizes the human effort and the cost of software re-engineering, thus allowing more application design iterations in a fixed amount of time. During the last year we have completed a new JP software release v 2.1 in which we added:• a graphical tool for visual application (task graph) development and management. • an automatically implemented scheme for launching and terminating gracefully a distributed application. Releasing the code developer from the distributed termination responsibility removes a major headache in developing programs for clusters (as it can be attested by users of message passing systems such as MPI and PVM).• Run-time support for a variety of networks of workstations, including Linux- and Solaris-based clusters (with and without NFS capabilities)With Matlab v. 6 now available (which supports Java) we have also achieved the full integration of Matlab components into the JavaPorts framework. A developer can mix, into the same distributed application, any number of Matlab and Java components that may interact directly (not via files) and pass messages anonymously to each other using the JavaPorts communication API. Such a capability is essential because although the Matlab code base is increasing rapidly there is still no easy mechanism for integrating Matlab functions into a distributed computation without investing a substantial effort in re-coding. JavaPorts not only allows us to implement arbitrary patterns of component interactions but also supports the development of mixed Java/Matlab distributed applications for heterogeneous clusters with computers running under different operating systems and possibly including reconfigurable hardware boards (FPGAs) to accelerate a specific part of the overall network computation (joint work with Prof. M. Leeser, Northeastern University [3]). In the presentation we will discuss different application examples and present encouraging performance data.References[1] E. S. Manolakos, D. Galatopoullos, A. Funk, "Component-based peer-to-peer distributed processing in heterogeneous networks using JavaPorts", Proceedings of the IEEE Conference on Network Computing, pp. 234-237, February 2002.[2] E. S. Manolakos, D. Galatopoullos, A. Funk, "JavaPorts: An Environment for the Rapid Prototyping of Heterogeneous Network-centric Distributed Processing Applications" in the Proceedings of the Fifth Workshop on High Performance Embedded Computing (HPEC-01), pp. 149-151, MIT Lincoln Labs, Lexington, MA, November 2001.[3] L. A. King, H. Quinn, M. Leeser, D. Galatopoullos, E.S. Manolakos, "Runtime Execution of Reconfigurable Hardware in a Java Environment" in the Proceedings of the IEEE International Conference on Computer Design (ICCD-01), pp. 380-385, September 2001.。
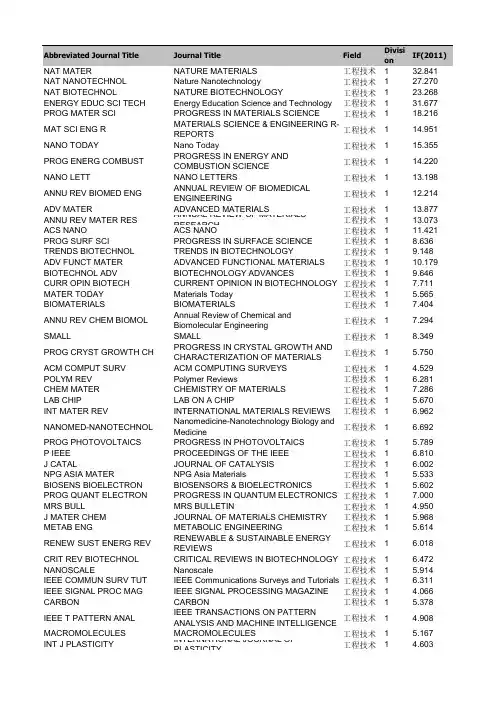
NAT NANOTECHNOL Nature Nanotechnology工程技术127.270 NAT BIOTECHNOL NATURE BIOTECHNOLOGY工程技术123.268 ENERGY EDUC SCI TECH Energy Education Science and Technology工程技术131.677 PROG MATER SCI PROGRESS IN MATERIALS SCIENCE工程技术118.216 MAT SCI ENG R MATERIALS SCIENCE & ENGINEERING R-RE工程技术114.951 NANO TODAY Nano Today工程技术115.355 PROG ENERG COMBUST PROGRESS IN ENERGY AND COMBUSTION工程技术114.220 NANO LETT NANO LETTERS工程技术113.198 ANNU REV BIOMED ENG ANNUAL REVIEW OF BIOMEDICAL ENGINEE工程技术112.214 ADV MATER ADVANCED MATERIALS工程技术113.877 ANNU REV MATER RES ANNUAL REVIEW OF MATERIALS RESEARC工程技术113.073 ACS NANO ACS NANO工程技术111.421 PROG SURF SCI PROGRESS IN SURFACE SCIENCE工程技术18.636 TRENDS BIOTECHNOL TRENDS IN BIOTECHNOLOGY工程技术19.148 ADV FUNCT MATER ADVANCED FUNCTIONAL MATERIALS工程技术110.179 BIOTECHNOL ADV BIOTECHNOLOGY ADVANCES工程技术19.646 CURR OPIN BIOTECH CURRENT OPINION IN BIOTECHNOLOGY工程技术17.711 MATER TODAY Materials Today工程技术1 5.565 BIOMATERIALS BIOMATERIALS工程技术17.404 ANNU REV CHEM BIOMOL Annual Review of Chemical and Biomolecular E工程技术17.294 SMALL SMALL工程技术18.349 PROG CRYST GROWTH CH PROGRESS IN CRYSTAL GROWTH AND CHA工程技术1 5.750 ACM COMPUT SURV ACM COMPUTING SURVEYS工程技术1 4.529 POLYM REV Polymer Reviews工程技术1 6.281 CHEM MATER CHEMISTRY OF MATERIALS工程技术17.286 LAB CHIP LAB ON A CHIP工程技术1 5.670 INT MATER REV INTERNATIONAL MATERIALS REVIEWS工程技术1 6.962 NANOMED-NANOTECHNOL Nanomedicine-Nanotechnology Biology and Me工程技术1 6.692 PROG PHOTOVOLTAICS PROGRESS IN PHOTOVOLTAICS工程技术1 5.789 P IEEE PROCEEDINGS OF THE IEEE工程技术1 6.810 J CATAL JOURNAL OF CATALYSIS工程技术1 6.002 NPG ASIA MATER NPG Asia Materials工程技术1 5.533 BIOSENS BIOELECTRON BIOSENSORS & BIOELECTRONICS工程技术1 5.602 PROG QUANT ELECTRON PROGRESS IN QUANTUM ELECTRONICS工程技术17.000 MRS BULL MRS BULLETIN工程技术1 4.950 J MATER CHEM JOURNAL OF MATERIALS CHEMISTRY工程技术1 5.968 METAB ENG METABOLIC ENGINEERING工程技术1 5.614 RENEW SUST ENERG REV RENEWABLE & SUSTAINABLE ENERGY REV工程技术1 6.018 CRIT REV BIOTECHNOL CRITICAL REVIEWS IN BIOTECHNOLOGY工程技术1 6.472 NANOSCALE Nanoscale工程技术1 5.914 IEEE COMMUN SURV TUT IEEE Communications Surveys and Tutorials工程技术1 6.311 IEEE SIGNAL PROC MAG IEEE SIGNAL PROCESSING MAGAZINE工程技术1 4.066 CARBON CARBON工程技术1 5.378 IEEE T PATTERN ANAL IEEE TRANSACTIONS ON PATTERN ANALYS工程技术1 4.908 MACROMOLECULES MACROMOLECULES工程技术1 5.167 INT J PLASTICITY INTERNATIONAL JOURNAL OF PLASTICITY工程技术1 4.603 BIOTECHNOL BIOFUELS Biotechnology for Biofuels工程技术1 6.088 MIS QUART MIS QUARTERLY工程技术1 4.447 SIAM J IMAGING SCI SIAM Journal on Imaging Sciences工程技术1 4.656 SOFT MATTER Soft Matter工程技术1 4.390 ACTA BIOMATER Acta Biomaterialia工程技术1 4.865 BIORESOURCE TECHNOL BIORESOURCE TECHNOLOGY工程技术1 4.980 ADV APPL MECH ADVANCES IN APPLIED MECHANICS工程技术1 5.000 ELECTROCHEM COMMUN ELECTROCHEMISTRY COMMUNICATIONS工程技术1 4.859MOL NUTR FOOD RES MOLECULAR NUTRITION & FOOD RESEARC工程技术1 4.301 IEEE T IND ELECTRON IEEE TRANSACTIONS ON INDUSTRIAL ELEC工程技术1 5.160 MACROMOL RAPID COMM MACROMOLECULAR RAPID COMMUNICATIO工程技术1 4.596 SOL ENERG MAT SOL C SOLAR ENERGY MATERIALS AND SOLAR CE工程技术1 4.542 J POWER SOURCES JOURNAL OF POWER SOURCES工程技术1 4.951 CRIT REV FOOD SCI CRITICAL REVIEWS IN FOOD SCIENCE AND工程技术1 4.789 CURR OPIN SOLID ST M CURRENT OPINION IN SOLID STATE & MATE工程技术1 4.233 INT J COMPUT VISION INTERNATIONAL JOURNAL OF COMPUTER 工程技术1 3.741 IEEE T EVOLUT COMPUT IEEE TRANSACTIONS ON EVOLUTIONARY C工程技术1 3.341 INT J HYDROGEN ENERG INTERNATIONAL JOURNAL OF HYDROGEN 工程技术1 4.054 J HAZARD MATER JOURNAL OF HAZARDOUS MATERIALS工程技术1 4.173 MED IMAGE ANAL MEDICAL IMAGE ANALYSIS工程技术1 4.424 HUM-COMPUT INTERACT HUMAN-COMPUTER INTERACTION工程技术1 1.476 MICROB CELL FACT Microbial Cell Factories工程技术1 3.552 INT J NEURAL SYST International Journal of Neural Systems工程技术1 4.284 TRENDS FOOD SCI TECH TRENDS IN FOOD SCIENCE & TECHNOLOGY工程技术1 3.672 IEEE J SEL AREA COMM IEEE JOURNAL ON SELECTED AREAS IN CO工程技术1 3.413 ORG ELECTRON ORGANIC ELECTRONICS工程技术1 4.047 ACTA MATER ACTA MATERIALIA工程技术1 3.755 APPL ENERG APPLIED ENERGY工程技术1 5.106 ACS APPL MATER INTER ACS Applied Materials & Interfaces工程技术1 4.525 BIOTECHNOL BIOENG BIOTECHNOLOGY AND BIOENGINEERING工程技术1 3.946 IEEE T POWER ELECTR IEEE TRANSACTIONS ON POWER ELECTRO工程技术1 4.650 BIOMASS BIOENERG BIOMASS & BIOENERGY工程技术1 3.646 ELECTROCHIM ACTA ELECTROCHIMICA ACTA工程技术1 3.832 ANNU REV FOOD SCI T Annual Review of Food Science and Technolog工程技术1 3.600 NANOTECHNOLOGY NANOTECHNOLOGY工程技术1 3.979 ACM T GRAPHIC ACM TRANSACTIONS ON GRAPHICS工程技术1 3.489 J MEMBRANE SCI JOURNAL OF MEMBRANE SCIENCE工程技术1 3.850 SENSOR ACTUAT B-CHEM SENSORS AND ACTUATORS B-CHEMICAL工程技术1 3.898 APPL SPECTROSC REV APPLIED SPECTROSCOPY REVIEWS工程技术2 3.385 IEEE J SEL TOP QUANT IEEE JOURNAL OF SELECTED TOPICS IN QU工程技术2 3.780 IEEE T FUZZY SYST IEEE TRANSACTIONS ON FUZZY SYSTEMS工程技术2 4.260 FOOD CHEM FOOD CHEMISTRY工程技术2 3.655 PLASMONICS Plasmonics 工程技术2 2.989 J NEURAL ENG Journal of Neural Engineering工程技术2 3.837 MICROFLUID NANOFLUID Microfluidics and Nanofluidics工程技术2 3.371 ENERGY ENERGY工程技术2 3.487 FUEL FUEL工程技术2 3.248 INT J NONLIN SCI NUM INTERNATIONAL JOURNAL OF NONLINEAR 工程技术2 1.484 FOOD MICROBIOL FOOD MICROBIOLOGY工程技术2 3.283 BIOMED MICRODEVICES BIOMEDICAL MICRODEVICES工程技术2 3.032 APPL MICROBIOL BIOT APPLIED MICROBIOLOGY AND BIOTECHNO工程技术2 3.425 CURR PROTEOMICS Current Proteomics工程技术2 3.179 BIOMECH MODEL MECHAN Biomechanics and Modeling in Mechanobiology工程技术2 3.192 IEEE J SOLID-ST CIRC IEEE JOURNAL OF SOLID-STATE CIRCUITS工程技术2 3.226 INT J FOOD MICROBIOL INTERNATIONAL JOURNAL OF FOOD MICRO工程技术2 3.327 INT J NANOMED International Journal of Nanomedicine 工程技术2 3.130 CHEM ENG J CHEMICAL ENGINEERING JOURNAL工程技术2 3.461 SCI TECHNOL ADV MAT SCIENCE AND TECHNOLOGY OF ADVANCED工程技术2 3.513 FOOD HYDROCOLLOID FOOD HYDROCOLLOIDS工程技术2 3.473 CORROS SCI CORROSION SCIENCE工程技术2 3.734 MICROSC MICROANAL MICROSCOPY AND MICROANALYSIS工程技术2 3.007 J MECH BEHAV BIOMED Journal of the Mechanical Behavior of Biomedic工程技术2 2.814 COMBUST FLAME COMBUSTION AND FLAME工程技术2 3.585 INT J ROBOT RES INTERNATIONAL JOURNAL OF ROBOTICS R工程技术2 3.107 ENVIRON MODELL SOFTW ENVIRONMENTAL MODELLING & SOFTWAR工程技术2 3.114IEEE COMMUN MAG IEEE COMMUNICATIONS MAGAZINE工程技术2 3.785 FUEL CELLS Fuel Cells工程技术2 3.149 J NANOPART RES JOURNAL OF NANOPARTICLE RESEARCH工程技术2 3.287 MAR BIOTECHNOL MARINE BIOTECHNOLOGY工程技术2 3.430 J STAT SOFTW Journal of Statistical Software工程技术2 4.010 INFORM SCIENCES INFORMATION SCIENCES工程技术2 2.833 DENT MATER DENTAL MATERIALS工程技术2 3.135 COMPOS SCI TECHNOL COMPOSITES SCIENCE AND TECHNOLOGY工程技术2 3.144 J BIOTECHNOL JOURNAL OF BIOTECHNOLOGY工程技术2 3.045 IEEE COMPUT INTELL M IEEE Computational Intelligence Magazine工程技术2 3.368 J CIV ENG MANAG Journal of Civil Engineering and Management工程技术2 2.171 IEEE T IMAGE PROCESS IEEE TRANSACTIONS ON IMAGE PROCESSI工程技术2 3.042 IEEE T SYST MAN CY B IEEE TRANSACTIONS ON SYSTEMS MAN AN工程技术2 3.080 INT J ELECTROCHEM SC International Journal of Electrochemical Science工程技术2 3.729 P COMBUST INST PROCEEDINGS OF THE COMBUSTION INST工程技术2 3.633 DYES PIGMENTS DYES AND PIGMENTS工程技术2 3.126 IEEE IND ELECTRON M IEEE Industrial Electronics Magazine工程技术2 5.000 SEP PURIF TECHNOL SEPARATION AND PURIFICATION TECHNOL工程技术2 2.921 CELLULOSE CELLULOSE工程技术2 3.600 GOLD BULL GOLD BULLETIN工程技术2 3.517 COMPUT-AIDED CIV INF COMPUTER-AIDED CIVIL AND INFRASTRUC工程技术2 3.382 J BIOMED MATER RES A JOURNAL OF BIOMEDICAL MATERIALS RES工程技术2 2.625 J SUPERCRIT FLUID JOURNAL OF SUPERCRITICAL FLUIDS工程技术2 2.860 IEEE T NEURAL NETWOR IEEE TRANSACTIONS ON NEURAL NETWOR工程技术2 2.952 SCRIPTA MATER SCRIPTA MATERIALIA工程技术2 2.699 IBM J RES DEV IBM JOURNAL OF RESEARCH AND DEVELO工程技术20.723 J ACM JOURNAL OF THE ACM工程技术2 2.353 J BIOACT COMPAT POL JOURNAL OF BIOACTIVE AND COMPATIBLE工程技术2 2.953 J MACH LEARN RES JOURNAL OF MACHINE LEARNING RESEAR工程技术2 2.561 VLDB J VLDB JOURNAL工程技术2 1.564 NANOSCALE RES LETT Nanoscale Research Letters工程技术2 2.726 IEEE ELECTR DEVICE L IEEE ELECTRON DEVICE LETTERS工程技术2 2.849 IEEE T INFORM THEORY IEEE TRANSACTIONS ON INFORMATION TH工程技术2 3.009 FUEL PROCESS TECHNOL FUEL PROCESSING TECHNOLOGY工程技术2 2.945 INNOV FOOD SCI EMERG Innovative Food Science & Emerging Technolo工程技术2 3.030 J NEUROENG REHABIL Journal of NeuroEngineering and Rehabilitation工程技术2 3.264 PROG AEROSP SCI PROGRESS IN AEROSPACE SCIENCES工程技术2 3.000 BIOFABRICATION Biofabrication工程技术2 3.480 IEEE T SOFTWARE ENG IEEE TRANSACTIONS ON SOFTWARE ENGI工程技术2 1.980 FOOD RES INT FOOD RESEARCH INTERNATIONAL工程技术2 3.150 SCI ADV MATER Science of Advanced Materials工程技术2 3.308 ADV BIOCHEM ENG BIOT ADVANCES IN BIOCHEMICAL ENGINEERING工程技术2 1.644 BMC BIOTECHNOL BMC BIOTECHNOLOGY工程技术2 2.349 FOOD CONTROL FOOD CONTROL工程技术2 2.656 ANNU REV INFORM SCI ANNUAL REVIEW OF INFORMATION SCIENC工程技术2 2.955 IEEE INTELL SYST IEEE INTELLIGENT SYSTEMS工程技术2 2.154 J FIELD ROBOT Journal of Field Robotics工程技术2 2.244 ARTIF INTELL ARTIFICIAL INTELLIGENCE工程技术2 2.252 IEEE T INTELL TRANSP IEEE TRANSACTIONS ON INTELLIGENT TRA工程技术2 3.452 RENEW ENERG RENEWABLE ENERGY工程技术2 2.978 IEEE-ASME T MECH IEEE-ASME TRANSACTIONS ON MECHATRO工程技术2 2.865 BIOTECHNIQUES BIOTECHNIQUES工程技术2 2.669 MABS-AUSTIN mAbs工程技术2 3.174 COMPR REV FOOD SCI F COMPREHENSIVE REVIEWS IN FOOD SCIEN工程技术2 3.724 FOOD CHEM TOXICOL FOOD AND CHEMICAL TOXICOLOGY工程技术2 2.999 IEEE T ROBOT IEEE Transactions on Robotics工程技术2 2.536 AUTOMATICA AUTOMATICA工程技术2 2.829IEEE INTERNET COMPUT IEEE INTERNET COMPUTING工程技术2 2.000 INTEGR COMPUT-AID E INTEGRATED COMPUTER-AIDED ENGINEER工程技术2 3.451 IEEE T GEOSCI REMOTE IEEE TRANSACTIONS ON GEOSCIENCE AND工程技术2 2.895 BIOCHEM ENG J BIOCHEMICAL ENGINEERING JOURNAL工程技术2 2.645 PATTERN RECOGN PATTERN RECOGNITION工程技术2 2.292 IEEE MICRO IEEE MICRO工程技术2 1.783 EARTHQ SPECTRA EARTHQUAKE SPECTRA工程技术20.894 J WEB SEMANT Journal of Web Semantics工程技术2 1.302 IEEE T SIGNAL PROCES IEEE TRANSACTIONS ON SIGNAL PROCESS工程技术2 2.628 REACT FUNCT POLYM REACTIVE & FUNCTIONAL POLYMERS工程技术2 2.479 ENERG FUEL ENERGY & FUELS工程技术2 2.721 COMPOS PART A-APPL S COMPOSITES PART A-APPLIED SCIENCE AN工程技术2 2.695 IEEE T ENERGY CONVER IEEE TRANSACTIONS ON ENERGY CONVER工程技术2 2.272 ISPRS J PHOTOGRAMM ISPRS JOURNAL OF PHOTOGRAMMETRY A工程技术2 2.885 IEEE POWER ENERGY M IEEE Power & Energy Magazine工程技术2 2.408 CEMENT CONCRETE RES CEMENT AND CONCRETE RESEARCH工程技术2 2.781 IEEE T MOBILE COMPUT IEEE TRANSACTIONS ON MOBILE COMPUTI工程技术2 2.283 COMPUT EDUC COMPUTERS & EDUCATION工程技术2 2.621 ENTERP INF SYST-UK Enterprise Information Systems工程技术2 3.684 J INF TECHNOL JOURNAL OF INFORMATION TECHNOLOGY工程技术2 2.321 J ELECTROCHEM SOC JOURNAL OF THE ELECTROCHEMICAL SOC工程技术2 2.590 J LIGHTWAVE TECHNOL JOURNAL OF LIGHTWAVE TECHNOLOGY工程技术2 2.784 J CEREAL SCI JOURNAL OF CEREAL SCIENCE工程技术2 2.073 TRANSPORT RES B-METH TRANSPORTATION RESEARCH PART B-MET工程技术2 2.856 J CHEM THERMODYN JOURNAL OF CHEMICAL THERMODYNAMIC工程技术2 2.422 ARCH COMPUT METHOD E ARCHIVES OF COMPUTATIONAL METHODS工程技术2 2.767 ANN BIOMED ENG ANNALS OF BIOMEDICAL ENGINEERING工程技术2 2.368 APPL SOFT COMPUT APPLIED SOFT COMPUTING工程技术2 2.612 INFORM MANAGE-AMSTER INFORMATION & MANAGEMENT工程技术2 2.214 J INSTRUM Journal of Instrumentation工程技术2 1.869 MAT SCI ENG C-MATER Materials Science & Engineering C-Materials fo工程技术2 2.686 IEEE CONTR SYST MAG IEEE CONTROL SYSTEMS MAGAZINE工程技术2 2.491 COMPUT INTELL-US COMPUTATIONAL INTELLIGENCE工程技术20.971 EXPERT SYST APPL EXPERT SYSTEMS WITH APPLICATIONS工程技术2 2.203 IEEE T ELECTRON DEV IEEE TRANSACTIONS ON ELECTRON DEVIC工程技术2 2.318 J EUR CERAM SOC JOURNAL OF THE EUROPEAN CERAMIC SO工程技术2 2.353 IEEE PHOTONICS J IEEE Photonics Journal工程技术2 2.320 INT DAIRY J INTERNATIONAL DAIRY JOURNAL工程技术2 2.401 PLANT FOOD HUM NUTR PLANT FOODS FOR HUMAN NUTRITION工程技术2 2.505 IEEE T POWER SYST IEEE TRANSACTIONS ON POWER SYSTEMS工程技术2 2.678 LWT-FOOD SCI TECHNOL LEBENSMITTEL-WISSENSCHAFT UND-TECH工程技术2 2.545 J IND MICROBIOL BIOT JOURNAL OF INDUSTRIAL MICROBIOLOGY 工程技术2 2.735 CHEM ENG SCI CHEMICAL ENGINEERING SCIENCE工程技术2 2.431 IEEE T AUTON MENT DE IEEE Transactions on Autonomous Mental Deve工程技术2 2.310 BIOTECHNOL PROGR BIOTECHNOLOGY PROGRESS工程技术2 2.340 J FOOD ENG JOURNAL OF FOOD ENGINEERING工程技术2 2.414 AUST J GRAPE WINE R AUSTRALIAN JOURNAL OF GRAPE AND WIN工程技术2 2.467 MEAT SCI MEAT SCIENCE工程技术2 2.275 IEEE PERVAS COMPUT IEEE PERVASIVE COMPUTING工程技术2 1.554 USER MODEL USER-ADAP USER MODELING AND USER-ADAPTED INTE工程技术2 1.400 EVOL COMPUT EVOLUTIONARY COMPUTATION 工程技术2 1.061 FOOD QUAL PREFER FOOD QUALITY AND PREFERENCE工程技术2 1.824 IEEE WIREL COMMUN IEEE WIRELESS COMMUNICATIONS工程技术2 2.575 IEEE J-STSP IEEE Journal of Selected Topics in Signal Proce工程技术2 2.880 SOL ENERGY SOLAR ENERGY工程技术2 2.475 IEEE T WIREL COMMUN IEEE TRANSACTIONS ON WIRELESS COMM工程技术2 2.586 COMMUN ACM COMMUNICATIONS OF THE ACM工程技术2 1.919BIOINTERPHASES Biointerphases 工程技术2 2.208 IEEE T AUTOMAT CONTR IEEE TRANSACTIONS ON AUTOMATIC CONT工程技术2 2.110 MATER CHEM PHYS MATERIALS CHEMISTRY AND PHYSICS工程技术2 2.234 ULTRAMICROSCOPY ULTRAMICROSCOPY工程技术2 2.471 J MATER SCI-MATER M JOURNAL OF MATERIALS SCIENCE-MATERI工程技术2 2.316 BIOMED MATER Biomedical Materials工程技术2 2.158 FUTURE GENER COMP SY FUTURE GENERATION COMPUTER SYSTEM工程技术2 1.978 J STRATEGIC INF SYST JOURNAL OF STRATEGIC INFORMATION SY工程技术2 1.457 J ALLOY COMPD JOURNAL OF ALLOYS AND COMPOUNDS工程技术2 2.289 PHOTONIC NANOSTRUCT Photonics and Nanostructures-Fundamentals an工程技术2 1.681 J BIOMED MATER RES B JOURNAL OF BIOMEDICAL MATERIALS RES工程技术2 2.147 COMPUT METHOD APPL M COMPUTER METHODS IN APPLIED MECHAN工程技术2 2.651 INT J COAL GEOL INTERNATIONAL JOURNAL OF COAL GEOLO工程技术2 2.542 J AM SOC INF SCI TEC JOURNAL OF THE AMERICAN SOCIETY FOR工程技术2 2.081 IEEE T VIS COMPUT GR IEEE TRANSACTIONS ON VISUALIZATION A工程技术2 2.215 DESALINATION DESALINATION工程技术2 2.590 J FOOD COMPOS ANAL JOURNAL OF FOOD COMPOSITION AND AN工程技术2 2.079 DECIS SUPPORT SYST DECISION SUPPORT SYSTEMS工程技术2 1.687 KNOWL INF SYST KNOWLEDGE AND INFORMATION SYSTEMS工程技术2 2.225 ARTIF LIFE ARTIFICIAL LIFE工程技术2 2.282 J AM CERAM SOC JOURNAL OF THE AMERICAN CERAMIC SOC工程技术2 2.272 J MICROMECH MICROENG JOURNAL OF MICROMECHANICS AND MICR工程技术2 2.105 IEEE ACM T NETWORK IEEE-ACM TRANSACTIONS ON NETWORKIN工程技术2 2.033 MATER LETT MATERIALS LETTERS工程技术2 2.307 NEURAL COMPUT NEURAL COMPUTATION工程技术2 1.884 INT J SEMANT WEB INF International Journal on Semantic Web and Info工程技术2 2.308 BUILD ENVIRON BUILDING AND ENVIRONMENT工程技术2 2.400 IEEE J QUANTUM ELECT IEEE JOURNAL OF QUANTUM ELECTRONIC工程技术2 1.879 IEEE NETWORK IEEE NETWORK工程技术2 2.239 COMPOS STRUCT COMPOSITE STRUCTURES工程技术2 2.240 IEEE ROBOT AUTOM MAG IEEE ROBOTICS & AUTOMATION MAGAZINE工程技术2 1.985 CHEMOMETR INTELL LAB CHEMOMETRICS AND INTELLIGENT LABOR工程技术2 1.920 INT J HEAT MASS TRAN INTERNATIONAL JOURNAL OF HEAT AND M工程技术2 2.407 FLUID PHASE EQUILIBR FLUID PHASE EQUILIBRIA工程技术2 2.139 IEEE T SYST MAN CY A IEEE TRANSACTIONS ON SYSTEMS MAN AN工程技术2 2.123 AICHE J AICHE JOURNAL工程技术2 2.261 J BIOMATER APPL JOURNAL OF BIOMATERIALS APPLICATION工程技术2 2.082 ENERG CONVERS MANAGE ENERGY CONVERSION AND MANAGEMENT工程技术2 2.216 IEEE T IND INFORM IEEE Transactions on Industrial Informatics工程技术2 2.990 IEEE T BIO-MED ENG IEEE TRANSACTIONS ON BIOMEDICAL ENG工程技术2 2.278 J CRYPTOL JOURNAL OF CRYPTOLOGY工程技术2 1.250 INTERMETALLICS INTERMETALLICS工程技术2 1.649 COMPUT CHEM ENG COMPUTERS & CHEMICAL ENGINEERING工程技术2 2.320 IEEE T CIRC SYST VID IEEE TRANSACTIONS ON CIRCUITS AND SY工程技术2 1.649 J SOLID STATE ELECTR JOURNAL OF SOLID STATE ELECTROCHEM工程技术2 2.131 J MANAGE INFORM SYST JOURNAL OF MANAGEMENT INFORMATION工程技术2 1.423 J MICROELECTROMECH S JOURNAL OF MICROELECTROMECHANICAL工程技术2 2.098 IEEE T SYST MAN CY C IEEE TRANSACTIONS ON SYSTEMS MAN AN工程技术2 2.009 J ASSOC INF SYST Journal of the Association for Information Syste工程技术2 1.667 MATER RES BULL MATERIALS RESEARCH BULLETIN工程技术2 2.105 FOOD ADDIT CONTAM A FOOD ADDITIVES AND CONTAMINANTS工程技术2 1.765 J ENG EDUC JOURNAL OF ENGINEERING EDUCATION工程技术2 1.569 BALT J ROAD BRIDGE E Baltic Journal of Road and Bridge Engineering工程技术2 1.610 INT J ELEC POWER INTERNATIONAL JOURNAL OF ELECTRICAL工程技术2 2.247 IND ENG CHEM RES INDUSTRIAL & ENGINEERING CHEMISTRY R工程技术2 2.237 EUR PHYS J E EUROPEAN PHYSICAL JOURNAL E工程技术2 1.944 INT J MACH TOOL MANU INTERNATIONAL JOURNAL OF MACHINE TO工程技术2 2.169J BIOMAT SCI-POLYM E JOURNAL OF BIOMATERIALS SCIENCE-POL工程技术2 1.691 NEURAL NETWORKS NEURAL NETWORKS工程技术2 2.182 J CHEM TECHNOL BIOT JOURNAL OF CHEMICAL TECHNOLOGY AND工程技术2 2.168 ACM T SENSOR NETWORK ACM Transactions on Sensor Networks 工程技术2 1.808 HYDROMETALLURGY HYDROMETALLURGY工程技术2 2.027 ENERG BUILDINGS ENERGY AND BUILDINGS工程技术2 2.386 MAT SCI ENG A-STRUCT MATERIALS SCIENCE AND ENGINEERING A工程技术2 2.003 IEEE PHOTONIC TECH L IEEE PHOTONICS TECHNOLOGY LETTERS工程技术2 2.191 IEEE ENG MED BIOL IEEE ENGINEERING IN MEDICINE AND BIOL工程技术2 2.057 INT J ADHES ADHES INTERNATIONAL JOURNAL OF ADHESION A工程技术2 2.170 INT J NUMER METH ENG INTERNATIONAL JOURNAL FOR NUMERICA工程技术2 2.009 FUNCT MATER LETT Functional Materials Letters工程技术20.724 IEEE T MICROW THEORY IEEE TRANSACTIONS ON MICROWAVE THE工程技术2 1.853 SMART MATER STRUCT SMART MATERIALS & STRUCTURES工程技术2 2.089 STRUCT SAF STRUCTURAL SAFETY工程技术2 1.867 INT J ENERG RES INTERNATIONAL JOURNAL OF ENERGY RES工程技术2 2.122 COMPUT LINGUIST COMPUTATIONAL LINGUISTICS工程技术20.721 J DISP TECHNOL Journal of Display Technology 工程技术2 2.280 BIODEGRADATION BIODEGRADATION工程技术2 2.017 IEEE T ANTENN PROPAG IEEE TRANSACTIONS ON ANTENNAS AND P工程技术2 2.151 MECH MATER MECHANICS OF MATERIALS工程技术2 1.769 J IND ENG CHEM JOURNAL OF INDUSTRIAL AND ENGINEERIN工程技术2 1.977 IEEE T NANOTECHNOL IEEE TRANSACTIONS ON NANOTECHNOLO工程技术2 2.292 ELECTROCHEM SOLID ST ELECTROCHEMICAL AND SOLID STATE LET工程技术2 1.995 APPL THERM ENG APPLIED THERMAL ENGINEERING工程技术2 2.064 SURF COAT TECH SURFACE & COATINGS TECHNOLOGY工程技术2 1.867 IEEE T KNOWL DATA EN IEEE TRANSACTIONS ON KNOWLEDGE AND工程技术2 1.657 CEMENT CONCRETE COMP CEMENT & CONCRETE COMPOSITES工程技术3 2.421 COAST ENG COASTAL ENGINEERING工程技术3 1.757 IET NANOBIOTECHNOL IET Nanobiotechnology工程技术3 1.833 DATA MIN KNOWL DISC DATA MINING AND KNOWLEDGE DISCOVER工程技术3 1.545 INT J APPROX REASON INTERNATIONAL JOURNAL OF APPROXIMAT工程技术3 1.948 POWDER TECHNOL POWDER TECHNOLOGY工程技术3 2.080 BIOPROC BIOSYST ENG BIOPROCESS AND BIOSYSTEMS ENGINEER工程技术3 1.809 STRUCT HEALTH MONIT STRUCTURAL HEALTH MONITORING-AN INT工程技术3 1.500 TRANSPORT RES A-POL TRANSPORTATION RESEARCH PART A-POL工程技术3 2.354 MECH SYST SIGNAL PR MECHANICAL SYSTEMS AND SIGNAL PROC工程技术3 1.824 MACROMOL MATER ENG MACROMOLECULAR MATERIALS AND ENGI工程技术3 1.986 J FUNCT FOODS Journal of Functional Foods工程技术3 2.446 J FOOD PROTECT JOURNAL OF FOOD PROTECTION工程技术3 1.937 COMPUT OPER RES COMPUTERS & OPERATIONS RESEARCH工程技术3 1.720 SYNTHETIC MET SYNTHETIC METALS工程技术3 1.829 ACM T WEB ACM Transactions on the Web 工程技术30.871 J PROCESS CONTR JOURNAL OF PROCESS CONTROL工程技术3 1.696 INT J THERM SCI INTERNATIONAL JOURNAL OF THERMAL SC工程技术3 2.142 ADSORPTION ADSORPTION-JOURNAL OF THE INTERNATI工程技术3 2.000 DIAM RELAT MATER DIAMOND AND RELATED MATERIALS工程技术3 1.913 TRANSPORT RES E-LOG TRANSPORTATION RESEARCH PART E-LOG工程技术3 1.648 THIN SOLID FILMS THIN SOLID FILMS工程技术3 1.890 COMPUT VIS IMAGE UND COMPUTER VISION AND IMAGE UNDERSTA工程技术3 1.340 IEEE T MULTIMEDIA IEEE TRANSACTIONS ON MULTIMEDIA工程技术3 1.935 ARTIF ORGANS ARTIFICIAL ORGANS工程技术3 2.000 APPL SURF SCI APPLIED SURFACE SCIENCE工程技术3 2.103 PROG ORG COAT PROGRESS IN ORGANIC COATINGS工程技术3 1.977 IEEE T INF FOREN SEC IEEE Transactions on Information Forensics an工程技术3 1.340 COMPUTER COMPUTER工程技术3 1.470 ACM T MATH SOFTWARE ACM TRANSACTIONS ON MATHEMATICAL S工程技术3 1.922J CHEM ENG DATA JOURNAL OF CHEMICAL AND ENGINEERING工程技术3 1.693 IEEE T BIOMED CIRC S IEEE Transactions on Biomedical Circuits and S工程技术3 2.032 ACM T COMPUT SYST ACM TRANSACTIONS ON COMPUTER SYST工程技术3 1.188 ENERG J ENERGY JOURNAL工程技术3 2.198 IEEE ACM T COMPUT BI IEEE-ACM Transactions on Computational Biolo工程技术3 1.543 FOOD SECUR Food Security工程技术3 1.970 PLASMA CHEM PLASMA P PLASMA CHEMISTRY AND PLASMA PROCES工程技术3 1.602 OPT MATER OPTICAL MATERIALS工程技术3 2.023 CHEM VAPOR DEPOS CHEMICAL VAPOR DEPOSITION工程技术3 1.796 SENSOR ACTUAT A-PHYS SENSORS AND ACTUATORS A-PHYSICAL工程技术3 1.802 MATER DESIGN MATERIALS & DESIGN工程技术3 2.200 IEEE MICROW WIREL CO IEEE MICROWAVE AND WIRELESS COMPON工程技术3 1.717 IEEE T BROADCAST IEEE TRANSACTIONS ON BROADCASTING工程技术3 1.703 CHEM ENG PROCESS CHEMICAL ENGINEERING AND PROCESSIN工程技术3 1.924 INT J CIRC THEOR APP INTERNATIONAL JOURNAL OF CIRCUIT THE工程技术3 1.625 TRANSPORT RES C-EMER TRANSPORTATION RESEARCH PART C-EME工程技术3 1.957 J FRANKLIN I JOURNAL OF THE FRANKLIN INSTITUTE-EN工程技术3 2.724 J MATER SCI JOURNAL OF MATERIALS SCIENCE工程技术3 2.015 SENSORS-BASEL SENSORS工程技术3 1.739 IET RENEW POWER GEN IET Renewable Power Generation工程技术3 1.742 POLYM ADVAN TECHNOL POLYMERS FOR ADVANCED TECHNOLOGIE工程技术3 2.007 KNOWL-BASED SYST KNOWLEDGE-BASED SYSTEMS工程技术3 2.422 INFORM FUSION Information Fusion工程技术3 1.467 POLYM TEST POLYMER TESTING工程技术3 1.608 WEAR WEAR工程技术3 1.872 J NUCL MATER JOURNAL OF NUCLEAR MATERIALS工程技术3 2.052 EMPIR SOFTW ENG EMPIRICAL SOFTWARE ENGINEERING工程技术3 1.854 APPL OPTICS APPLIED OPTICS工程技术3 1.748 AAPG BULL AAPG BULLETIN工程技术3 1.831 APPL BIOCHEM BIOTECH APPLIED BIOCHEMISTRY AND BIOTECHNOL工程技术3 1.943 FOOD NUTR BULL FOOD AND NUTRITION BULLETIN工程技术3 1.922 INT J HEAT FLUID FL INTERNATIONAL JOURNAL OF HEAT AND FL工程技术3 1.927 SIAM J COMPUT SIAM JOURNAL ON COMPUTING工程技术3 1.288 MACH LEARN MACHINE LEARNING工程技术3 1.587 COMPOS PART B-ENG COMPOSITES PART B-ENGINEERING工程技术3 1.731 FOOD BIOPHYS Food Biophysics工程技术3 2.187 MED ENG PHYS MEDICAL ENGINEERING & PHYSICS工程技术3 1.623 GPS SOLUT GPS SOLUTIONS工程技术3 1.667 INT J DAMAGE MECH INTERNATIONAL JOURNAL OF DAMAGE ME工程技术3 1.928 BIOINSPIR BIOMIM Bioinspiration & Biomimetics工程技术3 1.952 J AM OIL CHEM SOC JOURNAL OF THE AMERICAN OIL CHEMISTS工程技术3 1.773 MACROMOL RES MACROMOLECULAR RESEARCH工程技术3 1.153 EXP FLUIDS EXPERIMENTS IN FLUIDS工程技术3 1.735 INT J HUM-COMPUT ST INTERNATIONAL JOURNAL OF HUMAN-COM工程技术3 1.171 CURR NANOSCI Current Nanoscience工程技术3 1.776 J MICROSC-OXFORD JOURNAL OF MICROSCOPY-OXFORD工程技术3 1.631 ANNU REV CONTROL ANNUAL REVIEWS IN CONTROL工程技术3 1.319 BIOTECHNOL LETT BIOTECHNOLOGY LETTERS工程技术3 1.683 IEEE T INF TECHNOL B IEEE TRANSACTIONS ON INFORMATION TE工程技术3 1.676 METROLOGIA METROLOGIA工程技术3 1.750 IEEE SOFTWARE IEEE SOFTWARE工程技术3 1.508 IEEE T CONTR SYST T IEEE TRANSACTIONS ON CONTROL SYSTE工程技术3 1.766 EUR J LIPID SCI TECH EUROPEAN JOURNAL OF LIPID SCIENCE AN工程技术3 1.733 MACROMOL REACT ENG Macromolecular Reaction Engineering 工程技术3 1.848 COMPUT STRUCT COMPUTERS & STRUCTURES工程技术3 1.874 MATERIALS Materials工程技术3 1.677 DIG J NANOMATER BIOS Digest Journal of Nanomaterials and Biostructur工程技术3 1.200MODEL SIMUL MATER SC MODELLING AND SIMULATION IN MATERIAL工程技术3 2.298 J DATABASE MANAGE JOURNAL OF DATABASE MANAGEMENT工程技术30.875 AD HOC NETW Ad Hoc Networks工程技术3 2.110 CIRP ANN-MANUF TECHN CIRP ANNALS-MANUFACTURING TECHNOLO工程技术3 1.708 J THERM SPRAY TECHN JOURNAL OF THERMAL SPRAY TECHNOLOG工程技术3 1.812 IEEE T DEVICE MAT RE IEEE TRANSACTIONS ON DEVICE AND MAT工程技术3 1.543 ACM T SOFTW ENG METH ACM TRANSACTIONS ON SOFTWARE ENGIN工程技术3 1.269 J FOOD SCI JOURNAL OF FOOD SCIENCE工程技术3 1.658 APPL PHYS A-MATER APPLIED PHYSICS A-MATERIALS SCIENCE &工程技术3 1.630 IEEE T CIRCUITS-I IEEE TRANSACTIONS ON CIRCUITS AND SY工程技术3 1.970 J MICROENCAPSUL JOURNAL OF MICROENCAPSULATION工程技术3 1.553 APPL SPECTROSC APPLIED SPECTROSCOPY工程技术3 1.663 IEEE T ULTRASON FERR IEEE TRANSACTIONS ON ULTRASONICS FE工程技术3 1.694 INT J ROBUST NONLIN INTERNATIONAL JOURNAL OF ROBUST AND工程技术3 1.554 INT J FATIGUE INTERNATIONAL JOURNAL OF FATIGUE工程技术3 1.546 BIOL CYBERN BIOLOGICAL CYBERNETICS工程技术3 1.586 IEEE T AUDIO SPEECH IEEE Transactions on Audio Speech and Langu工程技术3 1.498 J APPL ELECTROCHEM JOURNAL OF APPLIED ELECTROCHEMISTR工程技术3 1.745 IEEE COMPUT GRAPH IEEE COMPUTER GRAPHICS AND APPLICAT工程技术3 1.411 J AUTOM REASONING JOURNAL OF AUTOMATED REASONING工程技术30.714 CERAM INT CERAMICS INTERNATIONAL工程技术3 1.751 LETT APPL MICROBIOL LETTERS IN APPLIED MICROBIOLOGY工程技术3 1.622 IEEE T VEH TECHNOL IEEE TRANSACTIONS ON VEHICULAR TECH工程技术3 1.921 J TAIWAN INST CHEM E Journal of the Taiwan Institute of Chemical Eng工程技术3 2.110 DATA KNOWL ENG DATA & KNOWLEDGE ENGINEERING工程技术3 1.422 INT J REFRACT MET H INTERNATIONAL JOURNAL OF REFRACTOR工程技术3 1.693 IEEE T COMP INTEL AI IEEE Transactions on Computational Intelligenc工程技术3 1.617 MACROMOL THEOR SIMUL MACROMOLECULAR THEORY AND SIMULAT工程技术3 1.709 CONTROL ENG PRACT CONTROL ENGINEERING PRACTICE工程技术3 1.481 NANOSC MICROSC THERM Nanoscale and Microscale Thermophysical Eng工程技术3 1.032 METALL MATER TRANS A METALLURGICAL AND MATERIALS TRANSA工程技术3 1.545 AUTON AGENT MULTI-AG AUTONOMOUS AGENTS AND MULTI-AGENT工程技术3 1.213 WIND ENERGY WIND ENERGY工程技术3 1.768 TRIBOL LETT TRIBOLOGY LETTERS工程技术3 1.582 J ARTIF INTELL RES JOURNAL OF ARTIFICIAL INTELLIGENCE RE工程技术3 1.143 TRIBOL INT TRIBOLOGY INTERNATIONAL工程技术3 1.553 MICRON MICRON工程技术3 1.527 DRY TECHNOL DRYING TECHNOLOGY工程技术3 2.084 COMPUT GRAPH FORUM COMPUTER GRAPHICS FORUM工程技术3 1.636 INT J REFRIG INTERNATIONAL JOURNAL OF REFRIGERAT工程技术3 1.817 NUMER HEAT TR A-APPL NUMERICAL HEAT TRANSFER PART A-APPL工程技术3 2.492 IEEE MICROW MAG IEEE MICROWAVE MAGAZINE工程技术3 2.111 IMAGE VISION COMPUT IMAGE AND VISION COMPUTING工程技术3 1.723 J MATER PROCESS TECH JOURNAL OF MATERIALS PROCESSING TEC工程技术3 1.783 AUTON ROBOT AUTONOMOUS ROBOTS工程技术3 1.500 INFORM SYST INFORMATION SYSTEMS工程技术3 1.198 MATER SCI ENG B-ADV Materials Science and Engineering B-Advanced工程技术3 1.518 WOOD SCI TECHNOL WOOD SCIENCE AND TECHNOLOGY工程技术3 1.727 J INTEL MAT SYST STR JOURNAL OF INTELLIGENT MATERIAL SYST工程技术3 1.953 MOB INF SYST Mobile Information Systems 工程技术3 2.432 J NANOPHOTONICS Journal of Nanophotonics工程技术3 1.570 SOFT COMPUT SOFT COMPUTING工程技术3 1.880 CHEM ENG RES DES CHEMICAL ENGINEERING RESEARCH & DES工程技术3 1.968 IEEE T PARALL DISTR IEEE TRANSACTIONS ON PARALLEL AND DI工程技术3 1.402 ELECTRON MATER LETT Electronic Materials Letters工程技术3 1.819 SOFT MATER SOFT MATERIALS工程技术3 1.154 IEEE T NANOBIOSCI IEEE TRANSACTIONS ON NANOBIOSCIENCE工程技术3 1.280J OPT COMMUN NETW Journal of Optical Communications and Networ工程技术3 1.872 ADV ENG MATER ADVANCED ENGINEERING MATERIALS工程技术3 1.185 INT COMMUN HEAT MASS INTERNATIONAL COMMUNICATIONS IN HEA工程技术3 1.892 OPT LASER ENG OPTICS AND LASERS IN ENGINEERING工程技术3 1.838 COMPUT IND COMPUTERS IN INDUSTRY工程技术3 1.529 ENG LIFE SCI ENGINEERING IN LIFE SCIENCES工程技术3 1.925 CONSTR BUILD MATER CONSTRUCTION AND BUILDING MATERIALS工程技术3 1.834 CMC-COMPUT MATER CON CMC-Computers Materials & Continua工程技术30.972 NONLINEAR DYNAM NONLINEAR DYNAMICS工程技术3 1.247 IEEE T DEPEND SECURE IEEE Transactions on Dependable and Secure C工程技术3 1.140 COMPUT IND ENG COMPUTERS & INDUSTRIAL ENGINEERING工程技术3 1.589 MICROELECTRON ENG MICROELECTRONIC ENGINEERING工程技术3 1.557 ADV ENG INFORM ADVANCED ENGINEERING INFORMATICS工程技术3 1.489 EARTHQ ENG STRUCT D EARTHQUAKE ENGINEERING & STRUCTURA工程技术3 1.778 INT J PHOTOENERGY INTERNATIONAL JOURNAL OF PHOTOENER工程技术3 1.769 B EARTHQ ENG Bulletin of Earthquake Engineering工程技术3 1.559 INFORM SOFTWARE TECH INFORMATION AND SOFTWARE TECHNOLO工程技术3 1.250 COMPUT ELECTRON AGR COMPUTERS AND ELECTRONICS IN AGRICU工程技术3 1.846 SCI TECHNOL WELD JOI SCIENCE AND TECHNOLOGY OF WELDING 工程技术3 1.735 IND MANAGE DATA SYST INDUSTRIAL MANAGEMENT & DATA SYSTEM工程技术3 1.472 INFORM PROCESS MANAG INFORMATION PROCESSING & MANAGEME工程技术3 1.119 IEEE SENS J IEEE SENSORS JOURNAL工程技术3 1.520 IEEE T NUCL SCI IEEE TRANSACTIONS ON NUCLEAR SCIENC工程技术3 1.447 ARTIF INTELL MED ARTIFICIAL INTELLIGENCE IN MEDICINE工程技术3 1.345 COMP MATER SCI COMPUTATIONAL MATERIALS SCIENCE工程技术3 1.574 IEEE T COMMUN IEEE TRANSACTIONS ON COMMUNICATION工程技术3 1.677 J SOL-GEL SCI TECHN JOURNAL OF SOL-GEL SCIENCE AND TECH工程技术3 1.632 FLAVOUR FRAG J FLAVOUR AND FRAGRANCE JOURNAL工程技术3 1.424 IEEE T COMPUT IEEE TRANSACTIONS ON COMPUTERS工程技术3 1.103 STRUCT MULTIDISCIP O STRUCTURAL AND MULTIDISCIPLINARY OP工程技术3 1.488 INT J IMPACT ENG INTERNATIONAL JOURNAL OF IMPACT ENG工程技术3 1.701 EUR FOOD RES TECHNOL EUROPEAN FOOD RESEARCH AND TECHNO工程技术3 1.566 J MATER RES JOURNAL OF MATERIALS RESEARCH工程技术3 1.434 TRANSPORT SCI TRANSPORTATION SCIENCE工程技术3 1.507 MATER CHARACT MATERIALS CHARACTERIZATION工程技术3 1.572 ENERGIES Energies工程技术3 1.865 REV SCI INSTRUM REVIEW OF SCIENTIFIC INSTRUMENTS工程技术3 1.367 IEEE T HAPTICS IEEE Transactions on Haptics工程技术3 1.490 EUR J INFORM SYST EUROPEAN JOURNAL OF INFORMATION SY工程技术3 1.500 NEUROCOMPUTING NEUROCOMPUTING工程技术3 1.580 ENG APPL ARTIF INTEL ENGINEERING APPLICATIONS OF ARTIFICIA工程技术3 1.665 ELECTRON COMMER R A Electronic Commerce Research and Application工程技术3 1.472 INFORMATICA-LITHUAN INFORMATICA工程技术3 1.627 COMPUT AIDED DESIGN COMPUTER-AIDED DESIGN工程技术3 1.234 SYST CONTROL LETT SYSTEMS & CONTROL LETTERS工程技术3 1.222 J POLYM ENVIRON JOURNAL OF POLYMERS AND THE ENVIRO工程技术3 1.349 J POLYM SCI POL PHYS JOURNAL OF POLYMER SCIENCE PART B-P工程技术3 1.531 COMPUT MATH APPL COMPUTERS & MATHEMATICS WITH APPLI工程技术3 1.747 J INF SCI JOURNAL OF INFORMATION SCIENCE工程技术3 1.299 TRANSPORTATION TRANSPORTATION工程技术3 1.023 J SENS STUD JOURNAL OF SENSORY STUDIES工程技术3 1.597 IEEE T SERV COMPUT IEEE Transactions on Services Computing工程技术3 1.468 IEEE GEOSCI REMOTE S IEEE Geoscience and Remote Sensing Letters工程技术3 1.560 J NANOSCI NANOTECHNO JOURNAL OF NANOSCIENCE AND NANOTEC工程技术3 1.563 INT J WEB GRID SERV International Journal of Web and Grid Services工程技术3 1.919 ENG ANAL BOUND ELEM ENGINEERING ANALYSIS WITH BOUNDARY工程技术3 1.451 J SOUND VIB JOURNAL OF SOUND AND VIBRATION工程技术3 1.588。
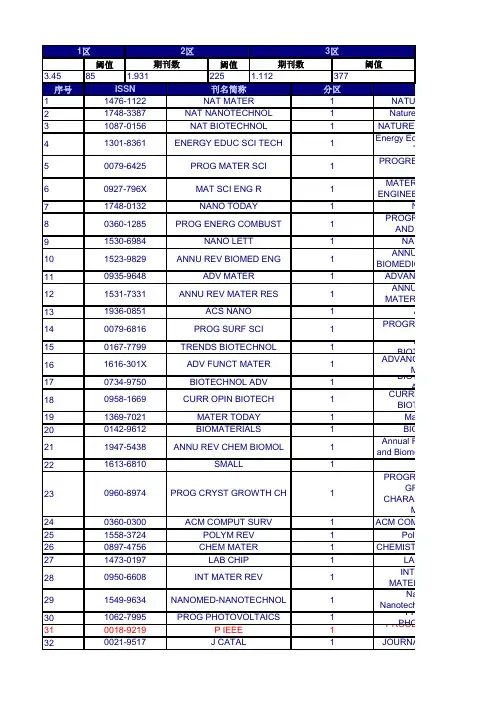
阈值阈值3.4585225序号123456789101112131415161718192021222324252627282930 31 32NanoNanotechnology Biology andPROPHOTOVOLTAICSPROCEEDIEEEJOURNALPROGRESGROWTH ANDCHARACTERIZATION OFMATERIALSACM COMPUPolymCHEMISTRYACPROGRESSCIENCETREBIOTECHNOLOGYADVANCEMATERIALSNANOANNUALBIOMEDICAL ENGINEERINGLAB OINTERMATERIALS REVIEWSBIOTECADVANCESCURRENBIOTECHNOLOGYMaterBIOMAnnual Revand Biomolecular EngineeringSADVANCEANNUALMATERIALS RESEARCHNATURENature NNATURE BIEnergy EducTechnologyPROGRESSSCIENCEMATERIAENGINEERING R-REPORTSNanPROGRESAND COMBUSTION刊111111111111111111111111377分区111111111549-9634NANOMED-NANOTECHNOL1062-7995PROG PHOTOVOLTAICS0018-9219P IEEE1369-7021MATER TODAY0142-9612BIOMATERIALS0021-9517J CATAL1473-0197LAB CHIP0950-6608INT MATER REV0960-8974PROG CRYST GROWTH CH0360-0300ACM COMPUT SURV1558-3724POLYM REV1616-301X ADV FUNCT MATER0734-9750BIOTECHNOL ADV0897-4756CHEM MATER1947-5438ANNU REV CHEM BIOMOL1613-6810SMALL0958-1669CURR OPIN BIOTECH1531-7331ANNU REV MATER RES1936-0851ACS NANO0079-6816PROG SURF SCI0167-7799TRENDS BIOTECHNOLISSN刊名简称1476-1122NAT MATER1748-3387NAT NANOTECHNOL1523-9829ANNU REV BIOMED ENG1区2区期刊数期刊数3区阈值1.931 1.1121087-0156NAT BIOTECHNOL1301-8361ENERGY EDUC SCI TECH0079-6425PROG MATER SCI0935-9648ADV MATER0927-796X MAT SCI ENG R1748-0132NANO TODAY0360-1285PROG ENERG COMBUST1530-6984NANO LETT33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 5051 52 5354 55 56 57 58 59 6061 62CRITICALFOOD SCIENCE ANDCURRENSOLID STATE & MATERIALSIEEE TRANINDUSTRIAL ELECTRONICSMACROMOLCOMMUNICATIONSSOLAMATERIALS AND SOLARJOURNASOURCESINTERNATIOF PLASTICITYBiotechnolMIS QSIAM JouSciencesBIORTECHNOLOGYADVANCEMECHANICSELECTROCOMMUNICATIONSMOLECULAFOOD RESEARCHJOURNALCHEMISTRYMETABOLICSoActa BNaIEEE CoSurveys and TutorialsIEEE SIGNAMAGAZINECAIEEE TRANPATTERN ANALYSIS ANDMACHINE INTELLIGENCEMACRORENESUSTAINABLE ENERGYCRITICALBIOTECHNOLOGYNPG ABIOSEBIOELECTRONICSPROGRESELECTRONICSMRS1111111111111111111111111111110378-7753J POWER SOURCES1040-8398CRIT REV FOOD SCI1388-2481ELECTROCHEM COMMUN1359-0286CURR OPIN SOLID ST M0278-0046IEEE T IND ELECTRON1022-1336MACROMOL RAPID COMM0927-0248SOL ENERG MAT SOL C1613-4125MOL NUTR FOOD RES1744-683X SOFT MATTER1742-7061ACTA BIOMATER0960-8524BIORESOURCE TECHNOL0065-2156ADV APPL MECH1754-6834BIOTECHNOL BIOFUELS0276-7783MIS QUART1053-5888IEEE SIGNAL PROC MAG0008-6223CARBON2040-3364NANOSCALE1936-4954SIAM J IMAGING SCI0162-8828IEEE T PATTERN ANAL0024-9297MACROMOLECULES0749-6419INT J PLASTICITY1553-877X IEEE COMMUN SURV TUT0883-7694MRS BULL0959-9428J MATER CHEM1364-0321RENEW SUST ENERG REV0738-8551CRIT REV BIOTECHNOL1096-7176METAB ENG1884-4049NPG ASIA MATER0956-5663BIOSENS BIOELECTRON0079-6727PROG QUANT ELECTRON63 64 65 6667 68 69 70 71 7273 74 7576 77 7879 8081 82 83 8485 86878889 90 91 92 93 94SENSACTUATORS B-CHEMICALAPPLIED SREVIEWSFOOD CPlaJournal of NMicrofluidicsENIEEE JOSELECTED TOPICS INQUANTUM ELECTRONICSIEEE TRANFUZZY SYSTEMSBIOTECHBIOENGINEERINGIEEE TRANPOWER ELECTRONICSBIOMASSELECTROAnnual RScience and TechnologyNANOTEACM TRANGRAPHICSJOURNALSCIENCETRENDS IN& TECHNOLOGYIEEE JOSELECTED AREAS INORGANICACTA MINTERNATIOF COMPUTER VISIONIEEE TRANEVOLUTIONARYAPPLIEACS ApplInterfacesINTERNATIOF HYDROGEN ENERGYJOURNAL OMATERIALSMEDICAL IMHUMANINTERACTIONMicrobialInternationalSystems222211112222111211111111111111111741-2560J NEURAL ENG1613-4982MICROFLUID NANOFLUID0308-8146FOOD CHEM0360-5442ENERGY0016-2361FUEL1557-1955PLASMONICS0376-7388J MEMBRANE SCI0925-4005SENSOR ACTUAT B-CHEM1077-260X IEEE J SEL TOP QUANT1063-6706IEEE T FUZZY SYST0961-9534BIOMASS BIOENERG0570-4928APPL SPECTROSC REV1941-1413ANNU REV FOOD SCI T0957-4484NANOTECHNOLOGY0730-0301ACM T GRAPHIC0013-4686ELECTROCHIM ACTA0306-2619APPL ENERG1944-8244ACS APPL MATER INTER0006-3592BIOTECHNOL BIOENG0885-8993IEEE T POWER ELECTR0733-8716IEEE J SEL AREA COMM1566-1199ORG ELECTRON1361-8415MED IMAGE ANAL0737-0024HUM-COMPUT INTERACT0360-3199INT J HYDROGEN ENERG1359-6454ACTA MATER1475-2859MICROB CELL FACT0129-0657INT J NEURAL SYST0924-2244TRENDS FOOD SCI TECH0304-3894J HAZARD MATER0920-5691INT J COMPUT VISION1089-778X IEEE T EVOLUT COMPUT9596 979899100 101 102 103 104 105106 107108 109 110 111 112 113 114 115116 117 118119 120 121 122 123 124DENTALCOMPOSAND TECHNOLOGYJOUBIOTECHNOLOGYIEEE CIntelligence MagazineJournal ofBehavior of BiomedicalCOMBUSTIINTERNATIOF ROBOTICS RESEARCHENVIRMODELLING & SOFTWARESCIETECHNOLOGY OFFOOD HYDJournal of Cand ManagementIEEE TRANIMAGE PROCESSINGIEEE COMMAGAZINEFuJOUNANOPARTICLE RESEARCHMARINE BIOJournal of SINFORMATCORROSMICROMICROANALYSISINTERNATIOF NONLINEAR SCIENCESAND NUMERICALSIMULATIONFOOD MIBIOMMICRODEVICESAPPLIED MAND BIOTECHNOLOGYIEEE JOURSTATE CIRCUITSINTERNATIOF FOOD MICROBIOLOGYInternatioNanomedicineCHEMICALJOURNALCurrenBiomechanicMechanobiology2222222222222222222222222222221392-3730J CIV ENG MANAG1057-7149IEEE T IMAGE PROCESS0266-3538COMPOS SCI TECHNOL0168-1656J BIOTECHNOL1388-0764J NANOPART RES1436-2228MAR BIOTECHNOL0163-6804IEEE COMMUN MAG1556-603X IEEE COMPUT INTELL M1548-7660J STAT SOFTW0020-0255INFORM SCIENCES0109-5641DENT MATER1615-6846FUEL CELLS1431-9276MICROSC MICROANAL1751-6161J MECH BEHAV BIOMED0278-3649INT J ROBOT RES1364-8152ENVIRON MODELL SOFTW1178-2013INT J NANOMED0010-2180COMBUST FLAME1468-6996SCI TECHNOL ADV MAT0268-005X FOOD HYDROCOLLOID0010-938X CORROS SCI1385-8947CHEM ENG J1570-1646CURR PROTEOMICS1617-7959BIOMECH MODEL MECHAN0018-9200IEEE J SOLID-ST CIRC0168-1605INT J FOOD MICROBIOL0740-0020FOOD MICROBIOL1387-2176BIOMED MICRODEVICES0175-7598APPL MICROBIOL BIOT1565-1339INT J NONLIN SCI NUM125126127128129130131132133134135136137138139140141142143144145146147148149150151152153Science of ANanoscale IEEE ELECLETTERSIEEE TRANINFORMATION THEORY FUEL PTECHNOLOGY PROGRESSSCIENCES BiofIEEE TRANSOFTWARE ENGINEERINGFOODINTERNATIONAL COMPUTEAND INFRASTRUCTUREENGINEERING JOURNAL OMATERIALS RESEARCHInnovativeEmerging Technologies Journal of Nand Rehabilitation SCRIPTA IBM JORESEARCH AND JOURNAL JOURNALAND COMPATIBLE JOURNALLEARNING RESEARCHVLDB JOUSUPERCRITICAL FLUIDS IEEE TRANNEURAL NETWORKS IEEE TRANSYSTEMS MAN AND CYBERNETICS PART B-CYBERNETICS InternatioElectrochemical Science PROCEEDCOMBUSTION INSTITUTE DYES AN IEEE IndusMagazineSEPARPURIFICATION CEL GOLD 222222222222222222222222222220098-5589IEEE T SOFTWARE ENG1947-2935SCI ADV MATER0963-9969FOOD RES INT 1466-8564INNOV FOOD SCI EMERG 1743-0003J NEUROENG REHABIL 0376-0421PROG AEROSP SCI 1758-5082BIOFABRICATION 0741-3106IEEE ELECTR DEVICE L 0018-9448IEEE T INFORM THEORY 0004-5411J ACM0883-9115J BIOACT COMPAT POL 1359-6462SCRIPTA MATER 0378-3820FUEL PROCESS TECHNOL 1532-4435J MACH LEARN RES 1066-8888VLDB J1931-7573NANOSCALE RES LETT 0018-8646IBM J RES DEV0017-1557GOLD BULL 1093-9687COMPUT-AIDED CIV INF 0896-8446J SUPERCRIT FLUID 1045-9227IEEE T NEURAL NETWOR1540-7489P COMBUST INST 1549-3296J BIOMED MATER RES A 1932-4529IEEE IND ELECTRON M 1383-5866SEP PURIF TECHNOL0969-0239CELLULOSE 0143-7208DYES PIGMENTS 1083-4419IEEE T SYST MAN CY B 1452-3981INT J ELECTROCHEM SC154155 156157158 159 160161 162 163164 165166167168 169 170171 172173174 175 176 177178 179 180181 182 183 184COMPOSAPPLIED SCIENCE ANDMANUFACTURINGIEEE TRANENERGY CONVERSIONISPRS JPHOTOGRAMMETRY ANDREMOTE SENSINGIEEE PoMagazineBIOCENGINEERING JOURNALPATTERNIEEEEARTHQUJournal ofIEEE TRANSIGNAL PROCESSINGREACTIVEPOLYMERSENERGFOOD ANTOXICOLOGYIEEE TraRoboticsAUTIEEECOMPUTINGANNUALINFORMATION SCIENCEAND TECHNOLOGYIEEE INSYSTEMSJournal ofARTIFICIALADVABIOCHEMICALENGINEERING /BIOTECHNOLOGYINTEGRATEAIDED ENGINEERINGIEEE TRANGEOSCIENCE AND REMOTESENSINGIEEE TRANINTELLIGENTTRANSPORTATIONSYSTEMSRENEWAIEEE-ASMEON MECHATRONICSBIOTECOMPREHEIN FOOD SCIENCE ANDFOOD SAFETYBMC BIOTFOOD22222222222222222222222222222220887-0624ENERG FUEL1359-835X COMPOS PART A-APPL S0924-2716ISPRS J PHOTOGRAMM1540-7977IEEE POWER ENERGY M0272-1732IEEE MICRO0885-8969IEEE T ENERGY CONVER1570-8268J WEB SEMANT1053-587X IEEE T SIGNAL PROCES1381-5148REACT FUNCT POLYM8755-2930EARTHQ SPECTRA1069-2509INTEGR COMPUT-AID E0196-2892IEEE T GEOSCI REMOTE1369-703X BIOCHEM ENG J0031-3203PATTERN RECOGN1552-3098IEEE T ROBOT0005-1098AUTOMATICA1083-4435IEEE-ASME T MECH0736-6205BIOTECHNIQUES1524-9050IEEE T INTELL TRANSP1089-7801IEEE INTERNET COMPUT1942-0862MABS-AUSTIN1541-4337COMPR REV FOOD SCI F0278-6915FOOD CHEM TOXICOL0960-1481RENEW ENERG0956-7135FOOD CONTROL0066-4200ANNU REV INFORM SCI1556-4959J FIELD ROBOT0004-3702ARTIF INTELL1541-1672IEEE INTELL SYST0724-6145ADV BIOCHEM ENG BIOT1472-6750BMC BIOTECHNOL185 186187 188189 190 191 192 193 194 195 196 197 198 199 200 201 202 203 204205 206 207 208 209 210 211 212JOURNEUROPEAN CERAMICIEEE PhoINTERNAJOURNALPLANT FOONUTRITIONIEEE CONTMAGAZINECOMPUINTELLIGENCEIEEE TRANPOWER SYSTEMSLEBENWISSENSCHAFT UND-TECHNOLOGIE-FOODSCIENCE ANDJOURNAL OMICROBIOLOGY &BIOTECHNOLOGYCHEMICALSCIENCEEXPERT SAPPLICATIONSIEEE TRANELECTRON DEVICESJOURNAL OTECHNOLOGYJOURNASCIENCETRANSRESEARCH PART B-JOURNALTHERMODYNAMICSAPPLIED SOINFORMANAGEMENTJournal ofMateriaEngineering C-Materials forARCCOMPUTATIONALANNALS OENGINEERINGCEMENT ARESEARCHIEEE TRANMOBILE COMPUTINGCOMPUTEREnterprisSystemsJOURNAL OTECHNOLOGYJOURNELECTROCHEMICAL22222222222222222222222222221367-5435J IND MICROBIOL BIOT0009-2509CHEM ENG SCI0885-8950IEEE T POWER SYST0023-6438LWT-FOOD SCI TECHNOL0018-9383IEEE T ELECTRON DEV0955-2219J EUR CERAM SOC0958-6946INT DAIRY J0921-9668PLANT FOOD HUM NUTR1748-0221J INSTRUM1943-0655IEEE PHOTONICS J1066-033X IEEE CONTR SYST MAG0824-7935COMPUT INTELL-US0957-4174EXPERT SYST APPL0928-4931MAT SCI ENG C-MATER1134-3060ARCH COMPUT METHOD E0090-6964ANN BIOMED ENG1568-4946APPL SOFT COMPUT0378-7206INFORM MANAGE-AMSTER0733-5210J CEREAL SCI0191-2615TRANSPORT RES B-METH0360-1315COMPUT EDUC1751-7575ENTERP INF SYST-UK0008-8846CEMENT CONCRETE RES0021-9614J CHEM THERMODYN0268-3962J INF TECHNOL0013-4651J ELECTROCHEM SOC0733-8724J LIGHTWAVE TECHNOL1536-1233IEEE T MOBILE COMPUT213214 215 216217 218219 220 221 222 223 224 225 226 227 228 229 230 231 232 233 234 235 236 237238239 240INTERNATIOF COAL GEOLOGYJOURNAMERICAN SOCIETY FORINFORMATION SCIENCEAND TECHNOLOGYMATERIALAND PHYSICSULTRAMFUTURECOMPUTER SYSTEMSJOURNALINFORMATION SYSTEMSJOURNAL OCOMPOUNDSPhotonics anFundamentals andJOURNAL OMATERIALS RESEARCHPART B-APPLIEDBIOMATERIALSCOMPUTEAPPLIED MECHANICS ANDENGINEERINGJOURNALSCIENCE-MATERIALS INMEDICINEBiomedFOOD QPREFERENCEIEEE WCOMMUNICATIONSIEEE JourTopics in Signal ProcessingSOLAIEEE TRANWIRELESSCOMMUNICACMBioinIEEE TRANAUTOMATIC CONTROLJOURNENGINEERINGAUSTRALIAGRAPE AND WINEMEATIEEE PCOMPUTINGUSER MOUSER-ADAPTEDEVOLCOMPUTATIONIEEE TraAutonomous MentalBIOTECPROGRESS22222222222222222222222222221532-2882J AM SOC INF SCI TEC0925-8388J ALLOY COMPD1569-4410PHOTONIC NANOSTRUCT0167-739X FUTURE GENER COMP SY1552-4973J BIOMED MATER RES B0045-7825COMPUT METHOD APPL M0166-5162INT J COAL GEOL0963-8687J STRATEGIC INF SYST0018-9286IEEE T AUTOMAT CONTR0254-0584MATER CHEM PHYS0957-4530J MATER SCI-MATER M1748-6041BIOMED MATER1932-4553IEEE J-STSP0304-3991ULTRAMICROSCOPY1536-1276IEEE T WIREL COMMUN0001-0782COMMUN ACM1934-8630BIOINTERPHASES0038-092X SOL ENERGY0924-1868USER MODEL USER-ADAP1063-6560EVOL COMPUT0950-3293FOOD QUAL PREFER1536-1284IEEE WIREL COMMUN1322-7130AUST J GRAPE WINE R0309-1740MEAT SCI1536-1268IEEE PERVAS COMPUT1943-0604IEEE T AUTON MENT DE8756-7938BIOTECHNOL PROGR0260-8774J FOOD ENG241 242243 244 245 246 247 248 249250 251252 253 254255 256257 258259 260261262 263 264 265 266267 268269COMPUTERENGINEERINGJOUBIOMATERIALSENERGY COMANAGEMENTIEEE TraIndustrial InformaticsIEEE TRANBIOMEDICAL ENGINEERINGBUILDENVIRONMENTIEEE JOQUANTUM ELECTRONICSIEEECOMPOSITIEEE-ACM TON NETWORKINGMATERIAJOURNAL OINTERIEEE RAUTOMATION MAGAZINECHEMOMINTELLIGENT LABORATORYSYSTEMSINTERNATIOF HEAT AND MASSFLUID PHAIEEE TRANSYSTEMS MAN ANDCYBERNETICS PART A-SYSTEMS AND HUMANSAICHENEURAL CInternatioSemantic Web andIEEE TRANVISUALIZATION ANDCOMPUTER GRAPHICSDESAKNOWLINFORMATION SYSTEMSARTIFJOURNAMERICAN CERAMICJOUMICROMECHANICS ANDJOURNCOMPOSITION ANDDECISIOSYSTEMS222222222222222222222222222220933-2790J CRYPTOL0966-9795INTERMETALLICS0098-1354COMPUT CHEM ENG0196-8904ENERG CONVERS MANAGE1551-3203IEEE T IND INFORM0017-9310INT J HEAT MASS TRAN0378-3812FLUID PHASE EQUILIBR1070-9932IEEE ROBOT AUTOM MAG0018-9294IEEE T BIO-MED ENG1083-4427IEEE T SYST MAN CY A0001-1541AICHE J0885-3282J BIOMATER APPL0169-7439CHEMOMETR INTELL LAB1552-6283INT J SEMANT WEB INF0360-1323BUILD ENVIRON0890-8044IEEE NETWORK0263-8223COMPOS STRUCT0002-7820J AM CERAM SOC0018-9197IEEE J QUANTUM ELECT1063-6692IEEE ACM T NETWORK0167-577X MATER LETT0899-7667NEURAL COMPUT0960-1317J MICROMECH MICROENG0889-1575J FOOD COMPOS ANAL0167-9236DECIS SUPPORT SYST0219-1377KNOWL INF SYST1064-5462ARTIF LIFE1077-2626IEEE T VIS COMPUT GR0011-9164DESALINATION270271272 273 274 275 276 277 278 279 280 281 282 283284 285 286287288 289290 291 292ACM TransaNetworksHYDROMENERGY AMATERIALSENGINEERING A-STRUCTURAL MATERIALSPROPERTIES MICROSTFOOD ADCONTAMINANTSJOURNAL OEDUCATIONIEEE PTECHNOLOGY LETTERSIEEE ENGMEDICINE AND BIOLOGYMAGAZINEINDUENGINEERING CHEMISTRYEUROPEJOURNAL EINTERNATIOF MACHINE TOOLS &MANUFACTUREJOUBIOMATERIALS SCIENCE-NEURALJOURNALTECHNOLOGY ANDBIOTECHNOLOGYBaltic JourBridge EngineeringINTERNATIOF ELECTRICAL POWER &ENERGY SYSTEMSIEEE TRANCIRCUITS AND SYSTEMSFOR VIDEO TECHNOLOGYJOURNAL OELECTROCHEMISTRYJOUMANAGEMENTJOUMICROELECTROMECHANICAL SYSTEMSIEEE TRANSYSTEMS MAN ANDCYBERNETICS PART C-APPLICATIONS AND REJournal of thInformation SystemsMATERIALBULLETIN222222222222222222222221041-1135IEEE PHOTONIC TECH L0739-5175IEEE ENG MED BIOL0304-386X HYDROMETALLURGY0378-7788ENERG BUILDINGS0890-6955INT J MACH TOOL MANU0920-5063J BIOMAT SCI-POLYM E0888-5885IND ENG CHEM RES0921-5093MAT SCI ENG A-STRUCT0893-6080NEURAL NETWORKS0268-2575J CHEM TECHNOL BIOT1550-4859ACM T SENSOR NETWORK1292-8941EUR PHYS J E0025-5408MATER RES BULL1944-0049FOOD ADDIT CONTAM A1822-427X BALT J ROAD BRIDGE E0142-0615INT J ELEC POWER1432-8488J SOLID STATE ELECTR1069-4730J ENG EDUC1057-7157J MICROELECTROMECH S1094-6977IEEE T SYST MAN CY C1536-9323J ASSOC INF SYST0742-1222J MANAGE INFORM SYST1051-8215IEEE T CIRC SYST VID293294295 296297 298 299300 301 302303 304 305 306 307 308 309 310 311312 313314 315 316317 318 319 320 321BIOPROBIOSYSTEMSSTRUCTUMONITORING-ANINTERNATIONAL JOURNALTRANSRESEARCH PART A-POLICYMECHANIAND SIGNAL PROCESSINGMACROMATERIALS ANDCEMENTCOMPOSITESCOASTALIET NanoDATA MKNOWLEDGE DISCOVERYJournal of DiBIODEGIEEE TRANANTENNAS ANDMECHANICSSMART MSTRUCTURESSTRUCTUINTERNATIOF APPROXIMATEPOWDERJOURNAL OAND ENGINEERINGIEEE TRANNANOTECHNOLOGYELECTROCSOLID STATE LETTERSAPPLIEENGINEERINGSURFACETECHNOLOGYIEEE TRANKNOWLEDGE AND DATAENGINEERINGINTERNATIOF ENERGY RESEARCHCOMPULINGUISTICSINTERNATIOF ADHESION ANDINTERNATIFOR NUMERICAL METHODSIN ENGINEERINGFunctionalIEEE TRANMICROWAVE THEORY ANDTECHNIQUES333333333332222222222222222220965-8564TRANSPORT RES A-POL1438-7492MACROMOL MATER ENG0888-3270MECH SYST SIGNAL PR0888-613X INT J APPROX REASON0032-5910POWDER TECHNOL1615-7591BIOPROC BIOSYST ENG1475-9217STRUCT HEALTH MONIT0378-3839COAST ENG1751-8741IET NANOBIOTECHNOL1099-0062ELECTROCHEM SOLID ST1359-4311APPL THERM ENG1226-086X J IND ENG CHEM1384-5810DATA MIN KNOWL DISC0257-8972SURF COAT TECH1041-4347IEEE T KNOWL DATA EN0958-9465CEMENT CONCRETE COMP1536-125X IEEE T NANOTECHNOL0891-2017COMPUT LINGUIST1551-319X J DISP TECHNOL0018-926X IEEE T ANTENN PROPAG0167-6636MECH MATER1793-6047FUNCT MATER LETT0923-9820BIODEGRADATION0964-1726SMART MATER STRUCT0167-4730STRUCT SAF0363-907X INT J ENERG RES0018-9480IEEE T MICROW THEORY0143-7496INT J ADHES ADHES0029-5981INT J NUMER METH ENG322323 324325 326327 328 329 330 331332 333 334335 336337 338 339 340 341 342 343 344 345 346 347 348349 350 351CHEMIDEPOSITIONSENSACTUATORS A-PHYSICALMATERIAIEEE-ACMComputational Biology andBioinformaticsFoodPLASMA CPLASMA PROCESSINGOPTICALARTIFICAPPLIESCIENCEPROGRESCOATINGSIEEE TraInformation Forensics andJOURNALAND ENGINEERING DATAIEEE TraBiomedical Circuits andACM TRANCOMPUTER SYSTEMSENERGSYNTHEACM TransaCOMACM TRANMATHEMATICALADSORPTIOTHE INTERNATIONALADSORPTION SOCIETYDIAMONDMATERIALSTRANSRESEARCH PART E-LOGISTICS ANDTRANSPORTATION REVIEWTHIN SCOMPUTEIMAGE UNDERSTANDINGIEEE TRANMULTIMEDIAJOURNALCONTROLINTERNATIOF THERMAL SCIENCESJournal of FJOURNPROTECTIONCOMPOPERATIONS RESEARCH3333333333333333333333333333330925-3467OPT MATER0948-1907CHEM VAPOR DEPOS0261-3069MATER DESIGN0734-2071ACM T COMPUT SYST0924-4247SENSOR ACTUAT A-PHYS1545-5963IEEE ACM T COMPUT BI1876-4517FOOD SECUR0272-4324PLASMA CHEM PLASMA P0195-6574ENERG J0018-9162COMPUTER0098-3500ACM T MATH SOFTWARE0021-9568J CHEM ENG DATA1932-4545IEEE T BIOMED CIRC S0169-4332APPL SURF SCI0300-9440PROG ORG COAT1366-5545TRANSPORT RES E-LOG0040-6090THIN SOLID FILMS0929-5607ADSORPTION1556-6013IEEE T INF FOREN SEC1077-3142COMPUT VIS IMAGE UND1520-9210IEEE T MULTIMEDIA0160-564X ARTIF ORGANS0925-9635DIAM RELAT MATER0305-0548COMPUT OPER RES0379-6779SYNTHETIC MET0959-1524J PROCESS CONTR1290-0729INT J THERM SCI1559-1131ACM T WEB1756-4646J FUNCT FOODS0362-028X J FOOD PROTECT352 353354 355 356 357 358359 360361362 363 364 365366 367368 369370 371 372373 374375376377378379380381SIAM JOCOMPUTINGMACHINMEDICAL EPHYSICSGPS SINTERNATIOF DAMAGE MECHANICSBioinspiratioJOURNAMERICAN OIL CHEMISTSCOMPOSENGINEERINGFoodWJOURNALMATERIALSEMPIRICAENGINEERINGAPPLIEAAPGAPPLIED BAND BIOTECHNOLOGYFOOD ANBULLETININTERNATIOF HEAT AND FLUID FLOWSEIET RenGenerationPOLYMADVANCEDKNOWLESYSTEMSIEEE MICWIRELESS COMPONENTSLETTERSInformPOLYMIEEE TRANBROADCASTINGCHEMICALAND PROCESSINGINTERNATIOF CIRCUIT THEORY ANDAPPLICATIONSTRANSRESEARCH PART C-EMERGING TECHNOLOGIESJOURNFRANKLIN INSTITUTE-ENGINEERING ANDAPPLIED MATHEMATICSJOURNALSCIENCE3333333333333333333333333333331056-7895INT J DAMAGE MECH1748-3182BIOINSPIR BIOMIM1350-4533MED ENG PHYS0003-021X J AM OIL CHEM SOC1080-5370GPS SOLUT0142-727X INT J HEAT FLUID FL0097-5397SIAM J COMPUT1359-8368COMPOS PART B-ENG1557-1858FOOD BIOPHYS1382-3256EMPIR SOFTW ENG0885-6125MACH LEARN0149-1423AAPG BULL0273-2289APPL BIOCHEM BIOTECH0379-5721FOOD NUTR BULL1559-128X APPL OPTICS1566-2535INFORM FUSION0142-9418POLYM TEST0043-1648WEAR0022-3115J NUCL MATER1752-1416IET RENEW POWER GEN1042-7147POLYM ADVAN TECHNOL0098-9886INT J CIRC THEOR APP0968-090X TRANSPORT RES C-EMER0018-9316IEEE T BROADCAST0950-7051KNOWL-BASED SYST0016-0032J FRANKLIN I0022-2461J MATER SCI1424-8220SENSORS-BASEL0255-2701CHEM ENG PROCESS1531-1309IEEE MICROW WIREL CO382 383384 385 386387 388389390 391392 393 394395 396397 398399 400 401 402 403 404 405 406407 408IEEE TRANCIRCUITS AND SYSTEMS I-FUNDAMENTAL THEORYAND APPLICATJOUMICROENCAPSULATIONDigesNanomaterials andMODESIMULATION IN MATERIALSSCIENCE ANDENGINEERINGJOURNALMANAGEMENTAd HoEUROPEALIPID SCIENCE ANDMacromolEngineeringCIRPMANUFACTURINGTECHNOLOGYJOURNALSPRAY TECHNOLOGYIEEE TRANDEVICE AND MATERIALSRELIABILITYACM TRANSOFTWARE ENGINEERINGAND METHODOLOGYJOURNSCIENCEAPPLIEDMATERIALS SCIENCE &COMPSTRUCTURESMEXPERIMEINTERNATIOF HUMAN-COMPUTERCurrentJOUMICROSCOPY-OXFORDIEEE TRANINFORMATIONTECHNOLOGY INBIOMEDICINEMETIEEE SIEEE TRANCONTROL SYSTEMSTECHNOLOGYANNUALCONTROLBIOTECHNOMACRORESEARCH3333333333333333333333333330265-2048J MICROENCAPSUL1530-4388IEEE T DEVICE MAT RE1049-331X ACM T SOFTW ENG METH0007-8506CIRP ANN-MANUF TECHN0022-1147J FOOD SCI0947-8396APPL PHYS A-MATER1549-8328IEEE T CIRCUITS-I1059-9630J THERM SPRAY TECHN1996-1944MATERIALS1842-3582DIG J NANOMATER BIOS1063-8016J DATABASE MANAGE1570-8705AD HOC NETW0740-7459IEEE SOFTWARE0965-0393MODEL SIMUL MATER SC1438-7697EUR J LIPID SCI TECH1862-832X MACROMOL REACT ENG0045-7949COMPUT STRUCT1063-6536IEEE T CONTR SYST T1367-5788ANNU REV CONTROL0141-5492BIOTECHNOL LETT1089-7771IEEE T INF TECHNOL B0026-1394METROLOGIA1071-5819INT J HUM-COMPUT ST1573-4137CURR NANOSCI0022-2720J MICROSC-OXFORD1598-5032MACROMOL RES0723-4864EXP FLUIDS409410 411412 413 414 415 416 417 418 419 420 421 422 423 424 425 426 427 428 429 430431432433 434 435 436TRIBOLOJOURNALINTELLIGENCE RESEARCHTRIINTERNATIONALMJournal of thof Chemical EngineersDATA & KENGINEERINGDRYING TCOMPUTFORUMMACROTHEORY AND SIMULATIONSCONTROLPRACTICENanoscaleThermophysical EngineeringMETALLUMATERIALSTRANSACTIONS A-PHYSICAL METALLURGYAND MATERIALAUTONOMAND MULTI-AGENTWINDINTERNATIOF REFRACTORY METALS& HARD MATERIALSIEEE TraComputational Intelligence andBIOLOGICAIEEE TransSpeech and LanguageJOURNAELECTROCHEMISTRYIEEE CGRAPHICS ANDJOURNAL OREASONINGCERAMICSLETTERMICROBIOLOGYIEEE TRANVEHICULAR TECHNOLOGYAPPLIED SIEEE TRANULTRASONICSFERROELECTRICS ANDFREQUENCY CONTROLINTERNATIOF ROBUST ANDNONLINEAR CONTROLINTERNATIOF FATIGUE33333333333333333333333333330737-3937DRY TECHNOL0167-7055COMPUT GRAPH FORUM1076-9757J ARTIF INTELL RES0301-679X TRIBOL INT1556-7265NANOSC MICROSC THERM1073-5623METALL MATER TRANS A1022-1344MACROMOL THEOR SIMUL0968-4328MICRON1387-2532AUTON AGENT MULTI-AG1095-4244WIND ENERGY1023-8883TRIBOL LETT0967-0661CONTROL ENG PRACT0018-9545IEEE T VEH TECHNOL1876-1070J TAIWAN INST CHEM E0263-4368INT J REFRACT MET H1943-068X IEEE T COMP INTEL AI0021-891X J APPL ELECTROCHEM0169-023X DATA KNOWL ENG0168-7433J AUTOM REASONING0272-8842CERAM INT0266-8254LETT APPL MICROBIOL0272-1716IEEE COMPUT GRAPH1049-8923INT J ROBUST NONLIN0142-1123INT J FATIGUE0340-1200BIOL CYBERN1558-7916IEEE T AUDIO SPEECH0003-7028APPL SPECTROSC0885-3010IEEE T ULTRASON FERR。
NASA Technical Memorandum 112871Lyceum: A Multi-Protocol Digital Library GatewayMing-Hokng MaaMassachusetts Institute of Technology, Cambridge, Massachusetts Sandra L. EslerUniversity of Alabama, Tuscaloosa, AlabamaMichael L. NelsonLangley Research Center, Hampton, VirginiaJuly 1997National Aeronautics andSpace AdministrationLangley Research CenterHampton, Virginia 23681-0001Lyceum: A Multi-Protocol Digital Library GatewayMing-Hokng Maammaa@Massachusetts Institute of Technology Cambridge, MA 02139Sandra L. Eslersesler@University of AlabamaTuscaloosa, AL 354877Michael L. Nelsonm.l.nelson@NASA Langley Research Center, MS 124Hampton, VA 23681AbstractLyceum is a prototype scalable query gateway that provides a logically central interface to multi-protocol and physically distributed, digital libraries of scientific and technical information. Lyceum processes queries to multiple syntactically distinct search engines used by various distributed information servers from a single logically central interface without modification of the remote search engines. A working prototype (/lyceum/) demonstrates the capabilities, potentials, and advantages of this type of meta-search engine by providing access to over 50 servers covering over 20 disciplines.IntroductionInternet document and information archival, indexing, and distribution is typically embodied in widely heterogeneous and distributed information servers, employing search engines with user interfaces and query syntax that vary significantly. The incompatibility and non-interoperability between search engines and the lack of a common and unified interface between users and distributed information servers present a significant challenge to the design of meta-search engines and the indexing and retrieval of comprehensive and apropos information on the Internet. Because of this growing problem we developed Lyceum(/lyceum/),a working scalable query gateway meta-search engine that provides a common and unified interface to widely heterogeneous and distributed information servers.DesignA number of digital libraries exist on the World Wide Web (WWW). However, many overlap with other information servers and are incomplete, both in terms of the content they provide and the subject areas they cover. This requires the user to have detailed knowledge of where the various digital libraries are and what resources can be found in them. In short, users must perform extensive integration of the information they receive from various sources (Figure 1). In addition, these information servers often utilize different search engines to index their information. Various search engines, e.g., Harvest [Bowman, et al., 1995], Wide Area Information Server (WAIS) [Kahle, et al., 1992], freeWAIS-sf [Pfeifer, et al., 1995]. often require different syntax for search functions such as Boolean searches, result limiting and ranking, case sensitivity, search method, and other miscellaneous return options. This variability has typically discouraged attempts to implement meta-search engines. We have previously examined various digital library architectures and have found the distributed architecture with the contributors being the authoring organization or individuals as the most desirable architecture (Esler & Nelson, 1997). There are two primary advantages to distributing information among multiple servers versus implementing one centralized information server:1. Each information server is now responsible only for maintaining information localto an organization.2. One canonical information server or database which covers the entire spectrum ofscientific research is patently neither feasible nor desirable.What is needed is a logically central interface to physically distributed and heterogeneous databases. As a gateway server, Lyceum allows users to query syntactically distinct search engines from a single interface by formatting a userÕs query submission to conform to the appropriate search engine query syntax and options (Figure 2).Because of the rapid pace with which new information servers are established, Lyceumwas designed for scalability. The ability to add both individual information servers and other meta-search engines similar to Lyceum enables Lyceum to access many already cataloged information servers by taking advantage of pre-existing services such as NCSTRL [Davis, et al., 1995],building on the work of others rather than recompiling databases of individual information servers.Within a distributed architecture, there are two methods to aggregating digital library resources:1. Encourage the proliferation and wide spread adoption of a single digital library protocol2. Provide a protocol conversion functionality to gateway between heterogeneous resourcesFigure 1: User Performs Multiple SearchesFigure 2: Lyceum Performs Multiple Searches for the UserThe first method is what is employed by NCSTRL and NCSTRL+ [Nelson, et al., 1997]. The second method is that adopted by Lyceum. Finally, Lyceum was designed to require no special input or coordination from the remote information servers. Inclusion of and gatewaying to the remote information servers is performed without any action from the remote servers. Indeed,direct queries from users or from Lyceum are indistinguishable to the remote servers.ImplementationLyceum runs on a UNIX platform as a package of Perl Common Gateway Interface (CGI) scripts separated into client, server database, and administration scripts. Because Lyceum typically gateways to numerous information servers per query, Lyceum sends queries to information servers in parallel. This significantly reduces the userÕs idle time by shifting the time dependence of query results away from slow bottleneck servers and stalled connections towards a process where query results are returned as soon as they are available. In addition, this also prevents bad Internet connections from deadlocking the entire query. The Lyceum client,therefore, is a multi-forking client designed to gateway query requests in parallel. As users submit queries to Lyceum, the client forks and submits an individually tailored query (dependent on the requirements of each search engine) to each information server. When all requests have been forked, the client waits for the results of each query, post-formatting and merging the returned query results, and displaying the results to the user as they return. This implementation is similar to the parallel search algorithm implemented in the NASA Technical Report Server (NTRS)[Nelson & Maa, 1996].Secondly, Lyceum was written with the goal of data type independence. Because Lyceum does not explicitly maintain records of the information type archived at various information servers, Lyceum may be used to index not only scientific information, but any arbitrary indexed information. To achieve data type independence, the server database, which maintains information on each of the information servers accessed by Lyceum, simply consists of a structured directory tree (Figure 3). Renaming the directory structure automatically changes the information type that users see. Each file in this directory structure is a record for an information server, containing relevant descriptors and most importantly, the unique uniform resource locator (URL) that is used to query the serverÕs search engine. This form URL stores the syntax rules by which to format a userÕs query string for compatibility with a particular search engine. Figure 4 shows an example of the data files used to describe individual servers in Lyceum. Although new values can be added, the following values are currently used:Type : WAIS, Glimpse, Split, Other Category : aerodynamics, aeronautics, astronautics, biology, chemistry, computer,earth, economics, energy, engineering, environmental, geography, geology,hierarchy, materials, mathematics, medicine, meteorology, multi-categories,nonlinear, physical, physics, psychology, social, zoology Sub-Category : Technical-Reports, Journals, Proceedings, Bibliographies,Newsletters, OtherObjectsaeronautics. . .. . .chemistry physicsindex.html chemistry.1chemistry.2. . .Figure 3: Objects Placed in the Subject CategoriesFinally, Lyceum was designed to be as maintenance free as possible. All system administration takes place through a WWW interface, providing a flexible layer that shields the administrator from the programming code (Figure 5). All query interfaces are generated on the fly according to the contents of the server database, erasing the need for periodic updating of the server database. Because query interfaces are generated on the fly (Figures 6 & 7), delays slightly increase as the server database populates. Currently, the delay is minimal, but if LyceumÕs population grew to the point where the dynamic construction of the interface became noticeable to the user, we could switch the interface construction to be static and periodically regenerated (e.g.,every 12 hours). The search results interface is a concatenation of what the various servers would return if they had been searched individually. Typical examples are too lengthy to be placed in a typical figure, so the reader is encouraged to experiment.Figure 5: The Lyceum Administrative Interface and FunctionsName: Electronic Conference on Trends in Organic Chemisty (ECTOC)Category: chemistry Sub-Category: Proceedings Description:Home: /ectoc/Date: Fri Aug 2 10:11:40 EDT 1996Form: /cgi-bin/pursuit-ectoc?$keywords Type: Other:+Boolean: YES POC:POCemail:POCphone:Comments:Figure 4: File Format for an ObjectFigure 6: Initial Lyceum Interface Figure 7: Lyceum Interface, 2 Subjects ChosenRelated WorkFew digital library projects attempt to build a multi-discipline digital library. The University of Illinois Urbana-ChampaignÕs portion of the Digital Library Initiative (DLI) [Shatz, et al., 1996] does, but it has explicit agreements with various journal publishers to provide their titles using a homogeneous protocol. Similarly, the NCSTRL+ project builds its multi-discipline project using a homogeneous protocol, but has the authoring organizations as participants instead of traditional publishers.Perhaps the most similar to Lyceum is StanfordÕs STARTS: Stanford Protocol Proposal for Internet Retrieval and Search project [Gravano, et al., 1997]. STARTS proposes to implement a minimally common query language and protocol based on a simple subset of the Z39.50-11995 type-101 [Z39.50, 1995] query language and the Government Information Locator Service (GILS) attribute set [Christian, 1996]. In order for a search engine to support meta-searching, it must be actively modified to support this basic query language and protocol. In contrast, Lyceum requires no modifications on the part of information servers or the search engines that are used. Rather, knowledge of the query syntax of a particular search engine enables Lyceum to format the query into an equivalent and valid query to each of the remote information servers. While this method may not provide a permanent or long-term solution to distributed document indexing and retrieval, it does provide an efficient and working interim solution.A historically similar project was the Unified Computer Science Technical Report Index (UCSTRI) [Van Heyningen, 1994]. UCSTRI would use a collection of heustrics to index various computer science department anonymous ftp servers, parsing their README and abstracts files. UCSTRI was similar to Lyceum in that both require no coordination or modification with the provider of the original server. UCSTRI is still functional, but has been superseded by NCSTRL. Discussion and Future WorkVariability in search syntax, search options, and output is inherent with different search engines. To provide a common gatewaying interface to multiple distributed information servers, Lyceum must by necessity either ignore or modify certain options that are available in certain search engines but missing in others. For example, while nearly all modern search engines provide Boolean searches, some older search engines do not. For this particular situation, in formatting the user query by the appropriate syntax rules, Lyceum filters out the Boolean syntax from query strings sent to search engines that do not support Boolean searches.Increased protocol and syntax conversion is an area for improvement with Lyceum. Other areas include obtaining user feedback about improved formatting of search and results interfaces, more automation in the areas of maintenance and resource discovery, and more sophisticated cataloging techniques. Currently, Lyceum gateways to 56 information servers spanning 22 scientific and engineering disciplines ranging from aeronautics to zoology. The information servers included range in diversity from government data servers to journal archives. While this has been sufficient to demonstrate Lyceum conceptually, in order for Lyceum to demonstrate true application, many more information servers must be included. We encourage others to test, evaluate, and contribute resources to Lyceum.ConclusionWe developed Lyceum, a working prototype of a scalable query gateway that provides a logically common and local interface to widely heterogeneous and physically distributed scientific and technical digital libraries. Lyceum allows users to query multiple, syntactically distinct search engines used by various distributed information servers from a single logically central interface without modification of the remote search engines. The current working prototype, incorporating more than 56 information servers and meta-servers across 22 scientific and technical disciplines, demonstrates the capabilities, potentials, and advantages of this type of meta-search engine. Suggestions and contributions to Lyceum are welcome. Contact the authors for more information.ReferencesBowman, C. Mic; Danzig, Peter B.; Hardy, Darren R.; Manber, Udi ; Schwartz, Michael F. & Wessels, Duane P. (1995). Harvest: A Scalable, Customizable Discovery and AccessSystem. University of Colorado Computer Science Technical Report CU-CS-732-94. Christian, Elliot (1996). GILS: What is it? Where is it going?, D-lib Magazine, December 1996, /dlib/december96/12christian.htmlDavis, James R.; Krafft, Dean B.; & Lagoze, Carl (1995). Diesnt: Building a Production Technical Report Server. Advances in Digital Libraries, Springer-Verlag, pp. 211-222. Esler, Sandra L. & Nelson, Michael L. (1997). The Evolution of Scientific and Technical Information Distribution, to appear in the Journal of the American Society forInformation Science.Gravano, L.; Chang, C.-C. K.; Garcia-Molina, H.; Paepcke, A. (1997). STARTS: Stanford Proposal for Internet Meta-Searching, Proceedings of the International Conferenceon Management of Data (SIGMOD), May 12-15, Tuscon, AZ.Kahle, Brewster; Morris, Harry; Davis, Franklin; Tine, Kevin; Hart, Clare & Palmer, Robin (1992). Wide Area Information Servers: An Executive Information Systemfor Unstructured Files. Electronic Networking: Research, Applications, and Policy,2(1), pp. 59-68.Nelson, Michael L. & Maa, Ming-Hokng (1996). Optimizing the NASA Technical Report Server, Internet Research: Electronic Networking Applications and Policy, 6(1), pp. 64-70. Nelson, Michael L.; Maly, Kurt; Shen, Stewart N. T. (1997). Buckets, Clusters, and Dienst.Old Dominion University Computer Science Technical Report 97-30 and NASATM-112877.Pfeifer, Ulrich; Fuhr, Norbert; & Huynh, Tung (1995). Searching Structured Documents with the Enhanced Retrieval Functionality of freeWAIS-sf and Sfgate. Computer Networksand ISDN Systems, 27, pp. 1027-1036.Schatz, B.; Mischo, W. H.; Cole, T. W.; Hardin, J. B.; Bishop, A. P. & Chen, H. (1996).Federating Diverse Collections of Scientific Literature. IEEE Computer, 29(5), pp. 28-36. Van Heyningen, Marc (1994). The Unified Computer Science Technical Report Index: Lessons in indexing diverse resources. Proceedings of the Second International World Wide Web Conference, Chicago, IL, October 19-21, 1994, pp. 535-543.Z39.50-1995 Maintenance Agency (1995). /z3950/agency/1995doce.htmlREPORT DOCUMENTATION PAGE Form ApprovedOMB No. 0704-0188Public reporting burden for this collection of information is estimated to average 1 hour per response, including the time for reviewing instructions, searching existing data sources, gathering and maintaining the data needed, and completing and reviewing the collection of information. Send comments regarding this burden estimate or any other aspect of this collection of information, including suggestions for reducing this burden, to Washington Headquarters Services, Directorate for Information Operations and Reports, 1215 Jefferson Davis Highway, Suite 1204, Arlington, VA 22202-4302, and to the Office of Management and Budget, Paperwork Reduction Project (0704-0188), Washington, DC 20503.1. AGENCY USE ONLY(Leave blank)2. REPORT DATEJuly 19973. REPORT TYPE AND DATES COVERED Technical Memorandum4. TITLE AND SUBTITLELyceum: A Multi-Protocol Digital Library Gateway5. FUNDING NUMBERS6. AUTHOR(S)Ming-Hokng Maa, Sandra L. Esler, Michael L. Nelson7. PERFORMING ORGANIZATION NAME(S) AND ADDRESS(ES)NASA Langley Research CenterHampton, VA 23681-21998. PERFORMING ORGANIZATIONREPORT NUMBER9. SPONSORING/MONITORING AGENCY NAME(S) AND ADDRESS(ES)National Aeronautics and Space AdministrationWashington, DC 20546-000110. SPONSORING/MONITORINGAGENCY REPORT NUMBER NASA TM-11287111. SUPPLEMENTARY NOTESMing-Hokng Maa, Massachusetts Institute of Technology, Cambridge MA; Sandra L. Esler, University of Alabama, Tuscaloosa, AL; Michael L. Nelson, NASA Langley Research Center, Hampton, VA12a. DISTRIBUTION/AVAILABILITY STATEMENTUnclassifiedÐUnlimitedSubject Category 82 Distribution: NonstandardAvailability: NASA CASI (301) 621-039012b. DISTRIBUTION CODE13. ABSTRACT (Maximum 200 words)Lyceum is a prototype scalable query gateway that provides a logically central interface to multi-protocol and physically distributed, digital libraries of scientific and technical information. Lyceum processes queries to multiple syntactically distinct search engines used by various distributed information servers from a single logically central interface without modification of the remote search engines. A working prototype(/lyceum/) demonstrates the capabilities, potentials, and advantages of this type of meta-search engine by providing access to over 50 servers covering over 20 disciplines.14. SUBJECT TERMSWWW, Digital Libraries, STI, Distributed Information Retrieval 15. NUMBER OF PAGES916. PRICE CODEA0217. SECURITY CLA SSIFICATIO NOF REPORTUnclassified 18. SECURITY CLA SSIFICATIO NOF THI S PAGEUnclassified19. SECURITY CLASSIFICATIONOF ABSTRACTUnclassified20. LIMITATIONOF ABSTRACTNSN 7540-01-280-5500 Standard Form 298 (Rev. 2-89)Prescribed by ANSI Std. Z-39-18298-102。
Rank ISSN Abbreviated Journal Title Full Title Category SubcategoryCountryUNITED STAT 10001-0782COMMUN ACM COMMUNICATIONS OF T工程技术计算机:理论20001-1452AIAA J AIAA JOURNAL工程技术工程:宇航UNITED STAT 30001-1541AICHE J AICHE JOURNAL工程技术工程:化工UNITED STAT 40001-2092AORN J AORN JOURNAL50001-2491ASHRAE J ASHRAE JOURNAL工程技术工程:机械UNITED STAT 60001-2815TISSUE ANTIGENS TISSUE ANTIGENS医学病理学DENMARK 70001-2998SEMIN NUCL MED SEMINARS IN NUCLEAR医学核医学UNITED STAT 80001-3765AN ACAD BRAS CIENC ANAIS DA ACADEMIA B综合性期刊综合性期刊BRAZIL90001-4338IZV ATMOS OCEAN PHY+IZVESTIYA ATMOSPHER地学海洋学RUSSIA 100001-4346MATH NOTES+MATHEMATICAL NOTES数学数学RUSSIA 110001-4370OCEANOLOGY+OCEANOLOGY地学海洋学RUSSIA 120001-4842ACCOUNTS CHEM RES ACCOUNTS OF CHEMICA化学化学综合UNITED STAT 130001-4966J ACOUST SOC AM JOURNAL OF THE ACOU物理声学UNITED STATCROATIA 140001-5113ACTA ADRIAT ACTA ADRIATICA生物海洋与淡水生150001-5172ACTA ANAESTH SCAND ACTA ANAESTHESIOLOG医学麻醉学DENMARKPOLAND 160001-5237ACTA ASTRONOM ACTA ASTRONOMICA地学天文天文与天体物POLAND 170001-527X ACTA BIOCHIM POL ACTA BIOCHIMICA POL生物生化与分子生180001-5296ACTA BIOL CRACOV BOT ACTA BIOLOGICA CRAC生物植物科学POLAND 190001-5342ACTA BIOTHEOR ACTA BIOTHEORETICA生物生物学NETHERLANDS 200001-5385ACTA CARDIOL ACTA CARDIOLOGICA医学心血管系统BELGIUM 210001-5415ACTA CHIR ORTHOP TR Acta Chirurgiae Ort ORTHOPEDICS CZECH REPUB 220001-5458ACTA CHIR BELG ACTA CHIRURGICA BEL医学外科BELGIUM 230001-5555ACTA DERM-VENEREOL ACTA DERMATO-VENERE医学皮肤病学NORWAY 240001-5644ACTA GASTRO-ENT BELG ACTA GASTRO-ENTEROL医学胃肠肝病学BELGIUM 250001-5652HUM HERED HUMAN HEREDITY生物遗传学SWITZERLAND 260001-5709ACTA GEOL POL ACTA GEOLOGICA POLO地学地质学POLANDPEOPLES R C 270001-5733CHINESE J GEOPHYS-CH CHINESE JOURNAL OF 地学地球化学与地280001-5792ACTA HAEMATOL-BASEL ACTA HAEMATOLOGICA医学血液学SWITZERLANDGERMANY 290001-5903ACTA INFORM ACTA INFORMATICA工程技术计算机:信息300001-5962ACTA MATH-DJURSHOLM ACTA MATHEMATICA数学数学SWEDEN 310001-5970ACTA MECH ACTA MECHANICA物理力学AUSTRIA 320001-6268ACTA NEUROCHIR ACTA NEUROCHIRURGIC医学临床神经学AUSTRIA 330001-6314ACTA NEUROL SCAND ACTA NEUROLOGICA SC医学临床神经学DENMARK 340001-6322ACTA NEUROPATHOL ACTA NEUROPATHOLOGI医学病理学GERMANY 350001-6349ACTA OBSTET GYN SCAN ACTA OBSTETRICIA ET医学妇产科学DENMARKNORWAY 360001-6357ACTA ODONTOL SCAND ACTA ODONTOLOGICA S医学牙科与口腔外370001-6454ACTA ORNITHOL ACTA ORNITHOLOGICA生物鸟类学POLAND 380001-6462ACTA ORTHOP BELG Acta Orthopaedica B医学整形外科BELGIUM 390001-6489ACTA OTO-LARYNGOL ACTA OTO-LARYNGOLOG医学耳鼻喉科学NORWAY 400001-6497B-ENT B-ENT医学耳鼻喉科学BELGIUM 410001-6837ACTA POL PHARM ACTA POLONIAE PHARM医学药学POLAND 420001-690X ACTA PSYCHIAT SCAND ACTA PSYCHIATRICA S医学精神病学ENGLAND 430001-6977ACTA SOC BOT POL ACTA SOCIETATIS BOT生物植物科学POLAND 440001-7051ACTA THERIOL ACTA THERIOLOGICA生物动物学POLAND 450001-706X ACTA TROP ACTA TROPICA医学寄生虫学NETHERLANDS 460001-7213ACTA VET BRNO ACTA VETERINARIA BR农林科学兽医学CZECH REPUB 470001-723X ACTA VIROL ACTA VIROLOGICA医学病毒学SLOVAKIA 480001-7272ACTA ZOOL-STOCKHOLM ACTA ZOOLOGICA生物动物学ENGLANDUNITED STAT 490001-7701GEN RELAT GRAVIT GENERAL RELATIVITY 物理天文与天体物GERMANY 500001-7868AKTUEL UROL AKTUELLE UROLOGIE医学泌尿学与肾脏510001-8244BEHAV GENET BEHAVIOR GENETICS生物行为科学UNITED STATENGLAND 520001-8678ADV APPL PROBAB ADVANCES IN APPLIED数学统计学与概率530001-8686ADV COLLOID INTERFAC ADVANCES IN COLLOID化学物理化学NETHERLANDS 540001-8708ADV MATH ADVANCES IN MATHEMA数学数学UNITED STATENGLAND 550001-8732ADV PHYS ADVANCES IN PHYSICS物理物理:凝聚态560001-9054AEQUATIONES MATH Aequationes Mathema MATHEMATICS MATHEMATICS SWITZERLAND 570001-9240AERONAUT J AERONAUTICAL JOURNA工程技术工程:宇航ENGLAND 580001-9704AFINIDAD AFINIDAD化学化学综合SPAIN 590002-0443J NURS ADMIN JOURNAL OF NURSING 医学护理UNITED STAT 600002-0729AGE AGEING AGE AND AGEING医学老年医学ENGLAND 610002-1121GER J AGR ECON German Journal of A AGRICULTURAL ECONOMI GERMANYUNITED STAT 620002-1482AGR HIST AGRICULTURAL HISTOR农林科学科学史与科学630002-1857AGROCHIMICA AGROCHIMICA农林科学土壤科学ITALY 640002-1962AGRON J AGRONOMY JOURNAL农林科学农艺学UNITED STAT 650002-5100ALDRICHIM ACTA ALDRICHIMICA ACTA化学有机化学UNITED STAT 660002-5232ALGEBR LOG+Algebra and Logic数学数学RUSSIA 670002-5240ALGEBR UNIV ALGEBRA UNIVERSALIS数学数学SWITZERLAND 680002-5852ALLG FORST JAGDZTG ALLGEMEINE FORST UN农林科学林学GERMANY 690002-6980AMBIX Ambix HISTORY & PHILOSOPHY ENGLAND 700002-7014AMEGHINIANA AMEGHINIANA地学古生物学ARGENTINA 710002-7685AM BIOL TEACH AMERICAN BIOLOGY TE BIOLOGY EDUCATION, UNITED STATUNITED STAT 720002-7812AM CERAM SOC BULL AMERICAN CERAMIC SO工程技术材料科学:硅UNITED STAT 730002-7820J AM CERAM SOC JOURNAL OF THE AMER工程技术材料科学:硅740002-7863J AM CHEM SOC JOURNAL OF THE AMER化学化学综合UNITED STATUNITED STAT 750002-8177J AM DENT ASSOC JOURNAL OF THE AMER医学牙科与口腔外760002-8320T AM ENTOMOL SOC TRANSACTIONS OF THE生物昆虫学UNITED STAT 770002-838X AM FAM PHYSICIAN AMERICAN FAMILY PHY医学医学:内科UNITED STAT 780002-8444AM FERN J AMERICAN FERN JOURN生物植物科学UNITED STAT 790002-8487T AM FISH SOC TRANSACTIONS OF THE农林科学渔业UNITED STAT 800002-8614J AM GERIATR SOC JOURNAL OF THE AMER医学老年医学UNITED STAT 810002-8703AM HEART J AMERICAN HEART JOUR医学心血管系统UNITED STAT 820002-8711J AM HELICOPTER SOC JOURNAL OF THE AMER工程技术工程:宇航UNITED STATUNITED STAT 830002-9092AM J AGR ECON AMERICAN JOURNAL OF管理科学农业经济与政840002-9122AM J BOT AMERICAN JOURNAL OF生物植物科学UNITED STAT 850002-9149AM J CARDIOL AMERICAN JOURNAL OF医学心血管系统UNITED STAT 860002-9165AM J CLIN NUTR AMERICAN JOURNAL OF医学营养学UNITED STAT 870002-9173AM J CLIN PATHOL AMERICAN JOURNAL OF医学病理学UNITED STATUNITED STAT 880002-9254AM J ENOL VITICULT AMERICAN JOURNAL OF农林科学生物工程与应UNITED STAT 890002-9262AM J EPIDEMIOL AMERICAN JOURNAL OF医学公共卫生、环900002-9270AM J GASTROENTEROL AMERICAN JOURNAL OF医学胃肠肝病学UNITED STAT 910002-9297AM J HUM GENET AMERICAN JOURNAL OF生物遗传学UNITED STAT 920002-9327AM J MATH AMERICAN JOURNAL OF数学数学UNITED STAT 930002-9343AM J MED AMERICAN JOURNAL OF医学医学:内科UNITED STAT 940002-936X AM J NURS AMERICAN JOURNAL OF医学护理UNITED STAT 950002-9378AM J OBSTET GYNECOL AMERICAN JOURNAL OF医学妇产科学UNITED STAT 960002-9394AM J OPHTHALMOL AMERICAN JOURNAL OF医学眼科学UNITED STAT 970002-9440AM J PATHOL AMERICAN JOURNAL OF医学病理学UNITED STAT 980002-9459AM J PHARM EDUC AMERICAN JOURNAL OF医学学科教育UNITED STAT 990002-9483AM J PHYS ANTHROPOL AMERICAN JOURNAL OF生物进化生物学UNITED STAT 1000002-9505AM J PHYS AMERICAN JOURNAL OF物理物理:综合UNITED STAT 1010002-953X AM J PSYCHIAT AMERICAN JOURNAL OF医学精神病学UNITED STATUNITED STAT 1020002-9599AM J SCI AMERICAN JOURNAL OF地学地球科学综合1030002-9610AM J SURG AMERICAN JOURNAL OF医学外科UNITED STAT 1040002-9629AM J MED SCI AMERICAN JOURNAL OF医学医学:内科UNITED STATUNITED STAT 1050002-9637AM J TROP MED HYG AMERICAN JOURNAL OF医学公共卫生、环1060002-9645AM J VET RES AMERICAN JOURNAL OF农林科学兽医学UNITED STAT1070002-9726J AM LEATHER CHEM AS JOURNAL OF THE AMER工程技术材料科学:纺UNITED STAT 1080002-9890AM MATH MON AMERICAN MATHEMATIC MATHEMATICS UNITED STAT 1090002-9939P AM MATH SOC PROCEEDINGS OF THE 数学数学UNITED STAT 1100002-9947T AM MATH SOC TRANSACTIONS OF THE数学数学UNITED STATUNITED STAT 1113月7日B AM METEOROL SOC BULLETIN OF THE AME地学气象与大气科1123月31日AM MIDL NAT AMERICAN MIDLAND NA环境科学生态学UNITED STAT 1130003-004X AM MINERAL AMERICAN MINERALOGI地学地球化学与地UNITED STAT 1140003-0082AM MUS NOVIT AMERICAN MUSEUM NOV环境科学动物学UNITED STAT 1150003-0090 B AM MUS NAT HIST BULLETIN OF THE AME环境科学生态学UNITED STAT 1160003-0147AM NAT AMERICAN NATURALIST环境科学进化生物学UNITED STAT 1170003-021X J AM OIL CHEM SOC JOURNAL OF THE AMER工程技术食品科技UNITED STAT 1180003-0996AM SCI AMERICAN SCIENTIST综合性期刊综合性期刊UNITED STAT 1190003-1062J AM SOC HORTIC SCI JOURNAL OF THE AMER农林科学园艺UNITED STAT 1200003-1305AM STAT AMERICAN STATISTICI数学统计学与概率UNITED STAT 1210003-1348AM SURGEON AMERICAN SURGEON医学外科UNITED STAT 1220003-1488JAVMA-J AM VET MED A JAVMA-JOURNAL OF TH农林科学兽医学UNITED STAT 1230003-2409ANAESTHESIA ANAESTHESIA医学麻醉学ENGLAND 1240003-2417ANAESTHESIST ANAESTHESIST医学麻醉学GERMANY 1250003-2654ANALYST ANALYST化学分析化学ENGLAND 1260003-2670ANAL CHIM ACTA ANALYTICA CHIMICA A化学分析化学NETHERLANDS 1270003-2697ANAL BIOCHEM ANALYTICAL BIOCHEMI生物分析化学UNITED STAT 1280003-2700ANAL CHEM ANALYTICAL CHEMISTR化学分析化学UNITED STAT 1290003-2719ANAL LETT ANALYTICAL LETTERS化学分析化学UNITED STAT 1300003-2778J ANAT SOC INDIA Journal of the Anat ANATOMY & MORPHOLOGY INDIA 1310003-2999ANESTH ANALG ANESTHESIA AND ANAL医学麻醉学UNITED STAT 1320003-3022ANESTHESIOLOGY ANESTHESIOLOGY医学麻醉学UNITED STAT 1330003-3197ANGIOLOGY ANGIOLOGY医学外周血管病UNITED STATUNITED STAT 1340003-3219ANGLE ORTHOD ANGLE ORTHODONTIST医学牙科与口腔外1350003-3472ANIM BEHAV ANIMAL BEHAVIOUR生物动物学ENGLANDENGLAND 1360003-3790ANN SCI ANNALS OF SCIENCE综合性期刊科学史与科学1370003-3804ANN PHYS-BERLIN ANNALEN DER PHYSIK物理物理:综合GERMANY 1380003-3847ANN BOT FENN ANNALES BOTANICI FE生物植物科学FINLANDFRANCE 1390003-3898ANN BIOL CLIN-PARIS ANNALES DE BIOLOGIE医学医学:研究与1400003-4088ANN LIMNOL-INT J LIM ANNALES DE LIMNOLOG地学湖沼学FRANCEFRANCE 1410003-4266ANN ENDOCRINOL-PARIS ANNALES D ENDOCRINO医学内分泌学与代1420003-4347ANN TELECOMMUN Annals of Telecommu工程技术电信学FRANCE 1430003-4487ANN MED-PSYCHOL ANNALES MEDICO-PSYC医学精神病学FRANCE 1440003-4541ANN ZOOL ANNALES ZOOLOGICI生物动物学POLAND 1450003-455X ANN ZOOL FENN ANNALES ZOOLOGICI F生物动物学FINLAND 1460003-4746ANN APPL BIOL ANNALS OF APPLIED B生物农业综合UNITED STAT 1470003-4800ANN HUM GENET ANNALS OF HUMAN GEN生物遗传学ENGLAND 1480003-4819ANN INTERN MED ANNALS OF INTERNAL 医学医学:内科UNITED STAT 1490003-486X ANN MATH ANNALS OF MATHEMATI数学数学UNITED STAT 1500003-4878ANN OCCUP HYG ANNALS OF OCCUPATIO医学毒理学ENGLAND 1510003-4894ANN OTO RHINOL LARYN ANNALS OF OTOLOGY R医学耳鼻喉科学UNITED STAT 1520003-4916ANN PHYS-NEW YORK ANNALS OF PHYSICS物理物理:综合UNITED STAT 1530003-4932ANN SURG ANNALS OF SURGERY医学外科UNITED STAT 1540003-4967ANN RHEUM DIS ANNALS OF THE RHEUM医学风湿病学ENGLAND 1550003-4975ANN THORAC SURG ANNALS OF THORACIC 医学呼吸系统UNITED STAT 1560003-5599ANTI-CORROS METHOD M ANTI-CORROSION METH工程技术冶金工程ENGLAND 1570003-6072ANTON LEEUW INT J G ANTONIE VAN LEEUWEN生物微生物学NETHERLANDS 1580003-6811APPL ANAL APPLICABLE ANALYSIS数学应用数学ENGLAND 1590003-682X APPL ACOUST APPLIED ACOUSTICS物理声学ENGLANDRUSSIA 1600003-6838APPL BIOCHEM MICRO+APPLIED BIOCHEMISTR生物生物工程与应1610003-6862APPL ENTOMOL ZOOL APPLIED ENTOMOLOGY 生物昆虫学JAPAN 1620003-6870APPL ERGON APPLIED ERGONOMICS工程技术工程:工业ENGLAND 1630003-6900APPL MECH REV Applied Mechanics R物理力学UNITED STAT 1640003-6951APPL PHYS LETT APPLIED PHYSICS LET物理物理:应用UNITED STAT 1650003-7028APPL SPECTROSC APPLIED SPECTROSCOP工程技术光谱学UNITED STAT 1660003-7214J WATER SUPPLY RES T JOURNAL OF WATER SU环境科学工程:土木ENGLANDENGLAND 1670003-813X ARCHAEOMETRY ARCHAEOMETRY地学地球科学综合1680003-889X ARCH MATH ARCHIV DER MATHEMAT数学数学SWITZERLAND 1690003-925X J FOOD SAF FOOD QUAL Journal of Food Safety and Food Quality-ArchivGERMANY 1700003-9438ARCH TIERZUCHT ARCHIV FUR TIERZUCH农林科学奶制品与动物1710003-9438ARCH ANIM BREED Archives Animal BreedingGERMANY 1720003-9519ARCH HIST EXACT SCI ARCHIVE FOR HISTORY管理科学科学史与科学1730003-9527ARCH RATION MECH AN ARCHIVE FOR RATIONA物理力学GERMANY 1740003-9829ARCH ITAL BIOL ARCHIVES ITALIENNES医学神经科学ITALY 1750003-9861ARCH BIOCHEM BIOPHYS ARCHIVES OF BIOCHEM生物生化与分子生UNITED STAT 1760003-9888ARCH DIS CHILD ARCHIVES OF DISEASE医学小儿科ENGLANDENGLAND 1770003-9969ARCH ORAL BIOL ARCHIVES OF ORAL BI医学牙科与口腔外1780003-9985ARCH PATHOL LAB MED ARCHIVES OF PATHOLO医学病理学UNITED STAT 1790003-9993ARCH PHYS MED REHAB ARCHIVES OF PHYSICA医学康复医学UNITED STAT 1800004-0614ARCH ESP UROL ARCHIVOS ESPANOLES UROLOGY & NEPHROLOGY SPAIN 1810004-0622ARCH LATINOAM NUTR ARCHIVOS LATINOAMER医学营养学VENEZUELA 1820004-069X ARCH IMMUNOL THER EX ARCHIVUM IMMUNOLOGI医学免疫学POLAND 1830004-0843ARCTIC ARCTIC地学环境科学CANADA 1840004-1254ARH HIG RADA TOKSIKO Arhiv za Higijenu R PUBLIC, ENV TOXICOLOGY C ROATIA 1850004-2080ARK MAT ARKIV FOR MATEMATIK数学数学SWEDEN 1860004-2730ARQ BRAS ENDOCRINOL Arquivos Brasileiro医学内分泌学与代BRAZIL 1870004-2749ARQ BRAS OFTALMOL ARQUIVOS BRASILEIRO OPHTHALMOLOGY BRAZIL 1880004-282X ARQ NEURO-PSIQUIAT ARQUIVOS DE NEURO-P医学精神病学BRAZILNETHERLANDS 1890004-3702ARTIF INTELL ARTIFICIAL INTELLIG工程技术计算机:人工UNITED STAT 1900004-5411J ACM JOURNAL OF THE ACM工程技术计算机:理论1910004-5632ANN CLIN BIOCHEM ANNALS OF CLINICAL BIOCHEMISTRYUNITED STAT 1920004-6256ASTRON J ASTRONOMICAL JOURNA地学天文天文与天体物1930004-6264PUBL ASTRON SOC JPN PUBLICATIONS OF THE地学天文天文与天体物JAPANUNITED STAT 1940004-6280PUBL ASTRON SOC PAC PUBLICATIONS OF THE地学天文天文与天体物GERMANY 1950004-6337ASTRON NACHR ASTRONOMISCHE NACHR地学天文天文与天体物UNITED STAT 1960004-637X ASTROPHYS J ASTROPHYSICAL JOURN地学天文天文与天体物NETHERLANDS 1970004-640X ASTROPHYS SPACE SCI ASTROPHYSICS AND SP地学天文天文与天体物1980004-8038AUK AUK生物鸟类学UNITED STAT 1990004-8380AUSTRALAS J DERMATOL AUSTRALASIAN JOURNA医学皮肤病学AUSTRALIA 2000004-8666AUST NZ J OBSTET GYN AUSTRALIAN & NEW ZE医学妇产科学AUSTRALIA 2010004-8674AUST NZ J PSYCHIAT AUSTRALIAN AND NEW 医学精神病学ENGLAND 2020004-9158AUST FORESTRY AUSTRALIAN FORESTRY FORESTRY AUSTRALIA 2030004-9425AUST J CHEM AUSTRALIAN JOURNAL 化学化学综合AUSTRALIA 2040004-959X AUST J ZOOL AUSTRALIAN JOURNAL 生物动物学AUSTRALIA 2050004-9727 B AUST MATH SOC BULLETIN OF THE AUS数学数学AUSTRALIA 2060005-0423AUST VET J AUSTRALIAN VETERINA农林科学兽医学ENGLANDUNITED STAT 2070005-1098AUTOMATICA AUTOMATICA工程技术工程:电子与2080005-1144AUTOMATIKA Automatika AUTOMATION ENGINEERING CROATIA 2090005-1179AUTOMAT REM CONTR+AUTOMATION AND REMO工程技术仪器仪表RUSSIA 2100005-2086AVIAN DIS AVIAN DISEASES农林科学兽医学UNITED STATNETHERLANDS 2110005-2728BBA-BIOENERGETICS BIOCHIMICA ET BIOPH生物生化与分子生2120005-2736BBA-BIOMEMBRANES BIOCHIMICA ET BIOPH生物生化与分子生NETHERLANDS 2130005-6650BAUINGENIEUR-GERMANY Bauingenieur工程技术工程:土木GERMANY 2140005-7959BEHAVIOUR BEHAVIOUR生物动物学NETHERLANDS2150005-9366BERL MUNCH TIERARZTL BERLINER UND MUNCHE农林科学兽医学GERMANYGERMANY 2160005-9900BETON- STAHLBETONBAU Beton- und Stahlbet工程技术材料科学:表UNITED STAT 2170006-291X BIOCHEM BIOPH RES CO BIOCHEMICAL AND BIO生物生化与分子生UNITED STAT 2180006-2928BIOCHEM GENET BIOCHEMICAL GENETIC生物生化与分子生2190006-2952BIOCHEM PHARMACOL BIOCHEMICAL PHARMAC医学药学UNITED STATUNITED STAT 2200006-2960BIOCHEMISTRY-US BIOCHEMISTRY生物生化与分子生2210006-2979BIOCHEMISTRY-MOSCOW+BIOCHEMISTRY-MOSCOW生物生化与分子生RUSSIA 2220006-3088BIOLOGIA BIOLOGIA生物生物学SLOVAKIA 2230006-3134BIOL PLANTARUM BIOLOGIA PLANTARUM生物植物科学NETHERLANDS 2240006-3185BIOL BULL-US BIOLOGICAL BULLETIN生物海洋与淡水生UNITED STAT 2250006-3207BIOL CONSERV BIOLOGICAL CONSERVA环境科学环境科学ENGLAND 2260006-3223BIOL PSYCHIAT BIOLOGICAL PSYCHIAT医学精神病学UNITED STAT 2270006-324X P BIOL SOC WASH PROCEEDINGS OF THE 生物生物学UNITED STAT 2280006-3363BIOL REPROD BIOLOGY OF REPRODUC生物生殖生物学UNITED STAT 2290006-341X BIOMETRICS BIOMETRICS生物生物学UNITED STAT 2300006-3444BIOMETRIKA BIOMETRIKA生物生物学ENGLAND 2310006-3495BIOPHYS J BIOPHYSICAL JOURNAL生物生物物理UNITED STATUNITED STAT 2320006-3525BIOPOLYMERS BIOPOLYMERS生物生化与分子生NETHERLANDS 2330006-355X BIORHEOLOGY BIORHEOLOGY医学工程:生物医2340006-3568BIOSCIENCE BIOSCIENCE生物生物学UNITED STATUNITED STAT 2350006-3592BIOTECHNOL BIOENG BIOTECHNOLOGY AND B工程技术生物工程与应2360006-3606BIOTROPICA BIOTROPICA环境科学生态学UNITED STAT 2370006-3657BIRD STUDY BIRD STUDY生物鸟类学ENGLANDNETHERLANDS 2380006-3835BIT BIT NUMERICAL MATHE数学计算机:软件2390006-4971BLOOD BLOOD医学血液学UNITED STAT 2400006-5196BLUMEA BLUMEA生物植物科学NETHERLANDS 2410006-579X BOIS FOR TROP BOIS ET FORETS DES FORESTRY FRANCEITALY 2420006-6729 B GEOFIS TEOR APPL Bollettino di Geofi地学地球化学与地GERMANY 2430006-8055BOT MAR BOTANICA MARINA生物海洋与淡水生2440006-8101BOT REV BOTANICAL REVIEW生物植物科学UNITED STAT 2450006-8241BOTHALIA BOTHALIA生物植物科学SOUTH AFRICNETHERLANDS 2460006-8314BOUND-LAY METEOROL BOUNDARY-LAYER METE地学气象与大气科2470006-8950BRAIN BRAIN医学临床神经学ENGLAND 2480006-8977BRAIN BEHAV EVOLUT BRAIN BEHAVIOR AND 医学行为科学SWITZERLAND 2490006-8993BRAIN RES BRAIN RESEARCH医学神经科学NETHERLANDS 2500006-9248BRATISL MED J Bratislava Medical 医学医学:内科SLOVAKIA 2510007-0610BRIT DENT J BRITISH DENTAL JOUR医学牙科与口腔外ENGLAND 2520007-070X BRIT FOOD J British Food Journa工程技术食品科技ENGLANDENGLAND 2530007-0882BRIT J PHILOS SCI BRITISH JOURNAL FOR管理科学科学史与科学2540007-0912BRIT J ANAESTH BRITISH JOURNAL OF 医学麻醉学ENGLAND 2550007-0920BRIT J CANCER BRITISH JOURNAL OF 医学肿瘤学ENGLAND 2560007-0963BRIT J DERMATOL BRITISH JOURNAL OF 医学皮肤病学ENGLAND 2570007-1048BRIT J HAEMATOL BRITISH JOURNAL OF 医学血液学ENGLANDENGLAND 2580007-1102BRIT J MATH STAT PSY BRITISH JOURNAL OF 医学数学跨学科应2590007-1145BRIT J NUTR BRITISH JOURNAL OF 医学营养学ENGLAND 2600007-1161BRIT J OPHTHALMOL BRITISH JOURNAL OF 医学眼科学ENGLAND 2610007-1188BRIT J PHARMACOL BRITISH JOURNAL OF 医学药学ENGLAND 2620007-1250BRIT J PSYCHIAT BRITISH JOURNAL OF 医学精神病学ENGLAND 2630007-1285BRIT J RADIOL BRITISH JOURNAL OF 医学核医学ENGLAND 2640007-1323BRIT J SURG BRITISH JOURNAL OF 医学外科ENGLAND 2650007-1420BRIT MED BULL BRITISH MEDICAL BUL医学医学:内科ENGLAND 2660007-1668BRIT POULTRY SCI BRITISH POULTRY SCI农林科学奶制品与动物ENGLAND 2670007-196X BRITTONIA BRITTONIA生物植物科学UNITED STAT 2680007-215X BRODOGRADNJA Brodogradnja ENGINEERING, MARINE C ROATIA2690007-2745BRYOLOGIST BRYOLOGIST生物植物科学UNITED STAT 2700007-4497 B SCI MATH BULLETIN DES SCIENC数学应用数学FRANCE 2710007-4551 B CANCER BULLETIN DU CANCER医学肿瘤学FRANCE 2720007-4853 B ENTOMOL RES BULLETIN OF ENTOMOL生物昆虫学ENGLAND 2730007-4861 B ENVIRON CONTAM TOX BULLETIN OF ENVIRON环境科学毒理学UNITED STATRUSSIA 2740007-4888 B EXP BIOL MED+BULLETIN OF EXPERIM医学医学:研究与2750007-4977 B MAR SCI BULLETIN OF MARINE 地学海洋学UNITED STAT 2760007-5027LAB MED LABORATORY MEDICINEUNITED STAT 2770007-5140 B HIST MED BULLETIN OF THE HIS医学科学史与科学2780007-5922MITT KLOSTERNEUBURG MITTEILUNGEN KLOSTE FOOD SCIENC HORTICULTUR Austria 2790007-8506CIRP ANN-MANUF TECHN CIRP ANNALS-MANUFAC工程技术工程:工业SWITZERLAND 2800007-9235CA-CANCER J CLIN CA-A CANCER JOURNAL医学肿瘤学UNITED STATFRANCE 2810007-9723CAH BIOL MAR CAHIERS DE BIOLOGIE生物海洋与淡水生2820008-0624CALCOLO CALCOLO数学数学ITALY 2830008-0845CALIF AGR CALIFORNIA AGRICULT农林科学农业综合UNITED STAT 2840008-1078CALIF FISH GAME CALIFORNIA FISH AND农林科学动物学UNITED STAT 2850008-347X CAN ENTOMOL CANADIAN ENTOMOLOGI生物昆虫学CANADA 2860008-350X CAN FAM PHYSICIAN CANADIAN FAMILY PHY医学医学:内科CANADACANADA 2870008-3674CAN GEOTECH J CANADIAN GEOTECHNIC地学地球科学综合CANADA 2880008-3976CAN J AGR ECON CANADIAN JOURNAL OF管理科学农业经济与政2890008-3984CAN J ANIM SCI CANADIAN JOURNAL OF农林科学奶制品与动物CANADA 2900008-4034CAN J CHEM ENG CANADIAN JOURNAL OF工程技术工程:化工CANADA 2910008-4042CAN J CHEM CANADIAN JOURNAL OF化学化学综合CANADA 2920008-4077CAN J EARTH SCI CANADIAN JOURNAL OF地学地球科学综合CANADA 2930008-414X CAN J MATH CANADIAN JOURNAL OF数学数学CANADA 2940008-4166CAN J MICROBIOL CANADIAN JOURNAL OF生物免疫学CANADA 2950008-4174CAN J OCCUP THER Canadian Journal of REHABILITATION CANADA 2960008-4182CAN J OPHTHALMOL CANADIAN JOURNAL OF医学眼科学CANADA 2970008-4204CAN J PHYS CANADIAN JOURNAL OF物理物理:综合CANADA 2980008-4212CAN J PHYSIOL PHARM CANADIAN JOURNAL OF医学生理学CANADA 2990008-4220CAN J PLANT SCI CANADIAN JOURNAL OF生物农艺学CANADA 3000008-4271CAN J SOIL SCI CANADIAN JOURNAL OF农林科学土壤科学CANADA 3010008-428X CAN J SURG CANADIAN JOURNAL OF医学外科CANADA 3020008-4301CAN J ZOOL CANADIAN JOURNAL OF生物动物学CANADA 3030008-4395CAN MATH BULL CANADIAN MATHEMATIC数学数学CANADA 3040008-4433CAN METALL QUART CANADIAN METALLURGI工程技术冶金工程CANADA 3050008-4476CAN MINERAL CANADIAN MINERALOGI地学矿物学CANADA 3060008-5286CAN VET J CANADIAN VETERINARY农林科学兽医学CANADA 3070008-543X CANCER-AM CANCER SOC CANCER医学肿瘤学UNITED STAT 3080008-5472CANCER RES CANCER RESEARCH医学肿瘤学UNITED STATNETHERLANDS 3090008-6215CARBOHYD RES CARBOHYDRATE RESEAR化学生化与分子生UNITED STAT 3100008-6223CARBON CARBON工程技术材料科学:综3110008-6312CARDIOLOGY CARDIOLOGY医学心血管系统SWITZERLAND 3120008-6363CARDIOVASC RES CARDIOVASCULAR RESE医学心血管系统ENGLANDUNITED STAT 3130008-6452CARIBB J SCI CARIBBEAN JOURNAL O综合性期刊生物多样性保SWITZERLAND 3140008-6568CARIES RES CARIES RESEARCH医学牙科与口腔外3150008-7114CARYOLOGIA CARYOLOGIA生物遗传学ITALY 3160008-7475CASTANEA CASTANEA生物植物科学UNITED STAT 3170008-8749CELL IMMUNOL CELLULAR IMMUNOLOGY生物免疫学UNITED STATENGLAND 3180008-8846CEMENT CONCRETE RES CEMENT AND CONCRETE工程技术材料科学:综3190008-8994CENTAURUS CENTAURUS HISTORY & PHILOSOPHY ENGLAND 3200009-0352CEREAL CHEM CEREAL CHEMISTRY工程技术食品科技UNITED STAT 3210009-2347CHEM ENG NEWS CHEMICAL & ENGINEER工程技术工程:化工UNITED STAT 3220009-2363CHEM PHARM BULL CHEMICAL & PHARMACE医学化学综合JAPAN3230009-2460CHEM ENG-NEW YORK CHEMICAL ENGINEERIN工程技术工程:化工UNITED STAT 3240009-2509CHEM ENG SCI CHEMICAL ENGINEERIN工程技术工程:化工UNITED STATNETHERLANDS 3250009-2541CHEM GEOL CHEMICAL GEOLOGY地学地球化学与地NETHERLANDS 3260009-2614CHEM PHYS LETT CHEMICAL PHYSICS LE化学物理:原子、3270009-2665CHEM REV CHEMICAL REVIEWS化学化学综合UNITED STAT 3280009-2673 B CHEM SOC JPN BULLETIN OF THE CHE化学化学综合JAPAN 3290009-2770CHEM LISTY CHEMICKE LISTY化学化学综合CZECH REPUB 3300009-2797CHEM-BIOL INTERACT CHEMICO-BIOLOGICAL 生物毒理学NETHERLANDSGERMANY 3310009-2819CHEM ERDE-GEOCHEM CHEMIE DER ERDE-GEO地学地球化学与地3320009-2851CHEM UNSERER ZEIT CHEMIE IN UNSERER Z化学化学综合GERMANY 3330009-286X CHEM-ING-TECH CHEMIE INGENIEUR TE工程技术工程:化工GERMANY 3340009-3068CHEM IND-LONDON CHEMISTRY & INDUSTR化学应用化学ENGLANDNETHERLANDS 3350009-3084CHEM PHYS LIPIDS CHEMISTRY AND PHYSI生物生化与分子生3360009-3092CHEM TECH FUELS OIL+CHEMISTRY AND TECHN工程技术工程:化工RUSSIA 3370009-3122CHEM HETEROCYCL COM+Chemistry of Hetero化学有机化学LATVIA 3380009-3130CHEM NAT COMPD+CHEMISTRY OF NATURA化学有机化学UZBEKISTAN 3390009-3157CHEMOTHERAPY CHEMOTHERAPY医学药学SWITZERLAND 3400009-4293CHIMIA CHIMIA化学化学综合SWITZERLAND 3410009-4536J CHIN CHEM SOC-TAIP JOURNAL OF THE CHIN化学化学综合TAIWAN 3420009-4722CHIRURG CHIRURG医学外科GERMANY 3430009-5893CHROMATOGRAPHIA CHROMATOGRAPHIA化学分析化学GERMANY 3440009-5915CHROMOSOMA CHROMOSOMA生物生化与分子生GERMANY 3450009-7322CIRCULATION CIRCULATION医学外周血管病UNITED STAT 3460009-7330CIRC RES CIRCULATION RESEARC医学外周血管病UNITED STAT 3470009-739X CIR ESPAN CIRUGIA ESPANOLA SURGERY SPAIN 3480009-7411CIR CIR Cirugia y Cirujanos医学外科MEXICO 3490009-8558CLAY MINER CLAY MINERALS地学矿物学ENGLANDUNITED STAT 3500009-8604CLAY CLAY MINER CLAYS AND CLAY MINE地学地球科学综合NETHERLANDS 3510009-8981CLIN CHIM ACTA CLINICA CHIMICA ACT医学医学实验技术3520009-9104CLIN EXP IMMUNOL CLINICAL AND EXPERI医学免疫学ENGLAND 3530009-9120CLIN BIOCHEM CLINICAL BIOCHEMIST医学医学实验技术CANADAUNITED STAT 3540009-9147CLIN CHEM CLINICAL CHEMISTRY医学医学实验技术3550009-9163CLIN GENET CLINICAL GENETICS医学遗传学DENMARK 3560009-9201CLIN OBSTET GYNECOL CLINICAL OBSTETRICS医学妇产科学UNITED STAT 3570009-921X CLIN ORTHOP RELAT R CLINICAL ORTHOPAEDI医学外科UNITED STAT 3580009-9228CLIN PEDIATR CLINICAL PEDIATRICS医学小儿科UNITED STAT 3590009-9236CLIN PHARMACOL THER CLINICAL PHARMACOLO医学药学UNITED STAT 3600009-9260CLIN RADIOL CLINICAL RADIOLOGY医学核医学ENGLAND 3610010-0285COGNITIVE PSYCHOL COGNITIVE PSYCHOLOG医学心理学UNITED STAT 3620010-065X COLEOPTS BULL COLEOPTERISTS BULLE生物昆虫学UNITED STAT 3630010-0757COLLECT MATH Collectanea Mathema数学数学SPAIN 3640010-1354COLLOQ MATH-WARSAW COLLOQUIUM MATHEMAT MATHEMATICS POLAND 3650010-2180COMBUST FLAME COMBUSTION AND FLAM工程技术工程:化工UNITED STAT 3660010-2202COMBUST SCI TECHNOL COMBUSTION SCIENCE 工程技术工程:化工UNITED STAT 3670010-2571COMMENT MATH HELV COMMENTARII MATHEMA数学数学SWITZERLANDGERMANY 3680010-3616COMMUN MATH PHYS COMMUNICATIONS IN M物理物理:数学物3690010-3624COMMUN SOIL SCI PLAN COMMUNICATIONS IN S农林科学分析化学UNITED STAT 3700010-3640COMMUN PUR APPL MATH COMMUNICATIONS ON P数学数学UNITED STAT 3710010-437X COMPOS MATH COMPOSITIO MATHEMAT数学数学NETHERLANDS 3720010-440X COMPR PSYCHIAT COMPREHENSIVE PSYCH医学精神病学UNITED STATENGLAND 3730010-4485COMPUT AIDED DESIGN COMPUTER-AIDED DESI工程技术计算机:软件ENGLAND 3740010-4620COMPUT J COMPUTER JOURNAL工程技术计算机:软件NETHERLANDS 3750010-4655COMPUT PHYS COMMUN COMPUTER PHYSICS CO物理计算机:跨学UNITED STAT 3760010-4825COMPUT BIOL MED COMPUTERS IN BIOLOG工程技术工程:生物医AUSTRIA 3770010-485X COMPUTING COMPUTING工程技术计算机:理论RUSSIA 3780010-5082COMBUST EXPLO SHOCK+COMBUSTION EXPLOSIO工程技术材料科学:综3790010-5422CONDOR CONDOR生物鸟类学UNITED STAT 3800010-7514CONTEMP PHYS CONTEMPORARY PHYSIC物理物理:综合ENGLAND 3810010-7824CONTRACEPTION CONTRACEPTION医学妇产科学UNITED STATGERMANY 3820010-7999CONTRIB MINERAL PETR CONTRIBUTIONS TO MI地学地球化学与地NETHERLANDS 3830010-8545COORDIN CHEM REV COORDINATION CHEMIS化学无机化学与核3840010-9312CORROSION-US CORROSION MATERIALS S METALLURGY UNITED STAT 3850010-938X CORROS SCI CORROSION SCIENCE工程技术材料科学:综ENGLAND 3860010-9452CORTEX CORTEX医学行为科学ITALY 3870010-9525COSMIC RES+COSMIC RESEARCH地学天文工程:宇航RUSSIA 3880011-1643CROAT CHEM ACTA CROATICA CHEMICA AC化学化学综合CROATIA 3890011-183X CROP SCI CROP SCIENCE农林科学农艺学UNITED STATNETHERLANDS 3900011-216X CRUSTACEANA CRUSTACEANA生物海洋与淡水生3910011-2240CRYOBIOLOGY CRYOBIOLOGY生物生理学UNITED STAT 3920011-2275CRYOGENICS CRYOGENICS物理热力学ENGLAND 3930011-3840CURR PROB SURG CURRENT PROBLEMS IN医学外科UNITED STAT 3940011-3891CURR SCI INDIA CURRENT SCIENCE综合性期刊综合性期刊INDIA 3950011-4162CUTIS CUTIS医学皮肤病学UNITED STAT 3960011-4545CYTOLOGIA CYTOLOGIA CELL BIOLOG GENETICS & Japan 3970011-4642CZECH MATH J CZECHOSLOVAK MATHEM数学数学CZECH REPUB 3980011-5029DM-DIS MON DM DISEASE-A-MONTH医学医学:内科UNITED STAT 3990011-748X DEFENCE SCI J DEFENCE SCIENCE JOU综合性期刊综合性期刊INDIA 4000011-9059INT J DERMATOL INTERNATIONAL JOURN医学皮肤病学UNITED STAT 4010011-9164DESALINATION DESALINATION工程技术工程:化工NETHERLANDS 4020012-0413DEUT LEBENSM-RUNDSCH DEUTSCHE LEBENSMITT工程技术食品科技GERMANY 4030012-0472DEUT MED WOCHENSCHR DEUTSCHE MEDIZINISC医学医学:内科GERMANY 4040012-1592DEV GROWTH DIFFER DEVELOPMENT GROWTH 生物发育生物学JAPAN 4050012-1606DEV BIOL DEVELOPMENTAL BIOLO生物发育生物学UNITED STAT 4060012-1622DEV MED CHILD NEUROL DEVELOPMENTAL MEDIC医学临床神经学ENGLAND 4070012-1630DEV PSYCHOBIOL DEVELOPMENTAL PSYCH生物发育生物学UNITED STATUNITED STAT 4080012-1797DIABETES DIABETES医学内分泌学与代GERMANY 4090012-186X DIABETOLOGIA DIABETOLOGIA医学内分泌学与代4100012-2661DIFF EQUAT+DIFFERENTIAL EQUATI数学数学RUSSIA 4110012-2823DIGESTION DIGESTION医学胃肠肝病学SWITZERLAND 4120012-365X DISCRETE MATH DISCRETE MATHEMATIC数学数学NETHERLANDS 4130012-3692CHEST CHEST医学呼吸系统UNITED STAT 4140012-3706DIS COLON RECTUM DISEASES OF THE COL医学外科UNITED STAT 4150012-3862DISS MATH Dissertationes Math数学数学POLAND 4160012-4486DOC OPHTHALMOL DOCUMENTA OPHTHALMO医学眼科学NETHERLANDS 4170012-5008DOKL CHEM DOKLADY CHEMISTRY化学化学综合UNITED STAT 4180012-5016DOKL PHYS CHEM DOKLADY PHYSICAL CH化学物理化学RUSSIA 4190012-6667DRUGS DRUGS医学毒理学NEW ZEALAND 4200012-6772DRVNA IND Drvna Industrija MATERIALS SCIENCE, P CROATIA 4210012-7094DUKE MATH J DUKE MATHEMATICAL J数学数学UNITED STAT 4220012-7361DYNA-BILBAO Dyna工程技术工程:综合SPAINNETHERLANDS 4230012-821X EARTH PLANET SC LETT EARTH AND PLANETARY地学地球化学与地NETHERLANDS 4240012-8252EARTH-SCI REV EARTH-SCIENCE REVIE地学地球科学综合4250012-9593ANN SCI ECOLE NORM S ANNALES SCIENTIFIQU数学数学FRANCE 4260012-9615ECOL MONOGR ECOLOGICAL MONOGRAP环境科学生态学UNITED STAT 4270012-9658ECOLOGY ECOLOGY环境科学生态学UNITED STATENGLAND 4280012-9682ECONOMETRICA ECONOMETRICA社会科学数学跨学科应4290013-0001ECON BOT ECONOMIC BOTANY生物植物科学UNITED STAT 4300013-0915P EDINBURGH MATH SOC PROCEEDINGS OF THE 数学数学ENGLAND4310013-1644EDUC PSYCHOL MEAS EDUCATIONAL AND PSY医学数学跨学科应UNITED STATUNITED STAT 4320013-4651J ELECTROCHEM SOC JOURNAL OF THE ELEC工程技术材料科学:膜4330013-4686ELECTROCHIM ACTA ELECTROCHIMICA ACTA工程技术电化学ENGLANDENGLAND 4340013-5194ELECTRON LETT ELECTRONICS LETTERS工程技术工程:电子与4350013-5585BIOMED ENG-BIOMED TE Biomedical Engineer ENGINEERING MEDICAL INF GERMANY 4360013-7006ENCEPHALE ENCEPHALE-REVUE DE 医学精神病学FRANCEUNITED STAT 4370013-7227ENDOCRINOLOGY ENDOCRINOLOGY医学内分泌学与代4380013-726X ENDOSCOPY ENDOSCOPY医学外科GERMANY 4390013-791X ENG ECON ENGINEERING ECONOMI ENGINEERING OPERATIONS UNITED STAT 4400013-7944ENG FRACT MECH ENGINEERING FRACTUR物理力学ENGLANDNETHERLANDS 4410013-7952ENG GEOL ENGINEERING GEOLOGY地学地球科学综合4420013-8029ENG J AISC ENGINEERING JOURNAL工程技术工程:土木UNITED STAT 4430013-8703ENTOMOL EXP APPL ENTOMOLOGIA EXPERIM生物昆虫学ENGLAND 4440013-872X ENTOMOL NEWS ENTOMOLOGICAL NEWS生物昆虫学UNITED STAT 4450013-8746ANN ENTOMOL SOC AM ANNALS OF THE ENTOM生物昆虫学UNITED STAT 4460013-8797P ENTOMOL SOC WASH PROCEEDINGS OF THE 生物昆虫学UNITED STAT 4470013-9157ENVIRONMENT ENVIRONMENT环境科学环境科学UNITED STATUNITED STAT 4480013-9351ENVIRON RES ENVIRONMENTAL RESEA环境科学公共卫生、环4490013-936X ENVIRON SCI TECHNOL ENVIRONMENTAL SCIEN环境科学工程:环境UNITED STAT 4500013-9580EPILEPSIA EPILEPSIA医学临床神经学UNITED STAT 4510013-9998ERDE ERDE GEOGRAPHY, GEOSCIENCES GERMANY 4520014-0015ERDKUNDE Erdkunde地学自然地理GERMANY 4530014-0139ERGONOMICS ERGONOMICS工程技术工程:工业ENGLAND 4540014-0309ERWERBS-OBSTBAU Erwerbs-Obstbau农林科学园艺GERMANY 4550014-2336EUPHYTICA EUPHYTICA农林科学农艺学NETHERLANDS 4560014-2565REV CLIN ESP REVISTA CLINICA ESP医学医学:内科SPAIN 4570014-2972EUR J CLIN INVEST EUROPEAN JOURNAL OF医学医学:内科GERMANY 4580014-2980EUR J IMMUNOL EUROPEAN JOURNAL OF医学免疫学UNITED STAT 4590014-2999EUR J PHARMACOL EUROPEAN JOURNAL OF医学药学NETHERLANDS 4600014-3022EUR NEUROL EUROPEAN NEUROLOGY医学临床神经学SWITZERLAND 4610014-3057EUR POLYM J EUROPEAN POLYMER JO化学高分子科学ENGLAND 4620014-3065POTATO RES POTATO RESEARCH AGRONOMY NETHERLANDS 4630014-312X EUR SURG RES EUROPEAN SURGICAL R医学外科SWITZERLAND 4640014-3820EVOLUTION EVOLUTION环境科学进化生物学UNITED STAT 4650014-4797EXP AGR EXPERIMENTAL AGRICU农林科学农艺学ENGLAND 4660014-4800EXP MOL PATHOL EXPERIMENTAL AND MO医学病理学UNITED STAT 4670014-4819EXP BRAIN RES EXPERIMENTAL BRAIN NEUROSCIENCES GERMANY 4680014-4827EXP CELL RES EXPERIMENTAL CELL R医学细胞生物学UNITED STAT 4690014-4835EXP EYE RES EXPERIMENTAL EYE RE医学眼科学UNITED STAT 4700014-4851EXP MECH EXPERIMENTAL MECHAN物理材料科学:表ENGLAND 4710014-4886EXP NEUROL EXPERIMENTAL NEUROL医学神经科学UNITED STAT 4720014-4894EXP PARASITOL EXPERIMENTAL PARASI医学寄生虫学UNITED STATNETHERLANDS 4730014-5793FEBS LETT FEBS LETTERS生物生化与分子生4740014-8237FARMACIA FARMACIA医学药学ROMANIA 4750015-0193FERROELECTRICS FERROELECTRICS工程技术材料科学:综ENGLAND 4760015-0282FERTIL STERIL FERTILITY AND STERI医学妇产科学UNITED STATRUSSIA 4770015-0541FIBRE CHEM+FIBRE CHEMISTRY工程技术材料科学:纺4780015-1882FILTR SEPARAT FILTRATION & SEPARA工程技术工程:化工ENGLANDUNITED STAT 4790015-2684FIRE TECHNOL FIRE TECHNOLOGY工程技术材料科学:综4800015-363X FLEISCHWIRTSCHAFT FLEISCHWIRTSCHAFT工程技术食品科技GERMANY 4810015-4040FLA ENTOMOL FLORIDA ENTOMOLOGIS生物昆虫学UNITED STAT 4820015-4628FLUID DYNAM+Fluid Dynamics MECHANICSPHYSICS, FL UNITED STAT 4830015-4725FLUORIDE FLUORIDE PUBLIC, ENV TOXICOLOGY N EW ZEALAND 4840015-5497FOLIA BIOL-KRAKOW FOLIA BIOLOGICA-KRA医学生物学POLAND。
Interest Management Middleware for Networked Games Graham Morgan, Fengyun Lu, Kier Storey School of Computing Science, University of Newcastle, UK
Abstract In this paper we present an implementation of an interest management scheme using standard message oriented middleware (MOM) technologies to provide scalable message dissemination for networked games. The aim of all interest management schemes is to identify when objects that inhabit a virtual world should be interacting and to enable such interaction via message passing while preventing objects that should not be interacting from exchanging messages. The time taken by existing interest management schemes to resolve which objects influence each other may be too large to enable the desired interaction to occur. Furthermore, existing interest management implementations tend to be proprietary and are built directly on top of networking protocols. In this paper we present an approach to interest management based on the predicted movement of objects. Our approach determines the frequency of message exchange between objects on the likelihood that such objects will influence each other in the near future. We then demonstrate, via implementation and experimentation, how existing middleware standards provide a suitable platform for the deployment of our interest management scheme.
Keywords: middleware, games, networking CCS: D.2.12 Interoperability - Distributed objects, I.3.2 Graphics Systems - Distributed/network graphics, C.2.4 Distributed Systems - Distributed applications
1 Introduction Networked games allow a geographically dispersed set of players to participate in a shared gaming environment. A gaming environment may provide a virtual world that presents some geographic model populated with moving objects with game play achieved by players influencing the state of the virtual world. Typically, a player’s console holds a sub-set of game state with players informing each other of their actions via the exchange of state update messages between consoles (either directly or indirectly via some intermediary server). The ability to allow players to maintain a mutually consistent view of the virtual world and still allow players to influence the virtual world in a timely manner are requirements that need to be satisfied to ensure players receive an appropriate gaming experience [Singhal and Zydra 1999]. A game may be played out in real-time, requiring
player directed changes of the virtual world to be propagated to other players in real-time. In early versions of such games [Sweany 1999], the number of players that could participate in a virtual world was limited to relatively low numbers (e.g., less than 16) with the geographic placement of players restricted to the same LAN to guarantee the most satisfying gaming experience. Recently, higher bandwidth, lower latency networks to the home have allowed one or two hundred geographically distributed players to participate in games of this genre (e.g., [Sony 2004]). However, this is still viewed as limiting as the desire of players to participate in large, complex, virtual spaces with thousands of other players have provided a substantial demand for large scale networked games.
The scalability issues presented by a networked game relate, primarily, to the number of players and the complexity of the game (e.g., number of objects populating the virtual world). An increase in the number of players may lead to an increase in network traffic as a player’s console attempts to propagate local game state updates to other players. If an attempt is not made to identify appropriate message recipients and so inhibit the sending and processing of unnecessary messages, then providing participation for many hundreds or thousands of players will not be possible. The process of identifying appropriate message recipients, referred to as interest management, introduces further computation and must be successfully completed in a timely manner to ensure the real-time and consistency requirements of a networked game are satisfied.
At present, networked games are built on standard protocols provided by existing network infrastructures (e.g., TCP/IP for the Internet) to ensure they are widely available for public use and so commercially viable. This approach results in enabling technologies that are proprietary and tend not to be suited to heterogeneous environments (i.e., deployment across varying platforms). Furthermore, programming distributed applications in this manner is a time consuming, non-trivial exercise. Therefore, middleware standards have been proposed (e.g., [OMG 2003]) that provide standard interfaces to services (e.g., location and discovery, security, inter-process communication) that ease the development of distributed applications. However, even the most recent networked games tend to be built directly above network layer protocols and do not benefit from the interoperability provided by existing middleware technologies.