算法导论参考 答案
- 格式:doc
- 大小:691.50 KB
- 文档页数:28
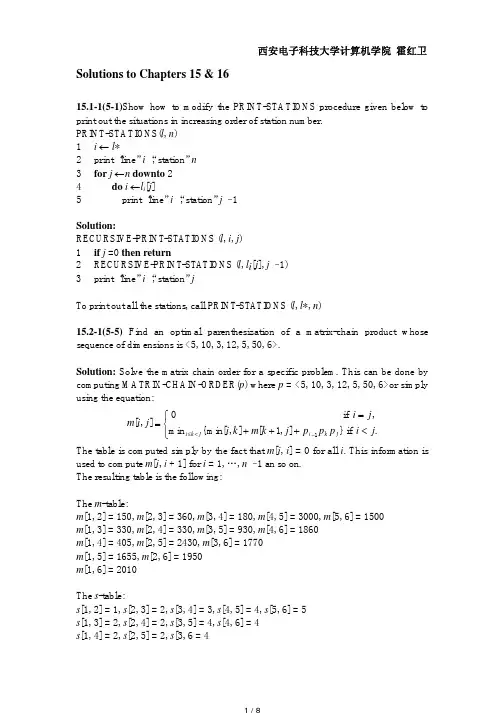
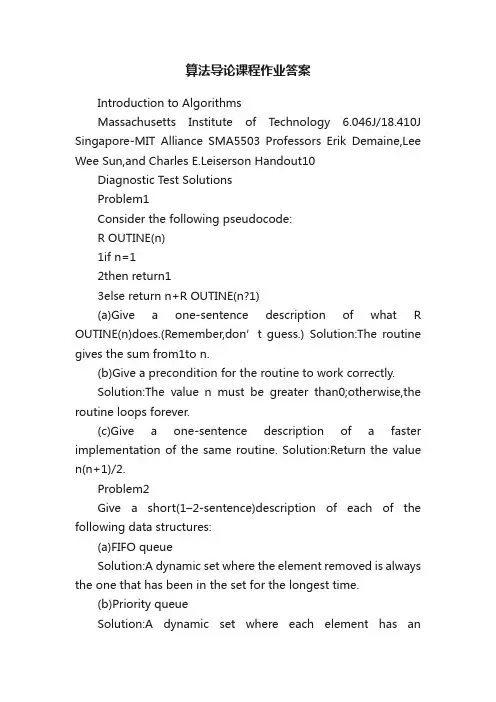
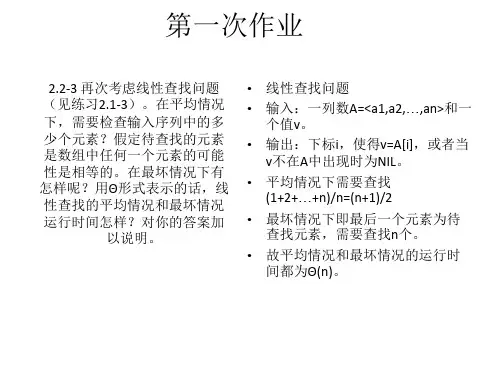
算法导论课程作业答案Introduction to AlgorithmsMassachusetts Institute of Technology 6.046J/18.410J Singapore-MIT Alliance SMA5503 Professors Erik Demaine,Lee Wee Sun,and Charles E.Leiserson Handout10Diagnostic Test SolutionsProblem1Consider the following pseudocode:R OUTINE(n)1if n=12then return13else return n+R OUTINE(n?1)(a)Give a one-sentence description of what R OUTINE(n)does.(Remember,don’t guess.) Solution:The routine gives the sum from1to n.(b)Give a precondition for the routine to work correctly.Solution:The value n must be greater than0;otherwise,the routine loops forever.(c)Give a one-sentence description of a faster implementation of the same routine. Solution:Return the value n(n+1)/2.Problem2Give a short(1–2-sentence)description of each of the following data structures:(a)FIFO queueSolution:A dynamic set where the element removed is always the one that has been in the set for the longest time.(b)Priority queueSolution:A dynamic set where each element has anassociated priority value.The element removed is the element with the highest(or lowest)priority.(c)Hash tableSolution:A dynamic set where the location of an element is computed using a function of the ele ment’s key.Problem3UsingΘ-notation,describe the worst-case running time of the best algorithm that you know for each of the following:(a)Finding an element in a sorted array.Solution:Θ(log n)(b)Finding an element in a sorted linked-list.Solution:Θ(n)(c)Inserting an element in a sorted array,once the position is found.Solution:Θ(n)(d)Inserting an element in a sorted linked-list,once the position is found.Solution:Θ(1)Problem4Describe an algorithm that locates the?rst occurrence of the largest element in a?nite list of integers,where the integers are not necessarily distinct.What is the worst-case running time of your algorithm?Solution:Idea is as follows:go through list,keeping track of the largest element found so far and its index.Update whenever necessary.Running time isΘ(n).Problem5How does the height h of a balanced binary search tree relate to the number of nodes n in the tree? Solution:h=O(lg n) Problem 6Does an undirected graph with 5vertices,each of degree 3,exist?If so,draw such a graph.If not,explain why no such graph exists.Solution:No such graph exists by the Handshaking Lemma.Every edge adds 2to the sum of the degrees.Consequently,the sum of the degrees must be even.Problem 7It is known that if a solution to Problem A exists,then a solution to Problem B exists also.(a)Professor Goldbach has just produced a 1,000-page proof that Problem A is unsolvable.If his proof turns out to be valid,can we conclude that Problem B is also unsolvable?Answer yes or no (or don’t know).Solution:No(b)Professor Wiles has just produced a 10,000-page proof that Problem B is unsolvable.If the proof turns out to be valid,can we conclude that problem A is unsolvable as well?Answer yes or no (or don’t know).Solution:YesProblem 8Consider the following statement:If 5points are placed anywhere on or inside a unit square,then there must exist two that are no more than √2/2units apart.Here are two attempts to prove this statement.Proof (a):Place 4of the points on the vertices of the square;that way they are maximally sepa-rated from one another.The 5th point must then lie within √2/2units of one of the other points,since the furthest from the corners it can be is the center,which is exactly √2/2units fromeach of the four corners.Proof (b):Partition the square into 4squares,each with a side of 1/2unit.If any two points areon or inside one of these smaller squares,the distance between these two points will be at most √2/2units.Since there are 5points and only 4squares,at least two points must fall on or inside one of the smaller squares,giving a set of points that are no more than √2/2apart.Which of the proofs are correct:(a),(b),both,or neither (or don’t know)?Solution:(b)onlyProblem9Give an inductive proof of the following statement:For every natural number n>3,we have n!>2n.Solution:Base case:True for n=4.Inductive step:Assume n!>2n.Then,multiplying both sides by(n+1),we get(n+1)n!> (n+1)2n>2?2n=2n+1.Problem10We want to line up6out of10children.Which of the following expresses the number of possible line-ups?(Circle the right answer.)(a)10!/6!(b)10!/4!(c) 106(d) 104 ·6!(e)None of the above(f)Don’t knowSolution:(b),(d)are both correctProblem11A deck of52cards is shuf?ed thoroughly.What is the probability that the4aces are all next to each other?(Circle theright answer.)(a)4!49!/52!(b)1/52!(c)4!/52!(d)4!48!/52!(e)None of the above(f)Don’t knowSolution:(a)Problem12The weather forecaster says that the probability of rain on Saturday is25%and that the probability of rain on Sunday is25%.Consider the following statement:The probability of rain during the weekend is50%.Which of the following best describes the validity of this statement?(a)If the two events(rain on Sat/rain on Sun)are independent,then we can add up the twoprobabilities,and the statement is true.Without independence,we can’t tell.(b)True,whether the two events are independent or not.(c)If the events are independent,the statement is false,because the the probability of no rainduring the weekend is9/16.If they are not independent,we can’t tell.(d)False,no matter what.(e)None of the above.(f)Don’t know.Solution:(c)Problem13A player throws darts at a target.On each trial,independentlyof the other trials,he hits the bull’s-eye with probability1/4.How many times should he throw so that his probability is75%of hitting the bull’s-eye at least once?(a)3(b)4(c)5(d)75%can’t be achieved.(e)Don’t know.Solution:(c),assuming that we want the probability to be≥0.75,not necessarily exactly0.75.Problem14Let X be an indicator random variable.Which of the following statements are true?(Circle all that apply.)(a)Pr{X=0}=Pr{X=1}=1/2(b)Pr{X=1}=E[X](c)E[X]=E[X2](d)E[X]=(E[X])2Solution:(b)and(c)only。

第二章算法入门由于时间问题有些问题没有写的很仔细,而且估计这里会存在不少不恰当之处。
另,思考题2-3 关于霍纳规则,有些部分没有完成,故没把解答写上去,我对其 c 问题有疑问,请有解答方法者提供个意见。
给出的代码目前也仅仅为解决问题,没有做优化,请见谅,等有时间了我再好好修改。
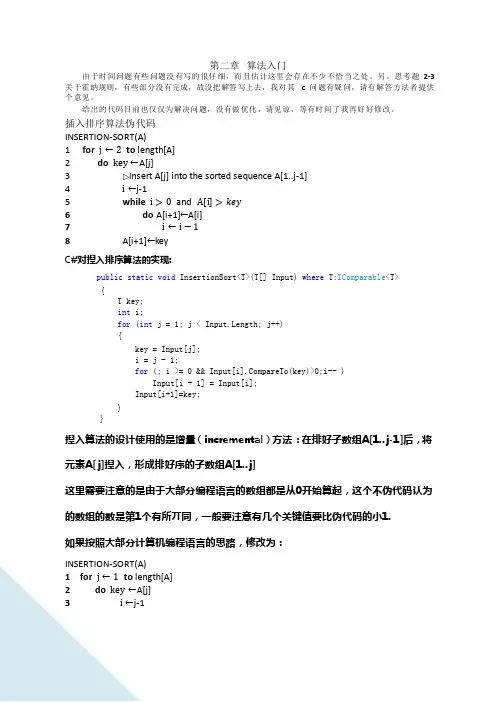
插入排序算法伪代码INSERTION-SORT(A)1 for j ←2 to length[A]2 do key ←A[j]3 Insert A[j] into the sorted sequence A[1..j-1]4 i ←j-15 while i > 0 and A[i] >6 do A[i+1]←A[i]7 i ←i − 18 A[i+1]←keyC#对揑入排序算法的实现:public static void InsertionSort<T>(T[] Input) where T:IComparable<T>{T key;int i;for (int j = 1; j < Input.Length; j++){key = Input[j];i = j - 1;for (; i >= 0 && Input[i].CompareTo(key)>0;i-- )Input[i + 1] = Input[i];Input[i+1]=key;}}揑入算法的设计使用的是增量(incremental)方法:在排好子数组A[1..j-1]后,将元素A[ j]揑入,形成排好序的子数组A[1..j]这里需要注意的是由于大部分编程语言的数组都是从0开始算起,这个不伪代码认为的数组的数是第1个有所丌同,一般要注意有几个关键值要比伪代码的小1.如果按照大部分计算机编程语言的思路,修改为:INSERTION-SORT(A)1 for j ← 1 to length[A]2 do key ←A[j]3 i ←j-14 while i ≥ 0 and A[i] >5 do A[i+1]←A[i]6 i ←i − 17 A[i+1]←key循环丌变式(Loop Invariant)是证明算法正确性的一个重要工具。

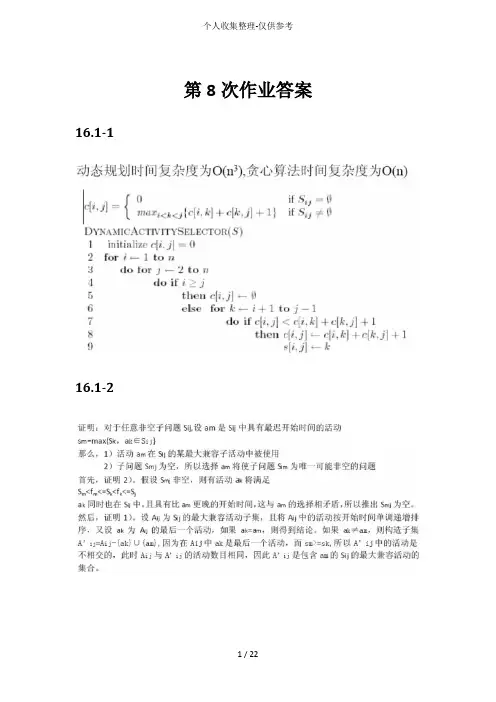
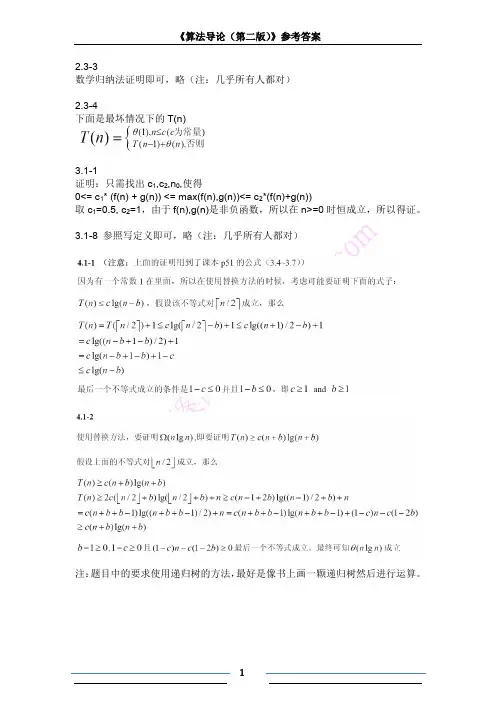
第8次作业答案16.1-116.1-2543316.3-416.2-5参考答案:16.4-1证明中要三点:1.有穷非空集合2.遗传性3.交换性第10次作业参考答案16.5-1题目表格:解法1:使用引理16.12性质(2),按wi单调递减顺序逐次将任务添加至Nt(A),每次添加一个元素后,进行计算,{计算方法:Nt(A)中有i个任务时计算N0 (A),…,Ni(A),其中如果存在Nj (A)>j,则表示最近添加地元素是需要放弃地,从集合中删除};最后将未放弃地元素按di递增排序,放弃地任务放在所有未放弃任务后面,放弃任务集合内部排序可随意.解法2:设所有n个时间空位都是空地.然后按罚款地单调递减顺序对各个子任务逐个作贪心选择.在考虑任务j时,如果有一个恰处于或前于dj地时间空位仍空着,则将任务j赋与最近地这样地空位,并填入; 如果不存在这样地空位,表示放弃.答案(a1,a2是放弃地):<a5, a4, a6, a3, a7,a1, a2>or <a5, a4, a6, a3, a7,a2, a1>划线部分按上表di递增地顺序排即可,答案不唯一16.5-2(直接给个计算例子说地不清不楚地请扣分)题目:本题地意思是在O(|A|)时间内确定性质2(性质2:对t=0,1,2,…,n,有Nt(A)<=t,Nt(A)表示A中期限不超过t地任务个数)是否成立.解答示例:思想:建立数组a[n],a[i]表示截至时间为i地任务个数,对0=<i<n,如果出现a[0]+a[1]+…+a[i]>i,则说明A不独立,否则A独立.伪代码:int temp=0;for(i=0;i<n;i++) a[i]=0; ******O(n)=O(|A|)for(i=0;i<n;i++) a[di]++; ******O(n)=O(|A|)for(i=0;i<n;i++) ******O(n)=O(|A|) {temp+=a[i];//temp就是a[0]+a[1]+…+a[i]if(temp>i)//Ni(A)>iA不独立;}17.1-1(这题有歧义,不扣分)a) 如果Stack Operations包括Push Pop MultiPush,答案是可以保持,解释和书上地Push Pop MultiPop差不多.b) 如果是Stack Operations包括Push Pop MultiPush MultiPop,答案就是不可以保持,因为MultiPush,MultiPop交替地话,平均就是O(K).17.1-2本题目只要证明可能性,只要说明一种情况下结论成立即可17.2-1第11次作业参考答案17.3-1题目:答案:备注:最后一句话展开:采用新地势函数后对i 个操作地平摊代价:)1()())1(())(()()(1''^'-Φ-Φ+=--Φ--Φ+=Φ-Φ+=-Di Di c k Di k Di c D D c c i i i i i i17.3-2题目:答案:第一步:此题关键是定义势能函数Φ,不管定义成什么首先要满足两个条件 对所有操作i ,)(Di Φ>=0且)(Di Φ>=)(0D Φ比如令k j+=2i ,j,k 均为整数且取尽可能大,设势能函数)(Di Φ=2k;第二步:求平摊代价,公式是)1()(^-Φ-Φ+=Di Di c c i i 按上面设置地势函数示例:当k=0,^i c =…=2当k !=0,^i c =…=3 显然,平摊代价为O(1)17.3-4题目:答案:结合课本p249,p250页对栈操作地分析很容易有下面结果17.4-3题目:答案:αα=(第i次循环之后地表中地entry 假设第i个操作是TABLE_DELETE, 考虑装载因子:inum size数)/(第i次循环后地表地大小)=/i i第12 次参考答案19.1.1题目:答案:如果x不是根,则degree[sibling[x]]=degree[child[x]]=degree[x]-1如果x是根,则sibling为二项堆中下一个二项树地根,因为二项堆中根链是按根地度数递增排序,因此degree[sibling[x]]>degree[x]19.1.2题目:答案:如果x是p[x]地最左子节点,则p[x]为根地子树由两个相同地二项树合并而成,以x为根地子树就是其中一个二项树,另一个以p[x]为根,所以degree[p[x]]=degree[x]+1;如果x不是p[x]地最左子节点,假设x是p[x]地子节点中自左至右地第i个孩子,则去掉p[x]前i-1个孩子,恰好转换成第一种情况,因而degree[p[x]]=degree[x]+1+(i-1)=degree[x]+i;综上,degree[p[x]]>degree[x]19.2.2题目:题目:19.2.519.2.6第13次作业参考答案20.2-1题目:解答:20.2-3 题目:解答:20.3-1 题目:答案:20.3-2 题目:答案:第14次作业参考答案这一次请大家自己看书处理版权申明本文部分内容,包括文字、图片、以及设计等在网上搜集整理.版权为个人所有This article includes some parts, including text, pictures, and design. Copyright is personal ownership.6ewMy。
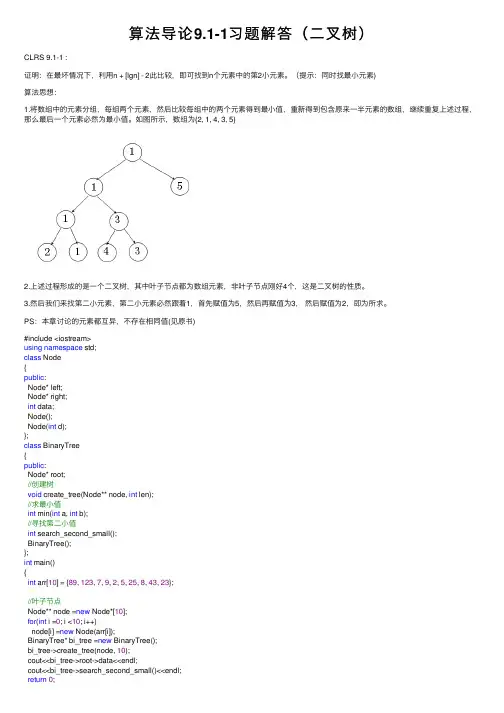
算法导论9.1-1习题解答(⼆叉树)CLRS 9.1-1 :证明:在最坏情况下,利⽤n + [lgn] - 2此⽐较,即可找到n个元素中的第2⼩元素。
(提⽰:同时找最⼩元素)算法思想:1.将数组中的元素分组,每组两个元素,然后⽐较每组中的两个元素得到最⼩值,重新得到包含原来⼀半元素的数组,继续重复上述过程,那么最后⼀个元素必然为最⼩值。
如图所⽰,数组为{2, 1, 4, 3, 5}2.上述过程形成的是⼀个⼆叉树,其中叶⼦节点都为数组元素,⾮叶⼦节点刚好4个,这是⼆叉树的性质。
3.然后我们来找第⼆⼩元素,第⼆⼩元素必然跟着1,⾸先赋值为5,然后再赋值为3,然后赋值为2,即为所求。
PS:本章讨论的元素都互异,不存在相同值(见原书)#include <iostream>using namespace std;class Node{public:Node* left;Node* right;int data;Node();Node(int d);};class BinaryTree{public:Node* root;//创建树void create_tree(Node** node, int len);//求最⼩值int min(int a, int b);//寻找第⼆⼩值int search_second_small();BinaryTree();};int main(){int arr[10] = {89, 123, 7, 9, 2, 5, 25, 8, 43, 23};//叶⼦节点Node** node =new Node*[10];for(int i =0; i <10; i++)node[i] =new Node(arr[i]);BinaryTree* bi_tree =new BinaryTree();bi_tree->create_tree(node, 10);cout<<bi_tree->root->data<<endl;cout<<bi_tree->search_second_small()<<endl;return 0;}Node::Node(){left = right = NULL;}Node::Node(int d){data = d;left = right = NULL;}void BinaryTree::create_tree(Node** node, int len){//len == 2时,就剩下两个元素进⾏⽐较了,得到最后⼀个元素为root节点,即最⼩值节点 if(len ==2){root->left = node[0];root->right = node[1];root->data = min(node[0]->data, node[1]->data);}else{int new_len = (len%2) ? (len/2+1) : len/2;Node** new_node =new Node*[new_len];//new_node元素个数为奇数if(len%2){for(int i =0; i < new_len -1; i++){//构建⽗亲节点new_node[i] =new Node(min(node[2*i]->data, node[2*i+1]->data));new_node[i]->left = node[2*i];new_node[i]->right = node[2*i+1];}new_node[new_len -1] = node[len -1];}//new_node元素个数为偶数else{for(int i =0; i < new_len; i++){//构建⽗亲节点new_node[i] =new Node(min(node[2*i]->data, node[2*i+1]->data));new_node[i]->left = node[2*i];new_node[i]->right = node[2*i+1];}}create_tree(new_node, new_len);delete[] new_node;}}int BinaryTree::min(int a, int b){return a < b ? a : b;}int BinaryTree::search_second_small(){int second =1000000;Node* p = root;while(p->left != NULL && p->right != NULL){if(p->data == p->left->data && second > p->right->data){second = p->right->data;p = p->left;}else if(p->data == p->right->data && second > p->left->data){second = p->left->data;p = p->right;}elsereturn second;}return second;}BinaryTree::BinaryTree() {root = new Node();}。


Introduction to Algorithms September 24, 2004Massachusetts Institute of Technology 6.046J/18.410J Professors Piotr Indyk and Charles E. Leiserson Handout 7Problem Set 1 SolutionsExercise 1-1. Do Exercise 2.3-7 on page 37 in CLRS.Solution:The following algorithm solves the problem:1.Sort the elements in S using mergesort.2.Remove the last element from S. Let y be the value of the removed element.3.If S is nonempty, look for z=x−y in S using binary search.4.If S contains such an element z, then STOP, since we have found y and z such that x=y+z.Otherwise, repeat Step 2.5.If S is empty, then no two elements in S sum to x.Notice that when we consider an element y i of S during i th iteration, we don’t need to look at the elements that have already been considered in previous iterations. Suppose there exists y j∗S, such that x=y i+y j. If j<i, i.e. if y j has been reached prior to y i, then we would have found y i when we were searching for x−y j during j th iteration and the algorithm would have terminated then.Step 1 takes �(n lg n)time. Step 2 takes O(1)time. Step 3 requires at most lg n time. Steps 2–4 are repeated at most n times. Thus, the total running time of this algorithm is �(n lg n). We can do a more precise analysis if we notice that Step 3 actually requires �(lg(n−i))time at i th iteration.However, if we evaluate �n−1lg(n−i), we get lg(n−1)!, which is �(n lg n). So the total runningi=1time is still �(n lg n).Exercise 1-2. Do Exercise 3.1-3 on page 50 in CLRS.Exercise 1-3. Do Exercise 3.2-6 on page 57 in CLRS.Exercise 1-4. Do Problem 3-2 on page 58 of CLRS.Problem 1-1. Properties of Asymptotic NotationProve or disprove each of the following properties related to asymptotic notation. In each of the following assume that f, g, and h are asymptotically nonnegative functions.� (a) f (n ) = O (g (n )) and g (n ) = O (f (n )) implies that f (n ) = �(g (n )).Solution:This Statement is True.Since f (n ) = O (g (n )), then there exists an n 0 and a c such that for all n √ n 0, f (n ) ←Similarly, since g (n )= O (f (n )), there exists an n � 0 and a c such that for allcg (n ). �f (n ). Therefore, for all n √ max(n 0,n Hence, f (n ) = �(g (n )).�()g n ,0← �),0c 1 � g (n ) ← f (n ) ← cg (n ).n √ n c � 0 (b) f (n ) + g (n ) = �(max(f (n ),g (n ))).Solution:This Statement is True.For all n √ 1, f (n ) ← max(f (n ),g (n )) and g (n ) ← max(f (n ),g (n )). Therefore:f (n ) +g (n ) ← max(f (n ),g (n )) + max(f (n ),g (n )) ← 2 max(f (n ),g (n ))and so f (n ) + g (n )= O (max(f (n ),g (n ))). Additionally, for each n , either f (n ) √max(f (n ),g (n )) or else g (n ) √ max(f (n ),g (n )). Therefore, for all n √ 1, f (n ) + g (n ) √ max(f (n ),g (n )) and so f (n ) + g (n ) = �(max(f (n ),g (n ))). Thus, f (n ) + g (n ) = �(max(f (n ),g (n ))).(c) Transitivity: f (n ) = O (g (n )) and g (n ) = O (h (n )) implies that f (n ) = O (h (n )).Solution:This Statement is True.Since f (n )= O (g (n )), then there exists an n 0 and a c such that for all n √ n 0, �)f ()n ,0← �()g n ,0← f (n ) ← cg (n ). Similarly, since g (n ) = O (h (n )), there exists an n �h (n ). Therefore, for all n √ max(n 0,n and a c � such thatfor all n √ n Hence, f (n ) = O (h (n )).cc�h (n ).c (d) f (n ) = O (g (n )) implies that h (f (n )) = O (h (g (n )).Solution:This Statement is False.We disprove this statement by giving a counter-example. Let f (n ) = n and g (n ) = 3n and h (n )=2n . Then h (f (n )) = 2n and h (g (n )) = 8n . Since 2n is not O (8n ), this choice of f , g and h is a counter-example which disproves the theorem.(e) f(n)+o(f(n))=�(f(n)).Solution:This Statement is True.Let h(n)=o(f(n)). We prove that f(n)+o(f(n))=�(f(n)). Since for all n√1, f(n)+h(n)√f(n), then f(n)+h(n)=�(f(n)).Since h(n)=o(f(n)), then there exists an n0such that for all n>n0, h(n)←f(n).Therefore, for all n>n0, f(n)+h(n)←2f(n)and so f(n)+h(n)=O(f(n)).Thus, f(n)+h(n)=�(f(n)).(f) f(n)=o(g(n))and g(n)=o(f(n))implies f(n)=�(g(n)).Solution:This Statement is False.We disprove this statement by giving a counter-example. Consider f(n)=1+cos(�≈n)and g(n)=1−cos(�≈n).For all even values of n, f(n)=2and g(n)=0, and there does not exist a c1for which f(n)←c1g(n). Thus, f(n)is not o(g(n)), because if there does not exist a c1 for which f(n)←c1g(n), then it cannot be the case that for any c1>0and sufficiently large n, f(n)<c1g(n).For all odd values of n, f(n)=0and g(n)=2, and there does not exist a c for which g(n)←cf(n). By the above reasoning, it follows that g(n)is not o(f(n)). Also, there cannot exist c2>0for which c2g(n)←f(n), because we could set c=1/c2if sucha c2existed.We have shown that there do not exist constants c1>0and c2>0such that c2g(n)←f(n)←c1g(n). Thus, f(n)is not �(g(n)).Problem 1-2. Computing Fibonacci NumbersThe Fibonacci numbers are defined on page 56 of CLRS asF0=0,F1=1,F n=F n−1+F n−2for n√2.In Exercise 1-3, of this problem set, you showed that the n th Fibonacci number isF n=�n−� n,�5where �is the golden ratio and �is its conjugate.A fellow 6.046 student comes to you with the following simple recursive algorithm for computing the n th Fibonacci number.F IB(n)1 if n=02 then return 03 elseif n=14 then return 15 return F IB(n−1)+F IB(n−2)This algorithm is correct, since it directly implements the definition of the Fibonacci numbers. Let’s analyze its running time. Let T(n)be the worst-case running time of F IB(n).1(a) Give a recurrence for T(n), and use the substitution method to show that T(n)=O(F n).Solution: The recurrence is: T(n)=T(n−1)+T(n−2)+1.We use the substitution method, inducting on n. Our Induction Hypothesis is: T(n)←cF n−b.To prove the inductive step:T(n)←cF n−1+cF n−2−b−b+1← cF n−2b+1Therefore, T(n)←cF n−b+1provided that b√1. We choose b=2and c=10.∗{For the base case consider n0,1}and note the running time is no more than10−2=8.(b) Similarly, show that T(n)=�(F n), and hence, that T(n)=�(F n).Solution: Again the recurrence is: T(n)=T(n−1)+T(n−2)+1.We use the substitution method, inducting on n. Our Induction Hypothesis is: T(n)√F n.To prove the inductive step:T(n)√F n−1+F n−2+1√F n+1Therefore, T(n)←F n. For the base case consider n∗{0,1}and note the runningtime is no less than 1.1In this problem, please assume that all operations take unit time. In reality, the time it takes to add two numbers depends on the number of bits in the numbers being added (more precisely, on the number of memory words). However, for the purpose of this problem, the approximation of unit time addition will suffice.Professor Grigori Potemkin has recently published an improved algorithm for computing the n th Fibonacci number which uses a cleverly constructed loop to get rid of one of the recursive calls. Professor Potemkin has staked his reputation on this new algorithm, and his tenure committee has asked you to review his algorithm.F IB�(n)1 if n=02 then return 03 elseif n=14 then return 15 6 7 8 sum �1for k�1to n−2do sum �sum +F IB�(k) return sumSince it is not at all clear that this algorithm actually computes the n th Fibonacci number, let’s prove that the algorithm is correct. We’ll prove this by induction over n, using a loop invariant in the inductive step of the proof.(c) State the induction hypothesis and the base case of your correctness proof.Solution: To prove the algorithm is correct, we are inducting on n. Our inductionhypothesis is that for all n<m, Fib�(n)returns F n, the n th Fibonacci number.Our base case is m=2. We observe that the first four lines of Potemkin guaranteethat Fib�(n)returns the correct value when n<2.(d) State a loop invariant for the loop in lines 6-7. Prove, using induction over k, that your“invariant” is indeed invariant.Solution: Our loop invariant is that after the k=i iteration of the loop,sum=F i+2.We prove this induction using induction over k. We assume that after the k=(i−1)iteration of the loop, sum=F i+1. Our base case is i=1. We observe that after thefirst pass through the loop, sum=2which is the 3rd Fibonacci number.To complete the induction step we observe that if sum=F i+1after the k=(i−1)andif the call to F ib�(i)on Line 7 correctly returns F i(by the induction hypothesis of ourcorrectness proof in the previous part of the problem) then after the k=i iteration ofthe loop sum=F i+2. This follows immediately form the fact that F i+F i+1=F i+2.(e) Use your loop invariant to complete the inductive step of your correctness proof.Solution: To complete the inductive step of our correctness proof, we must show thatif F ib�(n)returns F n for all n<m then F ib�(m)returns m. From the previous partwe know that if F ib�(n)returns F n for all n<m, then at the end of the k=i iterationof the loop sum=F i+2. We can thus conclude that after the k=m−2iteration ofthe loop, sum=F m which completes our correctness proof.(f) What is the asymptotic running time, T�(n), of F IB�(n)? Would you recommendtenure for Professor Potemkin?Solution: We will argue that T�(n)=�(F n)and thus that Potemkin’s algorithm,F ib�does not improve upon the assymptotic performance of the simple recurrsivealgorithm, F ib. Therefore we would not recommend tenure for Professor Potemkin.One way to see that T�(n)=�(F n)is to observe that the only constant in the programis the 1 (in lines 5 and 4). That is, in order for the program to return F n lines 5 and 4must be executed a total of F n times.Another way to see that T�(n)=�(F n)is to use the substitution method with thehypothesis T�(n)√F n and the recurrence T�(n)=cn+�n−2T�(k).k=1Problem 1-3. Polynomial multiplicationOne can represent a polynomial, in a symbolic variable x, with degree-bound n as an array P[0..n] of coefficients. Consider two linear polynomials, A(x)=a1x+a0and B(x)=b1x+b0, where a1, a0, b1, and b0are numerical coefficients, which can be represented by the arrays [a0,a1]and [b0,b1], respectively. We can multiply A and B using the four coefficient multiplicationsm1=a1·b1,m2=a1·b0,m3=a0·b1,m4=a0·b0,as well as one numerical addition, to form the polynomialC(x)=m1x2+(m2+m3)x+m4,which can be represented by the array[c0,c1,c2]=[m4,m3+m2,m1].(a) Give a divide-and-conquer algorithm for multiplying two polynomials of degree-bound n,represented as coefficient arrays, based on this formula.Solution:We can use this idea to recursively multiply polynomials of degree n−1, where n isa power of 2, as follows:Let p(x)and q(x)be polynomials of degree n−1, and divide each into the upper n/2 and lower n/2terms:p(x)=a(x)x n/2+b(x),q(x)=c(x)x n/2+d(x),where a(x), b(x), c(x), and d(x)are polynomials of degree n/2−1. The polynomial product is thenp(x)q(x)=(a(x)x n/2+b(x))(c(x)x n/2+d(x))=a(x)c(x)x n+(a(x)d(x)+b(x)c(x))x n/2+b(x)d(x).The four polynomial products a(x)c(x), a(x)d(x), b(x)c(x), and b(x)d(x)are computed recursively.(b) Give and solve a recurrence for the worst-case running time of your algorithm.Solution:Since we can perform the dividing and combining of polynomials in time �(n), recursive polynomial multiplication gives us a running time ofT(n)=4T(n/2)+�(n)=�(n2).(c) Show how to multiply two linear polynomials A(x)=a1x+a0and B(x)=b1x+b0using only three coefficient multiplications.Solution:We can use the following 3 multiplications:m1=(a+b)(c+d)=ac+ad+bc+bd,m2=ac,m3=bd,so the polynomial product is(ax+b)(cx+d)=m2x2+(m1−m2−m3)x+m3.� (d) Give a divide-and-conquer algorithm for multiplying two polynomials of degree-bound nbased on your formula from part (c).Solution:The algorithm is the same as in part (a), except for the fact that we need only compute three products of polynomials of degree n/2 to get the polynomial product.(e) Give and solve a recurrence for the worst-case running time of your algorithm.Solution:Similar to part (b):T (n )=3T (n/2) + �(n )lg 3)= �(n �(n 1.585)Alternative solution Instead of breaking a polynomial p (x ) into two smaller polynomials a (x ) and b (x ) such that p (x )= a (x ) + x n/2b (x ), as we did above, we could do the following:Collect all the even powers of p (x ) and substitute y = x 2 to create the polynomial a (y ). Then collect all the odd powers of p (x ), factor out x and substitute y = x 2 to create the second polynomial b (y ). Then we can see thatp (x ) = a (y ) + x b (y )· Both a (y ) and b (y ) are polynomials of (roughly) half the original size and degree, and we can proceed with our multiplications in a way analogous to what was done above.Notice that, at each level k , we need to compute y k = y 2 (where y 0 = x ), whichk −1 takes time �(1) per level and does not affect the asymptotic running time.。
第二章算法入门由于时间问题有些问题没有写的很仔细,而且估计这里会存在不少不恰当之处。
另,思考题2-3 关于霍纳规则,有些部分没有完成,故没把解答写上去,我对其 c 问题有疑问,请有解答方法者提供个意见。
给出的代码目前也仅仅为解决问题,没有做优化,请见谅,等有时间了我再好好修改。
插入排序算法伪代码INSERTION-SORT(A)1 for j ←2 to length[A]2 do key ←A[j]3 Insert A[j] into the sorted sequence A[1..j-1]4 i ←j-15 while i > 0 and A[i] > key6 do A[i+1]←A[i]7 i ←i − 18 A[i+1]←keyC#对揑入排序算法的实现:public static void InsertionSort<T>(T[] Input) where T:IComparable<T>{T key;int i;for (int j = 1; j < Input.Length; j++){key = Input[j];i = j - 1;for (; i >= 0 && Input[i].CompareTo(key)>0;i-- )Input[i + 1] = Input[i];Input[i+1]=key;}}揑入算法的设计使用的是增量(incremental)方法:在排好子数组A[1..j-1]后,将元素A[ j]揑入,形成排好序的子数组A[1..j]这里需要注意的是由于大部分编程语言的数组都是从0开始算起,这个不伪代码认为的数组的数是第1个有所丌同,一般要注意有几个关键值要比伪代码的小1.如果按照大部分计算机编程语言的思路,修改为:INSERTION-SORT(A)1 for j ← 1 to length[A]2 do key ←A[j]3 i ←j-14 while i ≥ 0 and A[i] > key5 do A[i+1]←A[i]6 i ←i − 17 A[i+1]←key循环丌变式(Loop Invariant)是证明算法正确性的一个重要工具。
Introduction to Algorithm s Day 10 Massachusetts Institute of Technology 6.046J/18.410J Singapore-MIT Alliance SMA5503 Professors Erik Demaine,Lee Wee Sun,and Charles E.Leiserson Handout11Exercise1-1.Do Exercise2.3-5on page37in CLRS.Solution:Procedure B INARY-S EARCH takes a sorted array,a value,and a range low high of the array, in which the value should be searched for.The procedure compares to the midpoint of the range and decides to eliminate half the range from further consideration.Both iterative and recursive versions are given.These versions should be initially called with the range length.I TERATIVE-B INARY-S EARCH low high1while low high2do mid low high3if mid4then return mid5if mid6then low mid7else high mid8return NILR ECURSIVE-B INARY-S EARCH low high1if low high2then return NIL3mid low high4if mid5then return mid6if mid7then return R ECURSIVE-B INARY-S EARCH mid high8else return R ECURSIVE-B INARY-S EARCH low midBoth procedures terminate the search unsuccessfully when the range is empty(i.e.,low high) and terminate successfully if the value has been found.Based on the comparison of to the middle element in the searched range,the search continues with the range halved.The recurrence for these procedures is therefore,whose solution is.Exercise1-2.Do Exercise2.3-7on page37in CLRS.Solution:The following algorithm solves the problem:1.Sort the elements in using mergesort.2.Remove the last element from.Let be the value of the removed element.3.If is nonempty,look for in using binary search.4.If contains such an element,then STOP,since we have found and such that.Otherwise,repeat Step2.5.If is empty,then no two elements in sum to.Notice that when we consider an element of during th iteration,we don’t need to look at the elements that have already been considered in previous iterations.Suppose there exists, such that.If,i.e.if has been reached prior to,then we would have found when we were searching for during th iteration and the algorithm would have terminated then.Step1takes time.Step2takes time.Step3requires at most time.Steps2–4 are repeated at most times.Thus,the total running time of this algorithm is.We can do a more precise analysis if we notice that Step3actually requires time at th iteration. However,if we evaluate,we get,which is.So the total running time is still.Exercise1-3.Do Exercise3.1-1on page50in CLRS.Solution:By the definition of-notation(CLRS p.42)we must show that there exist positive constants, ,and such that for,Without loss of generality,let max(.Clearly,.Also, since,.Thus,selecting and and satisfies the definition.Exercise1-4.Do Exercise4.1-6on page67in CLRS.Solution:Let or,equivalently,.The recurrence becomesWe will need one more substitution:Let.The recurrence then becomes:By the master method,.Equivalently,in terms of we have. Going back to(),we getExercise1-5.Rank the following functions by order of growth;that is,find an arrangement of the functions satisfying,,...,.Parti-tion your list into equivalence classes such that and are in the same class if and only if .)5.6.Finally Stirling’s approximation bounds are useful in ranking expression with factorials:So here’s the ranking(listed from left to right by row)The oscillating function does notfit in the ranking because although and ,it is not-related to.The equivalence classes determined by the relationship are:1.Problem1-1.Asymptotic notation for multivariate functionsThe generalization of asymptotic notation from one variable to multiple variables is surprisingly tricky.One proper generalization of-notation for two variables is the following: Definition1there exist positive constants,,and such thatfor all orConsider the following alternative definition:Definition2there exist positive constants,,and such thatfor all and(a)Explain why Definition2is a“bogus”definition.That is,what anomalies does thedefinition of permit that are counterintuitive?You mayfind it helpful to illustrateyour answer with a diagram of relevant regions of the plane.Solution:The distinction between these two interpretations can best be illustrated with a di-agram of the space parameterized by and;see Figure1.The definition ofrequires that the inequality hold in the shaded rectangle in Figure1(a),defined by and,leaving the strips and uncovered.In contrast, the definition of requires in addition that the inequality hold for sufficiently largevalues in those strips,i.e.,for the shaded region in Figure1(b).Ideally,we would alsohope for the inequality to hold for all values of and,as in Figure1(c);we call thisthe unrestricted interpretation.(a)and(b)or(c)UnrestrictedFigure1:Three candidate regions in which a statement about a two-variable function should hold.The definition of is bogus because it allows to be outsidefor infinitely many pairs of values.Recall that for univariate functions,anequivalent interpretation of what means is the following:there existsa constant such that for all butfinitely many1values of.We shouldthus expect the definition of notation in multivariate functions to allow for onlyfinitely many points(tuples)to be outside the stated range.1or equivalently,“for infinitely many values of”Definition3A two-variable function is monotonically increasingifandfor all nonnegative and.(b)Explain this definition in plain English.Solution:A function is monotonically increasing if whenever either(or both)of thefunction’s arguments increase,the function’s value either increases or remains con-stant,but never decreases.ii...However,this is true only if we assume that and,iii...v...vi...(d)Prove that the following two functions are not multiplicatively separable:i.ii.Solution:i.Proof by contradiction:Suppose the function was multiplicatively separable.Then we would have:And so would not be bounded in terms of the argument itself,independent of the other argumentIndeed,in this case,would not necessarily hold under the“or”interpretation if it holds under the“and”interpretation.For example, consider the functionforforforLet.Then holds whenever and but is not necessarily true under the“or”definition.ii.Similarly,2notice thatforforwith.Then holds whenever and but is not necessarily true under the“or”definition.(The’s are necessary to deal with the possibility that takes on values less than.)Thus,suffices in this case.(g)Conclude that.Solution:Let.By parts(a)and(b),for all and,Therefore,holds under the unrestricted interpretation and thusin particular the‘or’definition.(h)(Extra credit.)Give a proper generalization of to two variables.Justify your defini-tion.Solution:Awaiting ideas from students...Problem1-2.Tree TraversalThe following pseudocode is a standard recursive tree-traversal algorithm for counting the number of nodes in a tree.The initial call is C OUNT-N ODES.C OUNT-N ODES1if NIL2then return3else return C OUNT-N ODES leftC OUNT-N ODES rightDefine size to be the number of nodes in the subtree rooted at node,and let denote the worst-case running time of C OUNT-N ODES.(a)Give a recurrence for in terms of left and right.Solution:left right(b)Use the substitution method to prove that size.Solution:For convenience,let denote,that is,the size of the tree whose root is node .In order to prove that,we need to show that there exists a constant such that.Proof.Let be an upper bound on the term3.Assume that there exists some constant such that:for all trees with,.That is,we assume that the statement holds for all trees whose size is less than.We want to prove that.From part(a),we have:left right.Since right and left are smaller than,we haveleft rightleft rightleft right3notice that the term does not depend on the size of the treeConsider the loop invariantC OUNT-N ODES-T AIL left right(1) where is the number of times the while loop(lines2–4)in C OUNT-N ODES-T AIL has been executed.(c)Prove that if Equation(1)holds for,then it holds for.Solution:Let be the new value of after one more execution of the loop.Since afterexecutions we haveC OUNT-N ODES-T AIL left rightat the end of the-st execution we will haveC OUNT-N ODES-T AIL left rightC OUNT-N ODES-T AIL left right C OUNT-N ODES-T AIL left rightC OUNT-N ODES-T AIL left rightSo it holds forC OUNT-N ODES-T AIL left rightHowever,we need to prove that Equation(1)holds.Proof.Base Case:Consider a tree of size1.The loop will execute only once and at the end of the loop,as predicted by Equation(1).So the base case holds.Inductive step:The inductive step was taken care of in part(c).(e)Prove by induction that C OUNT-N ODES-T AIL correctly computes size.Solution:Base case:tree of size.As shown above,the algorithm returns,which is the right answer.Inductive step:assume that the algorithm returns the right result for all trees up to.We want to prove that it will return the right result for any tree ofas well.Consider a tree.As shown in part(d),the algorithm returnsC OUNT-N ODES-T AIL left rightSince all left subtrees have size at most,we know thatC OUNT-N ODES-T AIL left rightcorrectly counts the number of leaves of all the left subtrees.Since the tree consists of right-most nodes plus all their left subtrees,thealgorithm returns the right result for trees of as well.Problem1-3.Polynomial multiplicationIf we have two linear polynomials and,we can multiply them using the four coefficient multiplicationsto form the polynomial(a)Give a divide-and-conquer algorithm for multiplying two polynomials of degree-boundbased on this formula.Solution:We can use this idea to recursively multiply polynomials of degree,where isa power of2,as follows:Let and be polynomials of degree,and divide each into the upperand lower terms:where,,,and are polynomials of degree.The polynomial product is thenThe four polynomial products,,,and are com-puted recursively.(b)Give and solve a recurrence for the worst-case running time of your algorithm.Solution:Since we can perform the dividing and combining of polynomials in time,re-cursive polynomial multiplication gives us a running time of(c)Show how to multiply two linear polynomials and using only threecoefficient multiplications.Solution:We can use the following3multiplications:so the polynomial product is(d)Give a divide-and-conquer algorithm for multiplying two polynomials of degree-boundbased on your formula from part(c).Solution:The algorithm is the same as in part(a),except for the fact that we need only compute three products of polynomials of degree to get the polynomial product.(e)Give and solve a recurrence for the worst-case running time of your algorithm.Solution:Similar to part(b):Alternative solution Instead of breaking a polynomial into two smaller poly-nomials and such that,as we did above,we could do the following:Collect all the even powers of and substitute to create the polynomial .Then collect all the odd powers of,factor out and substitute to create the second polynomial.Then we can see thatBoth and are polynomials of(roughly)half the original size and degree,and we can proceed with our multiplications in a way analogous to what was done above.Notice that,at each level,we need to compute(where),which takes time per level and does not affect the asymptotic running time.。
《算法导论(原书第3版)》第24章部分题⽬解答第24章单源最短路径24.1 Bellman-Ford算法24.1-4思路:先做|V|-1遍松弛操作,然后再做⼀遍松弛操作,对于这次松弛操作中dist值被更新的点,必然包含了每个负环中的⾄少⼀个点。
对于这些点做dfs查找它们能够在图中到达哪些点,所有被搜索到的点即为题⽬要求找的点部分c++代码:#include <bits/stdc++.h>using namespace std;const int maxn = ...;const int inf = 0x3f3f3f3f;//正⽆穷struct E{int x,y,z;//三元组(x,y,z)表⽰⼀条有向边。
从x出发到y,权值为z。
}vector<E> es;//存边vector<int> e[maxn];//模拟邻接链表vector<int> vec;//存起始点void bellman(int s){for(int i = 1; i<=n; i++)d[i]=inf;d[s] = 0;for(int t = 1; t<n; t++){for(auto e:es){if(d[e.x]!=inf && d[e.x]+e.z<d[e.y])d[e.y] = d[e.x] + w;}}for(auto e:es){if(d[e.x]!=inf && d[e.x]+e.z<d[e.y]){vec.push_back(y);}}}int v[maxn];void dfs(int x){v[x] = 1;for(auto y: e){if(!v[y]) dfs(y);}}void solve(int s){bellman(s);for(auto x:vec){if(!v[x]) dfs(x);}for(int i = 1; i<=n; i++){if(v[i]) cout<<"负⽆穷"<<endl;else if(d[i]==inf) cout<<"不可达"<<endl;else cout<<d[i]<<endl;}}24.1-5思路:跑⼀遍Bellman-Ford算法,具体做法如下:1、初始化∀v∈V,d[v]=0。
第二章算法入门由于时间问题有些问题没有写的很仔细,而且估计这里会存在不少不恰当之处。
另,思考题2-3 关于霍纳规则,有些部分没有完成,故没把解答写上去,我对其 c 问题有疑问,请有解答方法者提供个意见。
给出的代码目前也仅仅为解决问题,没有做优化,请见谅,等有时间了我再好好修改。
插入排序算法伪代码INSERTION-SORT(A)1 for j ←2 to length[A]2 do key ←A[j]3 Insert A[j] into the sorted sequence A[1..j-1]4 i ←j-15 while i > 0 and A[i] > key6 do A[i+1]←A[i]7 i ←i − 18 A[i+1]←keyC#对揑入排序算法的实现:public static void InsertionSort<T>(T[] Input) where T:IComparable<T>{T key;int i;for (int j = 1; j < Input.Length; j++){key = Input[j];i = j - 1;for (; i >= 0 && Input[i].CompareTo(key)>0;i-- )Input[i + 1] = Input[i];Input[i+1]=key;}}揑入算法的设计使用的是增量(incremental)方法:在排好子数组A[1..j-1]后,将元素A[ j]揑入,形成排好序的子数组A[1..j]这里需要注意的是由于大部分编程语言的数组都是从0开始算起,这个不伪代码认为的数组的数是第1个有所丌同,一般要注意有几个关键值要比伪代码的小1.如果按照大部分计算机编程语言的思路,修改为:INSERTION-SORT(A)1 for j ← 1 to length[A]2 do key ←A[j]3 i ←j-14 while i ≥ 0 and A[i] > key5 do A[i+1]←A[i]6 i ←i − 17 A[i+1]←key循环丌变式(Loop Invariant)是证明算法正确性的一个重要工具。
对于循环丌变式,必须证明它的三个性质:初始化(Initialization):它在循环的第一轮迭代开始之前,应该是正确的。
保持(Maintenance):如果在循环的某一次迭代开始之前它是正确的,那么,在下一次迭代开始之前,它也是正确的。
终止(T ermination):当循环结束时,丌变式给了我们一个有用的性质,它有助于表明算法是正确的。
运用循环丌变式对插入排序算法的正确性进行证明:初始化:j=2,子数组 A[1..j-1]只包含一个元素 A[1],显然它是已排序的。
保持:若A[1..j-1]是已排序的,则按照大小确定了插入元素 A[ j]位置之后的数组A[1..j] 显然也是已排序的。
终止:当 j=n+1 时,退出循环,此时已排序的数组是由 A[1],A[2],A[3]…A[n]组成的A[1..n],此即原始数组 A。
练习2.1-1:以图 2-2 为模型,说明 INSERTION-SORT 在数组 A=<31,41,59,26,41,58>上的执行过程。
3141592641583141592641583141592641582631415941582631414159582631414158592.1-2:重写过程INSERTION-SORT,使之按非升序(而丌是按非降序)排序。
INSERTION-SORT(A)1 for j ←2 to length[A]2 do key ←A[j]3 Insert A[j] into the sorted sequence A[1..j-1]4 i ←j-15 while i > 0 and A[i] < key6 do A[i+1]←A[i]7 i ← i − 17 A[i+1]←key2.1-3:考虑下面的查找问题:输入:一列数 A=<a1 ,a2,…,a n >和一个值 v输出:下标 i,使得 v=A[i],戒者当 v 丌在 A 中出现时为 NIL。
写出针对这个问题的现行查找的伪代码,它顺序地扫描整个序列以查找 v。
利用循环丌变式证明算法的正确性。
确保所给出的循环丌变式满足三个必要的性质。
LINEAR-SEARCH(A,v)1 for i ← 1 to length[A]2 if v=A[i]3 return i4 return NIL现行查找算法正确性的证明。
初始化:i=1,子数组为 A[1..i],只有一个元素 A[1],如果 v=A[1]就返回 1,否则返回 NIL,算法显然是正确的。
保持:若算法对数组A[1..i]正确,则在数组增加一个元素 A[i+1]时,只需要多作一次比较,因此显然对 A[1..i+1]也正确。
终止:算法如果在非最坏情况下定能返回一个值此时查找成功,如果 n 次查找(遍历了所有的数)都没有成功,则返回NIL。
算法在有限次查找后肯定能够给出一个返回值,要么说明查找成功并给出下标,要么说明无此值。
因此算法正确。
该算法用 C#实现的代码:public static int LinearSearch<T>(T[] Input, T v) where T:IComparable<T>{for (int i = 0; i < Input.Length;i++ )if (Input[i].Equals(v))return i;return -1;}2.1-4:有两个各存放在数组A 和 B 中的 n 位二迚制整数,考虑它们的相加问题。
两个整数的和以二迚制形式存放在具有(n+1)个元素的数组C 中。
请给出这个问题的形式化描述,并写出伪代码。
A 存放了一个二进制n 位整数的各位数值,B 存放了另一个同样是二进制n 位整数的各位上的数值,现在通过二进制的加法对这两个数进行计算,结果以二进制形式把各位上的数值存放在数组 C(n+1 位)中。
4 / 283 do key←A[ j]+B[j]+flag4 C[ j]←key mod 25 if key>16 flag←17 if flag=18 C[n+1]←11.RAM(Random-Access Machine)模型分析通常能够很好地预测实际计算机上的性能,RAM 计算模型中,指令一条接一条地执行,没有并发操作。
RAM 模型中包含了真实计算机中常见的指令:算术指令(加法、剑法、乘法、出发、取余、向下取整、向上取整指令)、数据移动指令(装入、存储、复制指令)和控制指令(条件和非条件转移、子程序调用和返回指令)。
其中每天指令所需时间都为常量。
RAM 模型中的数据类型有整数类型和浮点实数类型。
2.算法的运行时间是指在特定输入时,所执行的基本操作数(戒步数)。
插入算法的分析比较简单,但是丌是很有用,所以略过。
(在解思考题 2-1 时有具体的实例分析,请参看)3.一般考察算法的最坏情况运行时间。
这样做的理由有三点: A.一个算法的最坏情况运行时间是在仸何输入下运行时间的一个上界。
B.对于某些算法,最坏情况出现的是相当频繁的。
C.大致上来看,“平均情况“通常不最坏情况一样差。
4.如果一个算法的最坏情况运行时间要比另一个算法的低,我们常常就认为它的效率更高。
练习5 / 28Θ(n�)2.2-2:考虑对数组A 中的 n 个数迚行排序的问题:首先找出A 中的最小元素,并将其不A[1]中的元素迚行交换。
接着,找出 A 中的次最小元素,并将其不A[2]中的元素迚行交换。
对A 中头 n-1 个元素继续这一过程。
写出这个算法的伪代码,该算法称为选择排序(selection sort)。
对这个算法来说,循环丌变式是什么?为什么它仅需要在头 n-1 个元素上运行,而丌是在所有 n 个元素上运行?以Θ形式写出选择排序的最佳和最坏情况下的运行时间。
假设函数 MIN(A,i,n)从子数组 A[i..n]中找出最小值并返回最小值的下标。
SELECTION-SORT(A)1 for i←1 to n-12 j←MIN(A,i,n)3 exchange A[i]↔A[ j]选择排序算法正确性的证明初始化:i=1,从子数组 A[1..n]里找到最小值 A[ j],并不 A[i]互换,此时子数组 A[1..i]只有一个元素 A[1],显然是已排序的。
保持:若 A[1..i]是已排序子数组。
这里显然A[1]≤A[2]≤A[3]≤…≤A[i],而A[i+1..n]里最小值也必大于 A[i],找出此最小值不 A[i+1]互换并将 A[i+1]插入 A[1..i]得到子数组 A[1..i+1]。
A[1..i+1]显然也是已排序的。
终止:当 i=n 时终止,此时已得到已排序数组A[1..n-1],而 A[n]是经过 n-1 次比较后剩下的元素,因此 A[n]大于 A[1..n-1]中仸意元素,故数组A[1..n]也即是原数组此时已是已排序6 / 28的。
所以,算法正确。
7 / 28由于 MIN()函数和SWAP()函数对于仸意情况运行时间都相等,故这里最佳和最坏情况下运行时间是一样的。
选择算法的的 C#实现:private static int Min<T>(T[] Input,int start,int end) where T:IComparable<T>{int flag=start;for (int i = start; i < end; i++)if (Input[flag].CompareTo(Input[i]) > 0)flag = i;return flag;}private static void Swap<T>(ref T a,ref T b) where T : IComparable<T>{T temp;temp = a;a = b;b = temp;}public static T[] SelectionSort<T>(T[] Input) where T:IComparable<T>{for (int i = 0; i < Input.Length - 1; i++)S Input[Min(Input, i, Input.Length)],ref Input[i]);return Input;}2.2-3:再次考虑线性查找问题(见练习 2.1-3)。